NewStar2023部分Reverse与Pwn
Re
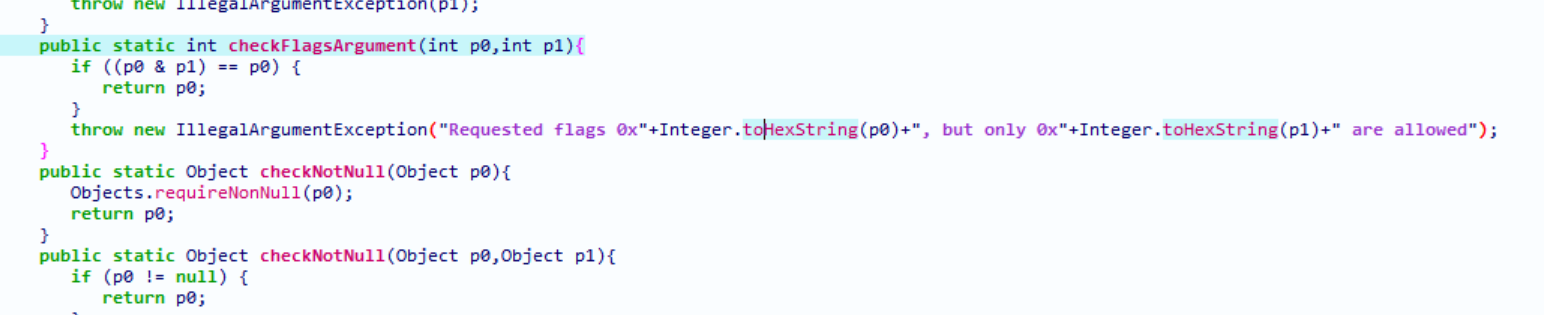
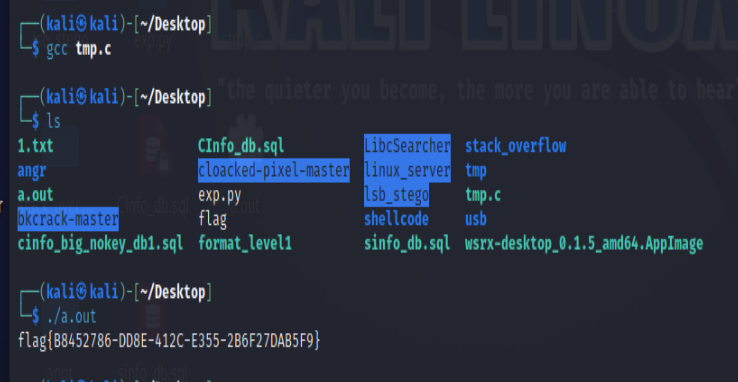
easy_re
把flag拆开了,拼起来就行
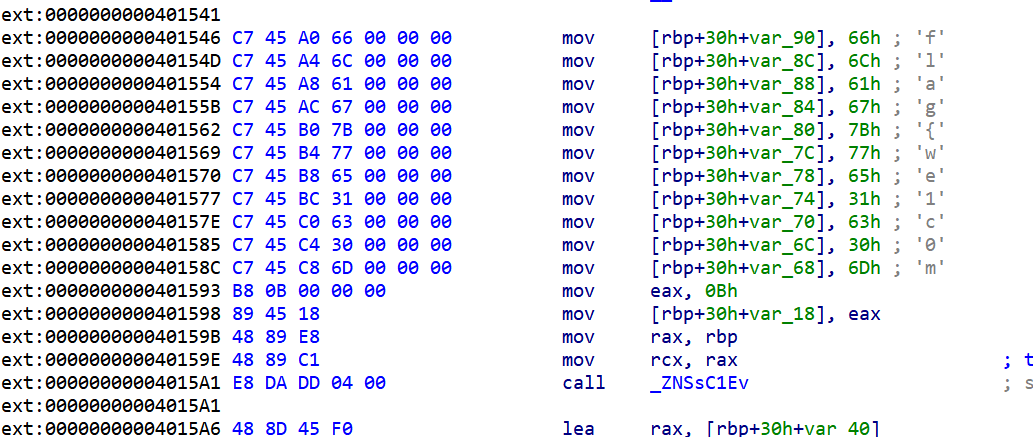
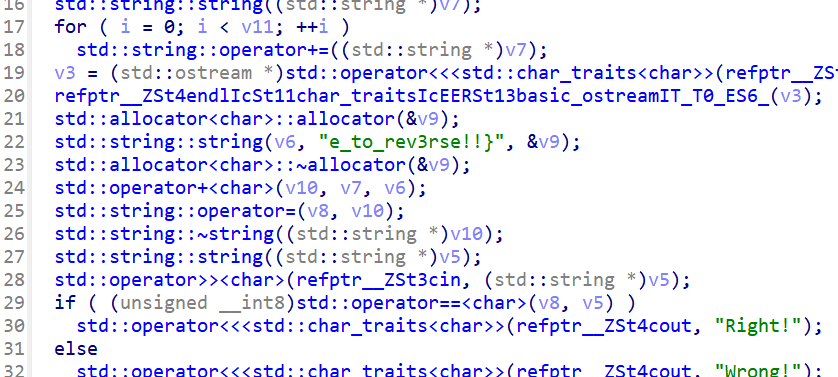
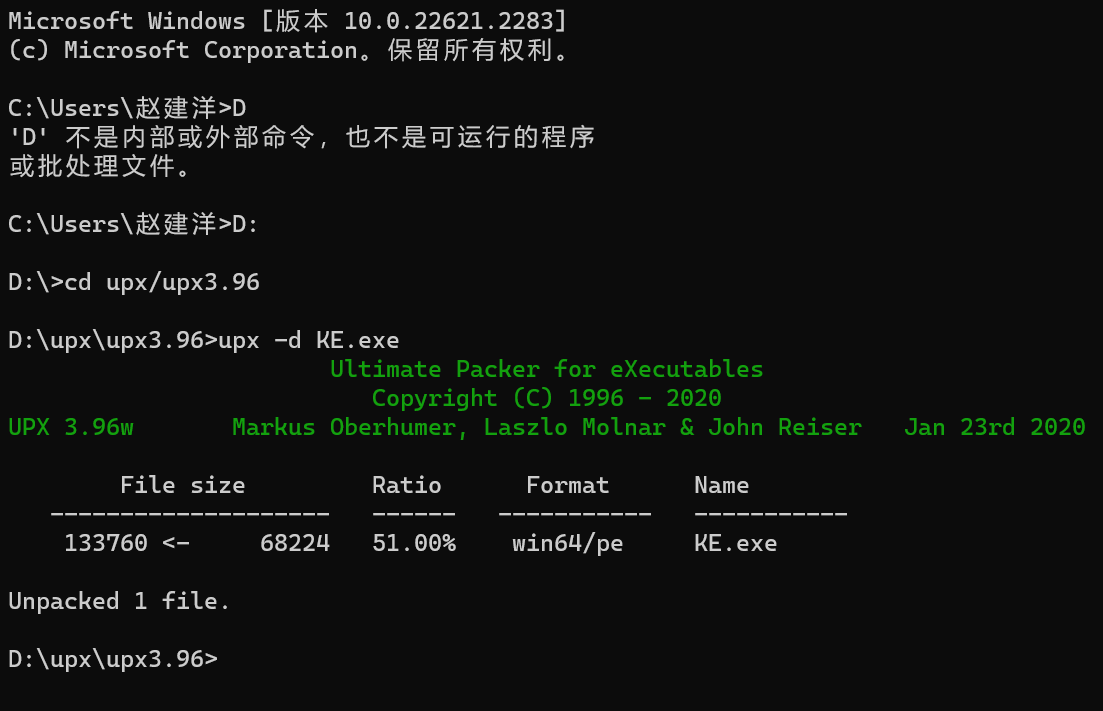
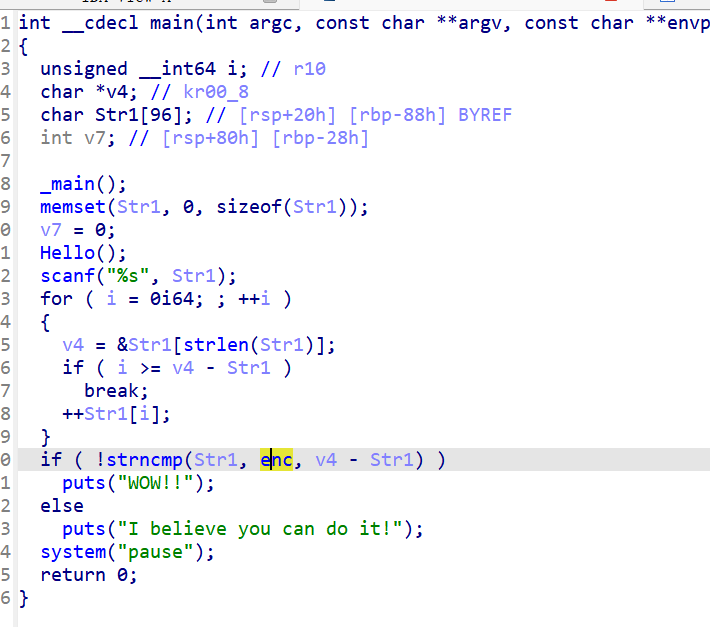
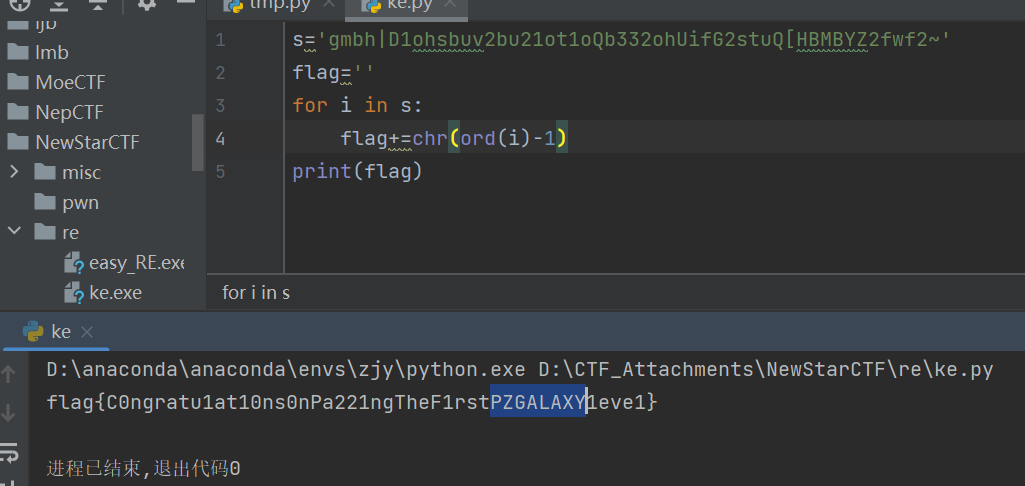
KE
脱壳
输入加1
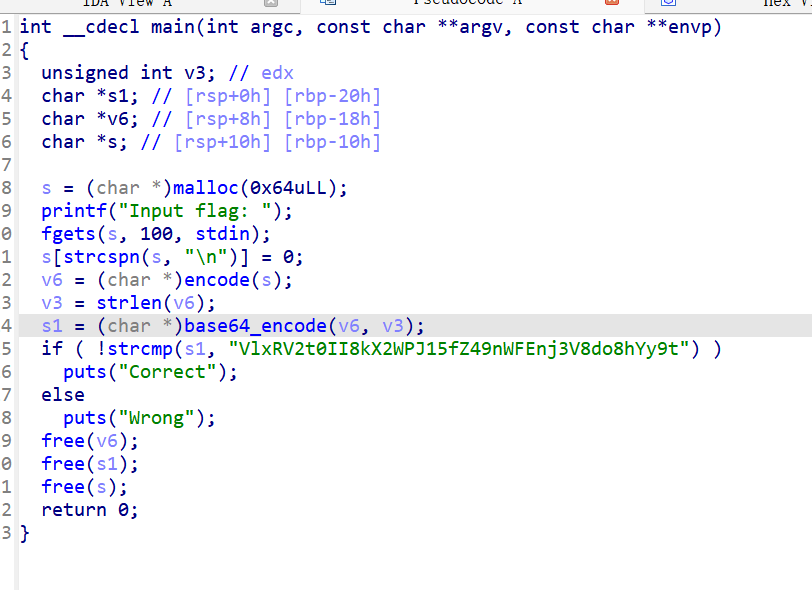
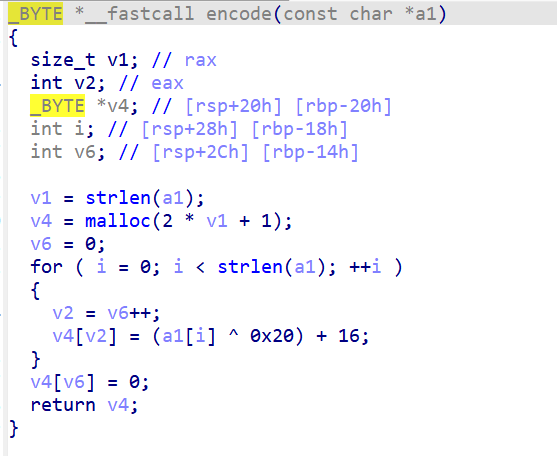
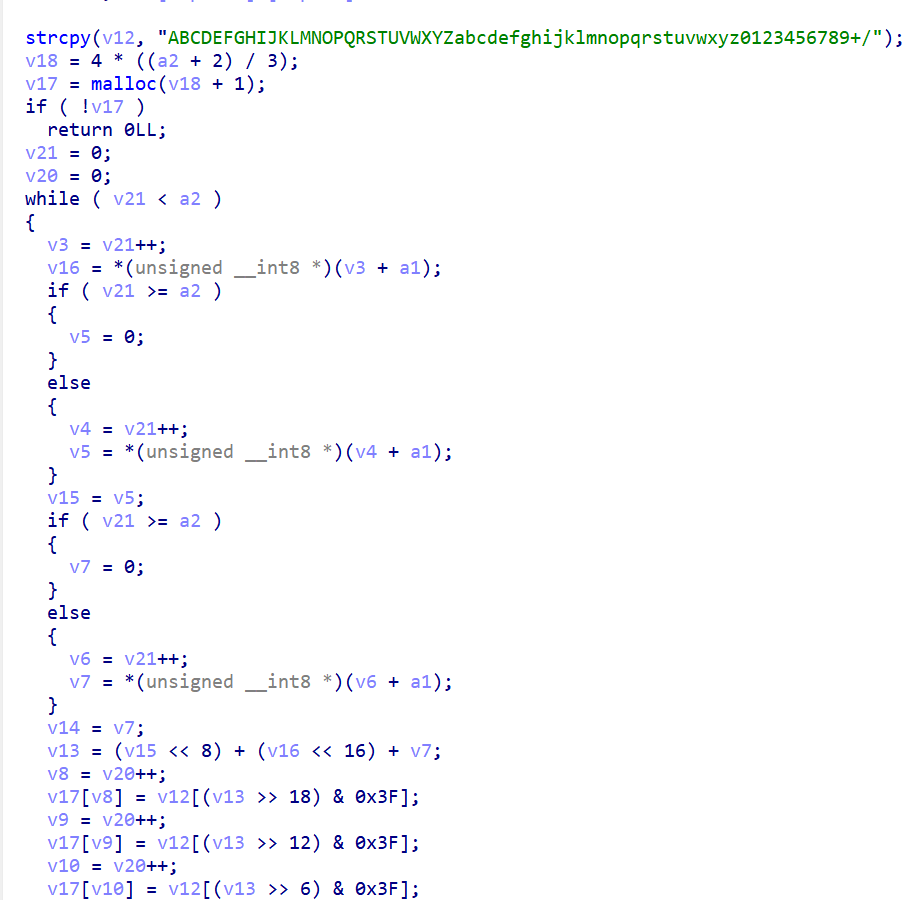
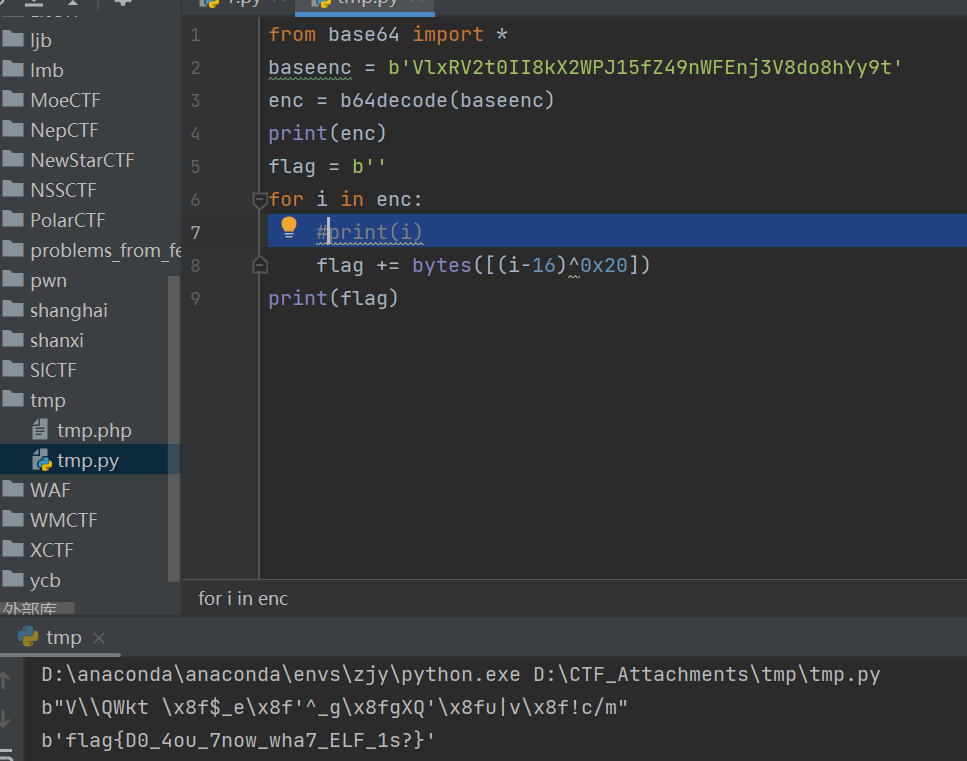
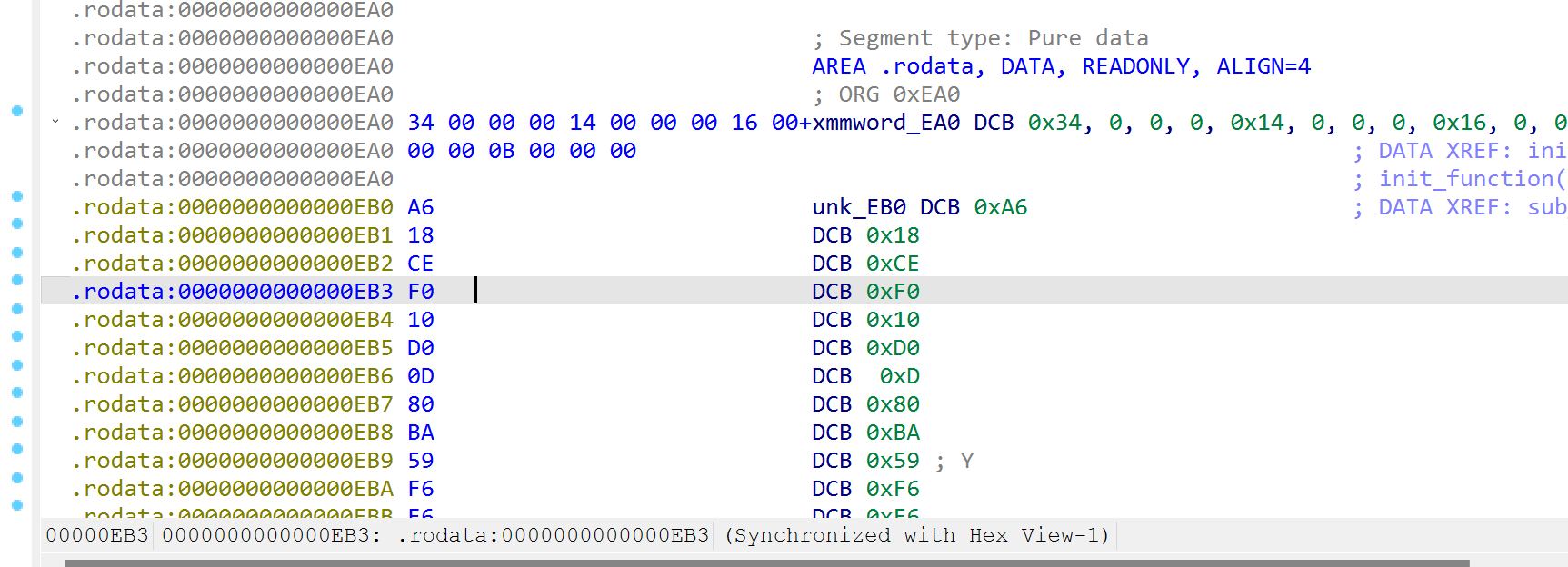
ELF
先加密,再base64
直接交发现不对
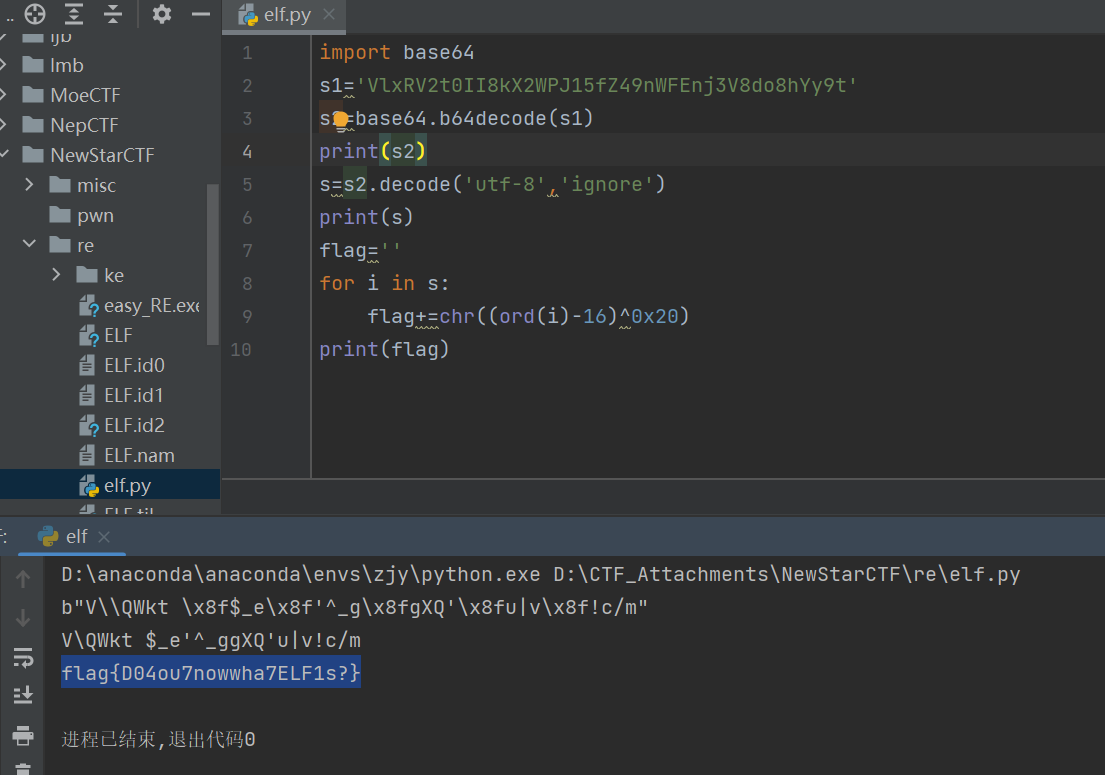
用下面这种方法把字节转字符串告诉我\x8f不能转化,于是去用python算一下
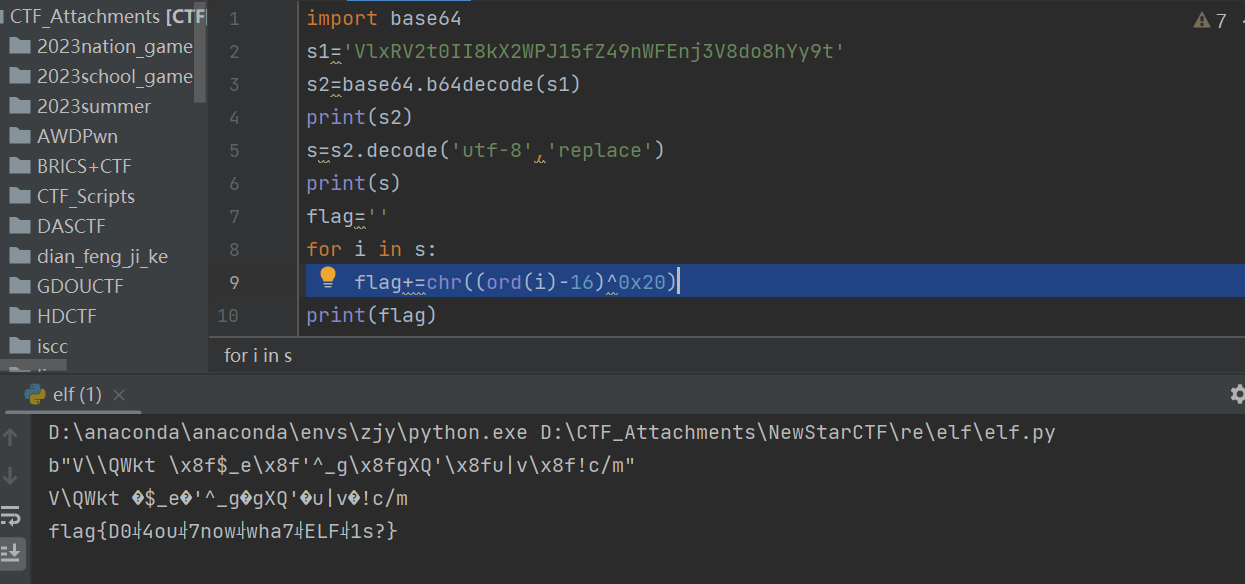
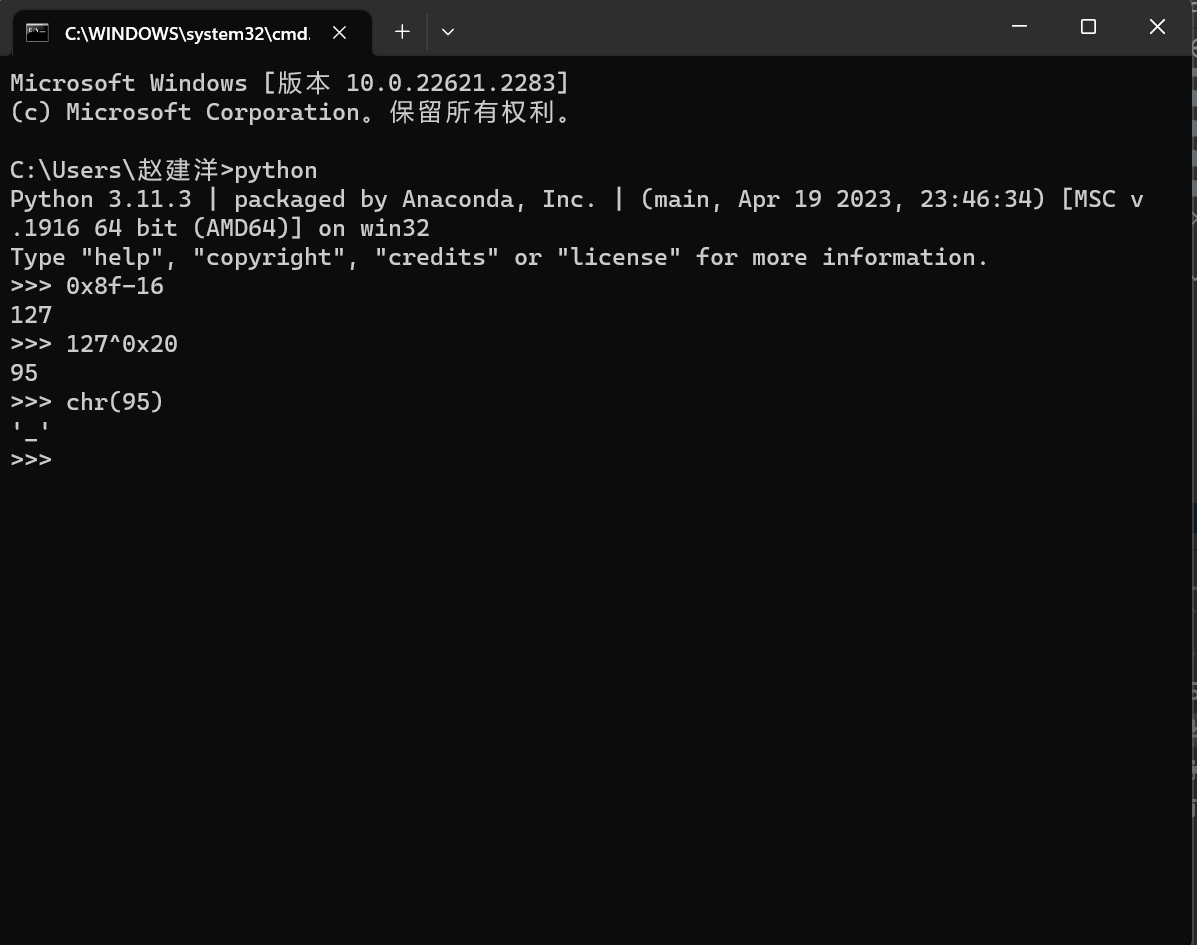
是下划线,那就在单词之间各加一下划线,且数量刚好对的上
字节类型也可以和数字进行运算
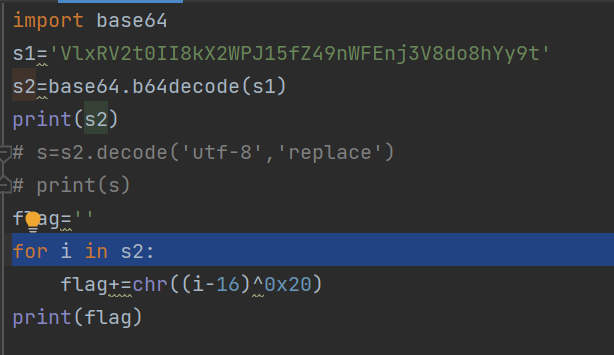
b64decode也可以解字节,最后解完得到的是字节类型,上面的s2也是如此
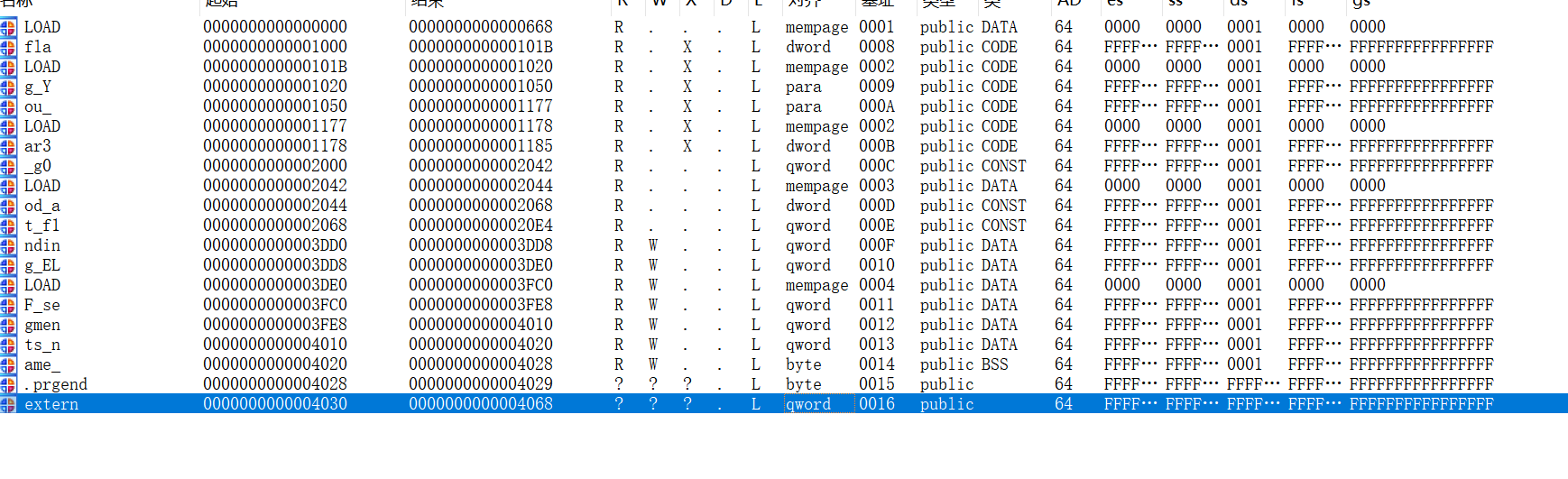
segments
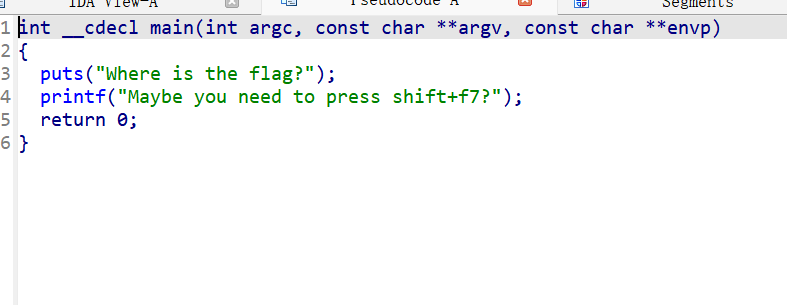
那就shift+f7
主要还是看语意吧
_flag_和name后面的_都要去掉
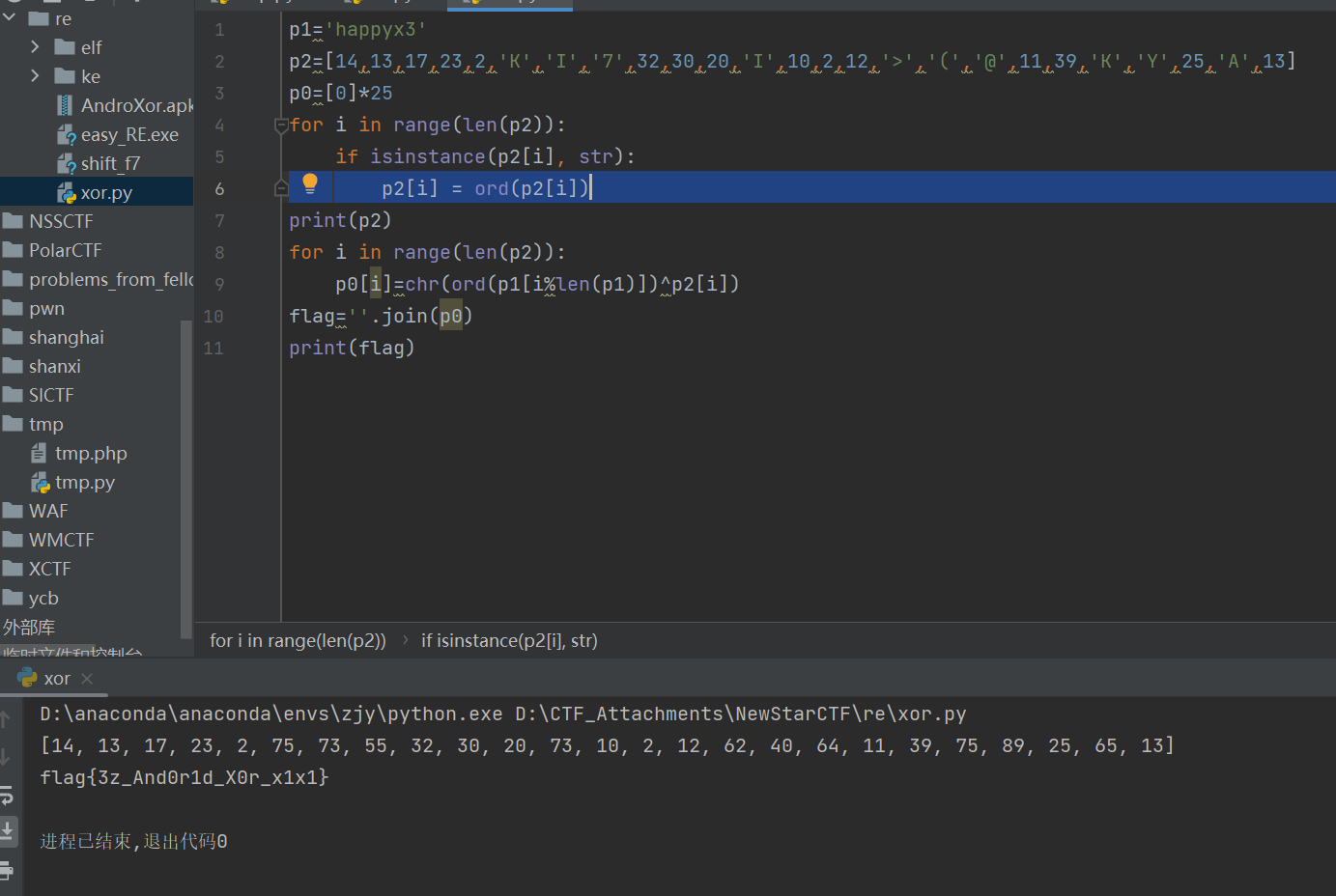
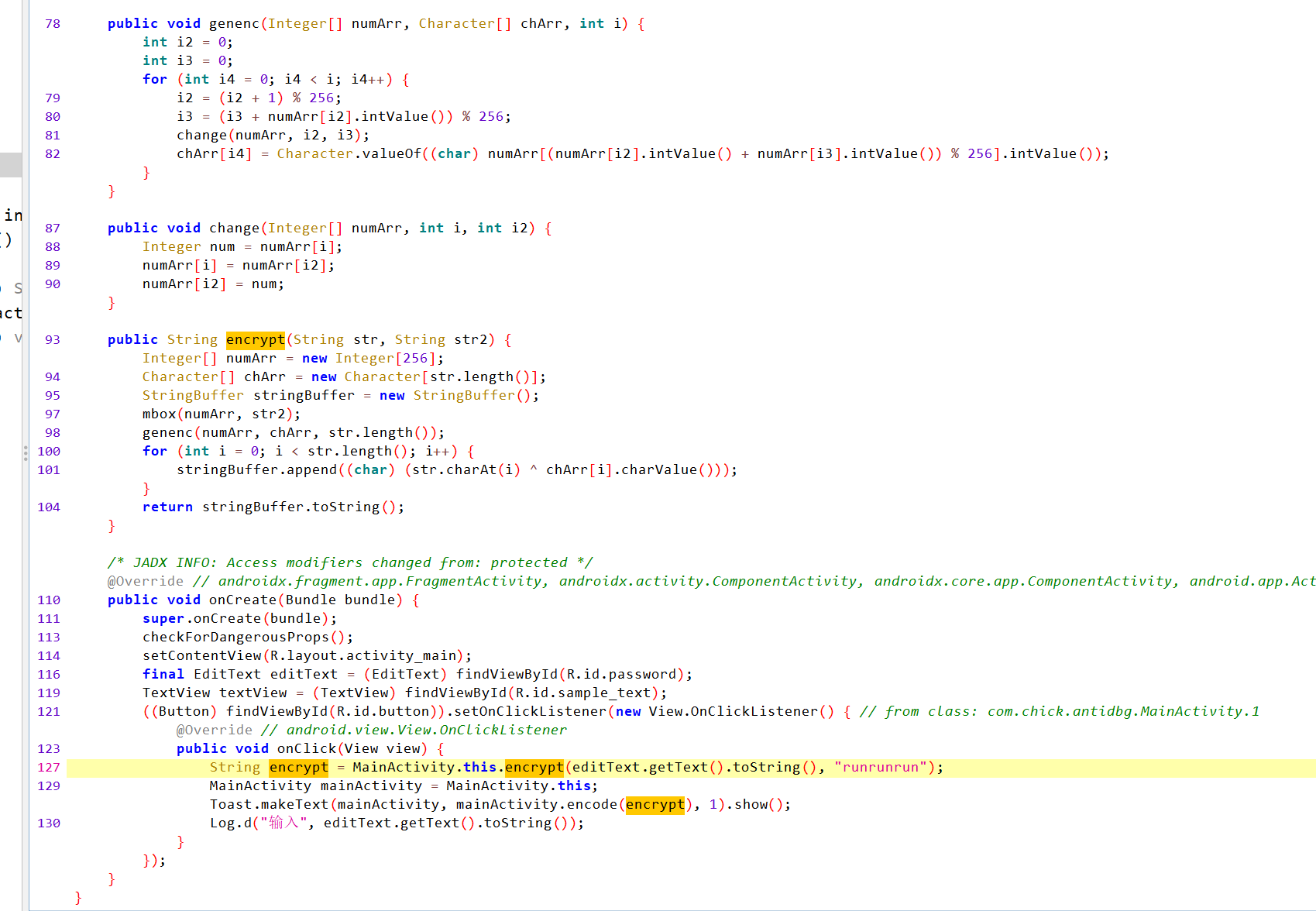
AndroXor
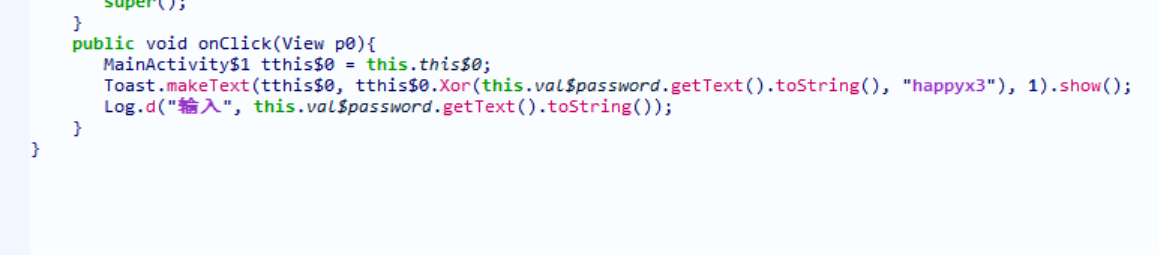
最后长度为25
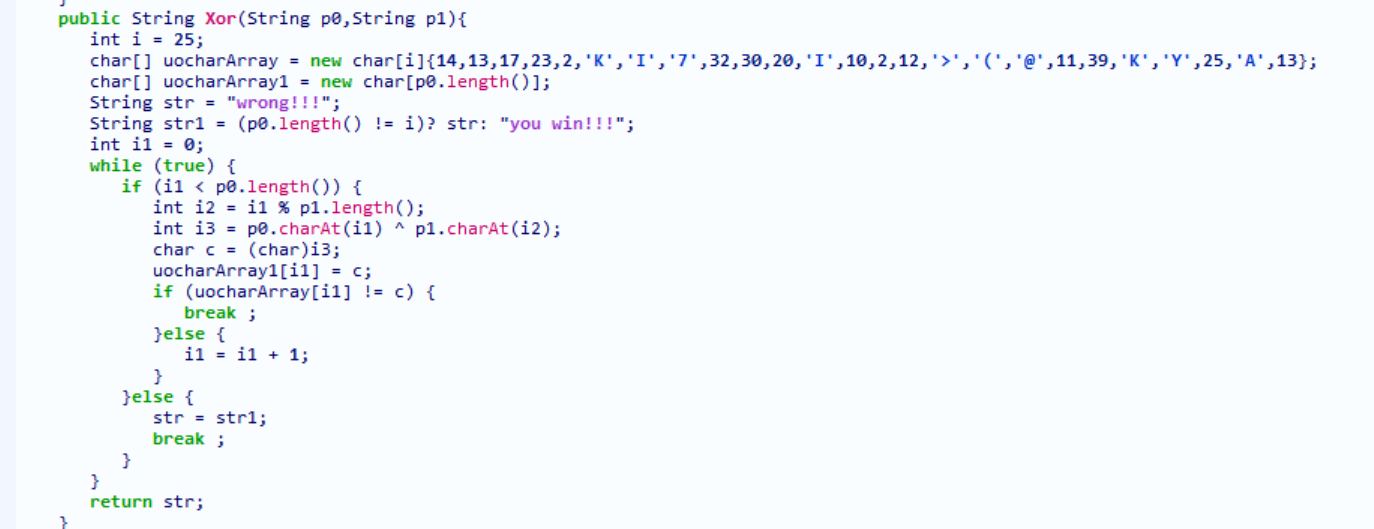
好像有点问题,把o改下划线就行
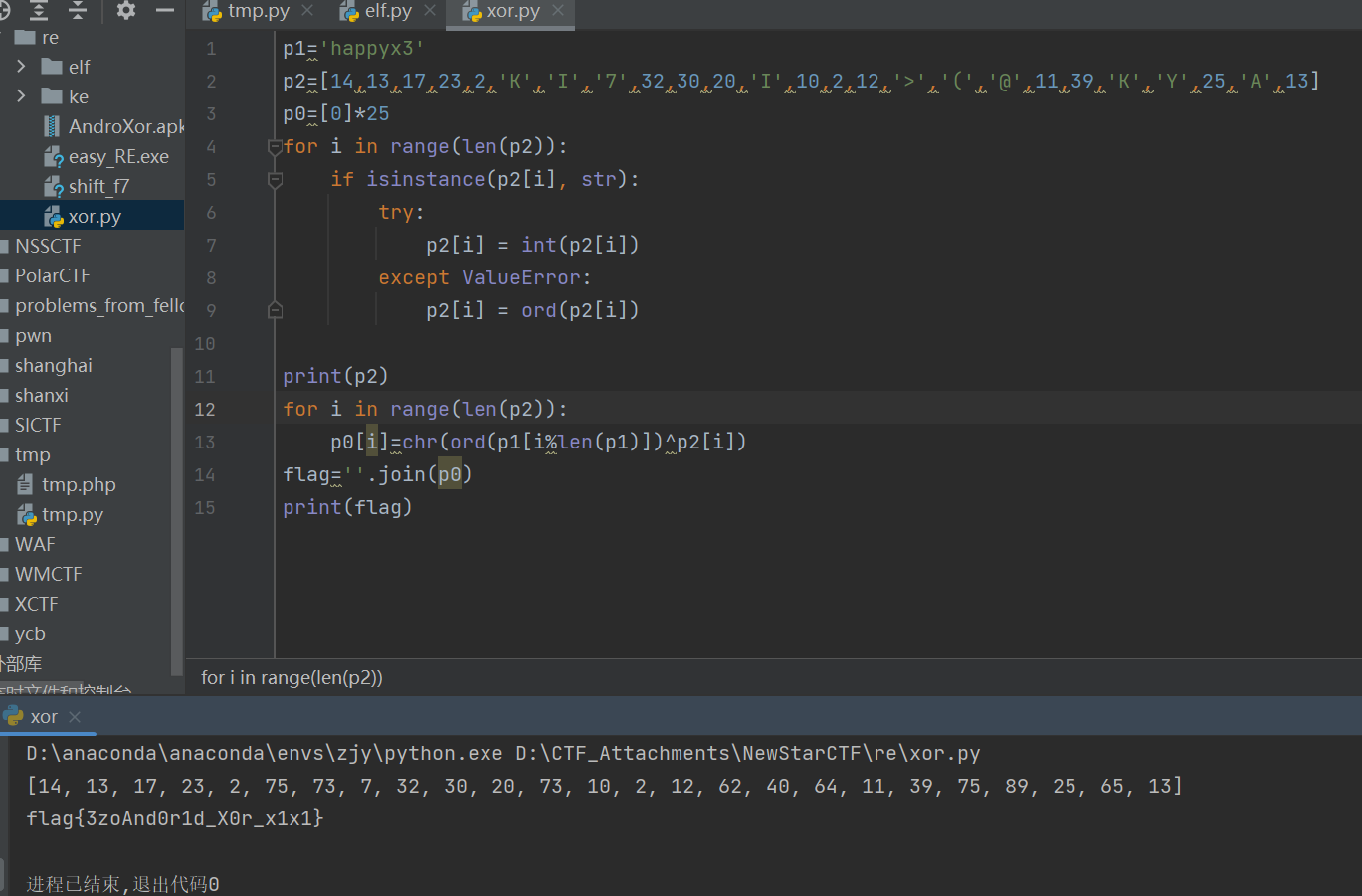
后来又想了一下,直接将ord(字符)就行,这样就对了
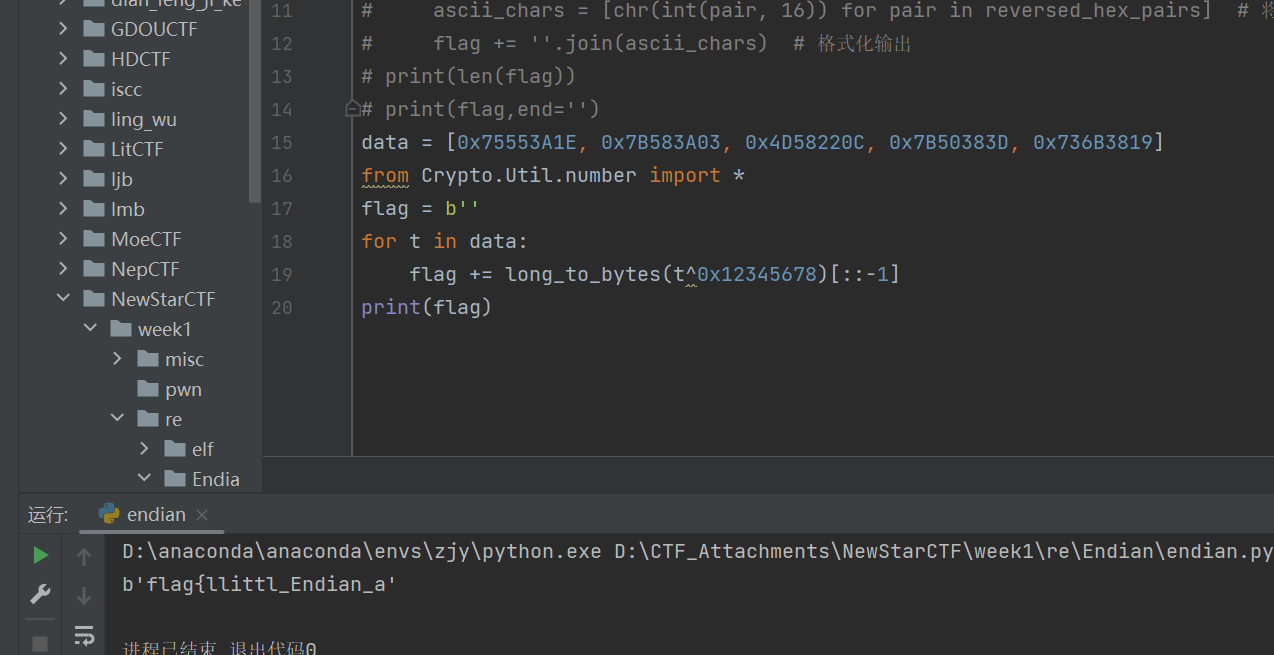
endian(段序)
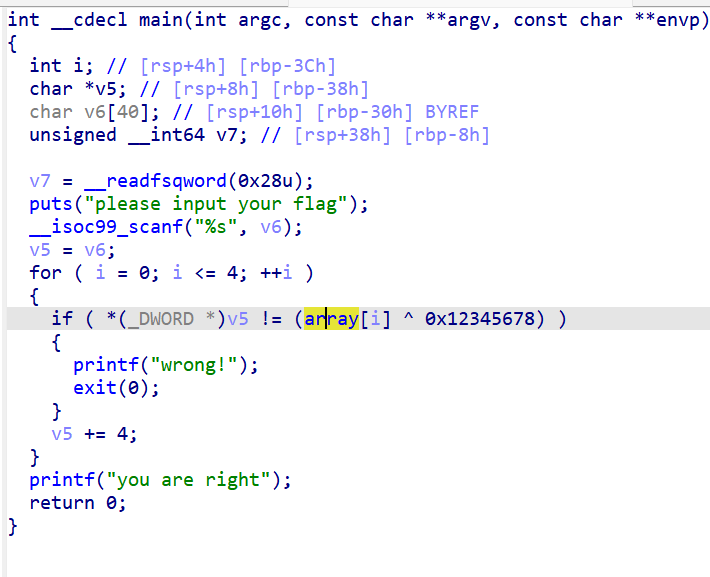
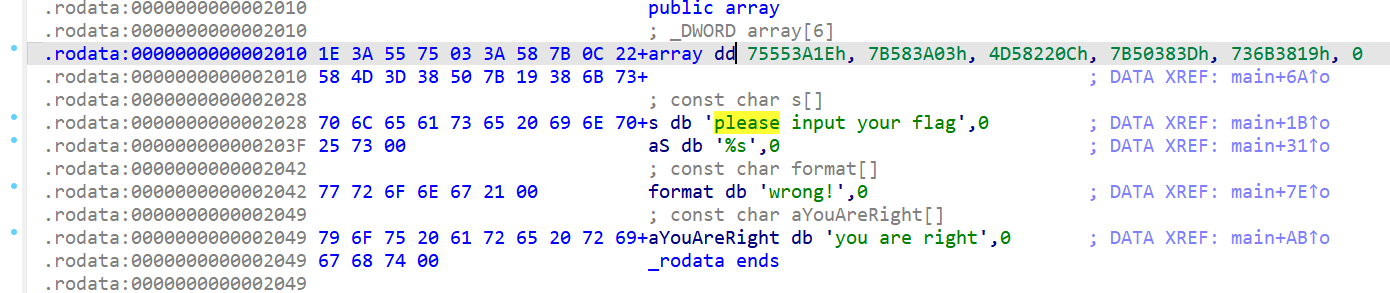
还以为简单异或随便出,结果我是小丑
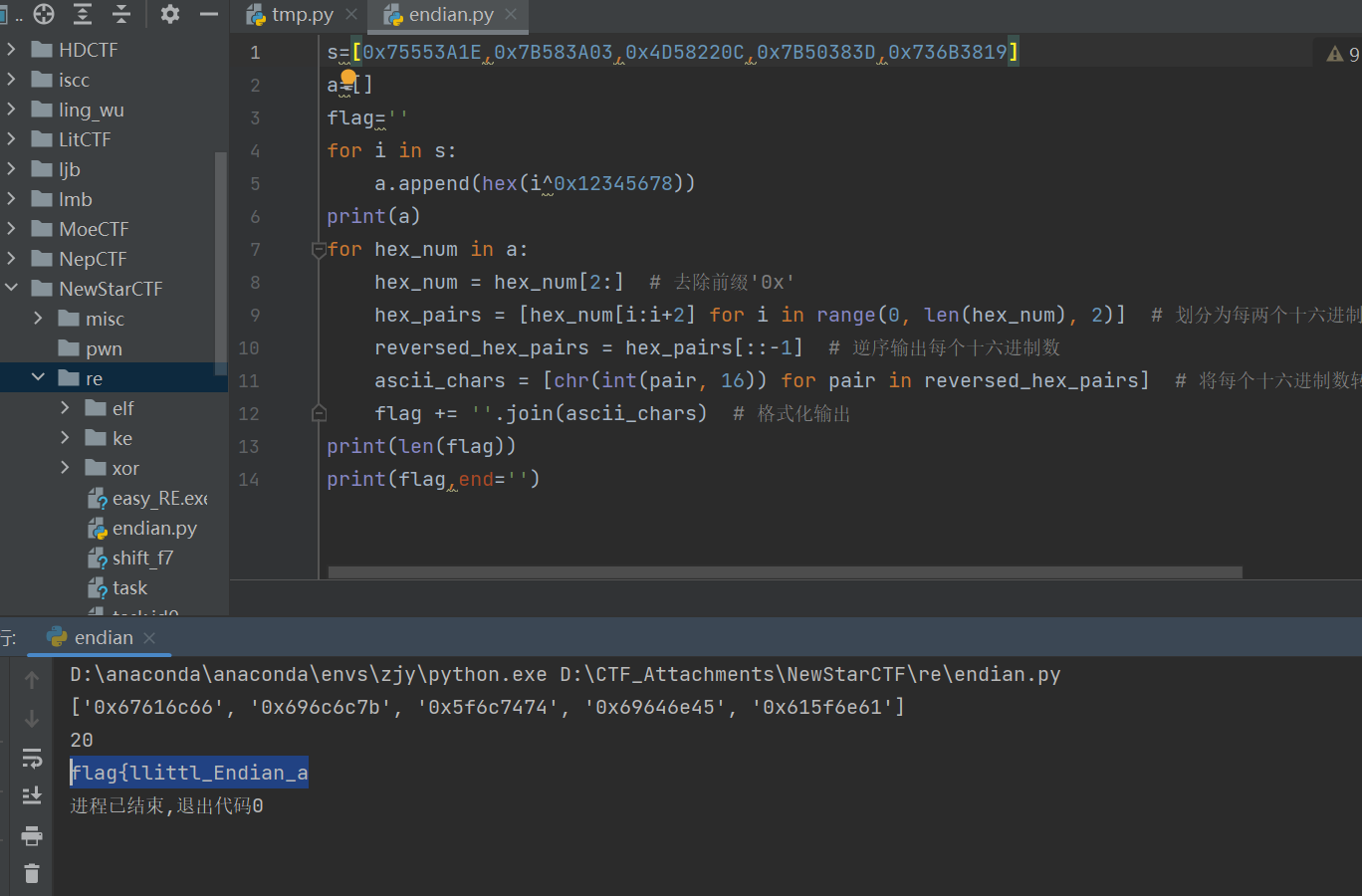
好吧加个}就对了,估计是为了格式加的,就有点莫名其妙😒😒
也可以long_to_bytes直接转
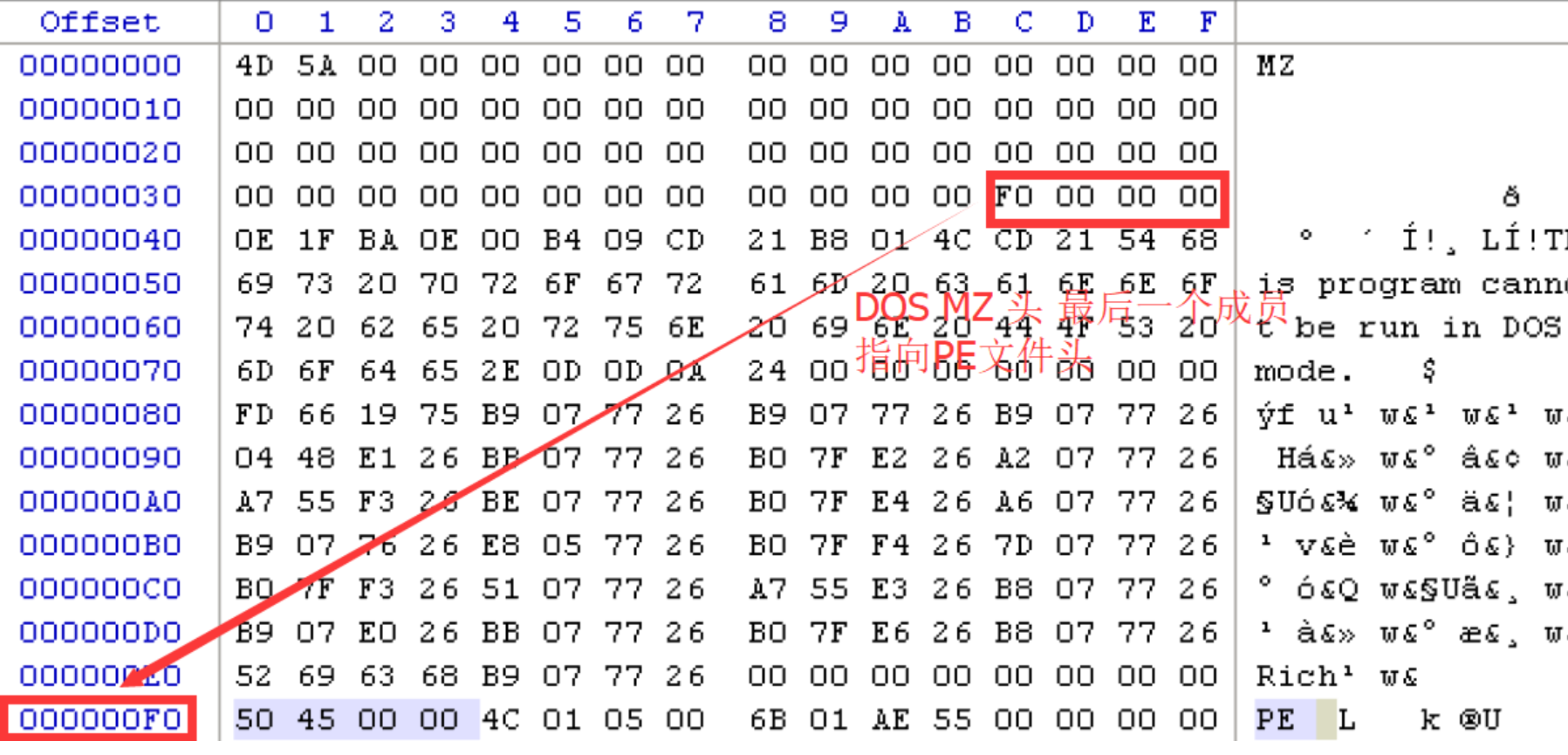
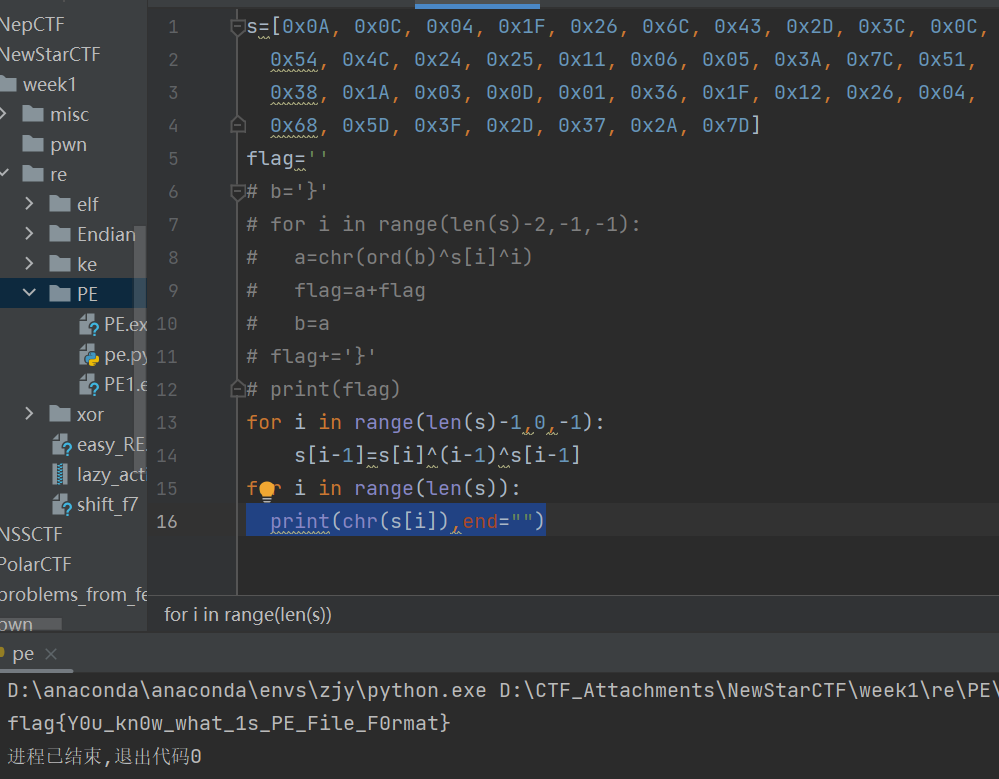
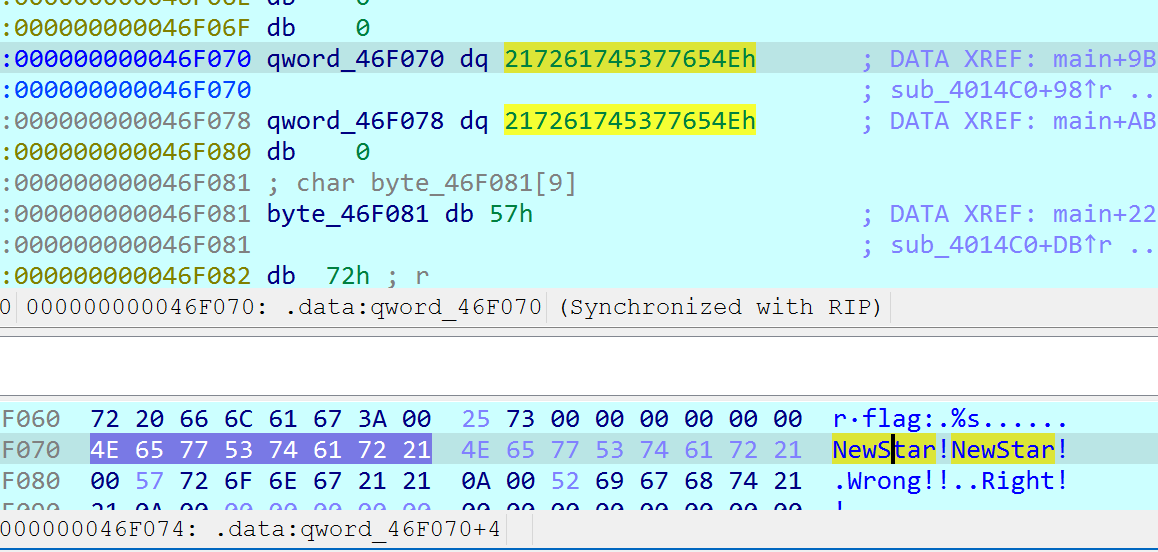
ezPE
提示修复PE文件头
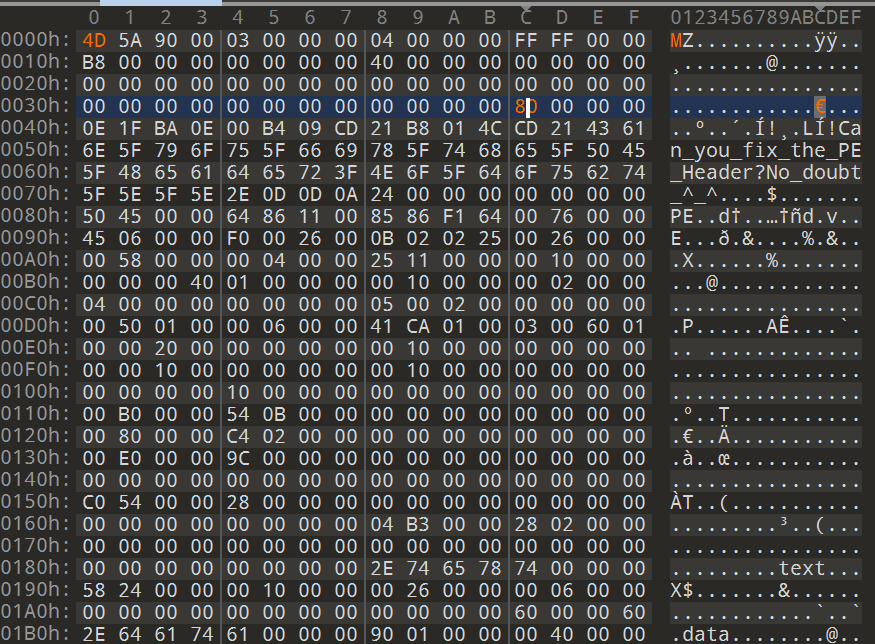
按博客的思路修,但其实没有20位的标准文件头,只要前四位(50 45 00 00)能对上就好
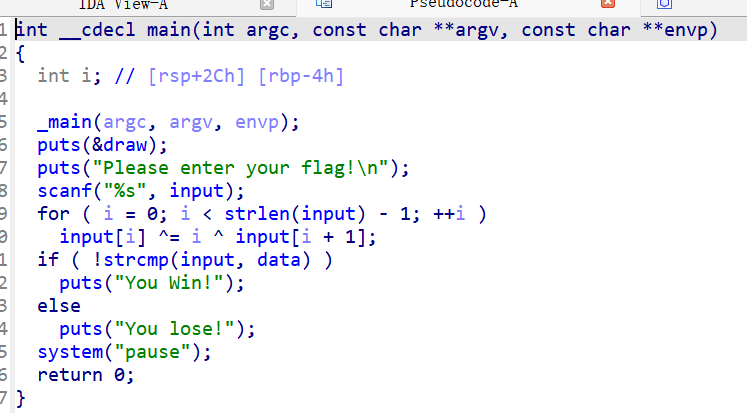
后半部分类似国赛初赛那题,异或的时候是i还是i+1举个例子就好
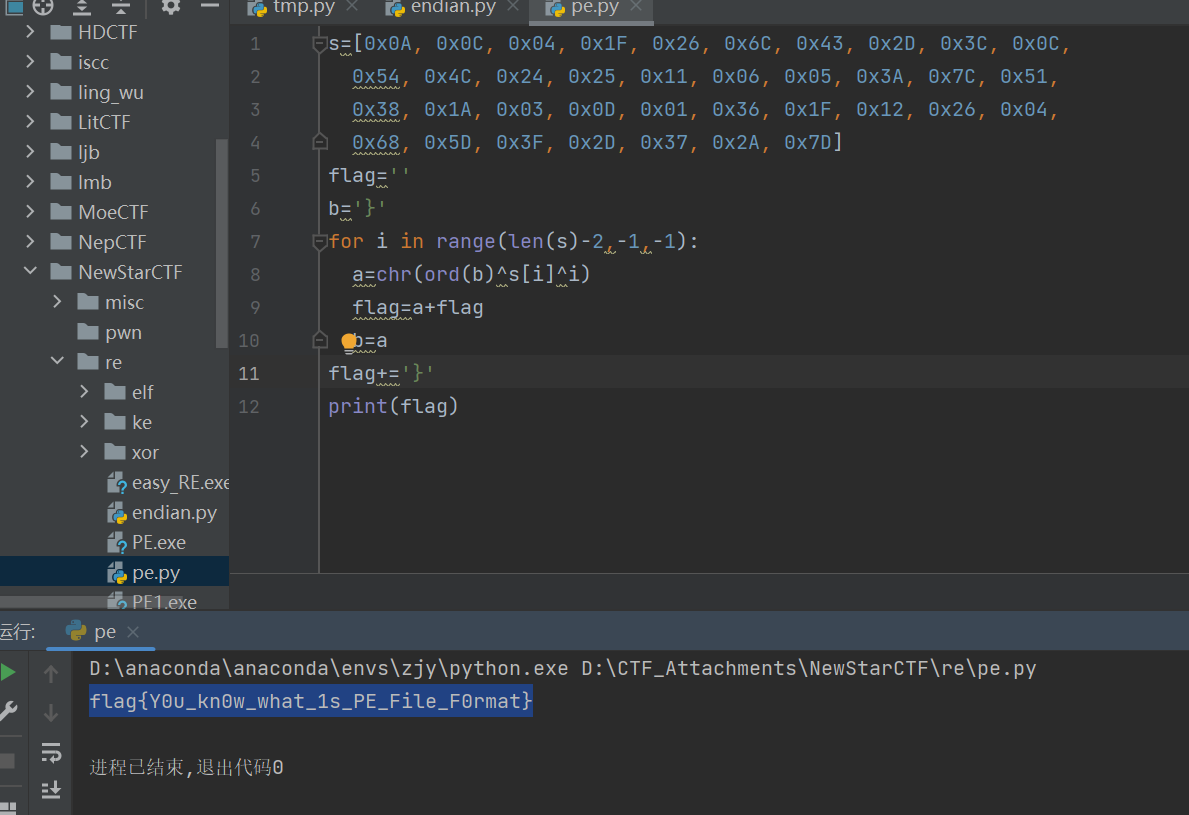
0x7D就是’}’,也可以直接反着写
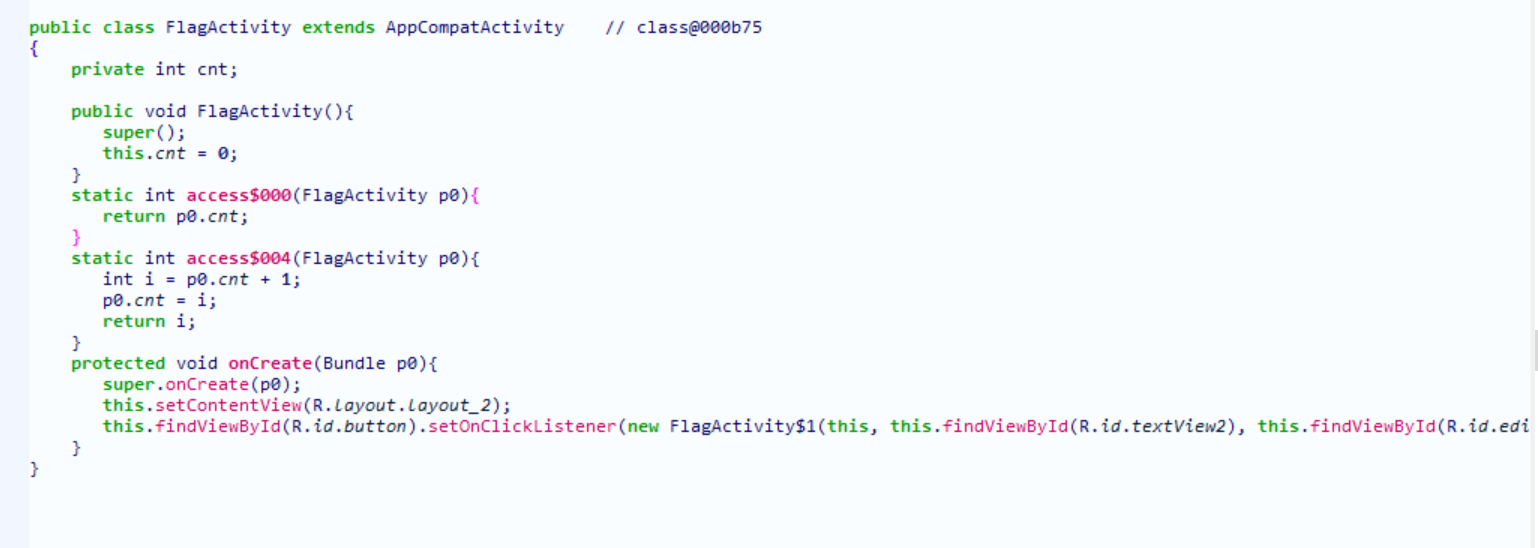
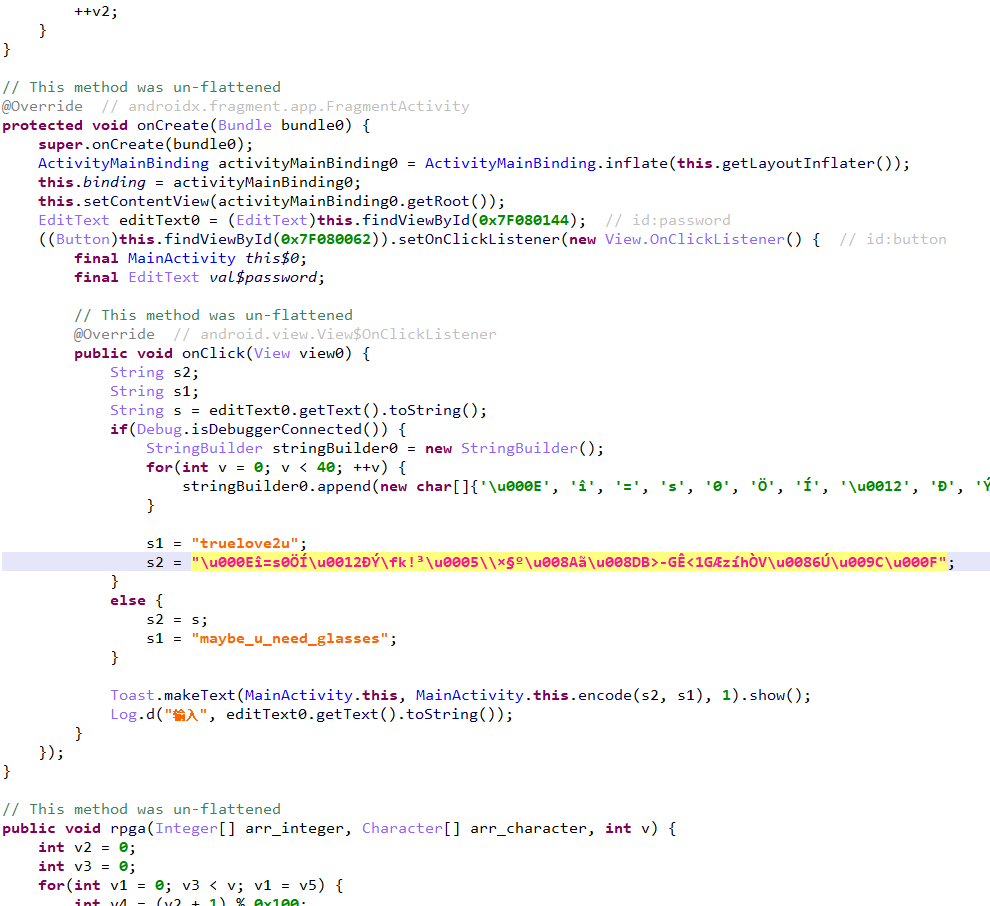
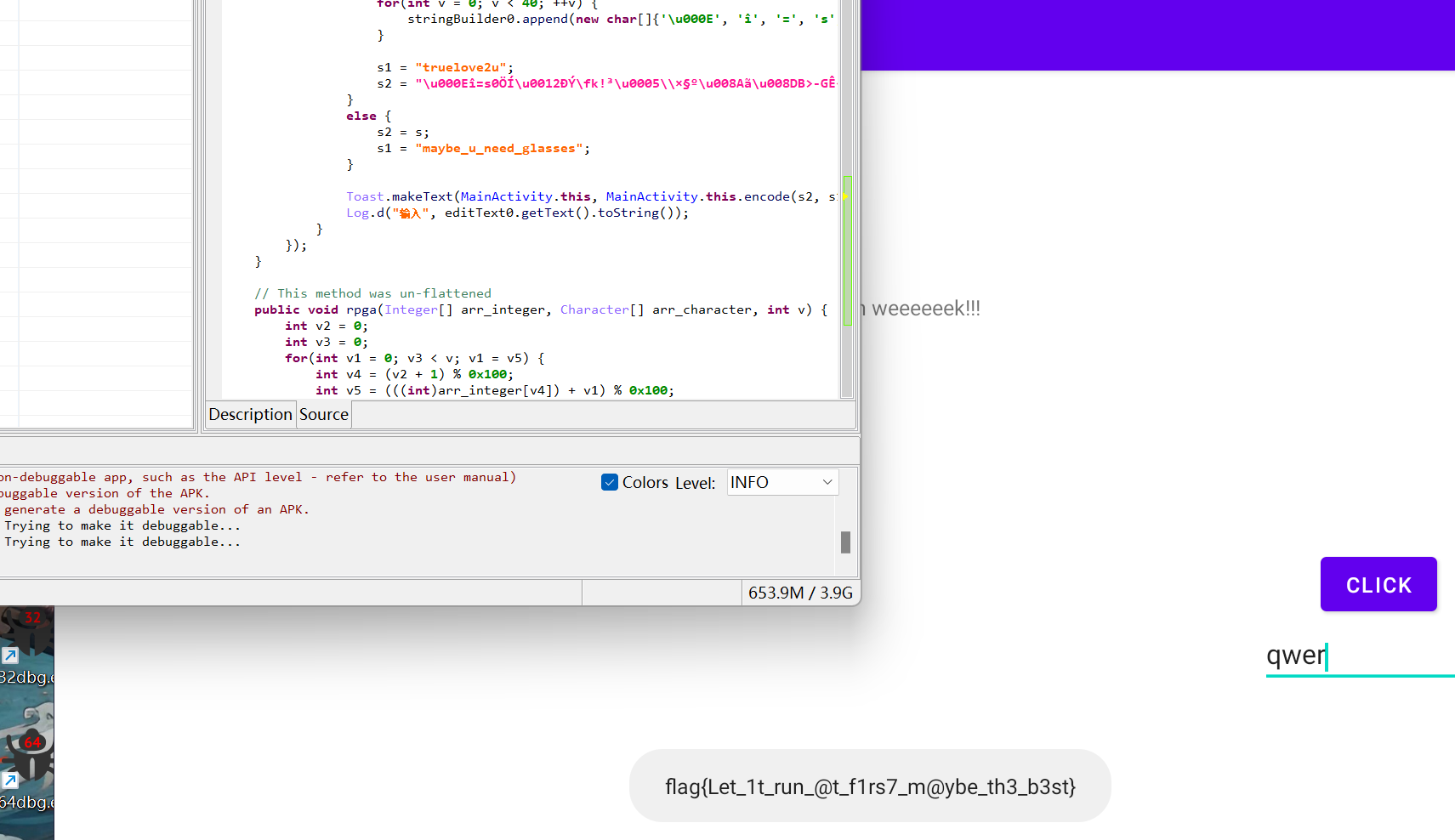
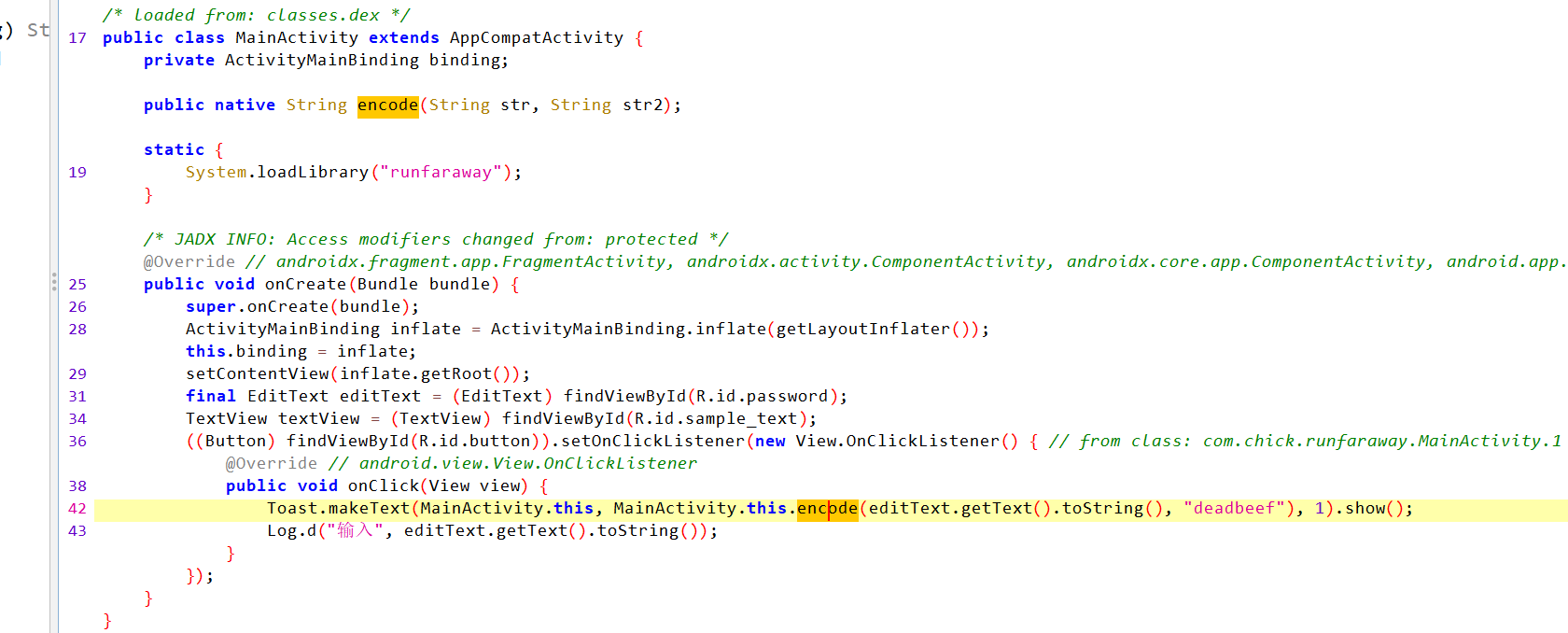
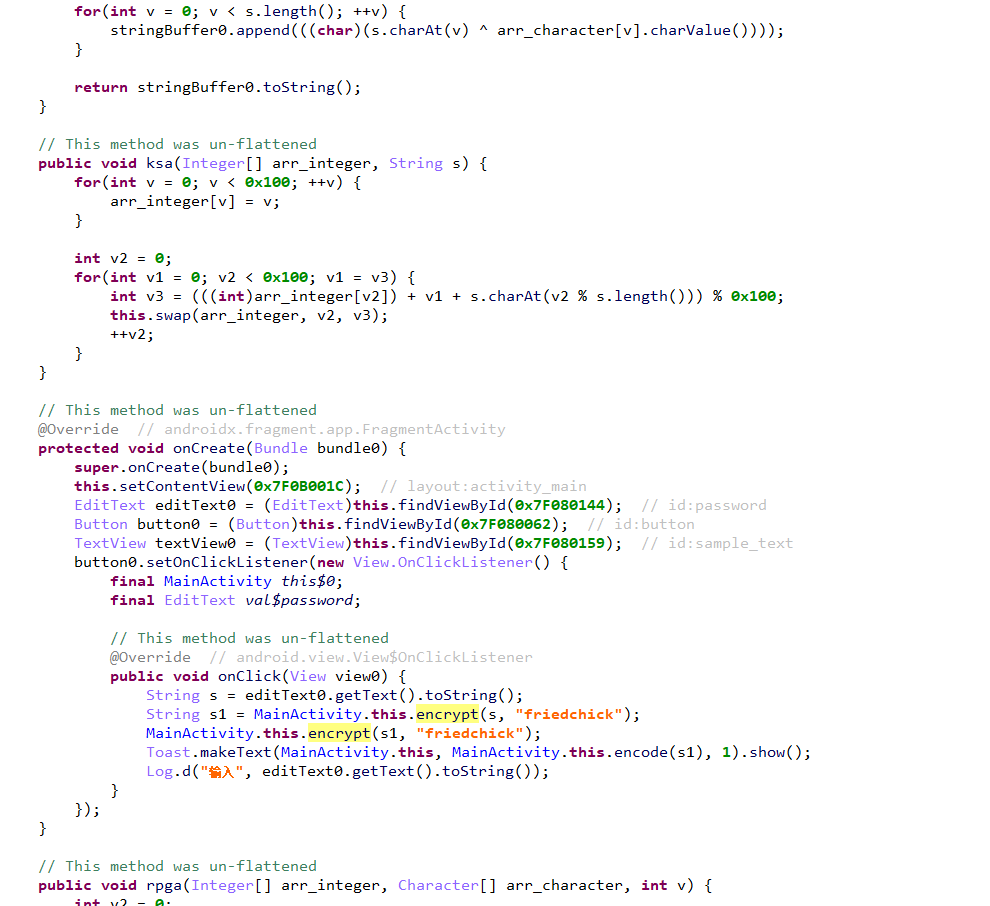
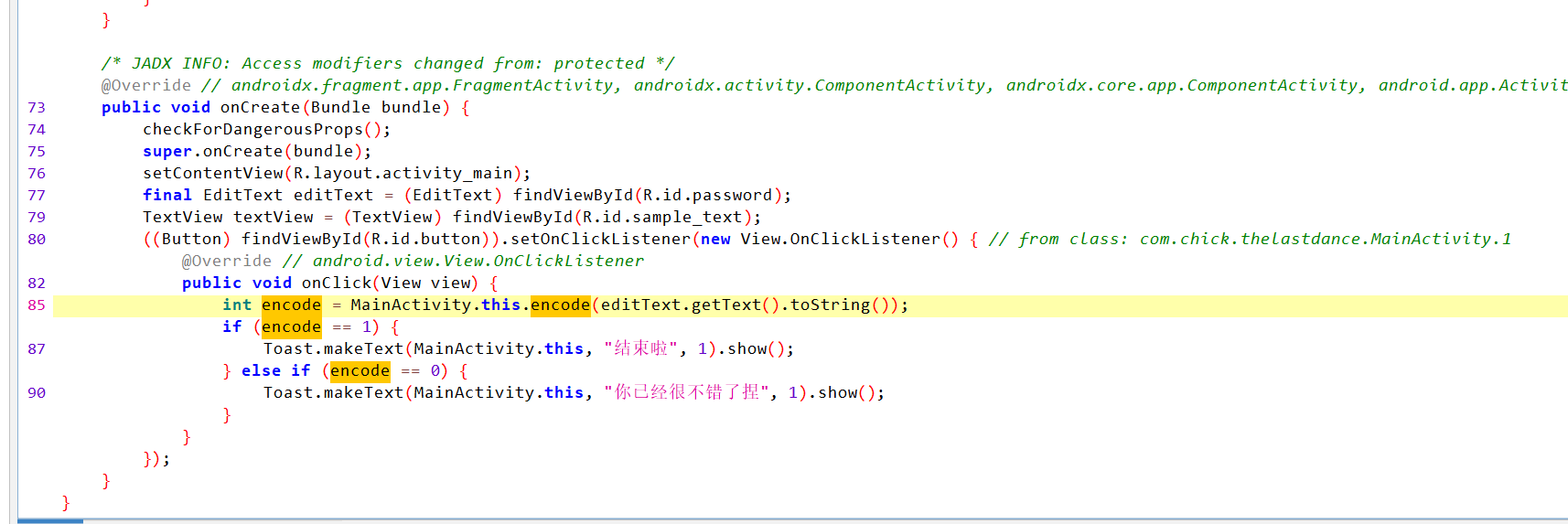
lazy_activitity
贪吃蛇
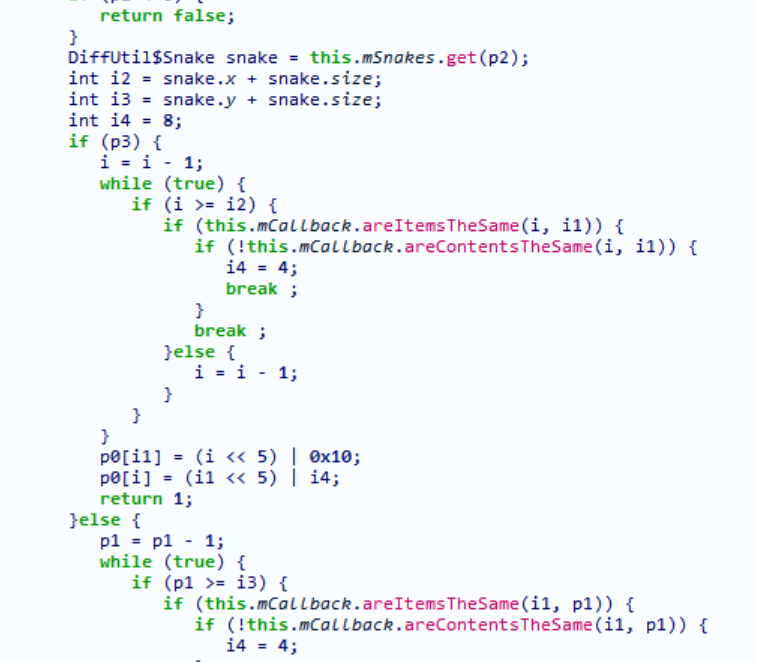
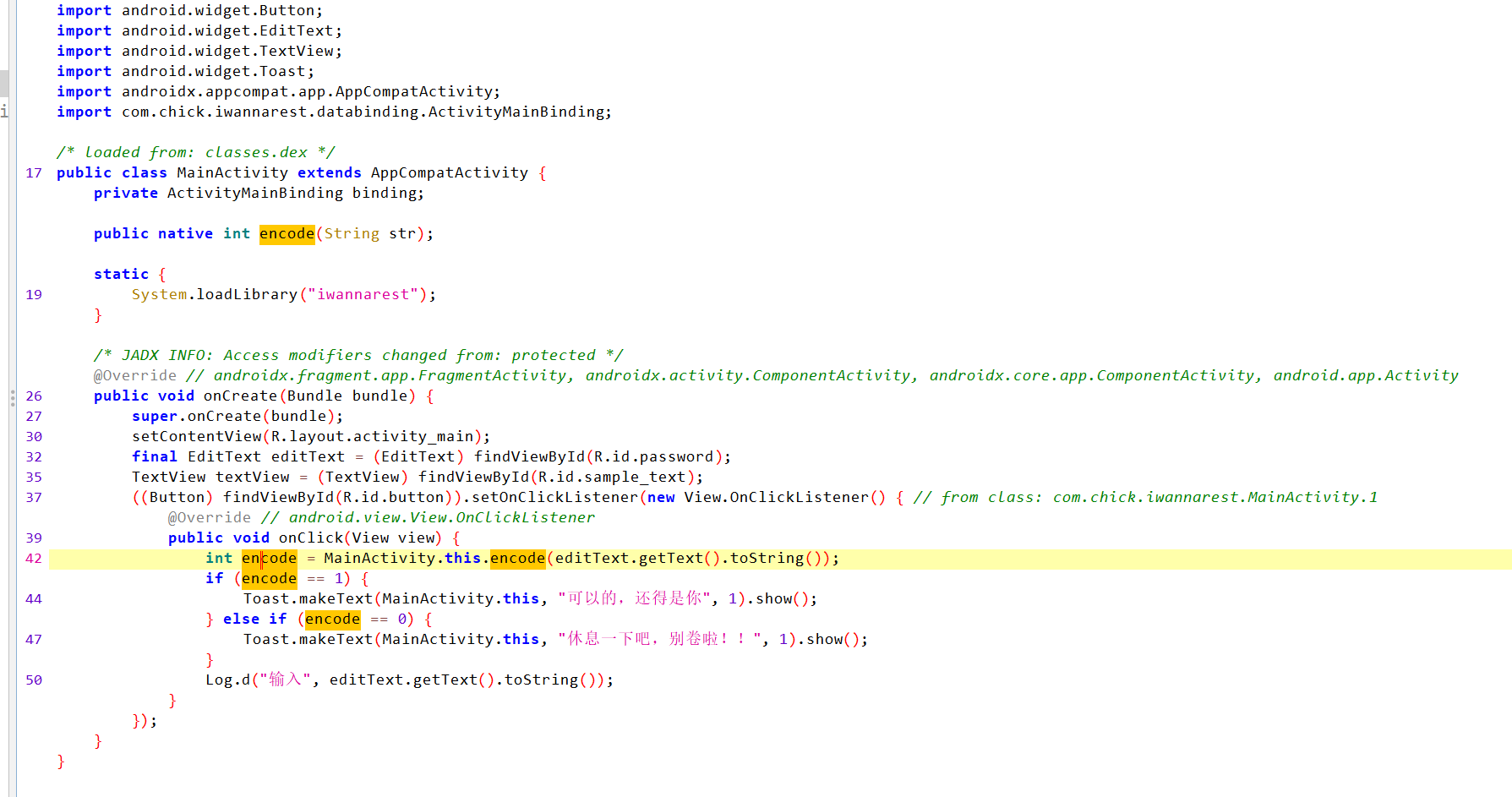
这是jadx的
直接搜关键词flag,看到有activity,和题目一样,比较关键
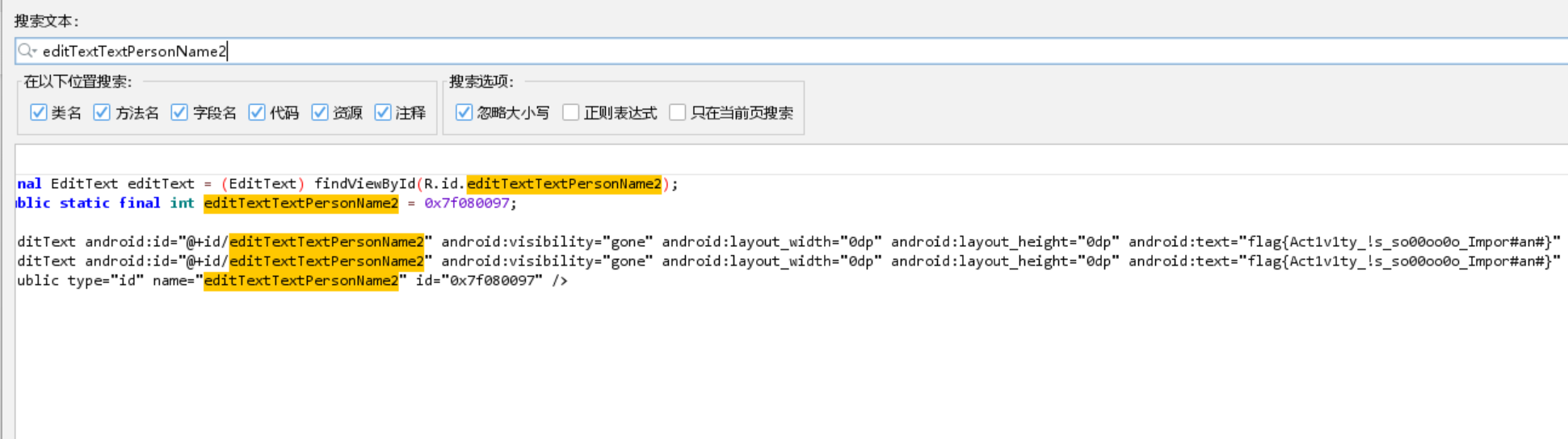
点击10000次可以getText(重复性的动作一般都是最后得到flag),找到flag的载体是editText,它在前面加载了editTextTextPersonName2这个资源,R表示资源
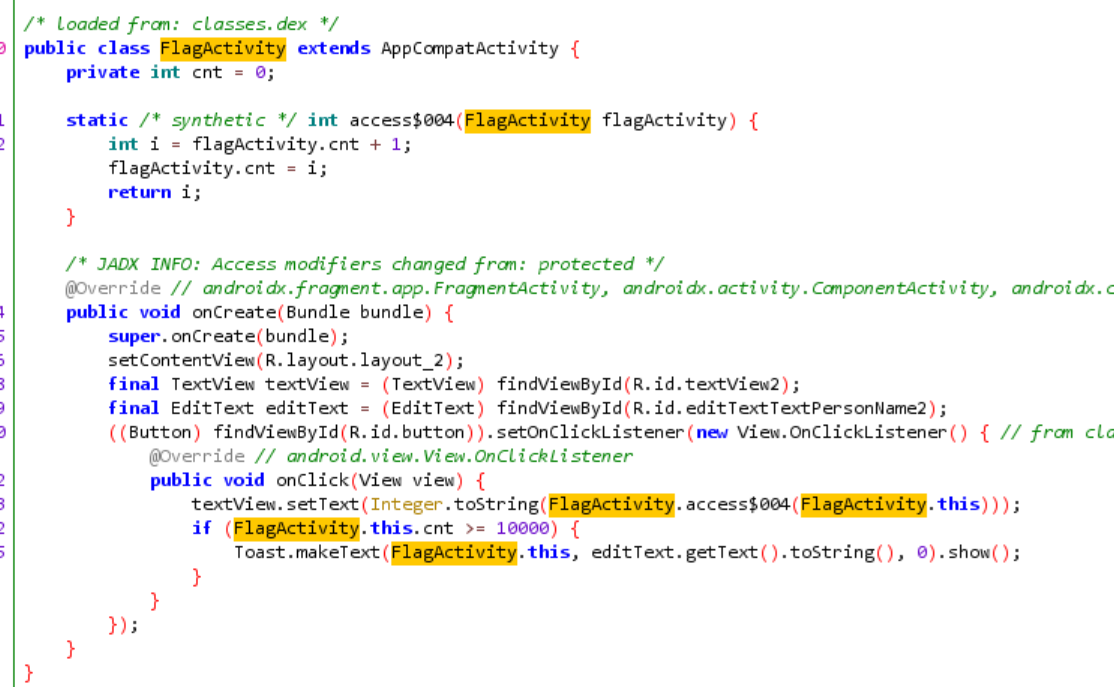
直接去搜资源就能找到
GDA的反编译,效果还是有差别
Pwn
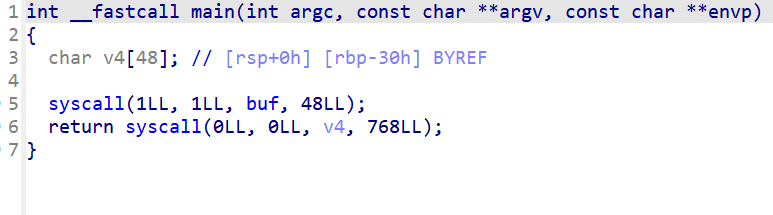
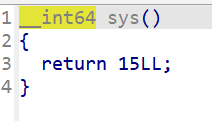
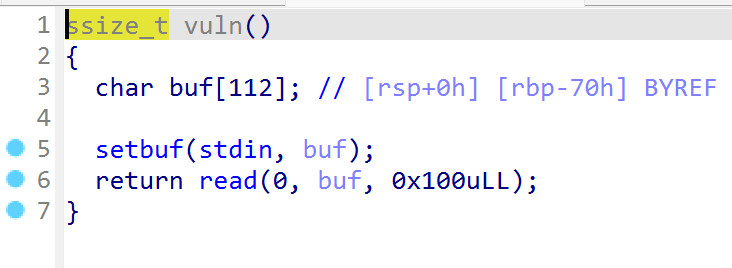
ezshellcode
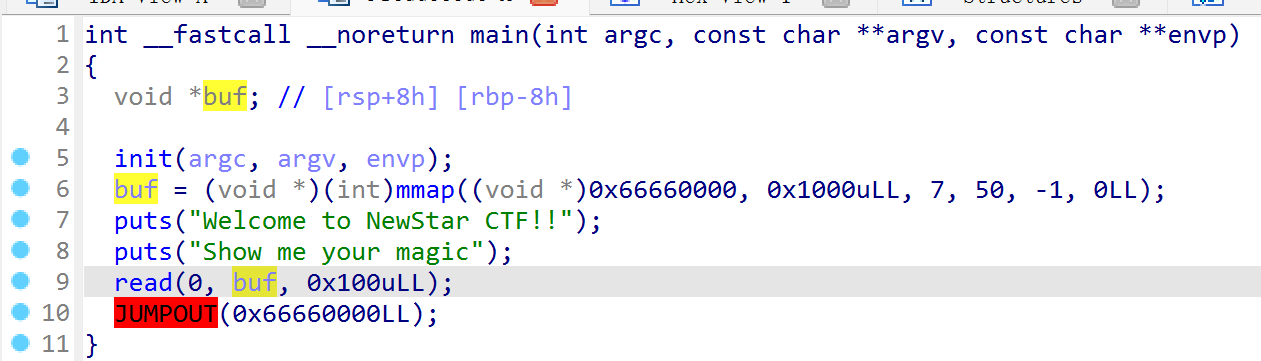
会自动跳转,直接写shellcode
1 | |
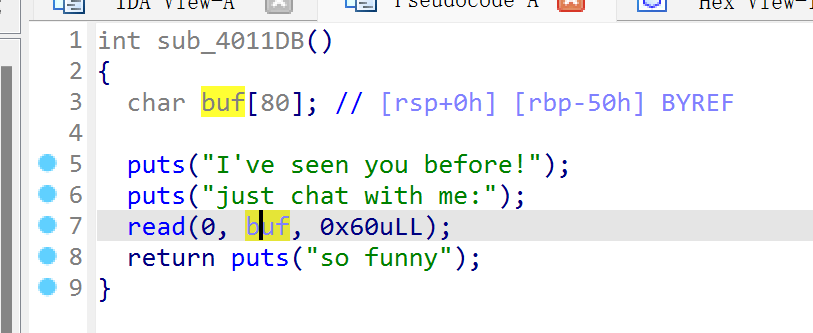
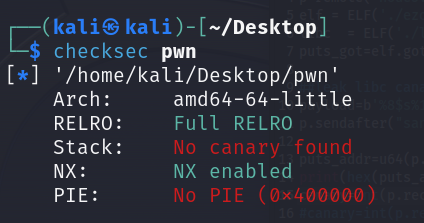
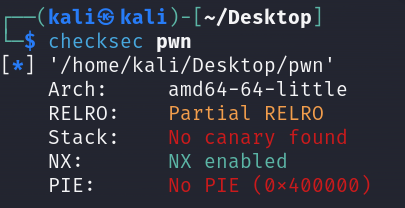
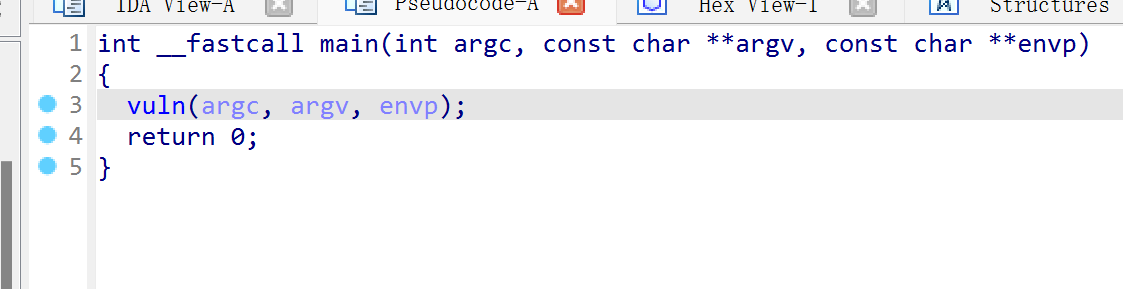
pleee
没法泄露,溢出的一字节直接修改低字节为system
1 | |
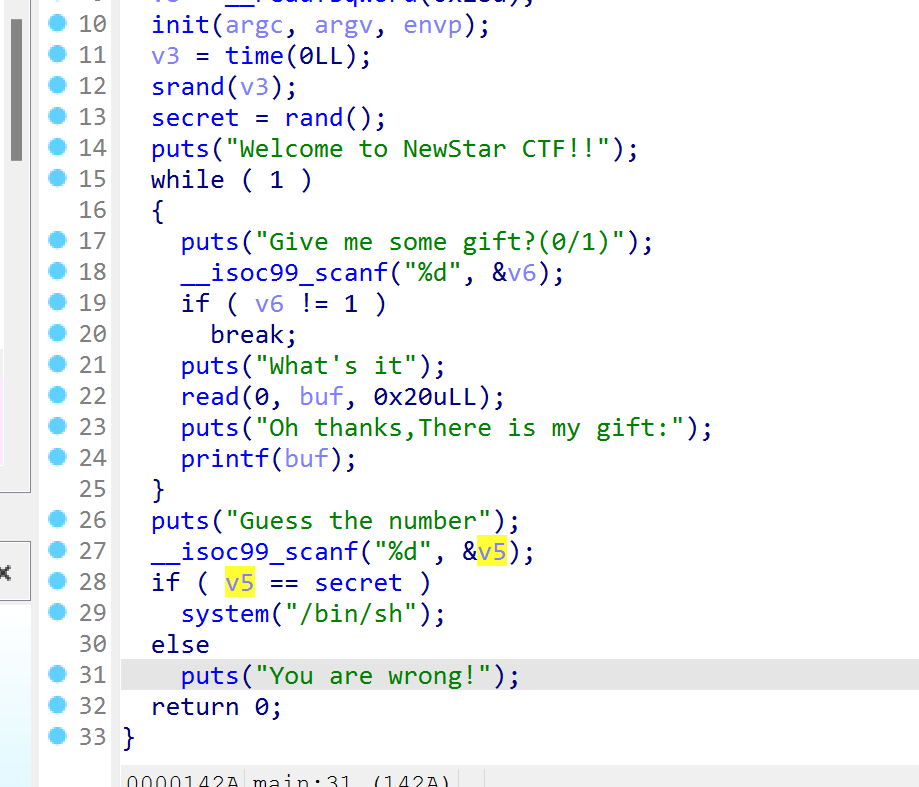
Random
期望参数为$0
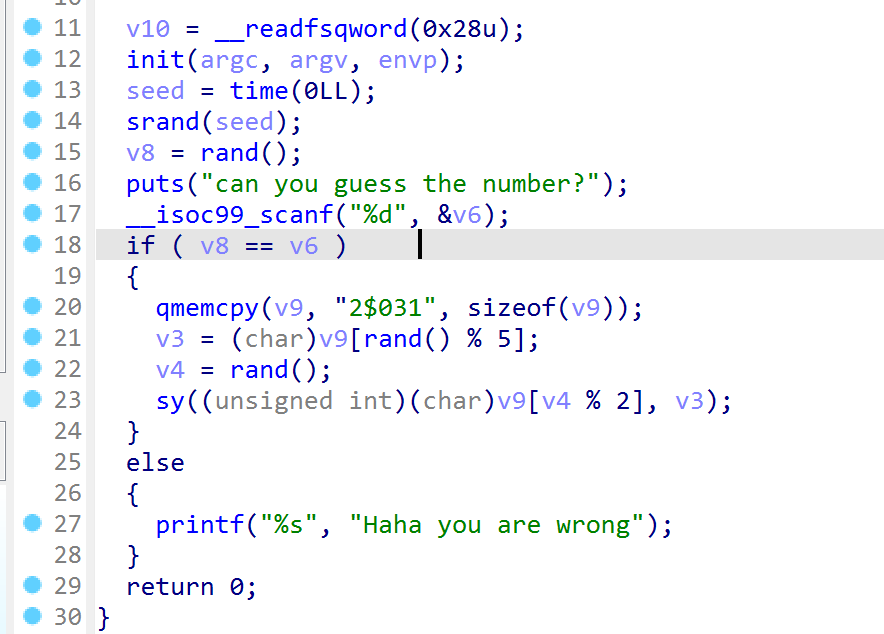
调用libc的srand函数,发送随机数多试几次就行
1 | |
Week2
Re
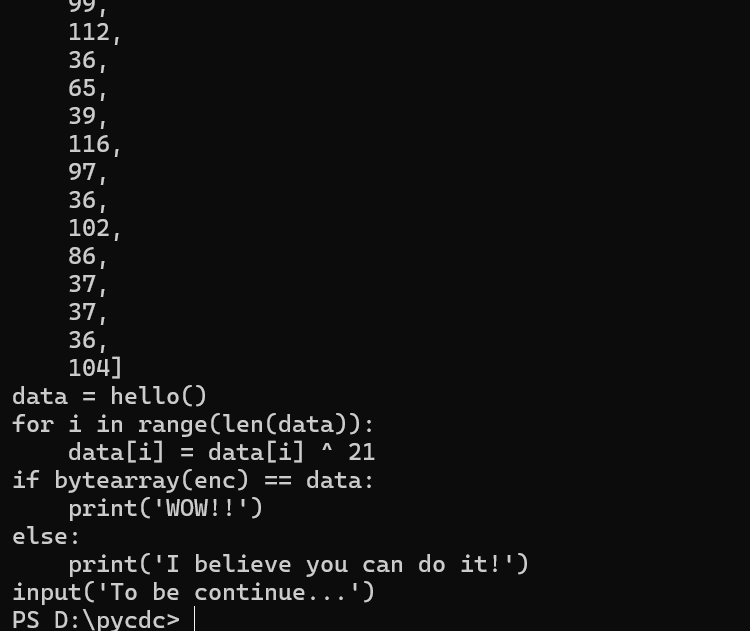
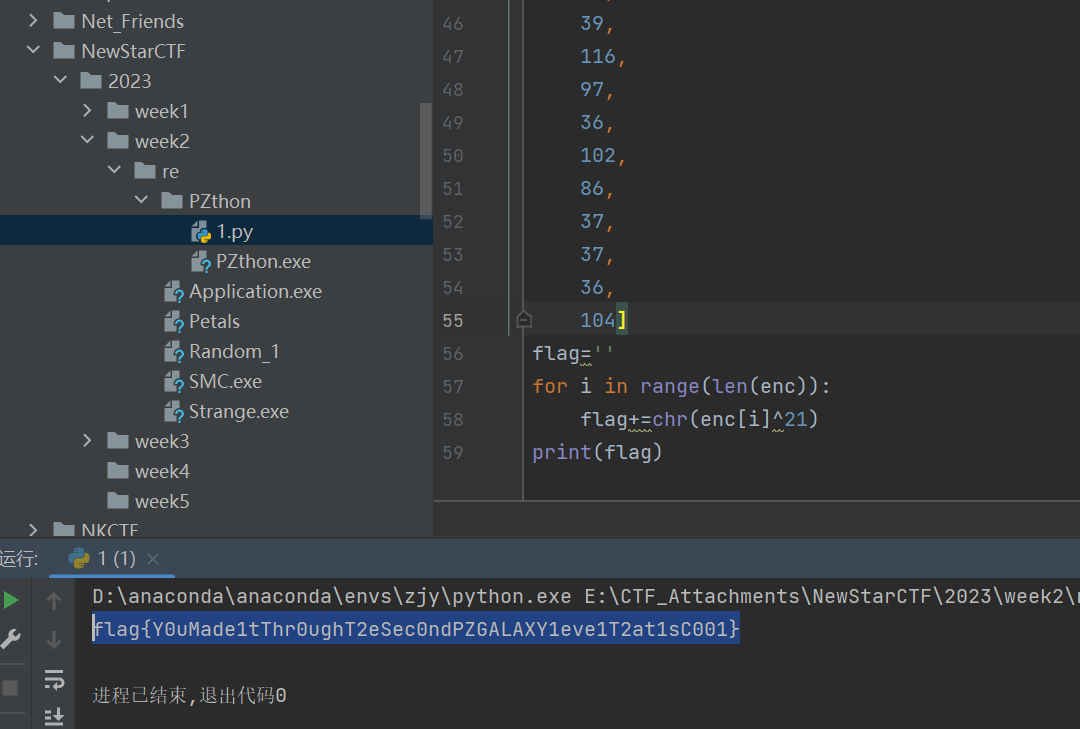
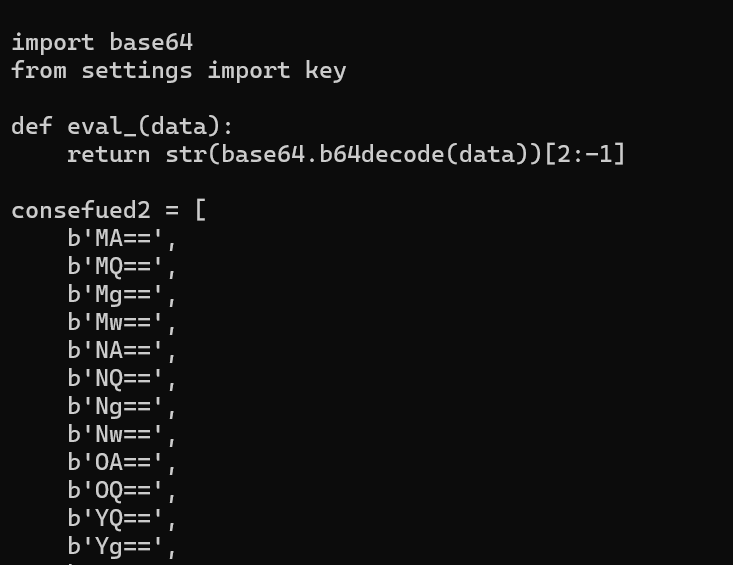
PZthon
常规题,pycdc得到源码后直接异或21
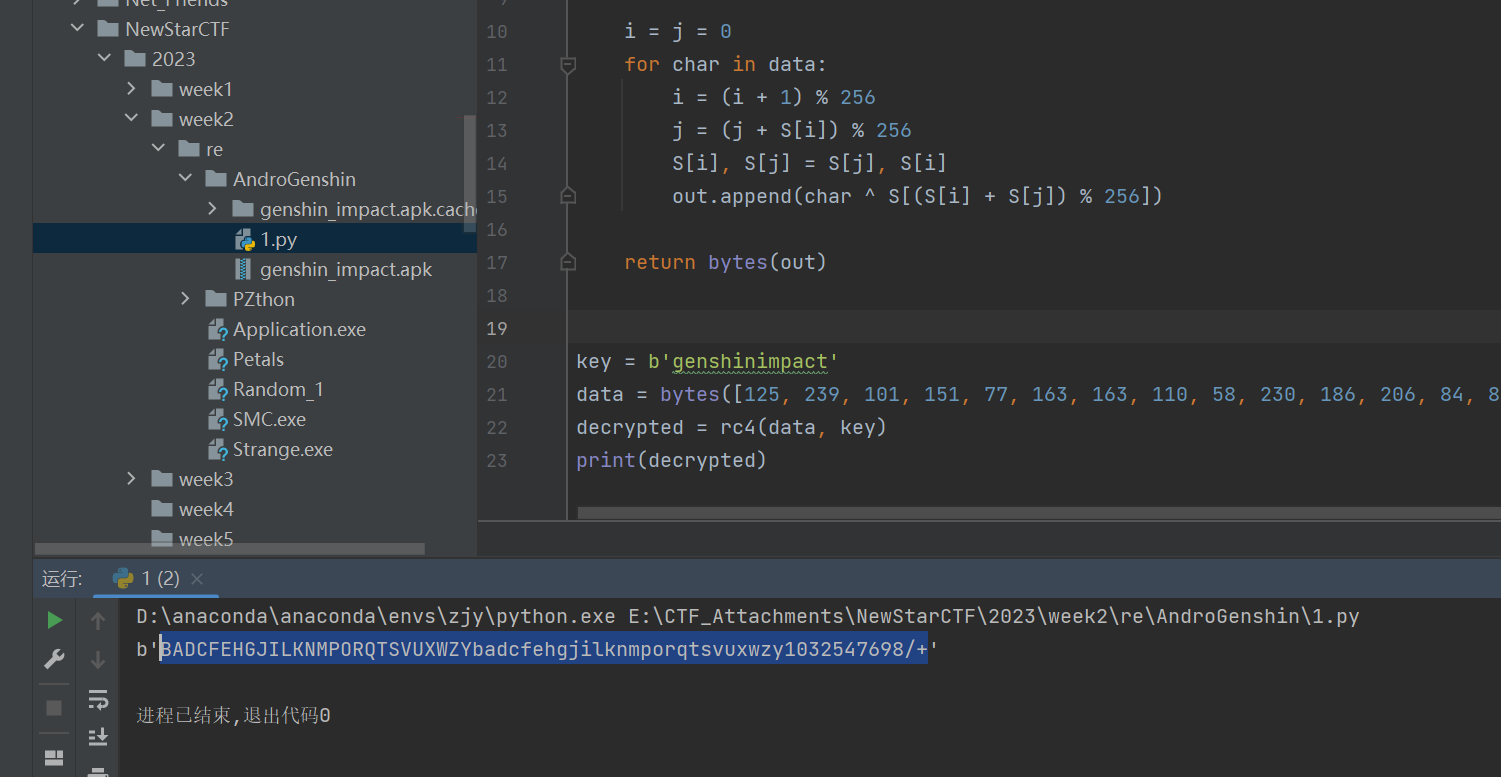
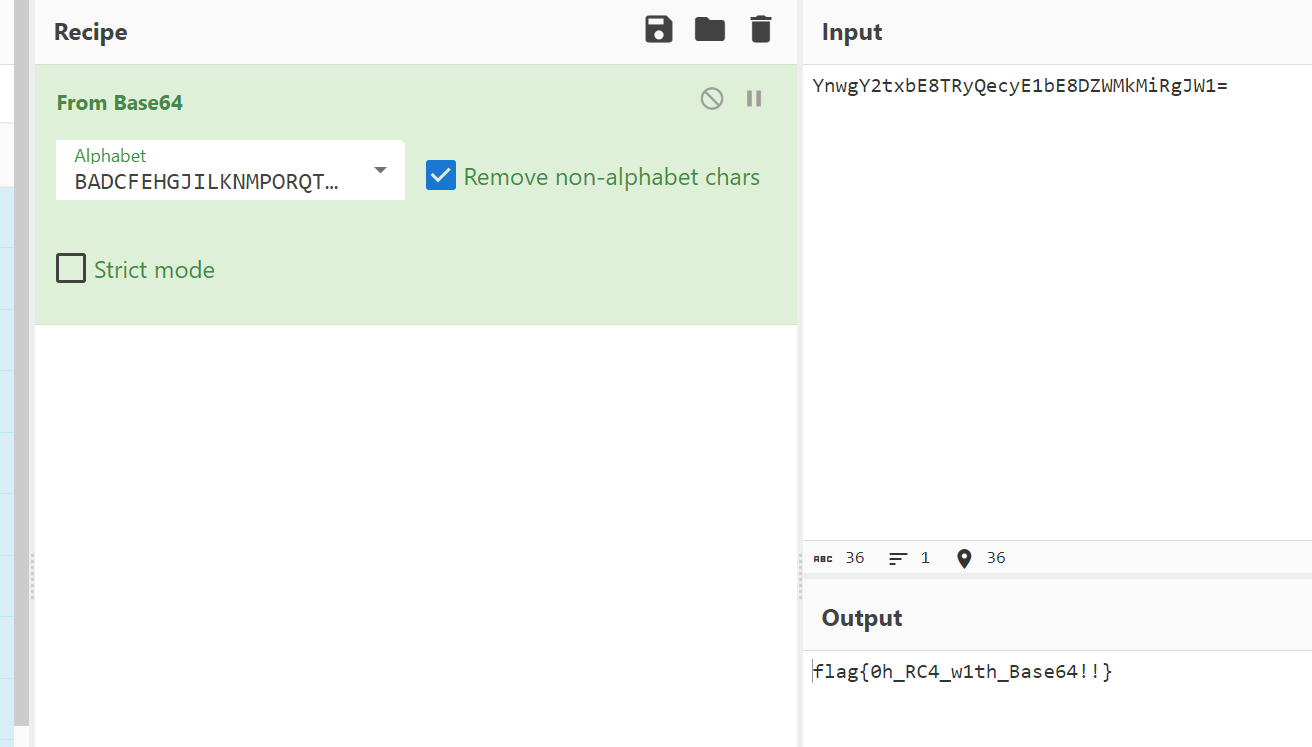
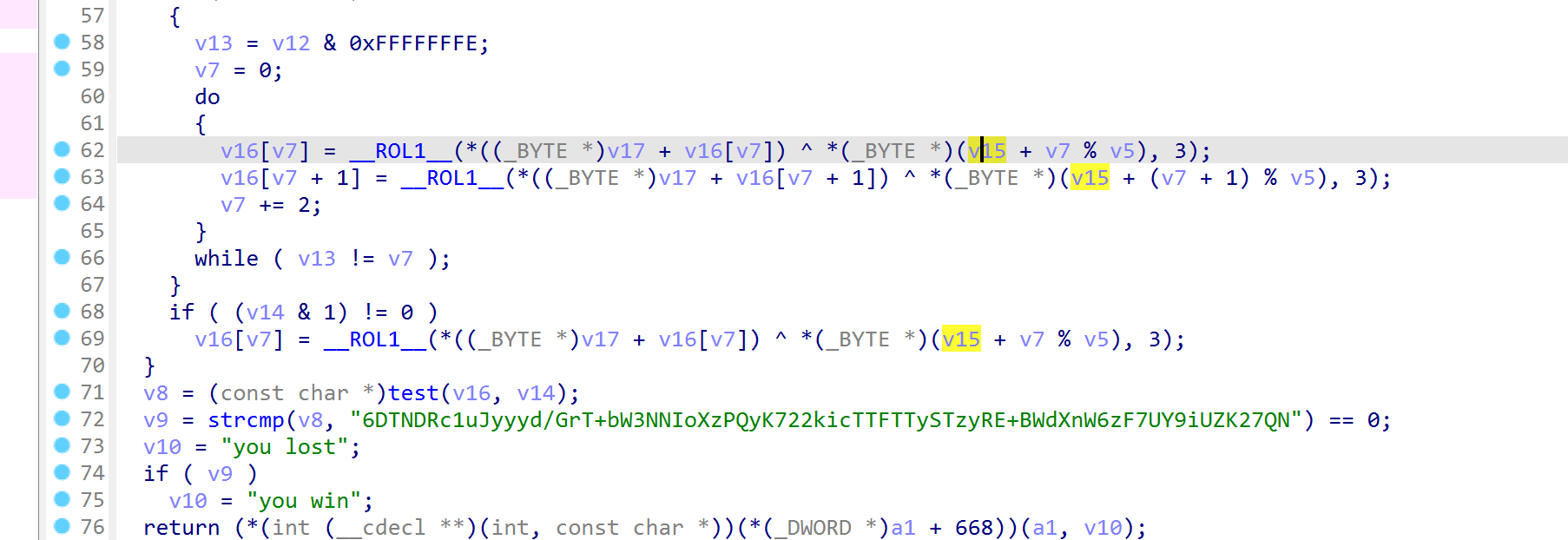
AndroGenshin
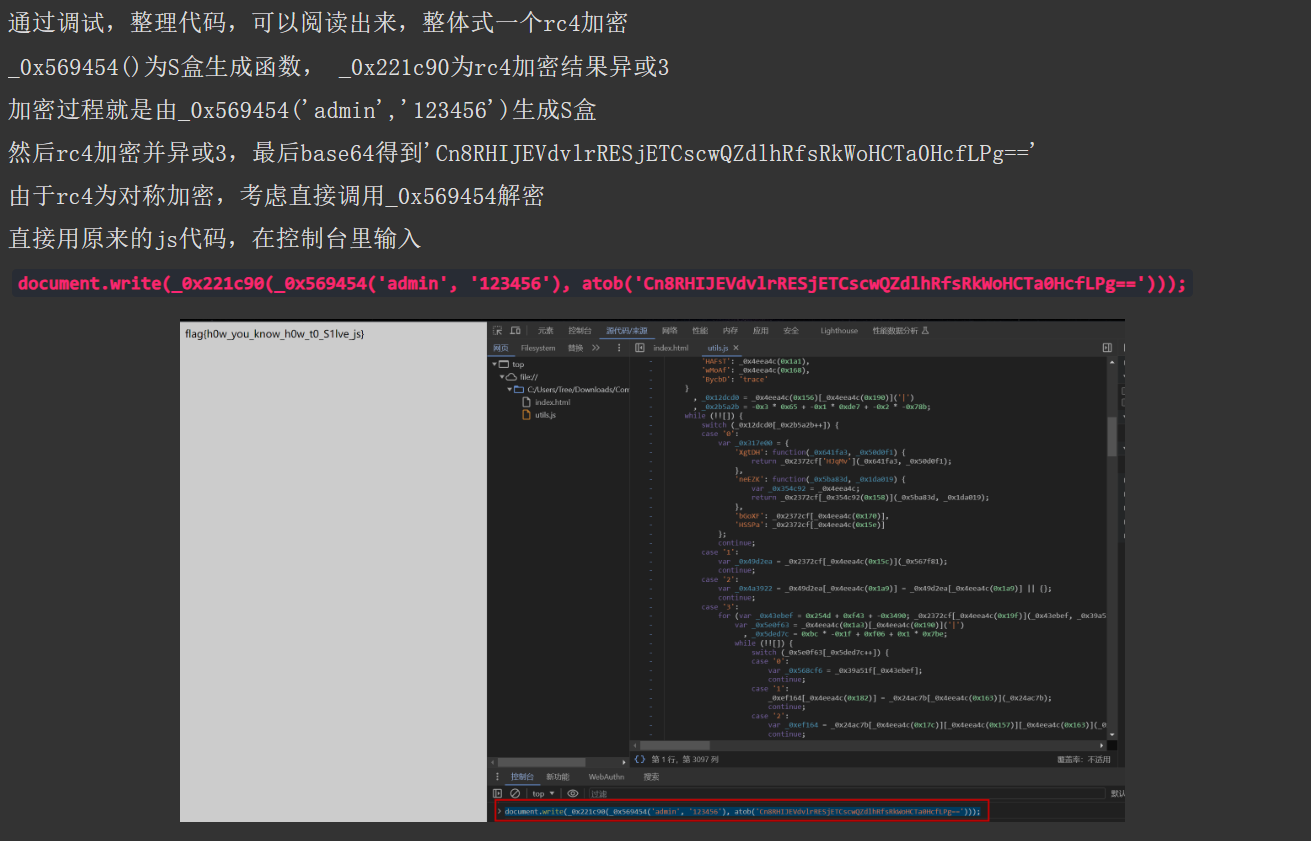
知道用户名,base64和rc4算法都没改,求password
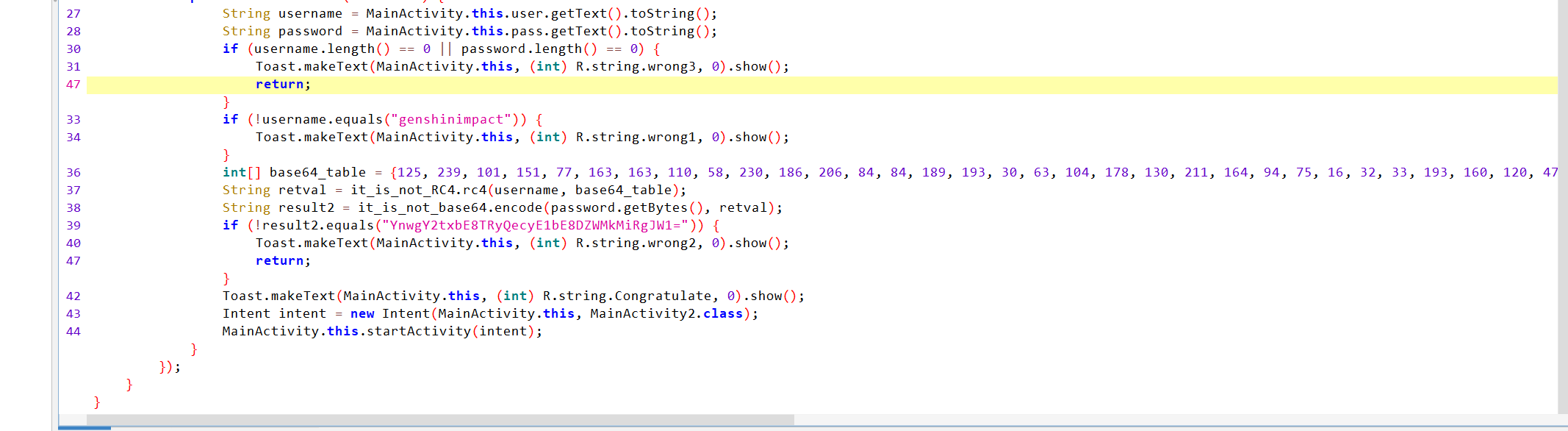
解rc4得到变表
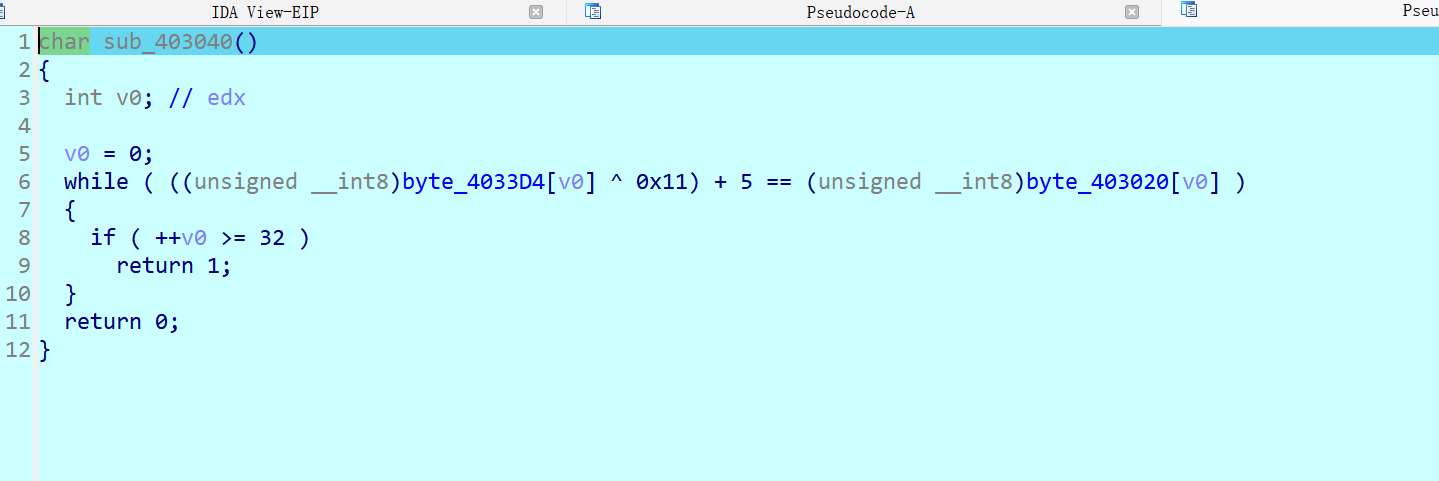
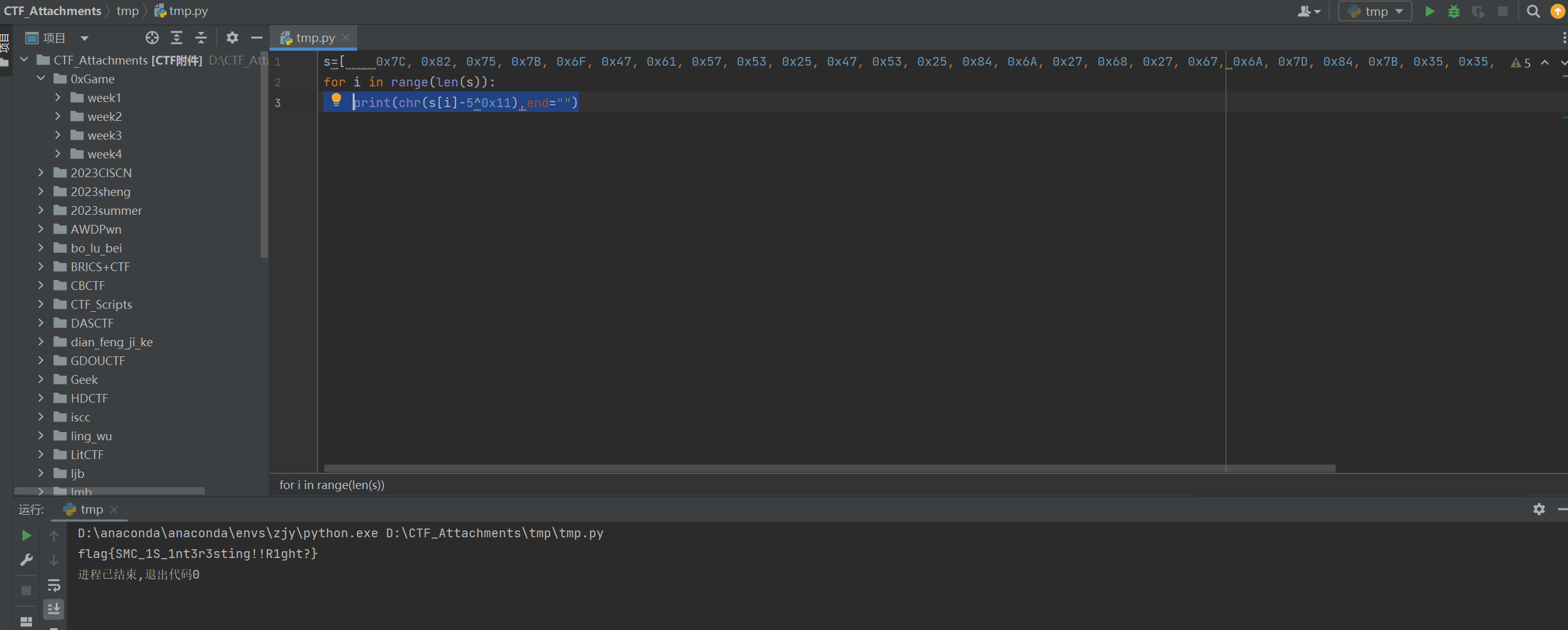
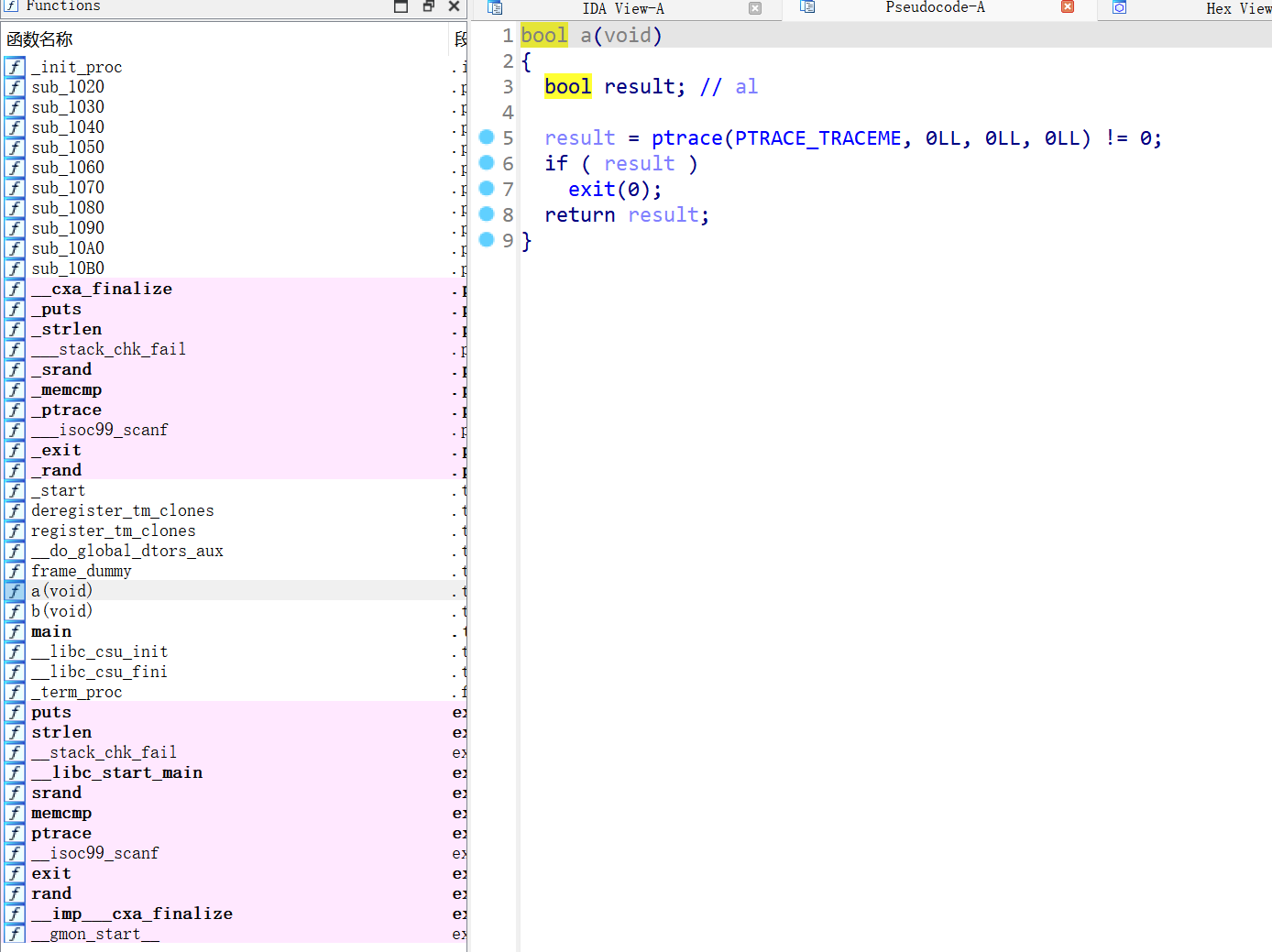
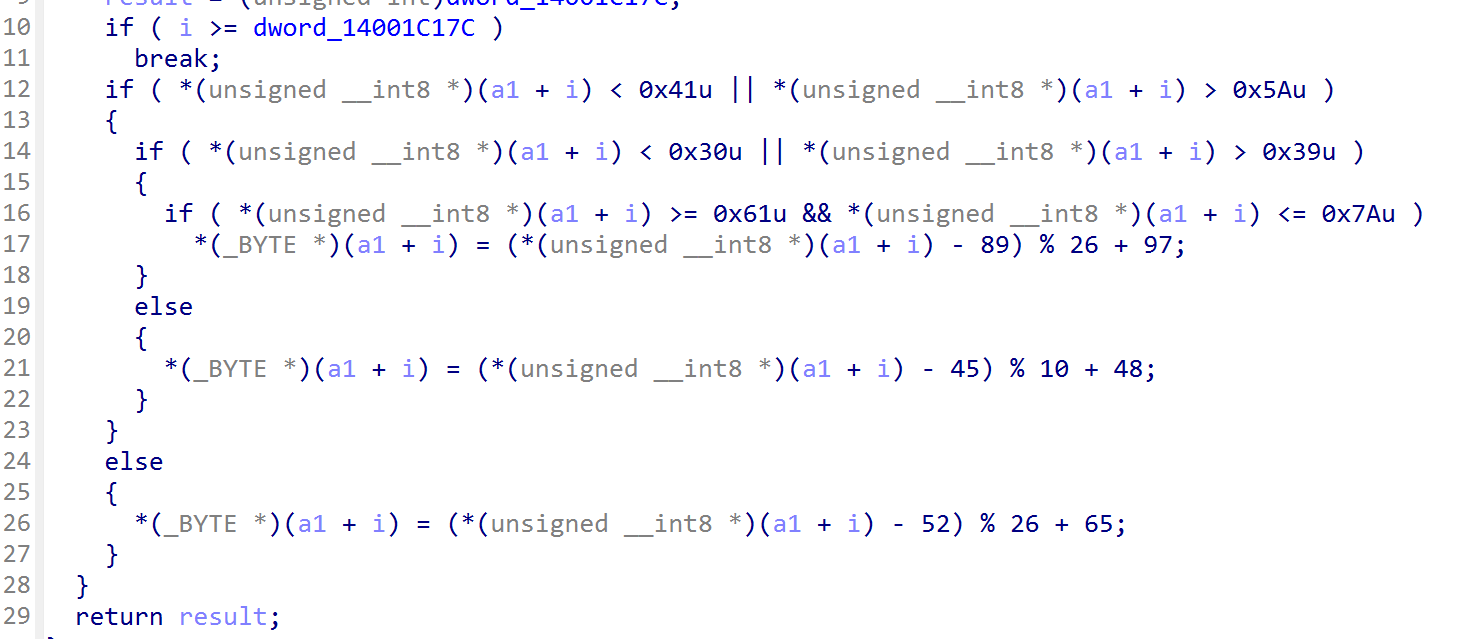
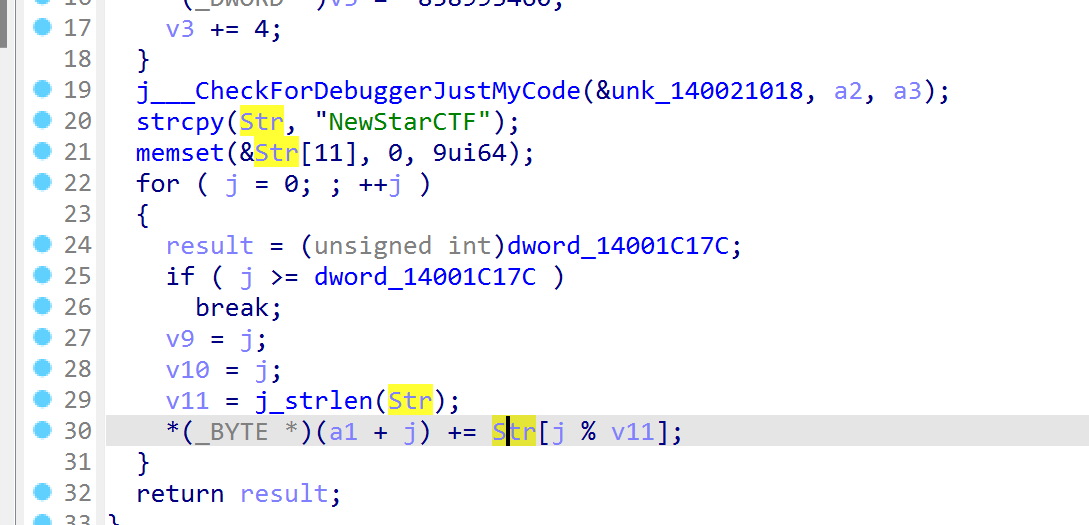
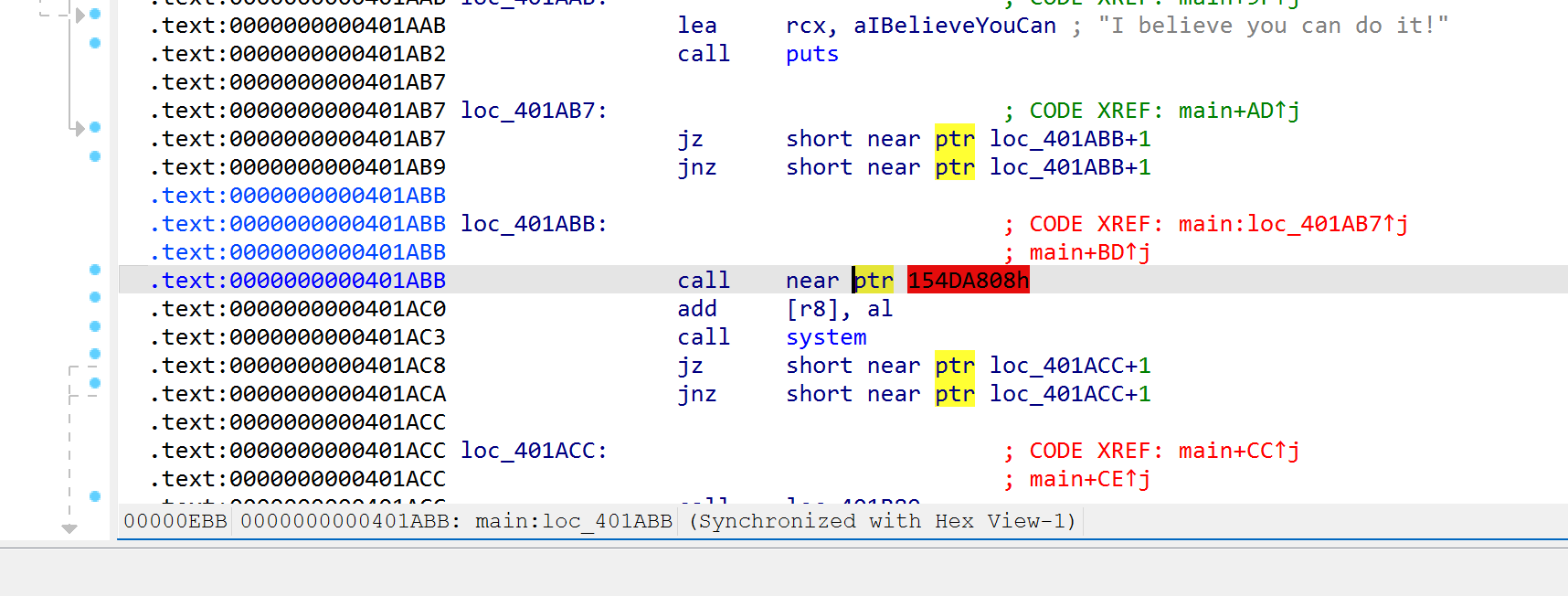
SMC
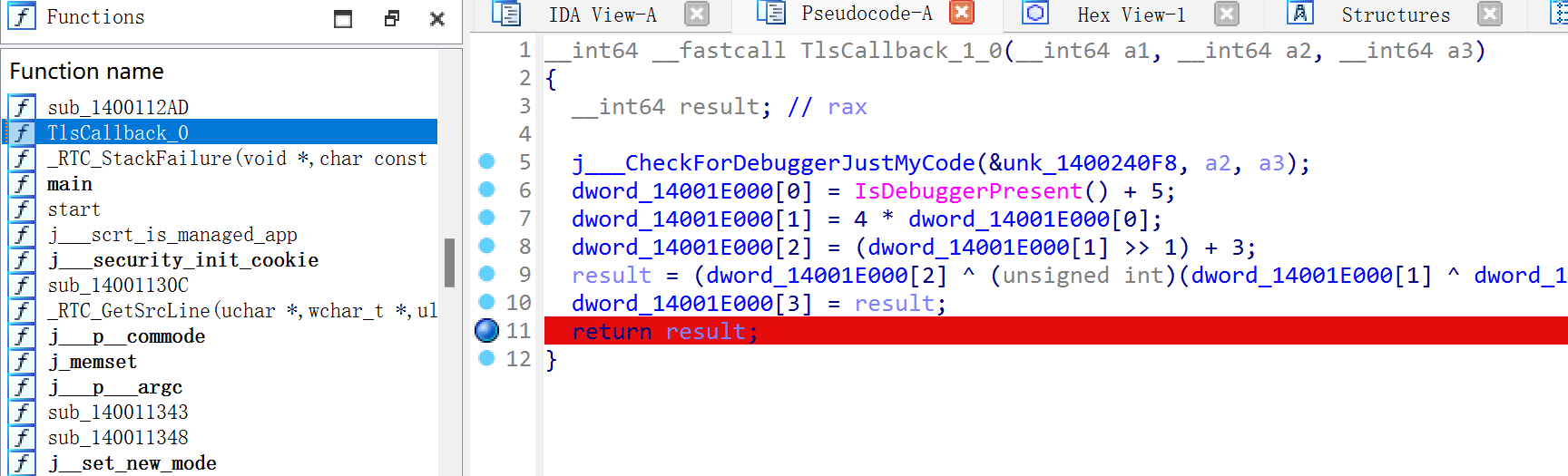
检测到调试就退出,说明有反调试
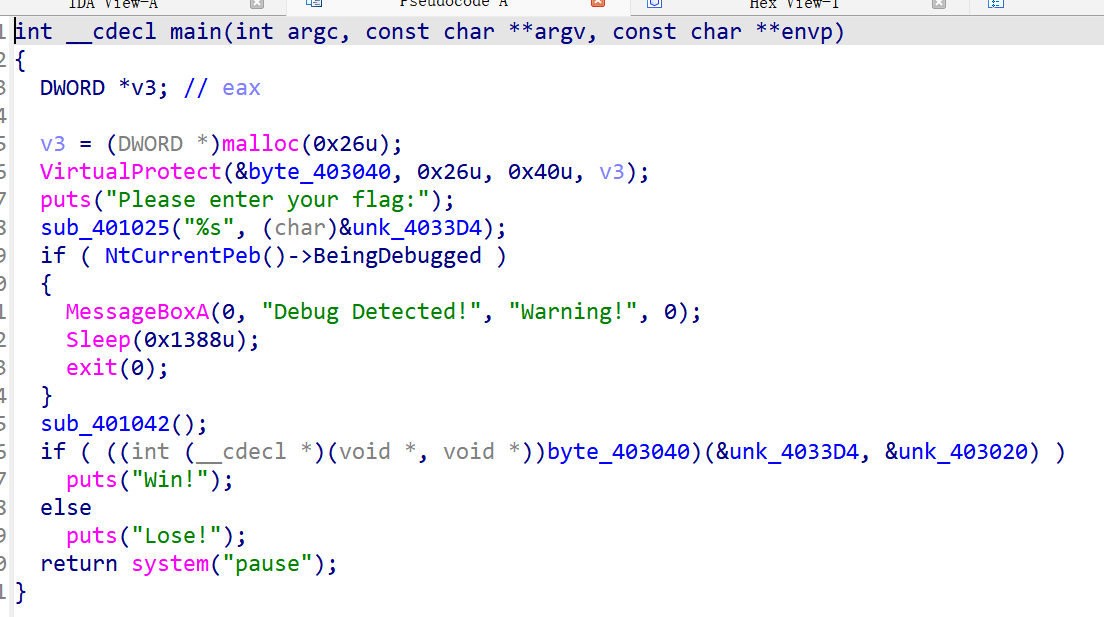
先异或,再函数调用
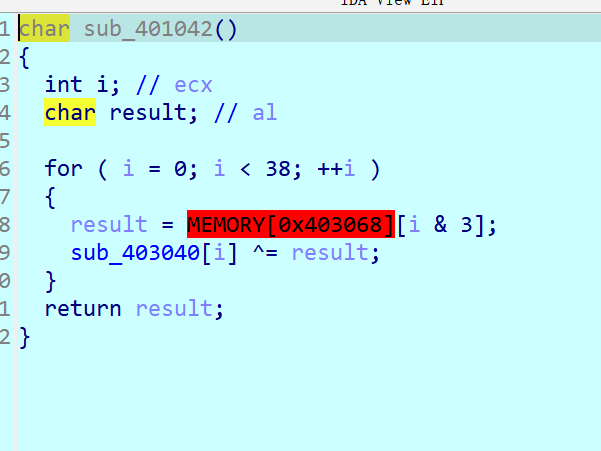
在跳转处修改ZF的值为1,本质上就是修改执行流程,修改使al=bl也行
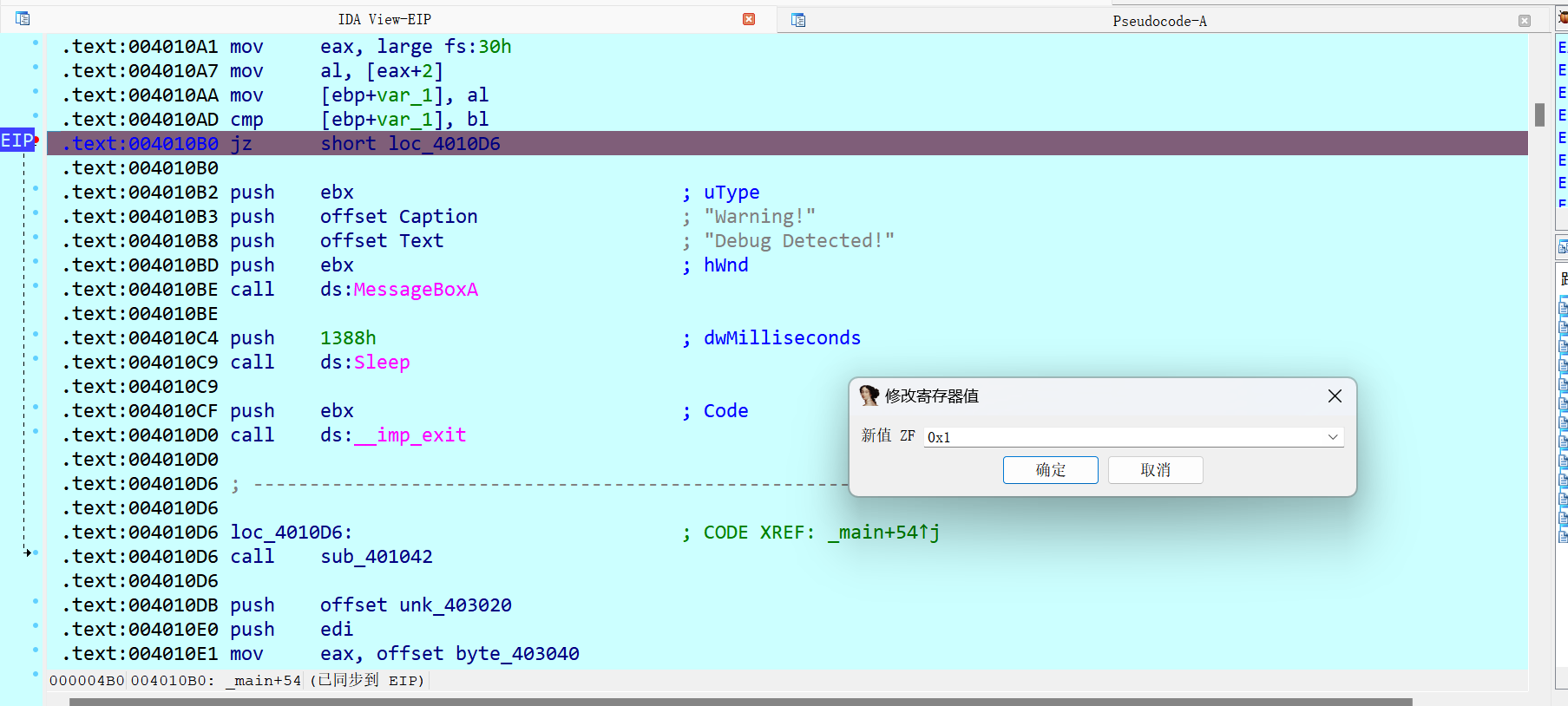
此时f7进入,创建函数即可
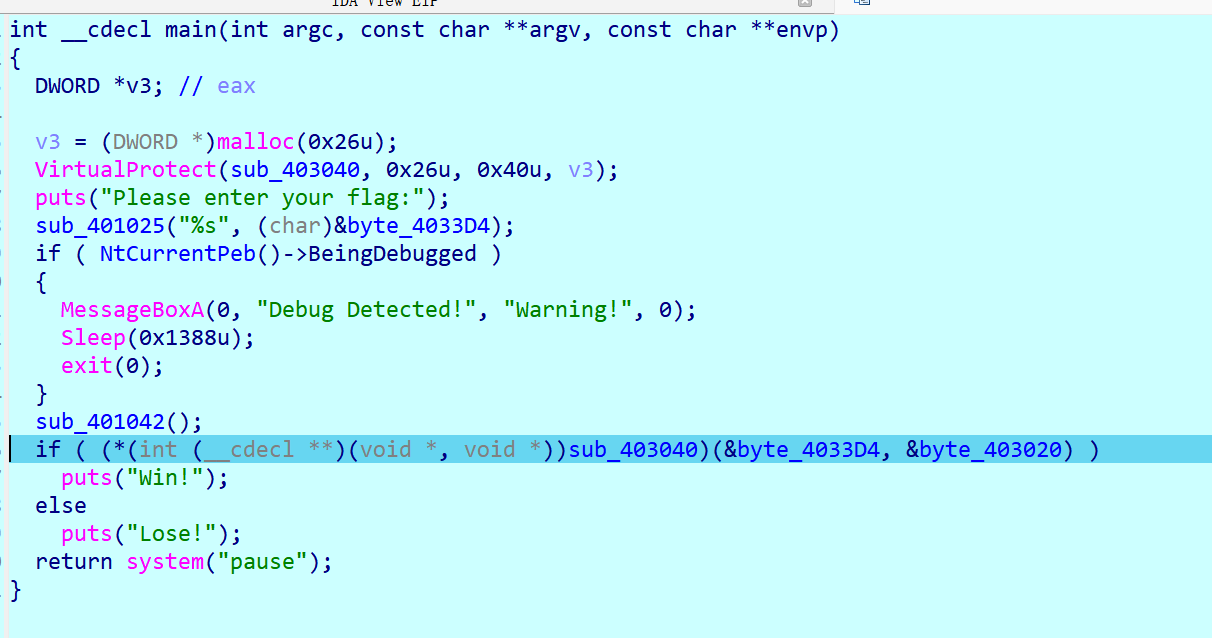
得到正确流程
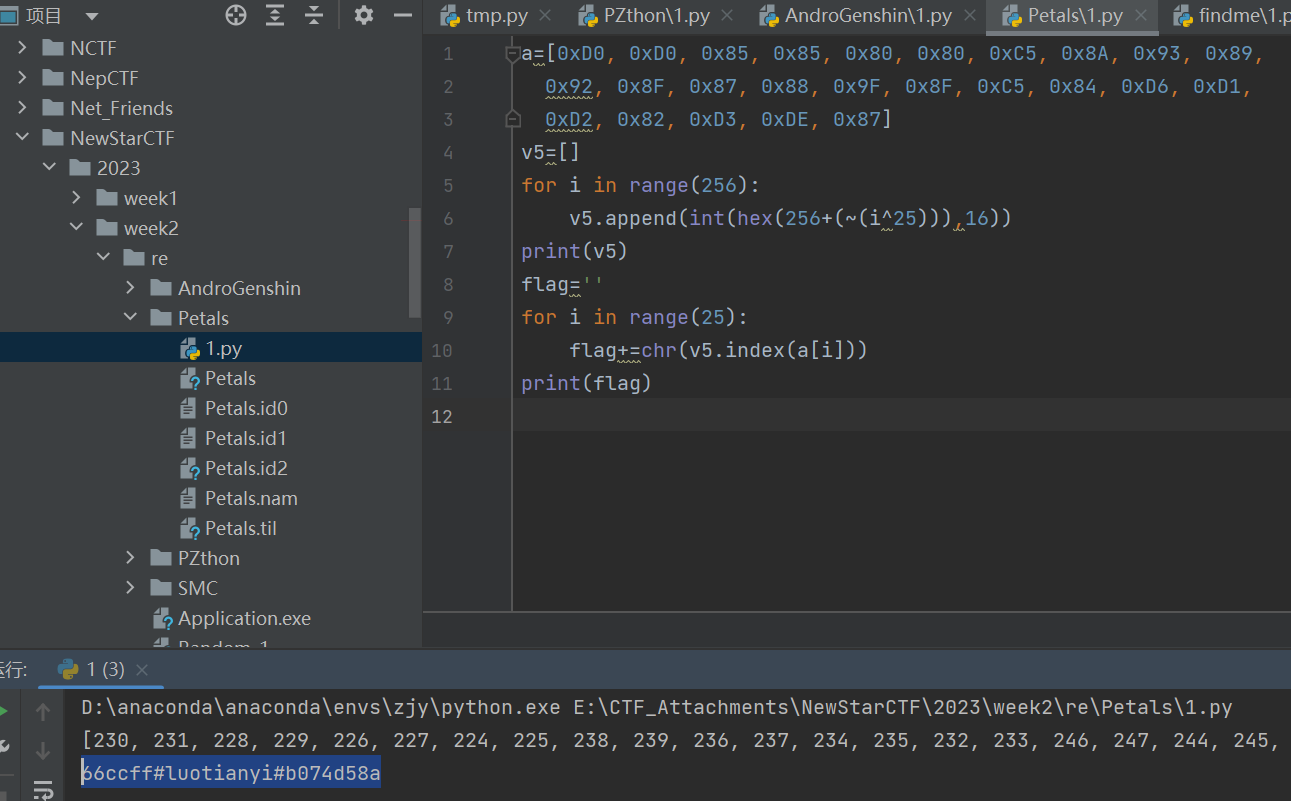
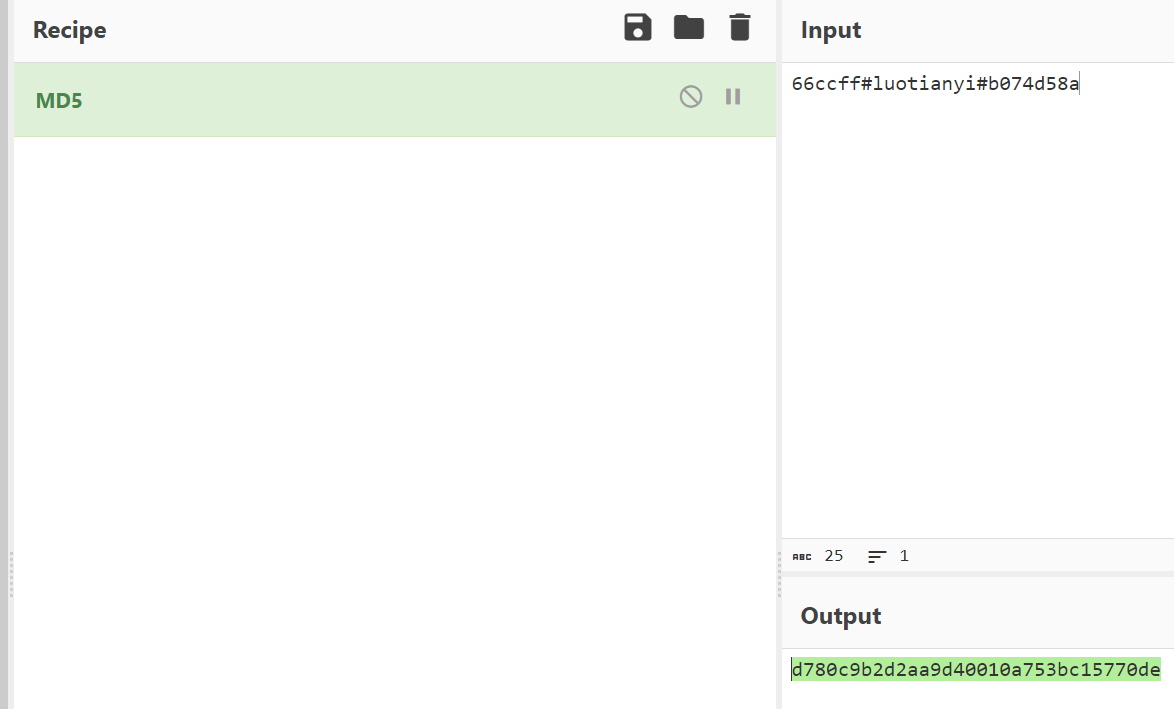
Petals
长度为25
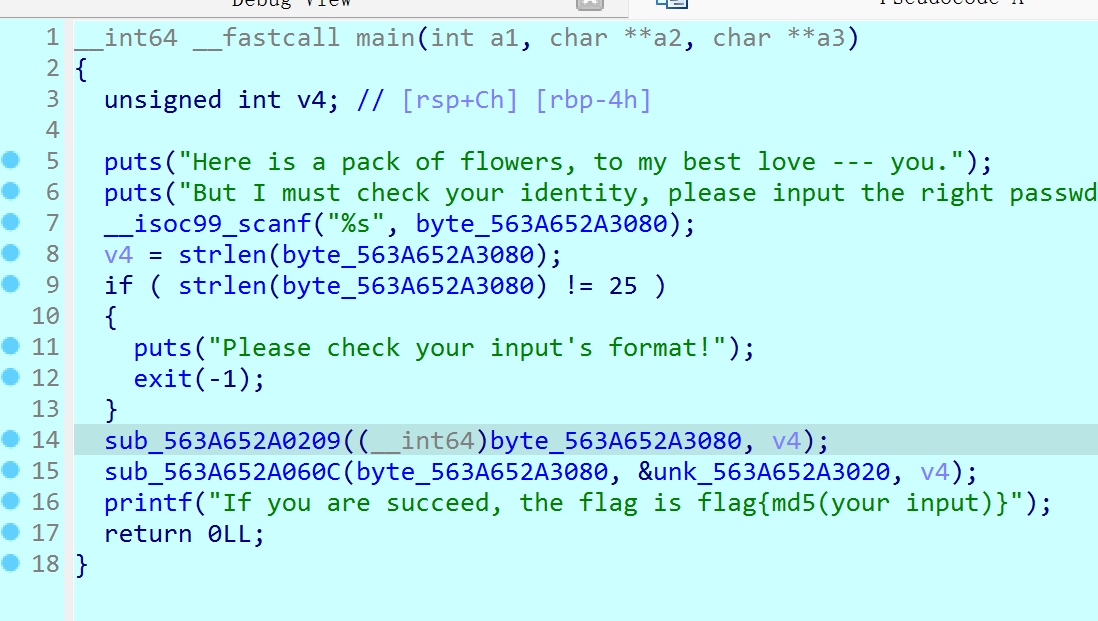
逻辑是a1[i]=v5[flag[i]]
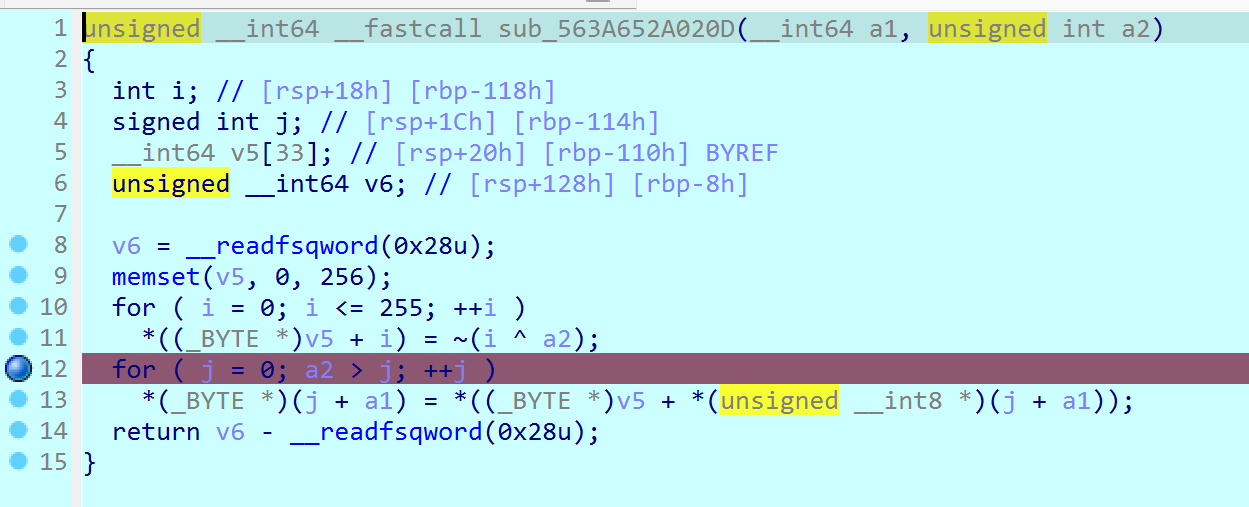
那就是简单的求下标
C or C++-1
dnspy竟然还可以打开exe
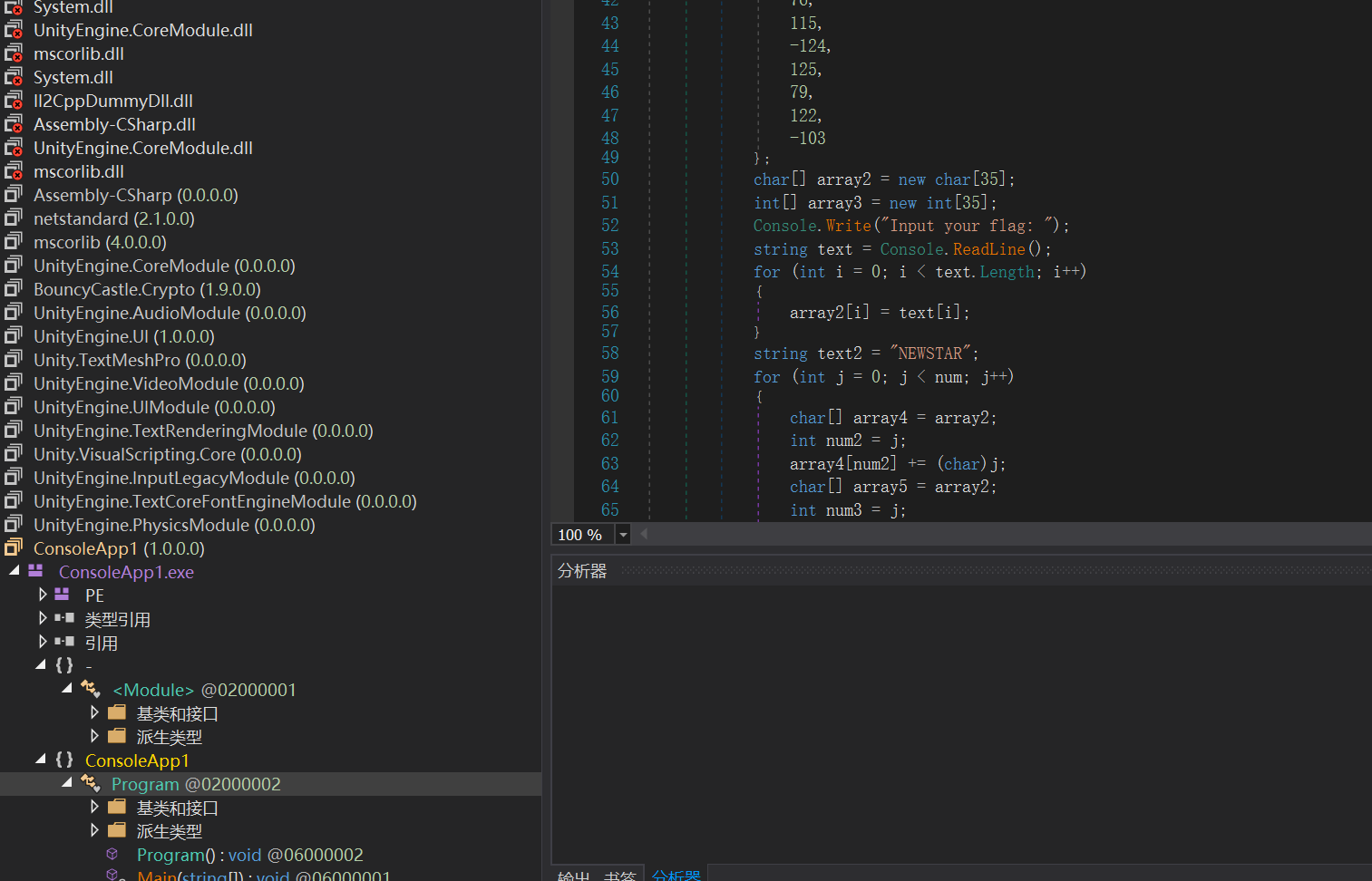
直接可以逆
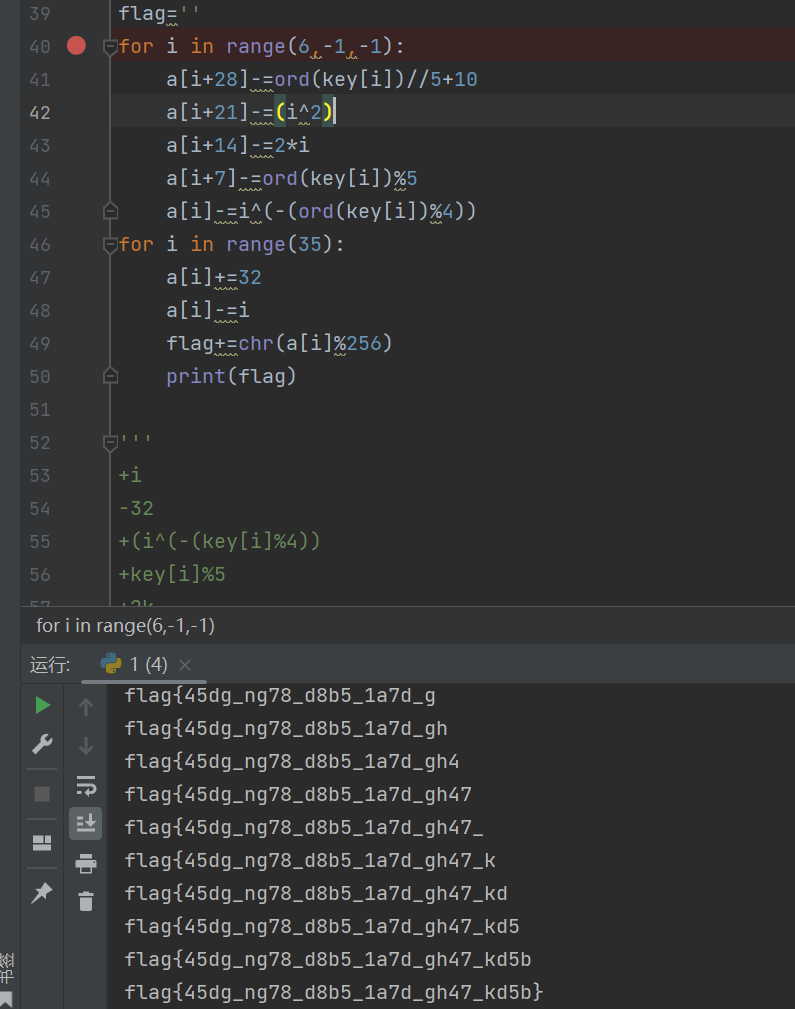
R4ndom-1
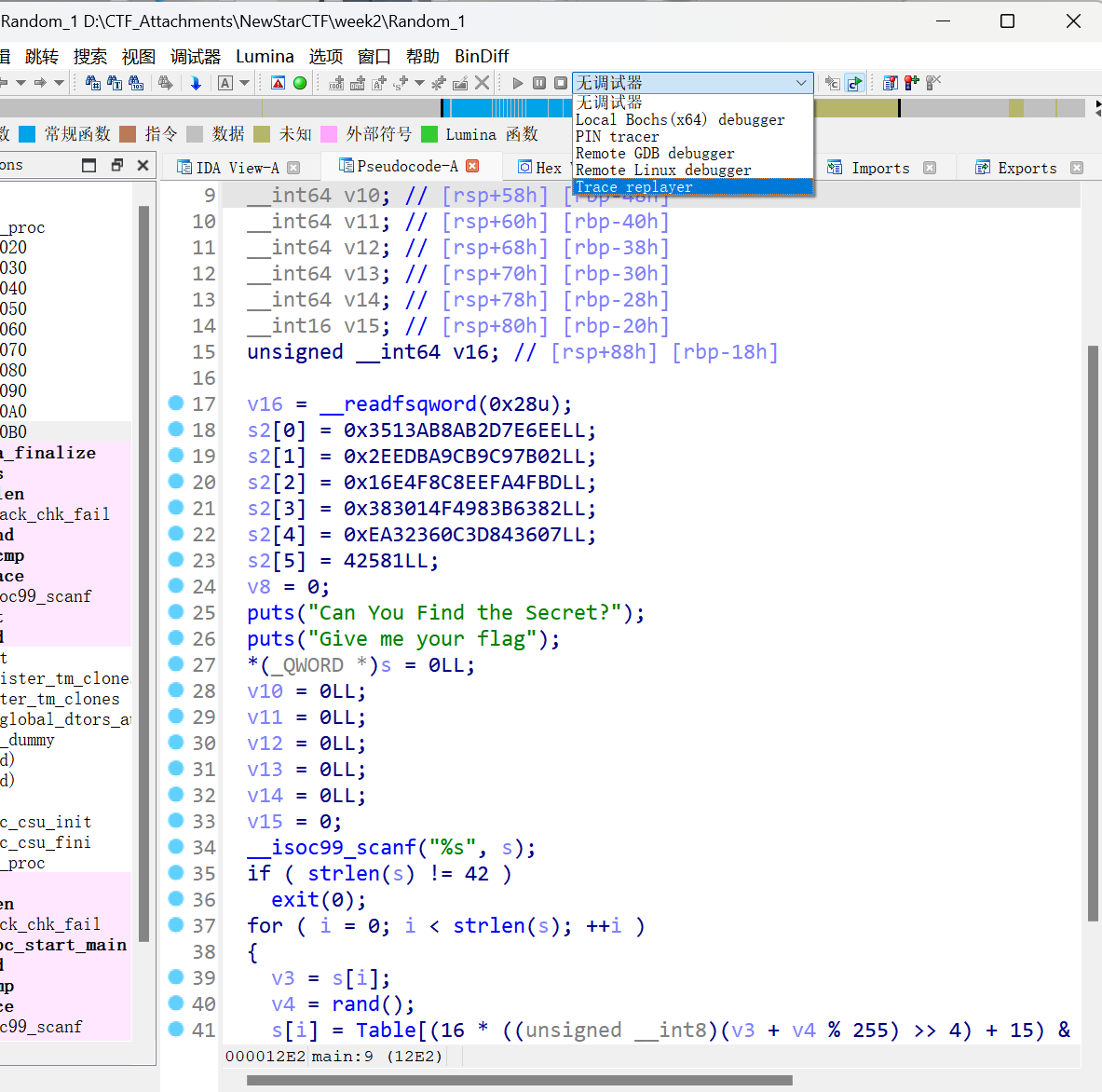 函数a很奇怪,有反调试,这里也可以不管
函数a很奇怪,有反调试,这里也可以不管
找到种子
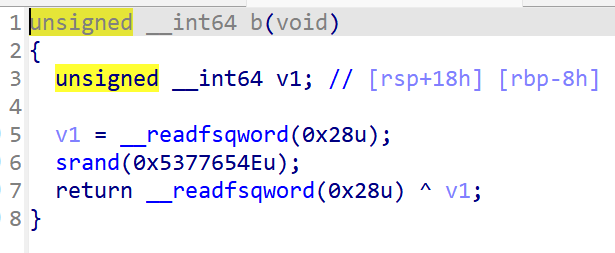
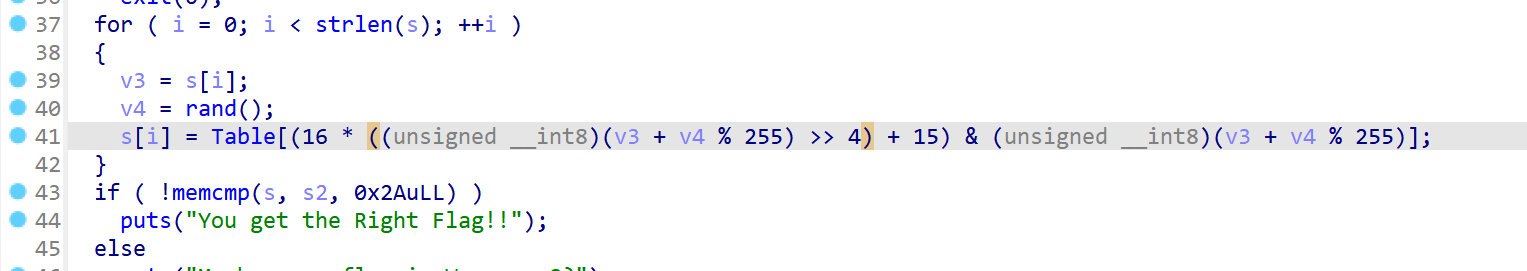
可以用python演示一下在干嘛
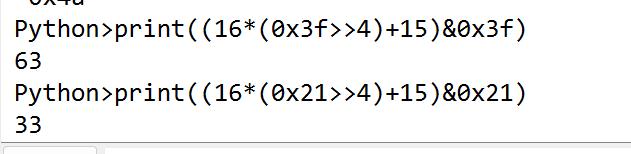
这里把低4字节变成f,再和自身异或,相当于没变
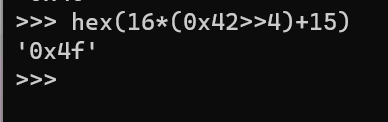
爆破一下
1 | |
注意win和linux的随机数不一样,这里要到linux去跑
easy_enc
格式为大小写字母
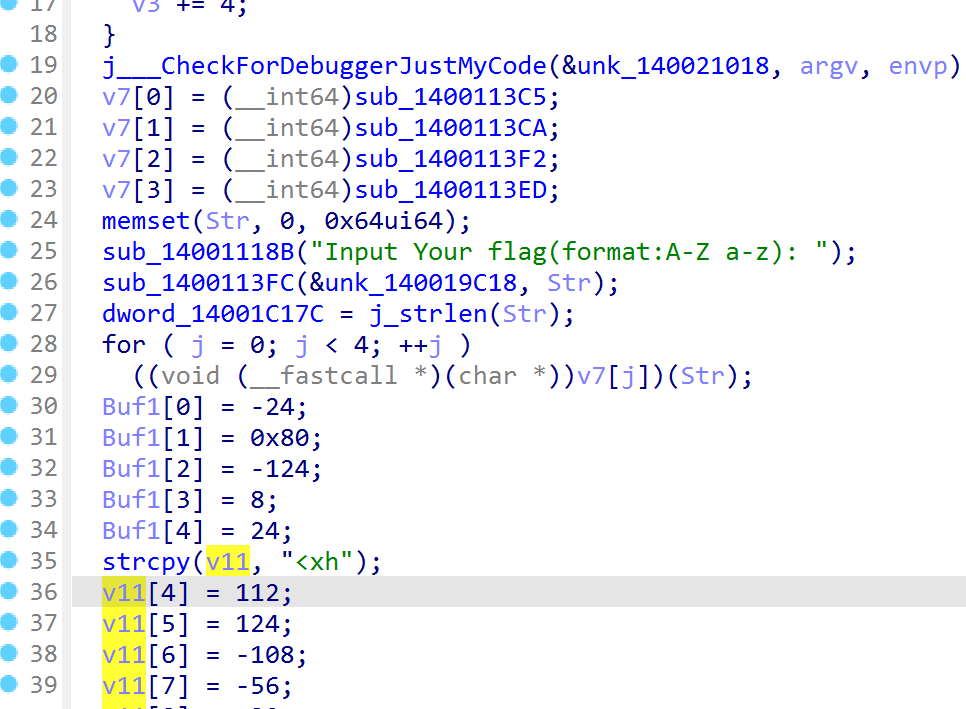
不同的偏移
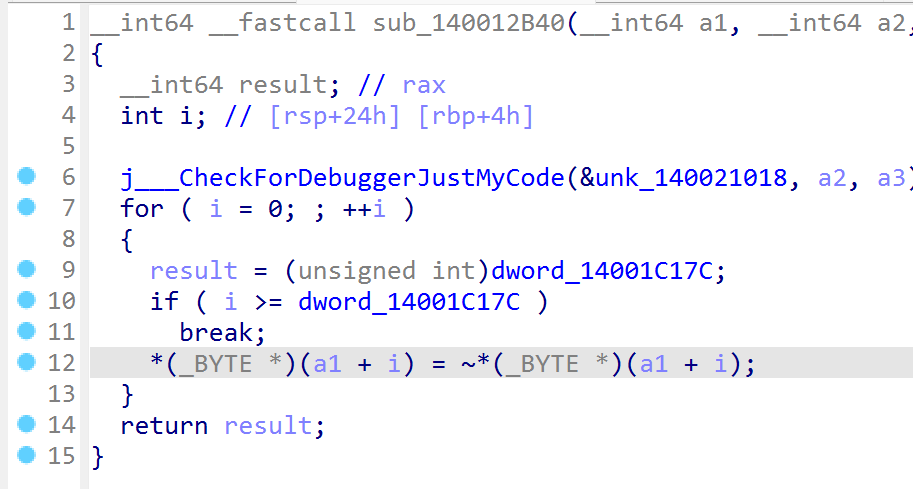
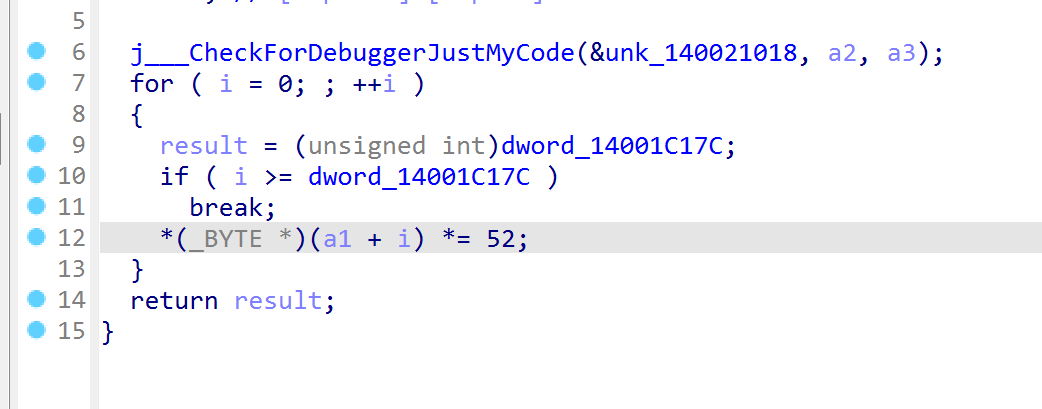
因为有*的存在,逆的时候不知道加几个256,所以直接爆破
1 | |
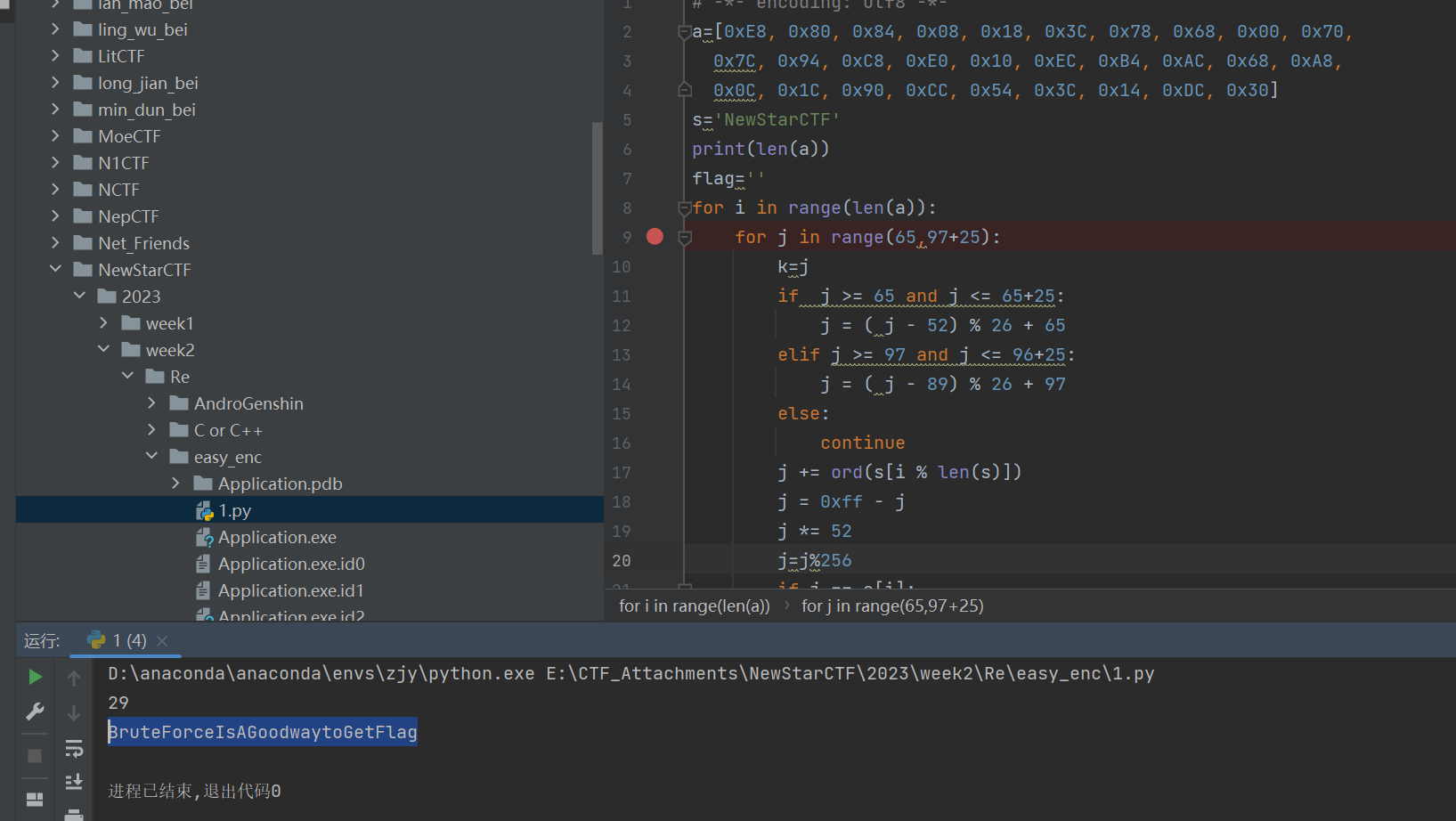
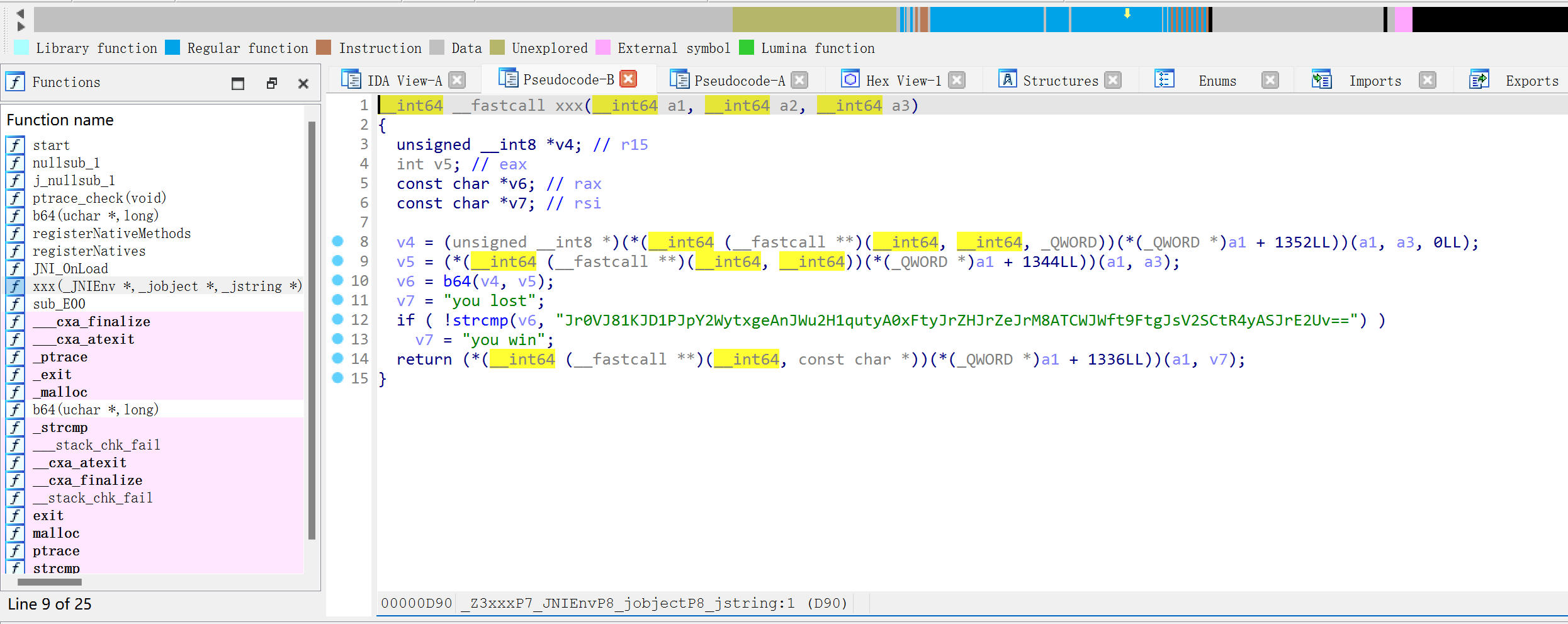
AndroDbgMe
被混淆了,直接调试
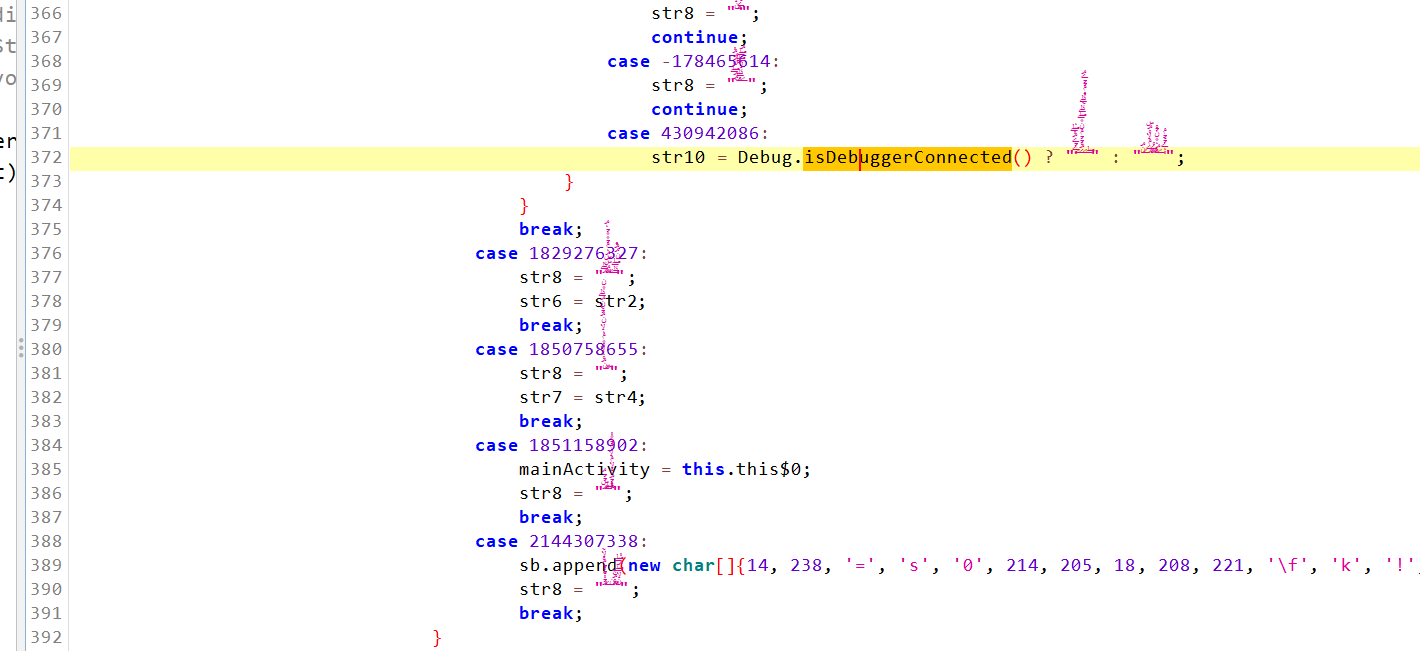
jeb好点,不设断点直接调试
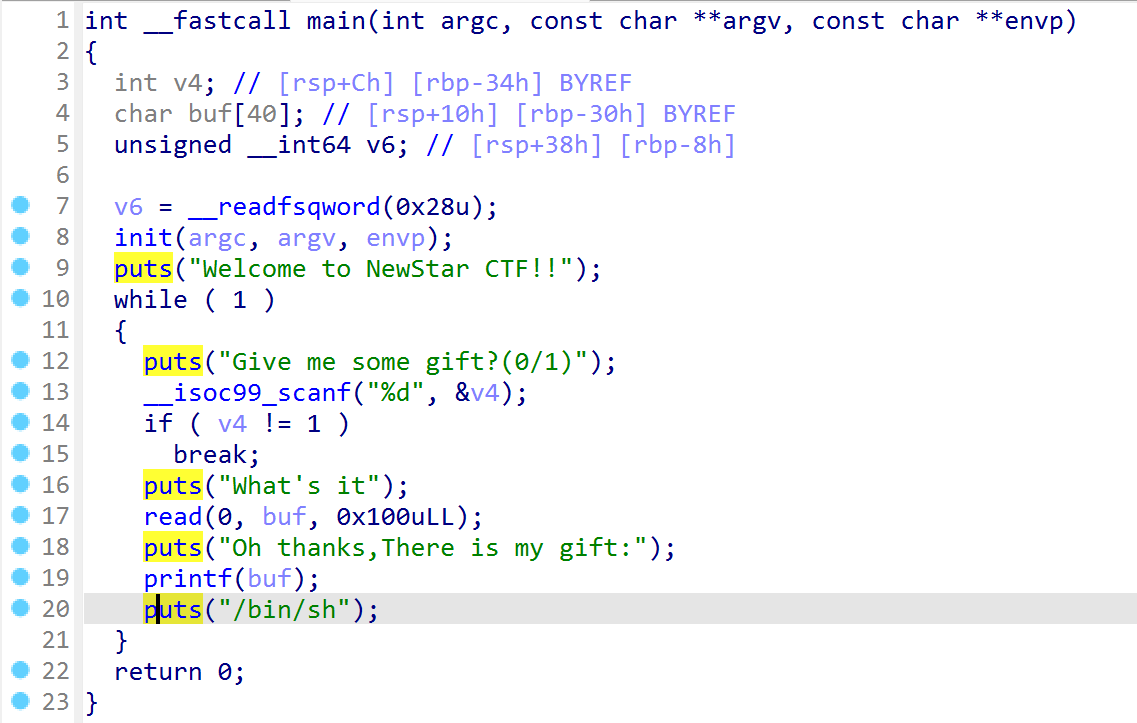
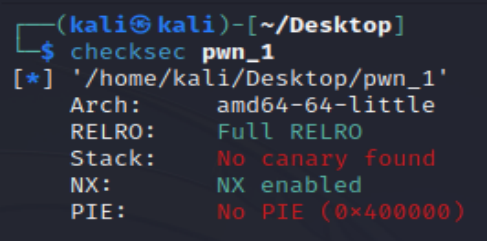
Pwn
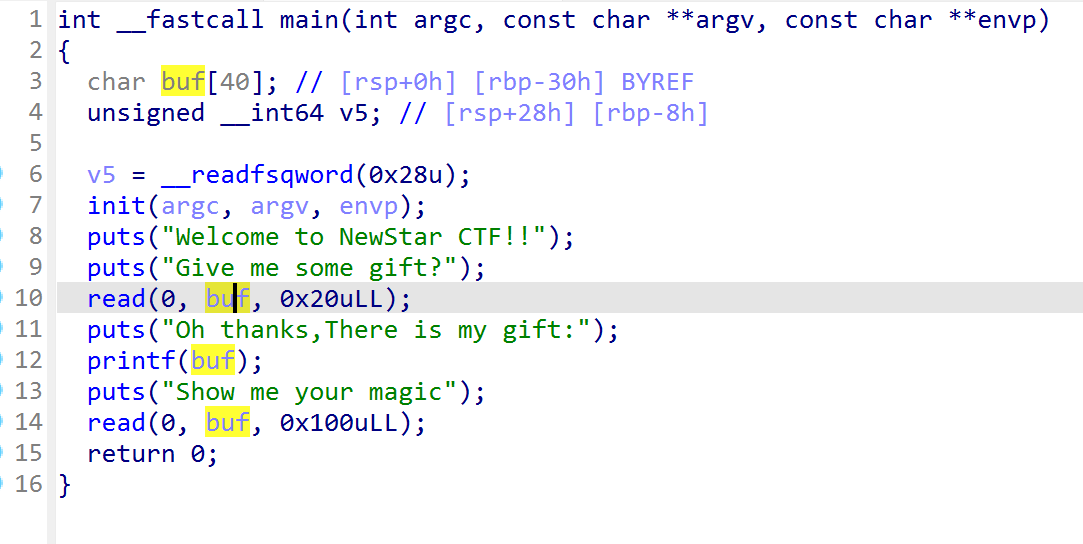
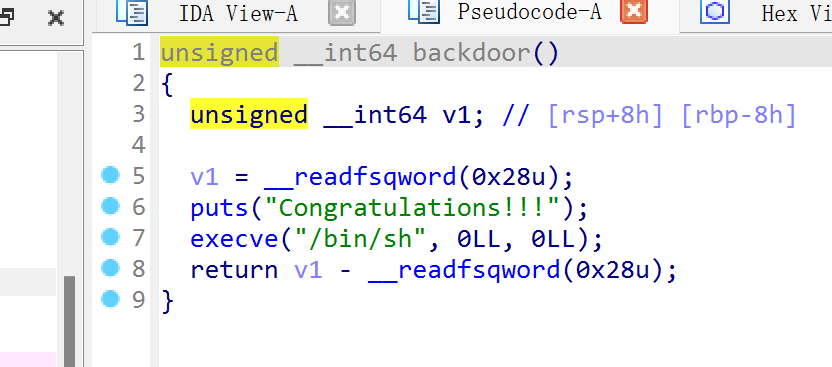
canary
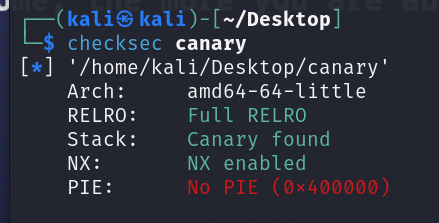
格式化字符串%11$p泄露canary然后栈溢出到返回地址
1 | |
secret_number
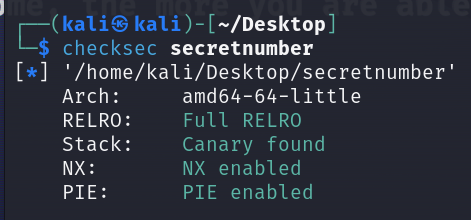
格式化字符串泄露canary,但是没必要,还是和上周的Random一样
1 | |
stack_migration
有了栈地址,直接迁移到栈上
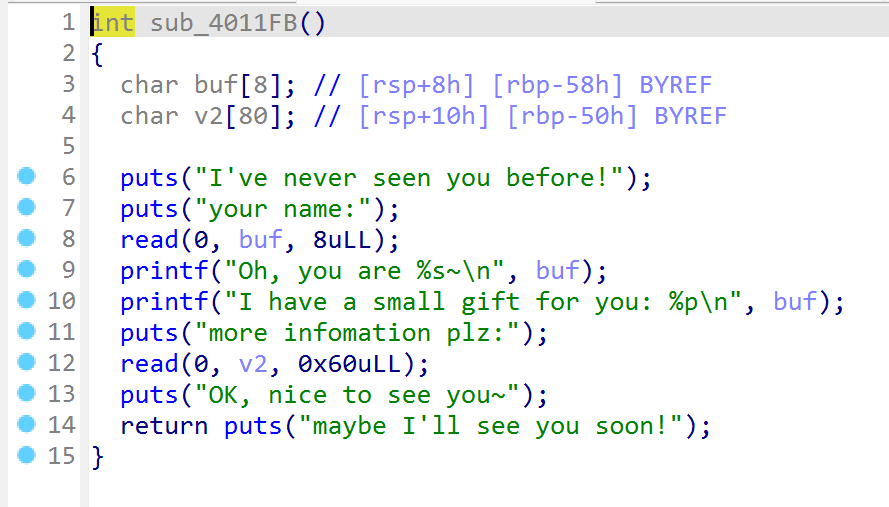
没有system的情况下就用ret2libc,注意返回之后栈地址需要重新泄露
1 | |
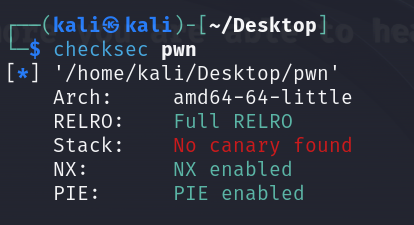
shellcode_revenge
这次只能写大写字母和数字
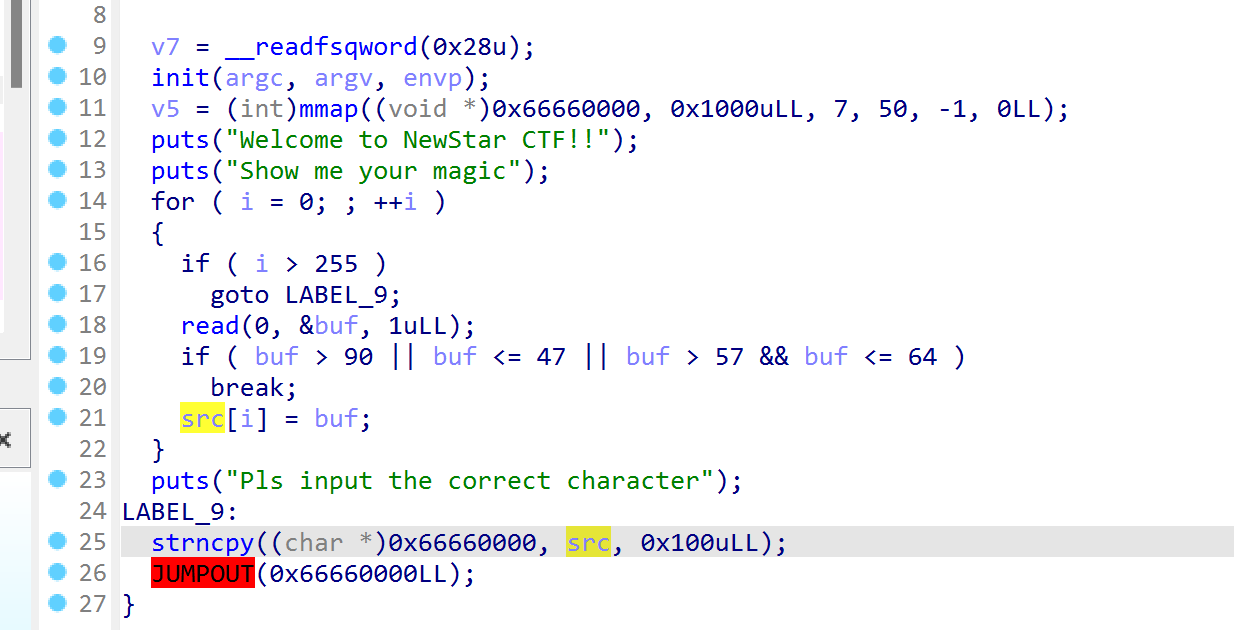
1 | |
Week3
Re
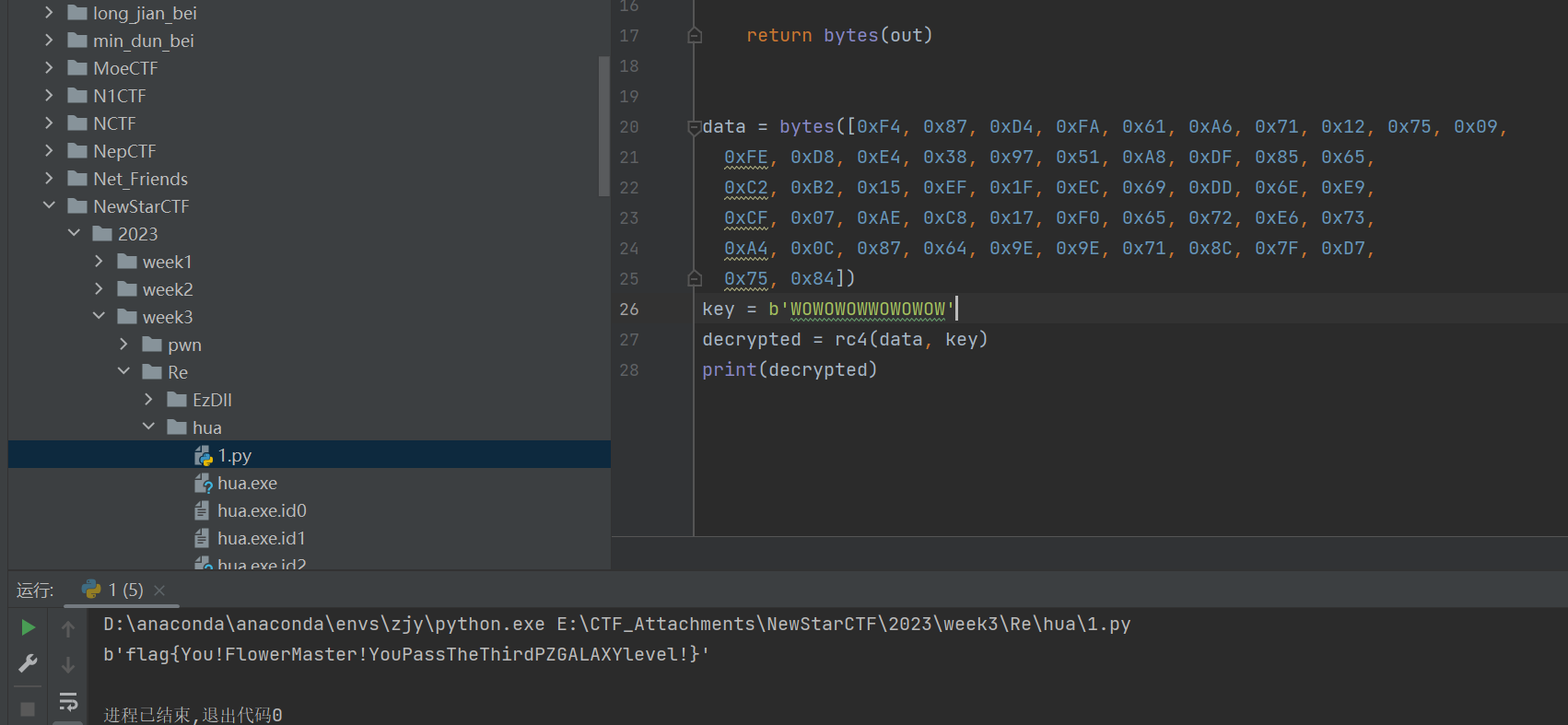
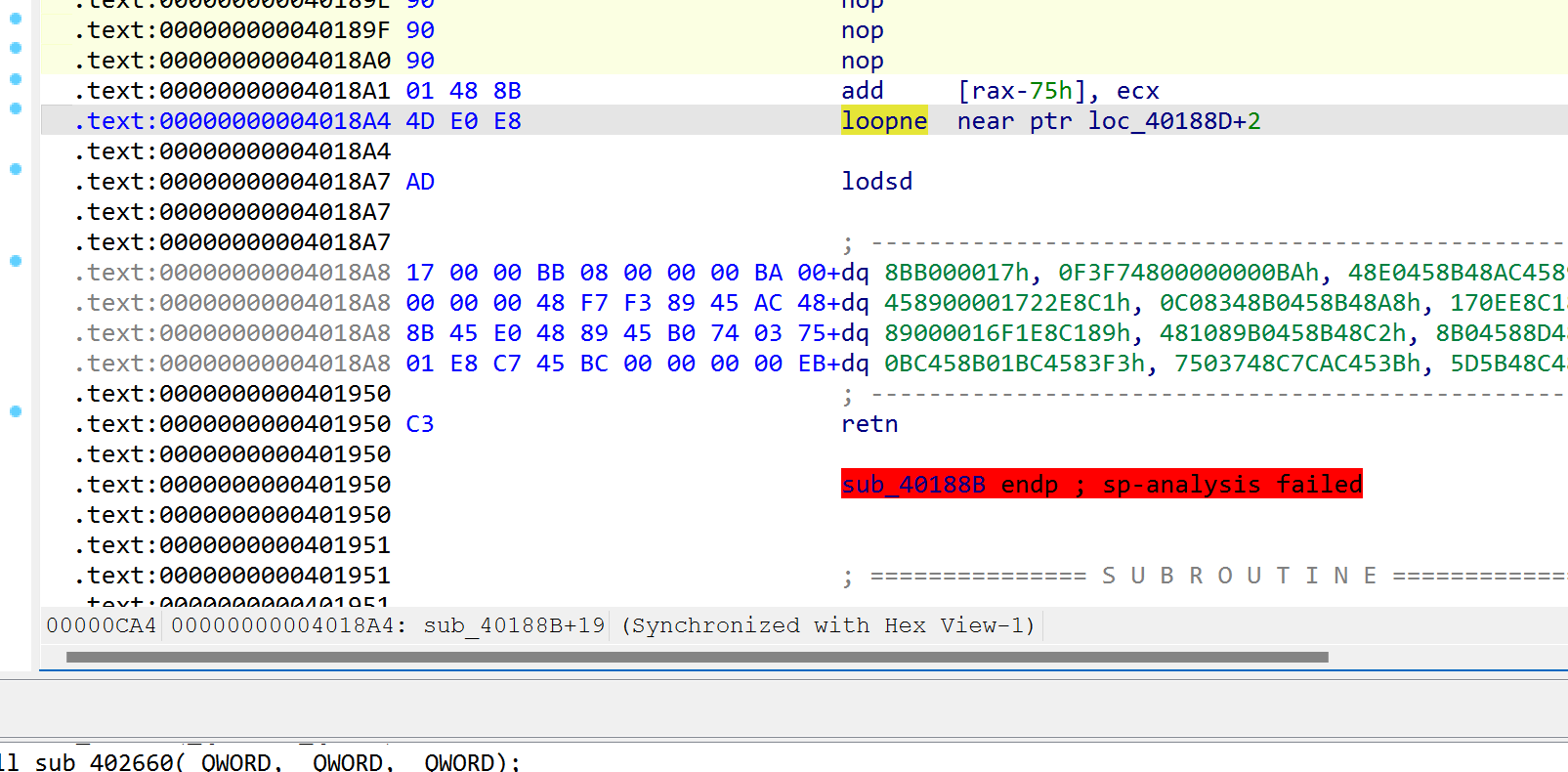
hua
经典花指令
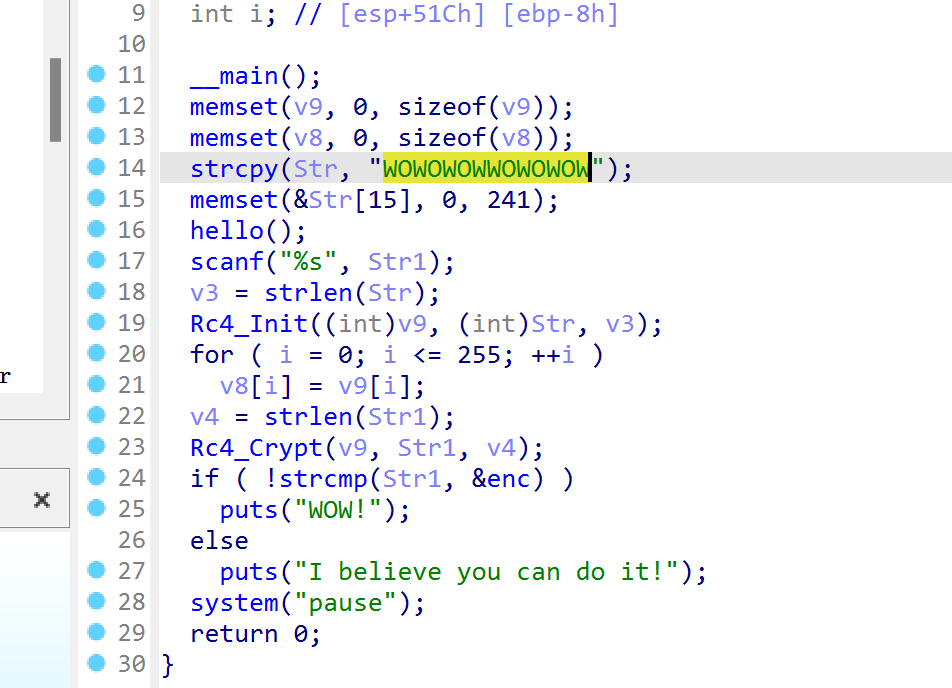
解rc4
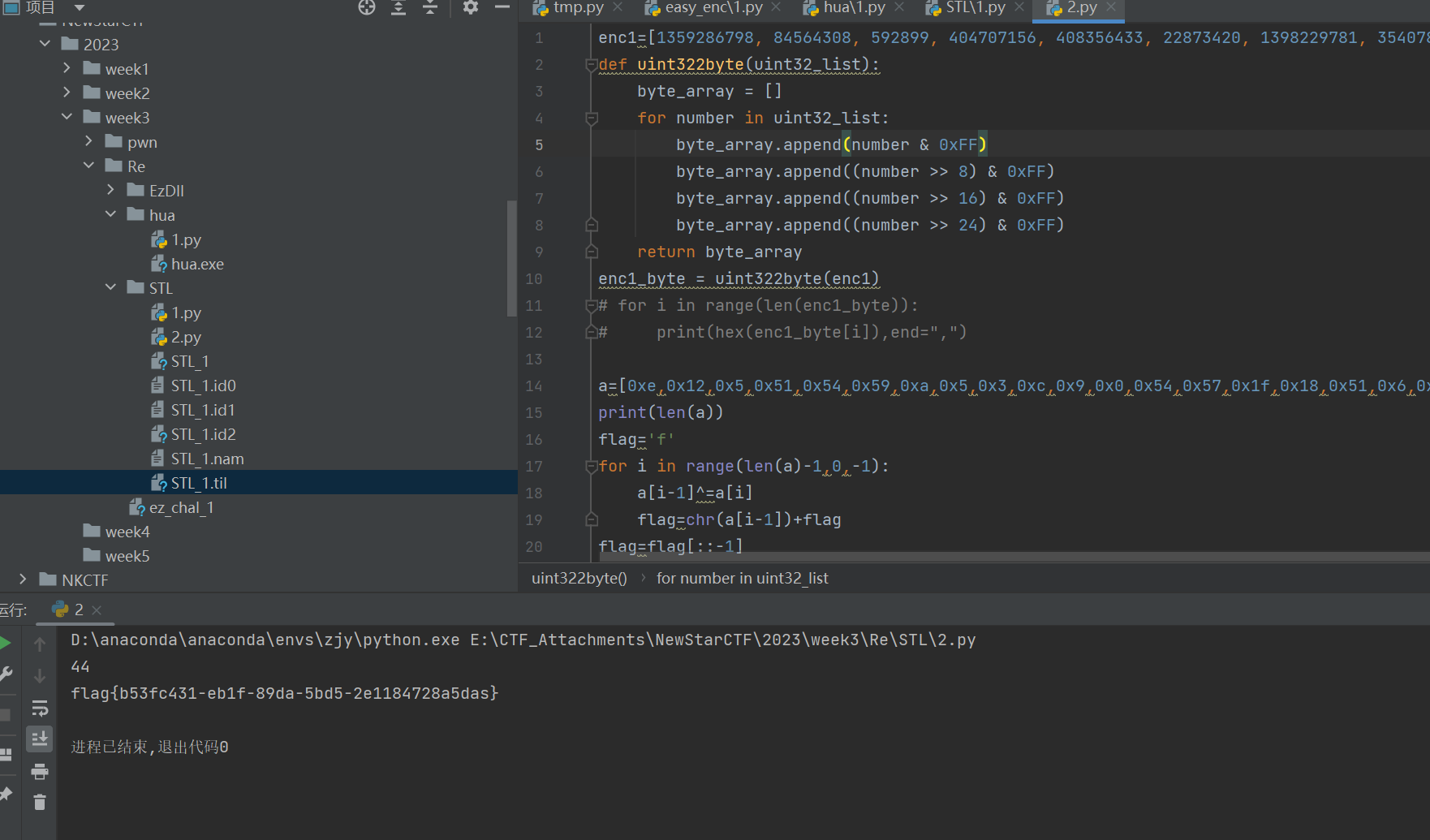
STL
调试的时候能很好解决数据提取问题
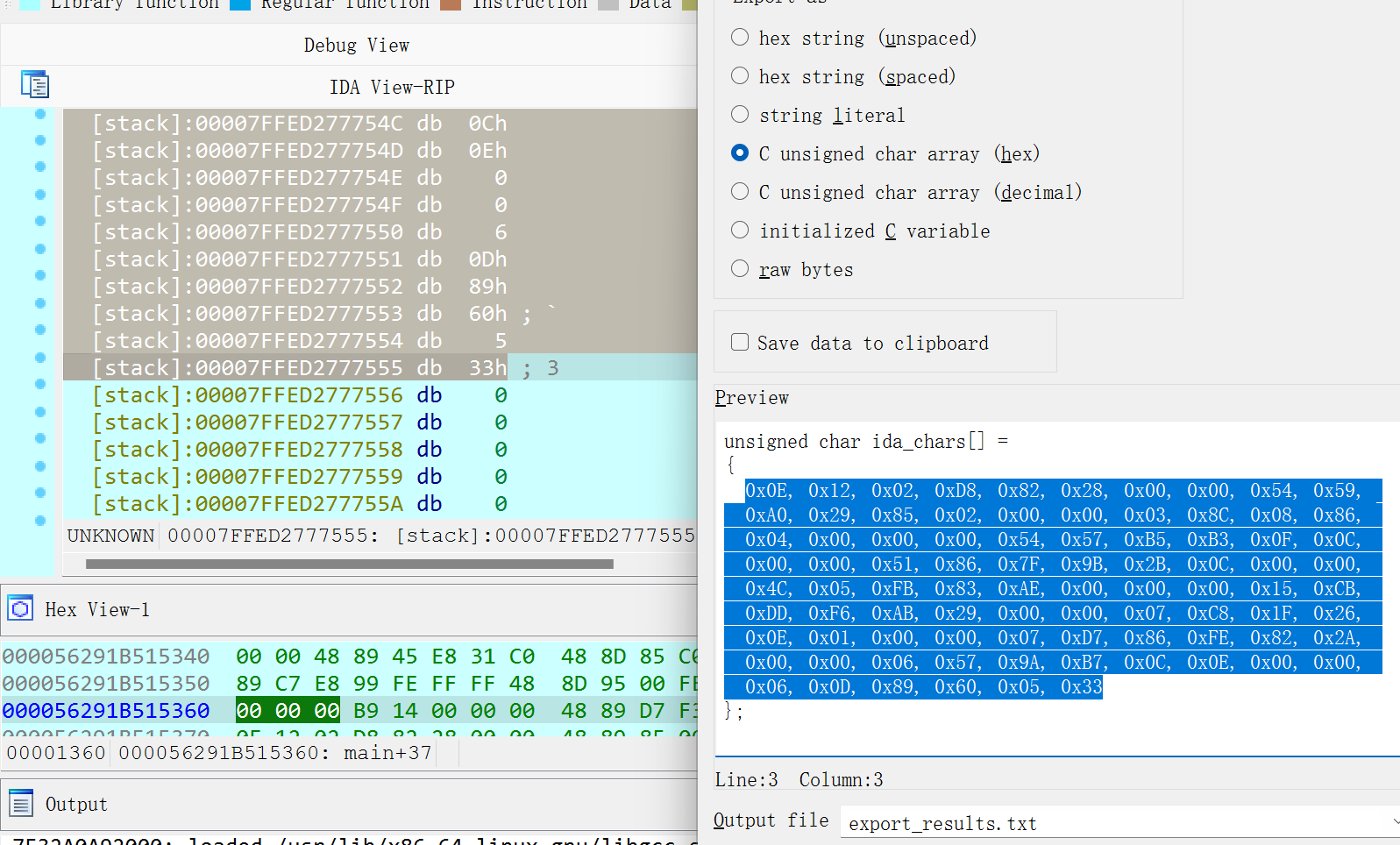 有<<15的存在考虑用z3
有<<15的存在考虑用z3
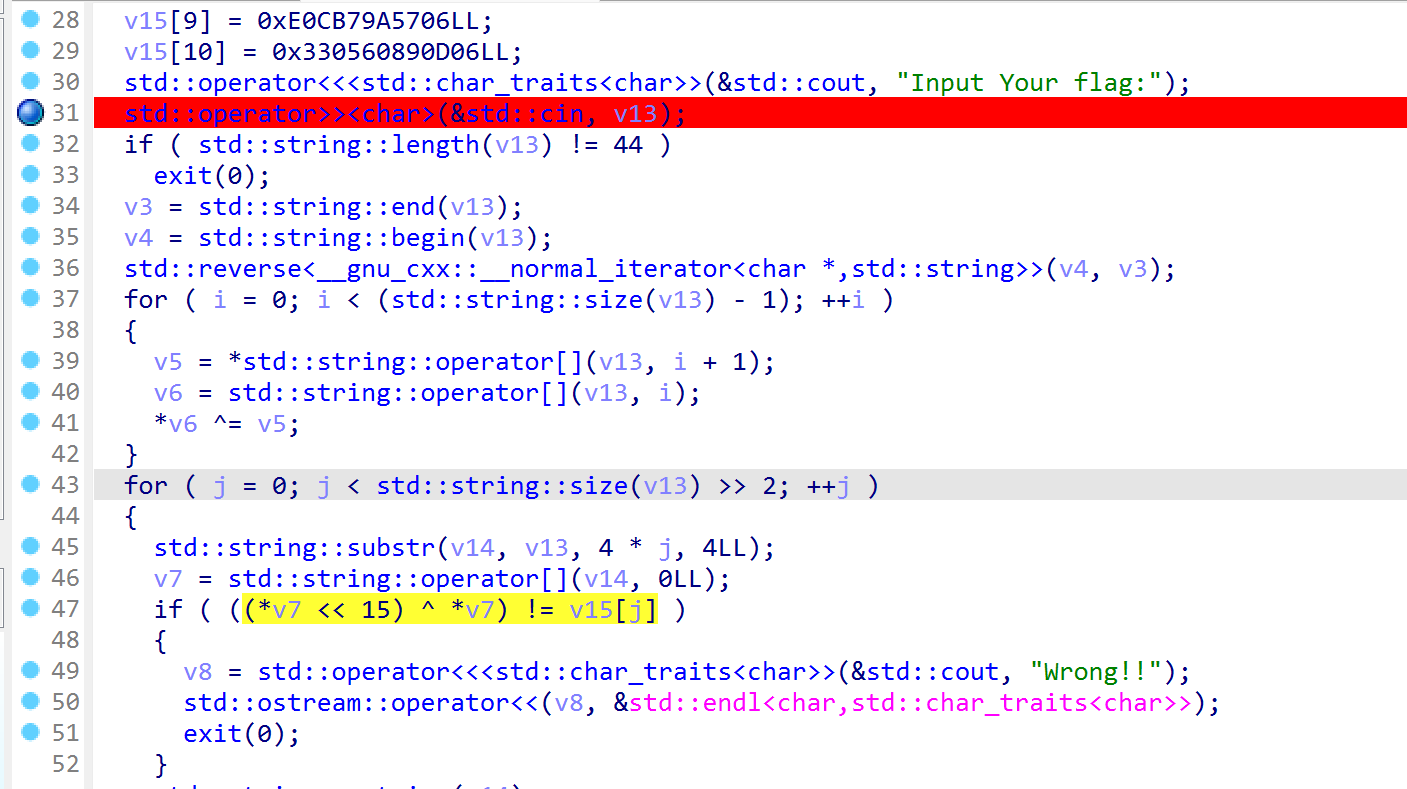
用z3求得v7数组
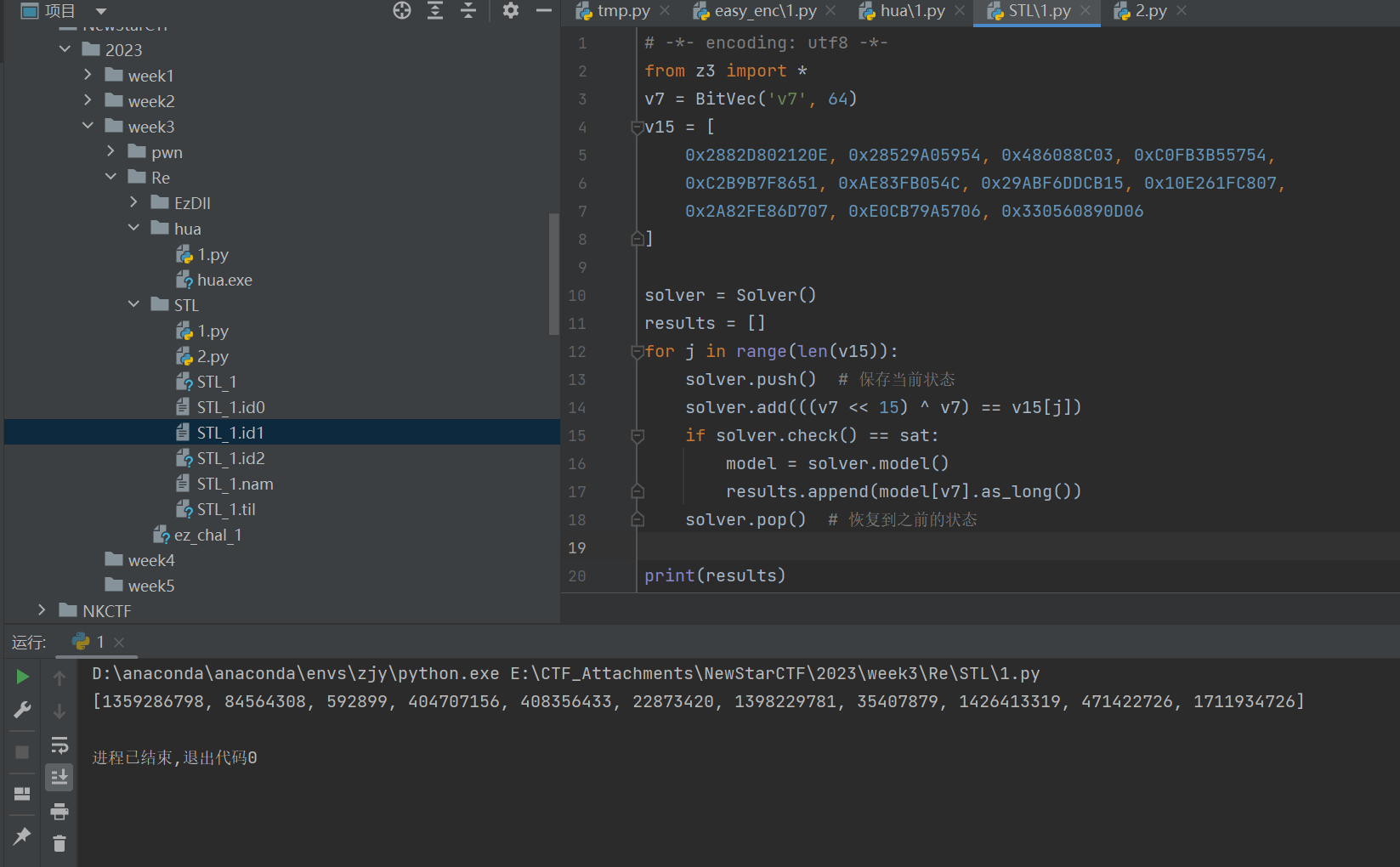
拆成44个字符,相邻异或之后再翻转
1 | |
ezDll
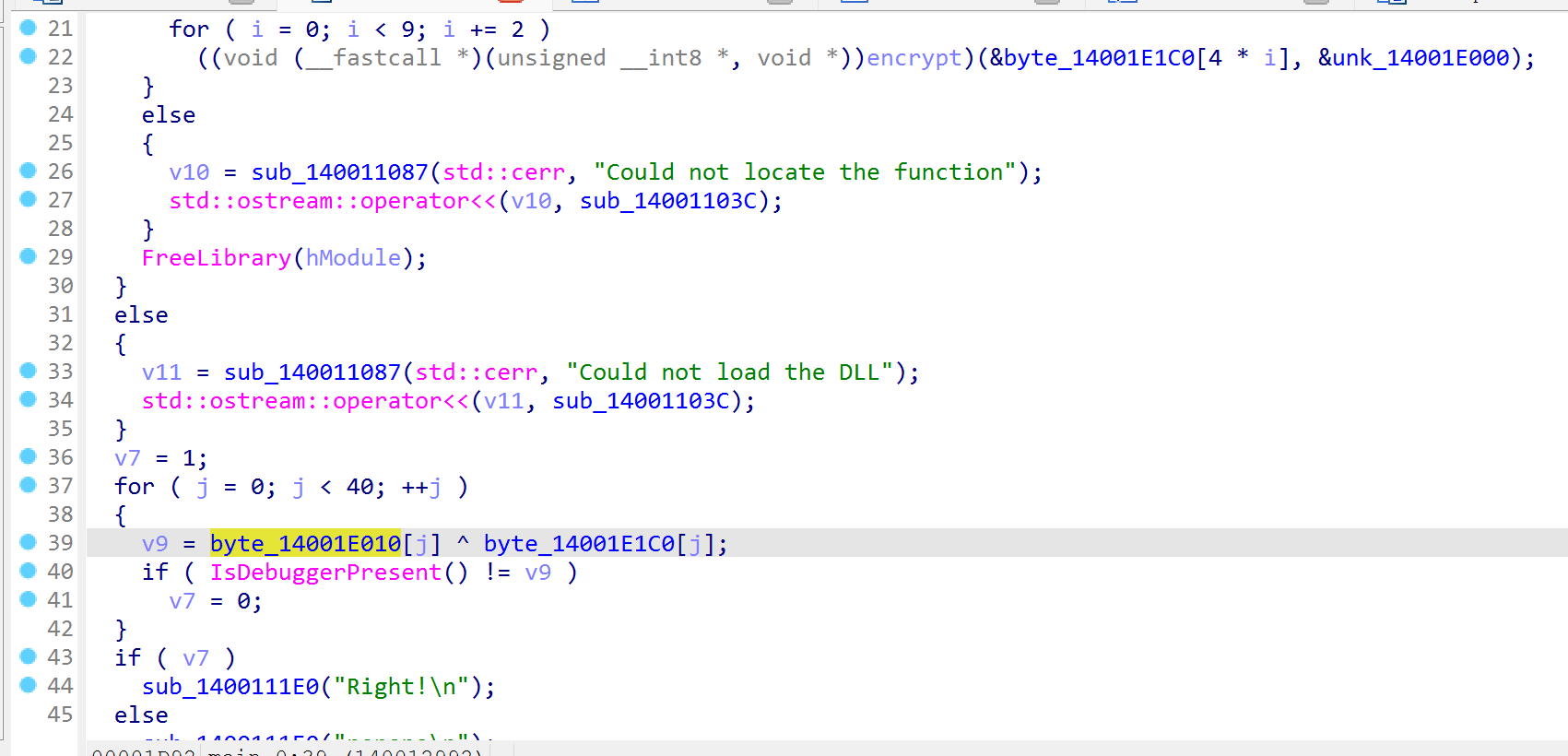
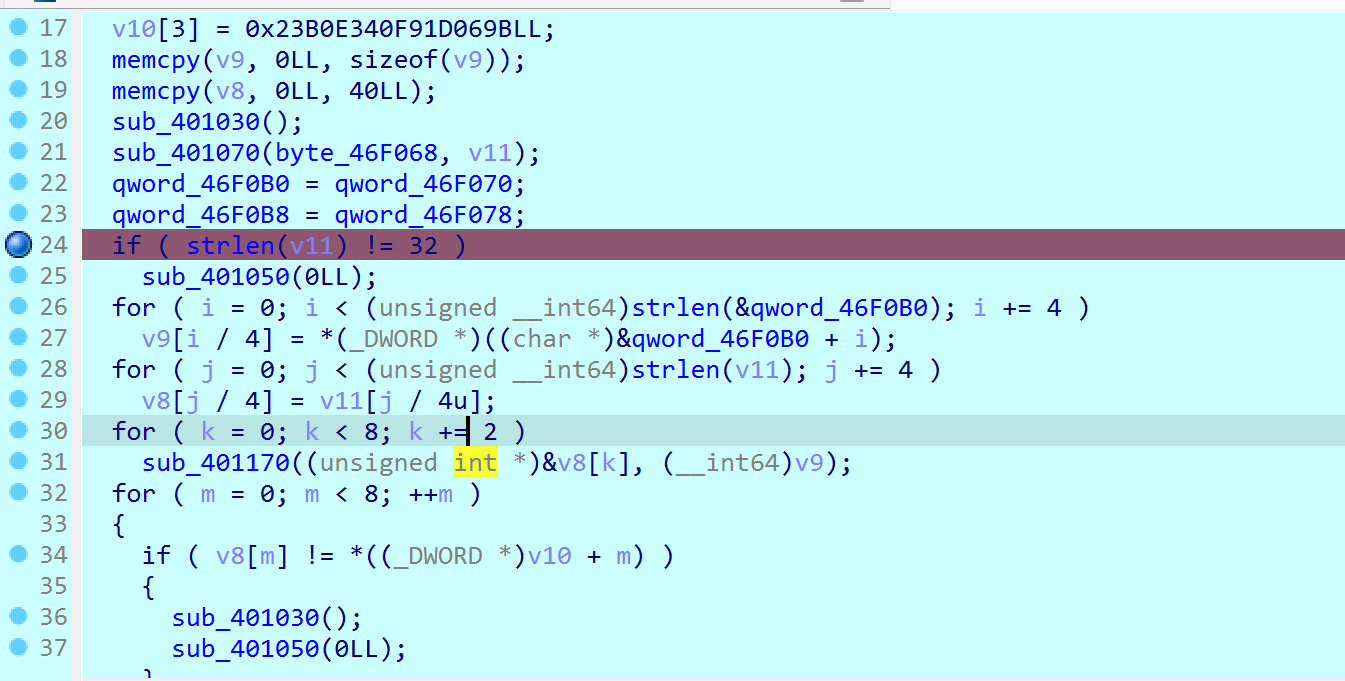
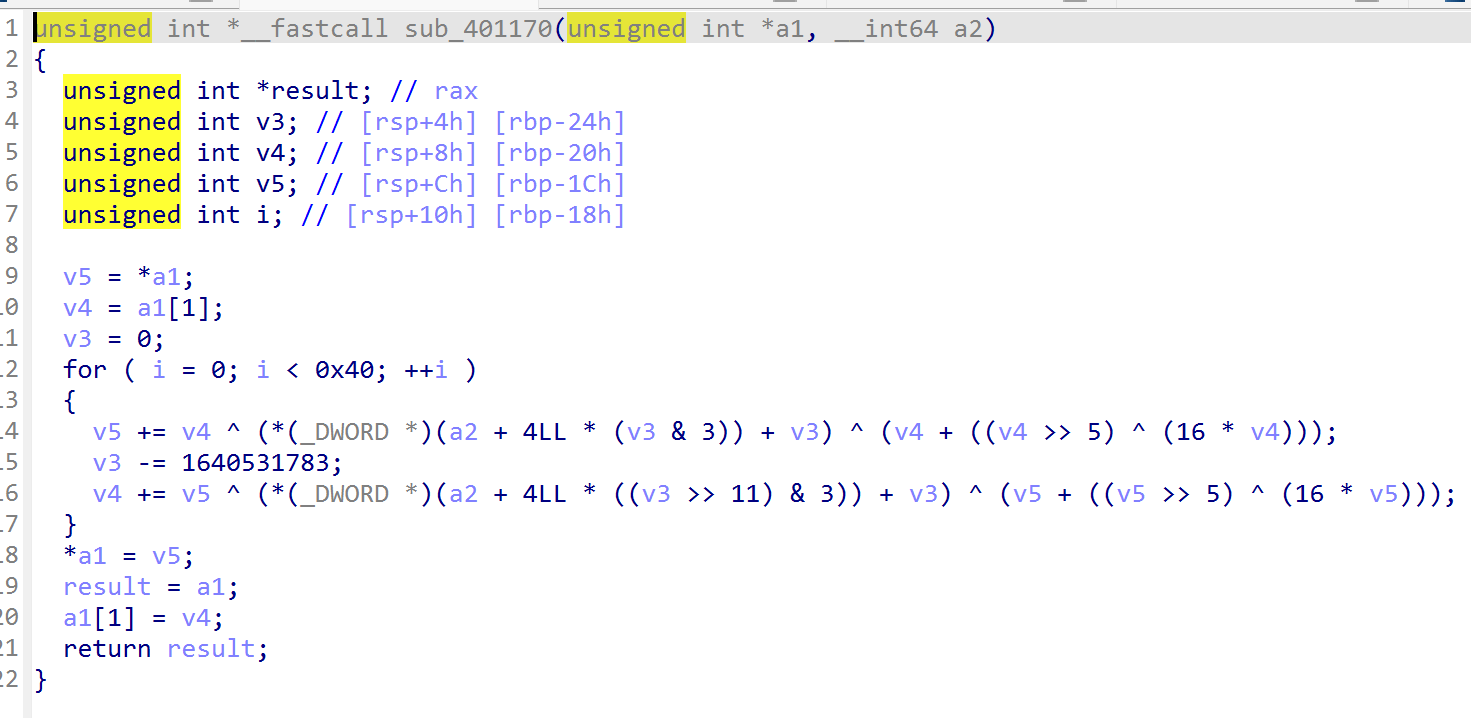
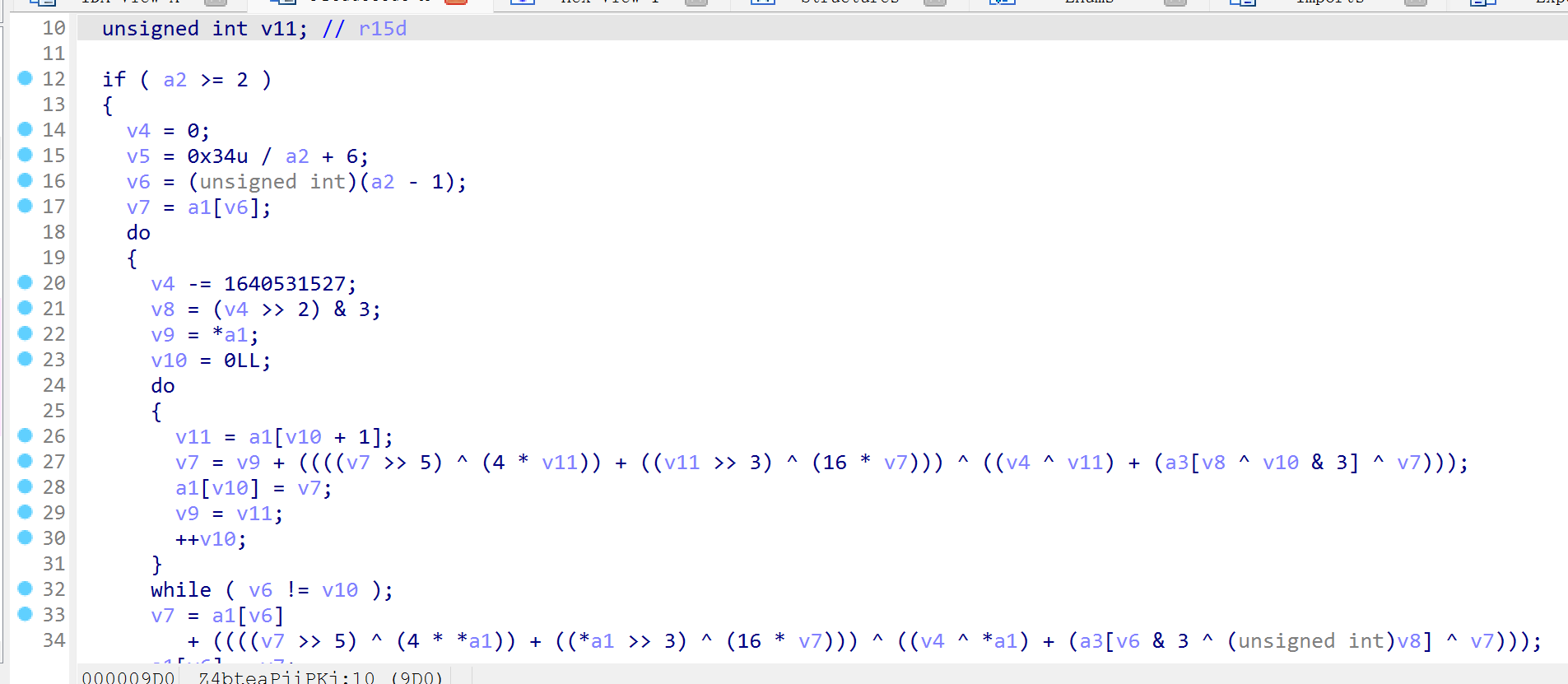
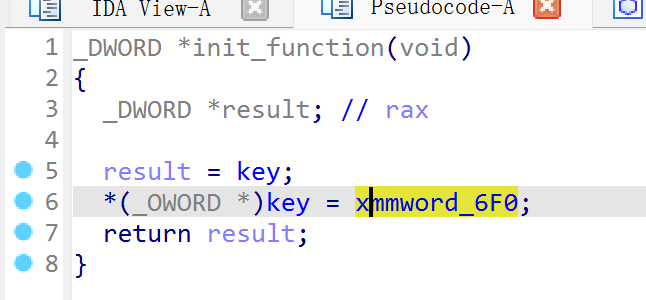
魔改tea
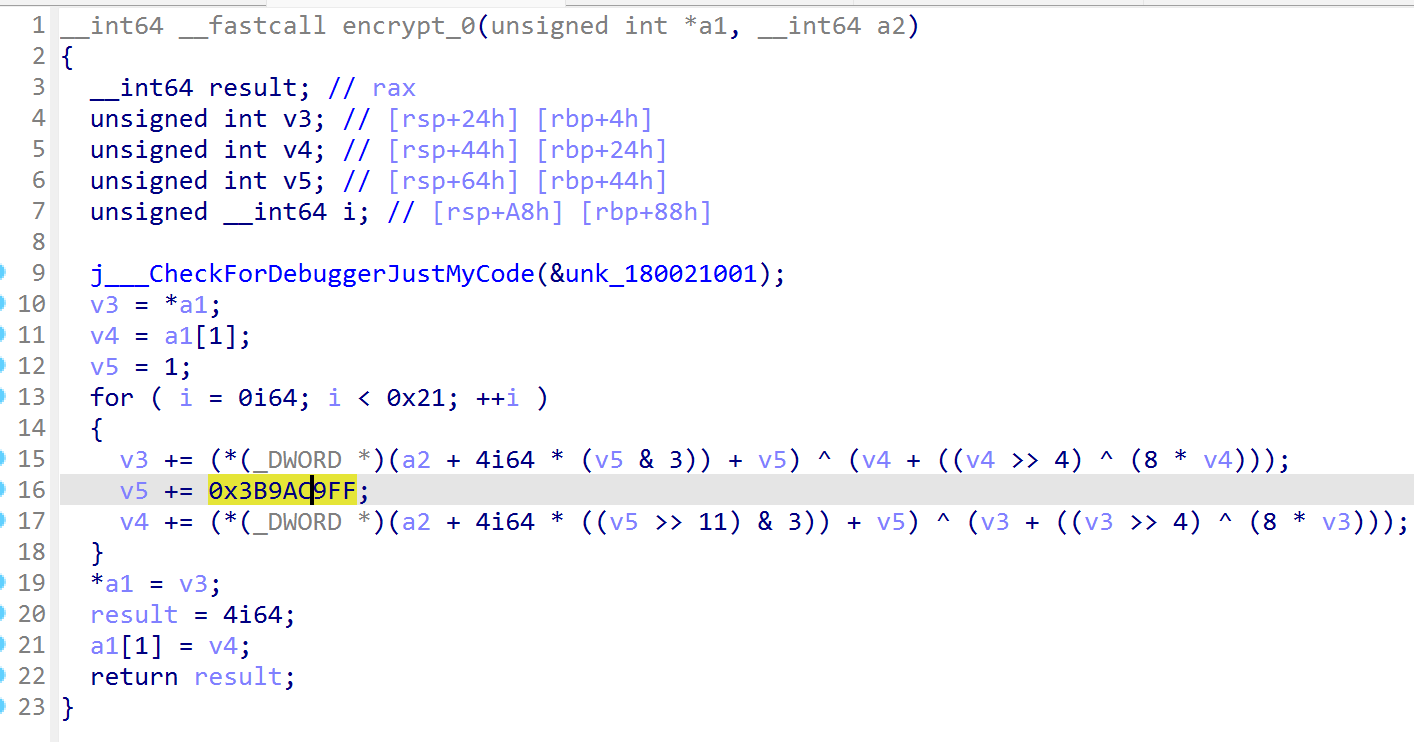
同时注意有反调试,看上面应该是不调试获得正确密文,所以这里第一个key是5而不是6
1 | |
ez_chal
又是魔改tea
调试得到真正的key
1 | |
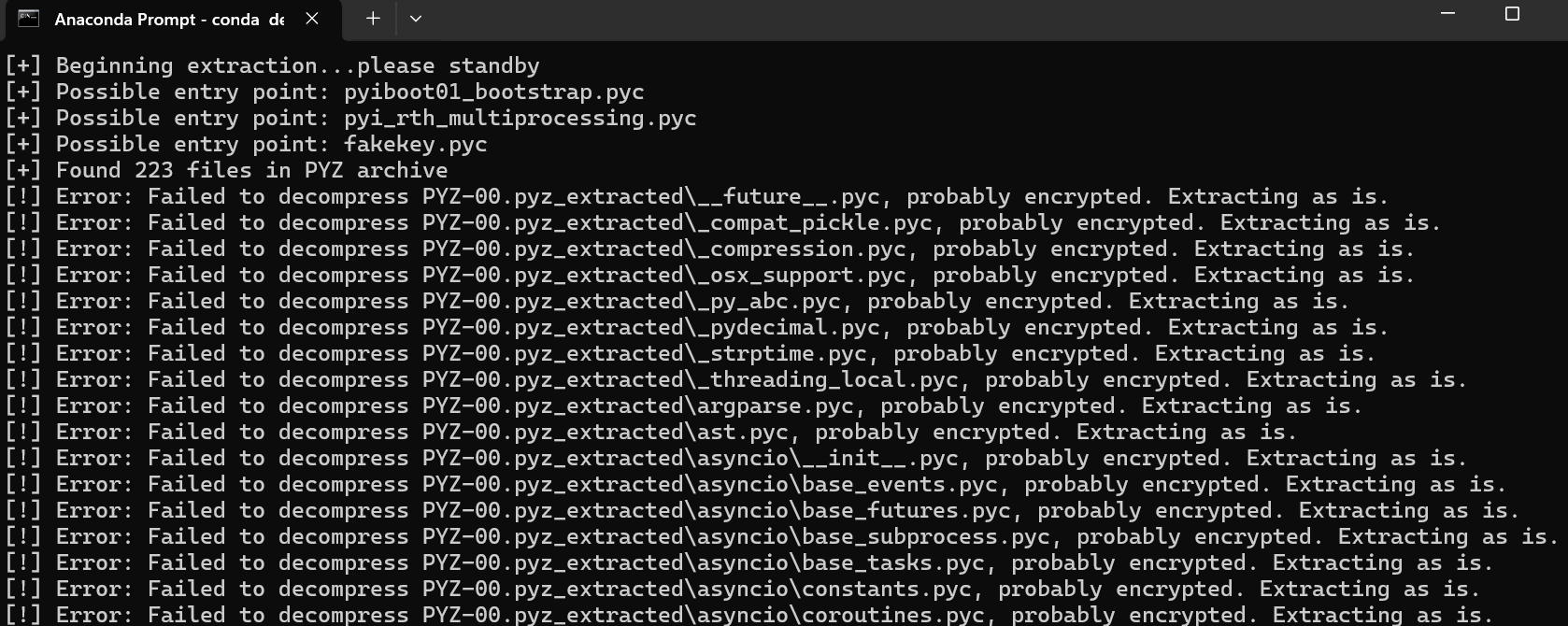
pyexe-1
最后要爆破
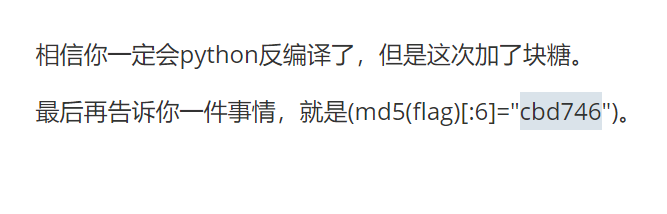
被加密了
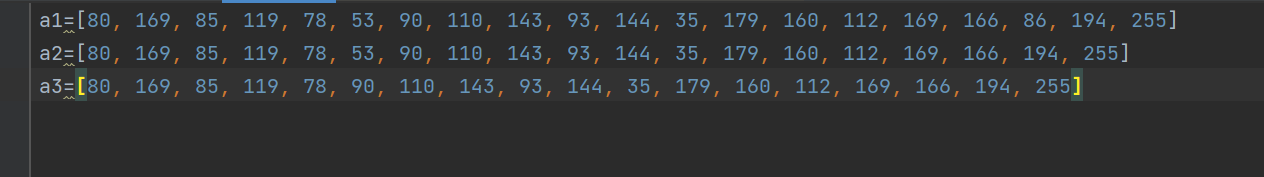
结合pycdc和uncompyle6尝试理解代码逻辑
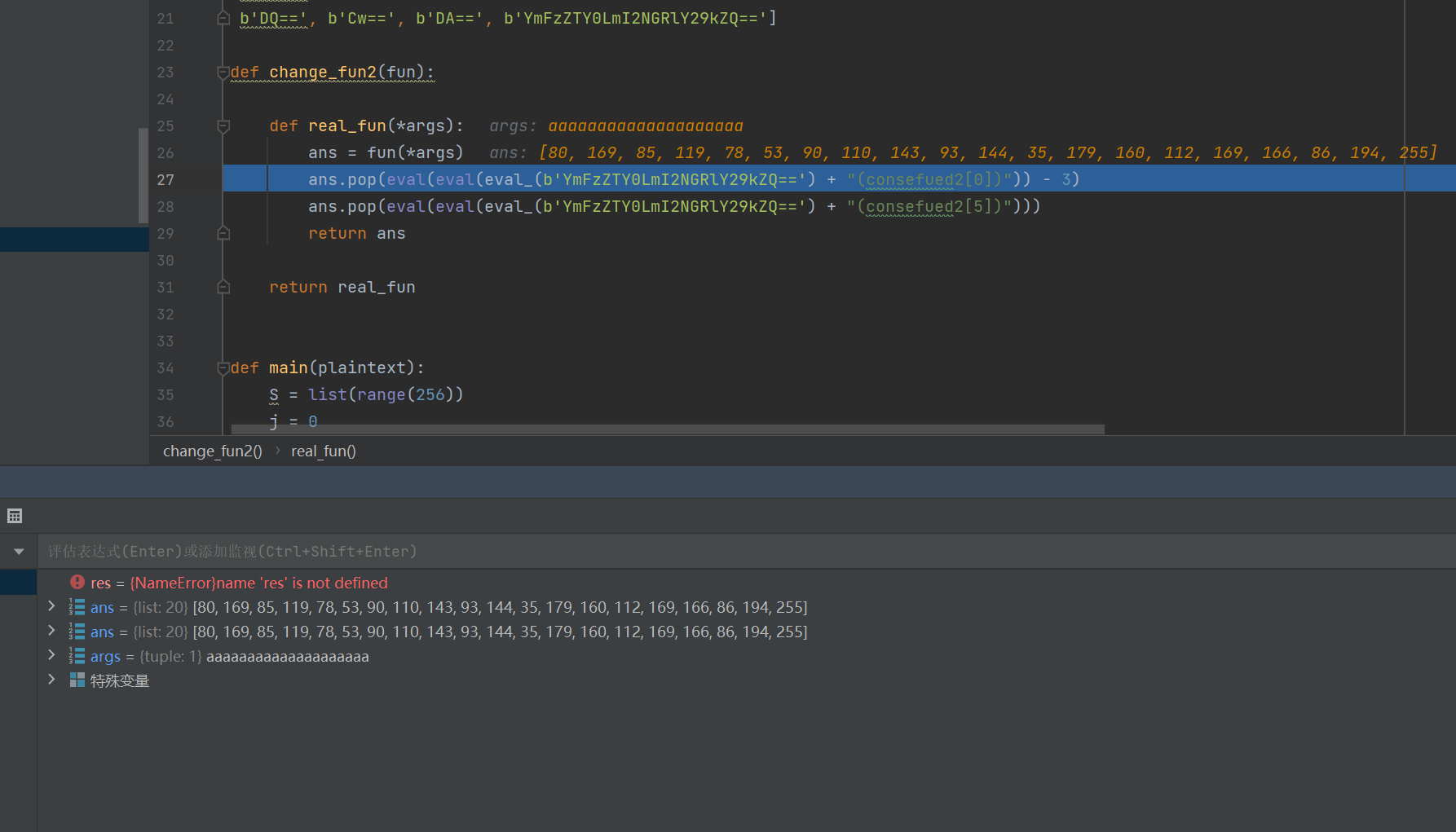
从调试来看应该是删了下标为5和-3的元素,告诉我md5最后应该是要爆破,但是key看了一眼010,不是直接异或,因为被加密的pyc前四位不一样,没思路了
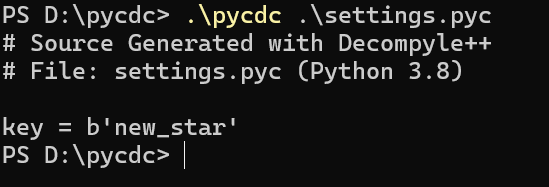
在反编译python生成可执行文件exe时,引用的类库文件经常遇到使用Crypto模块AES算法加密,解包生成的并不是pyc文件,而是加密的pyc.encrypted文件,它无法查看编译。解包完成后将在根目录形成名为 pyimod00_crypto_key.pyc 的文件,将它转为py文件即可查看key文件
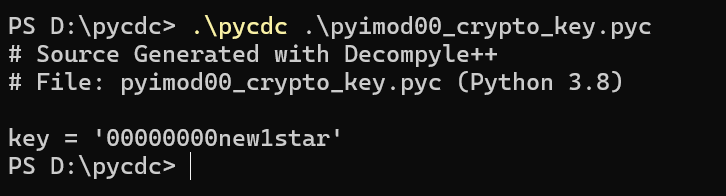
然后用脚本解密,需要注意版本
1 | |
和我想的一样

还是挺牛的
1 | |
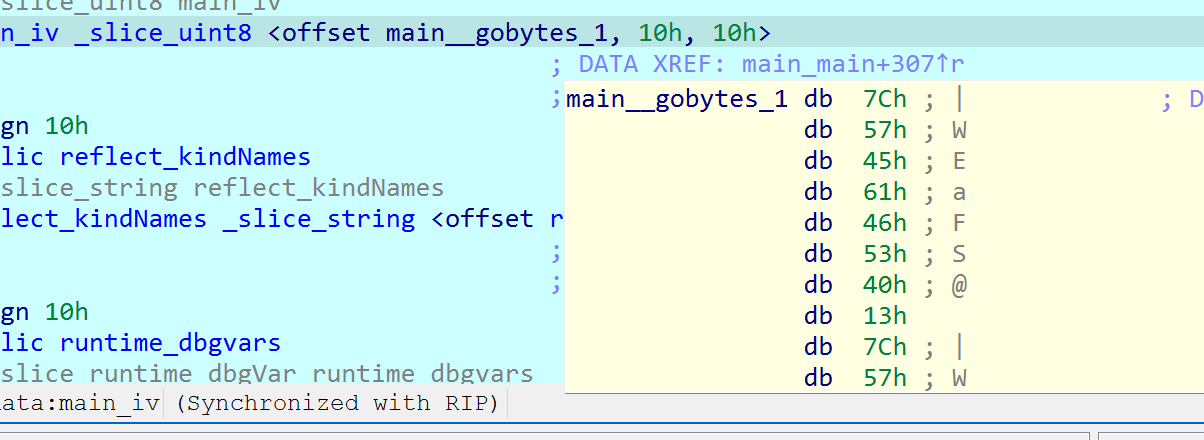
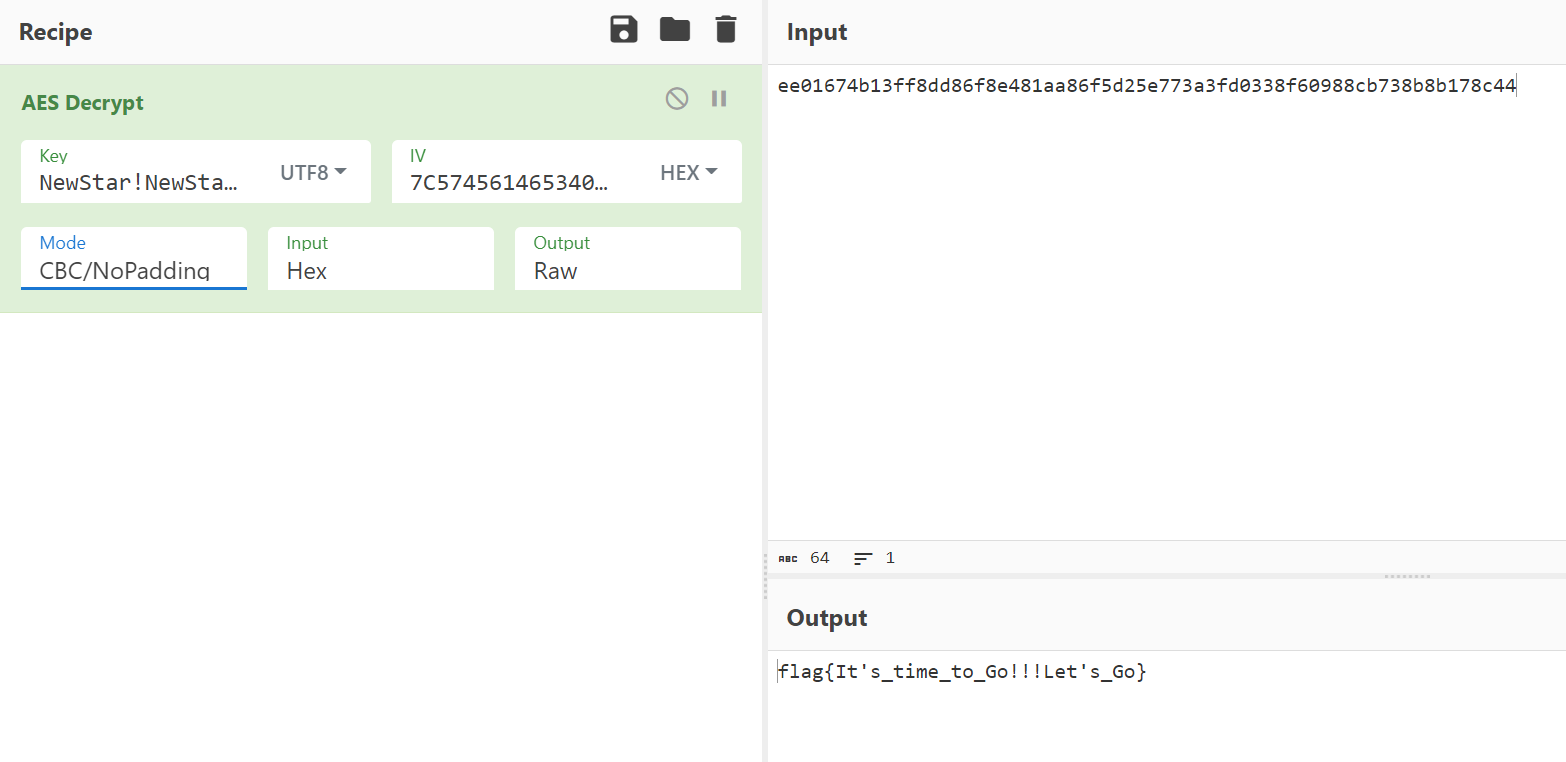
Let’s Go
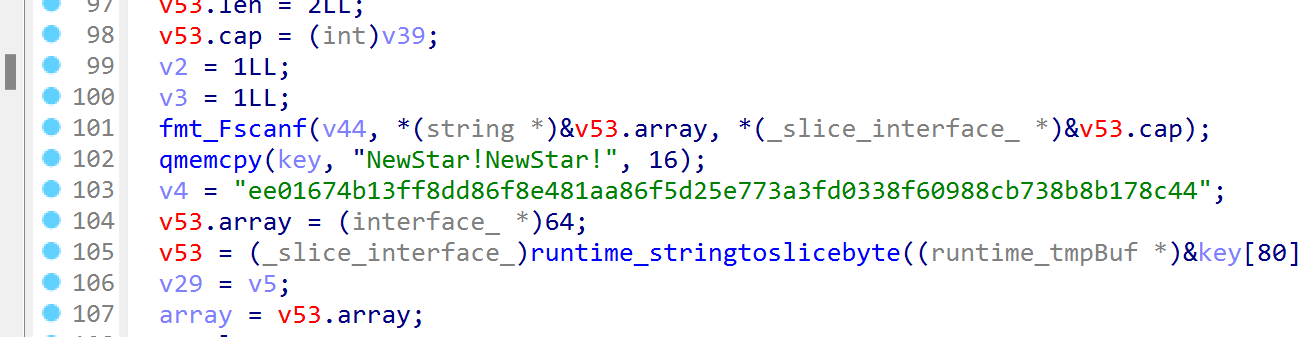
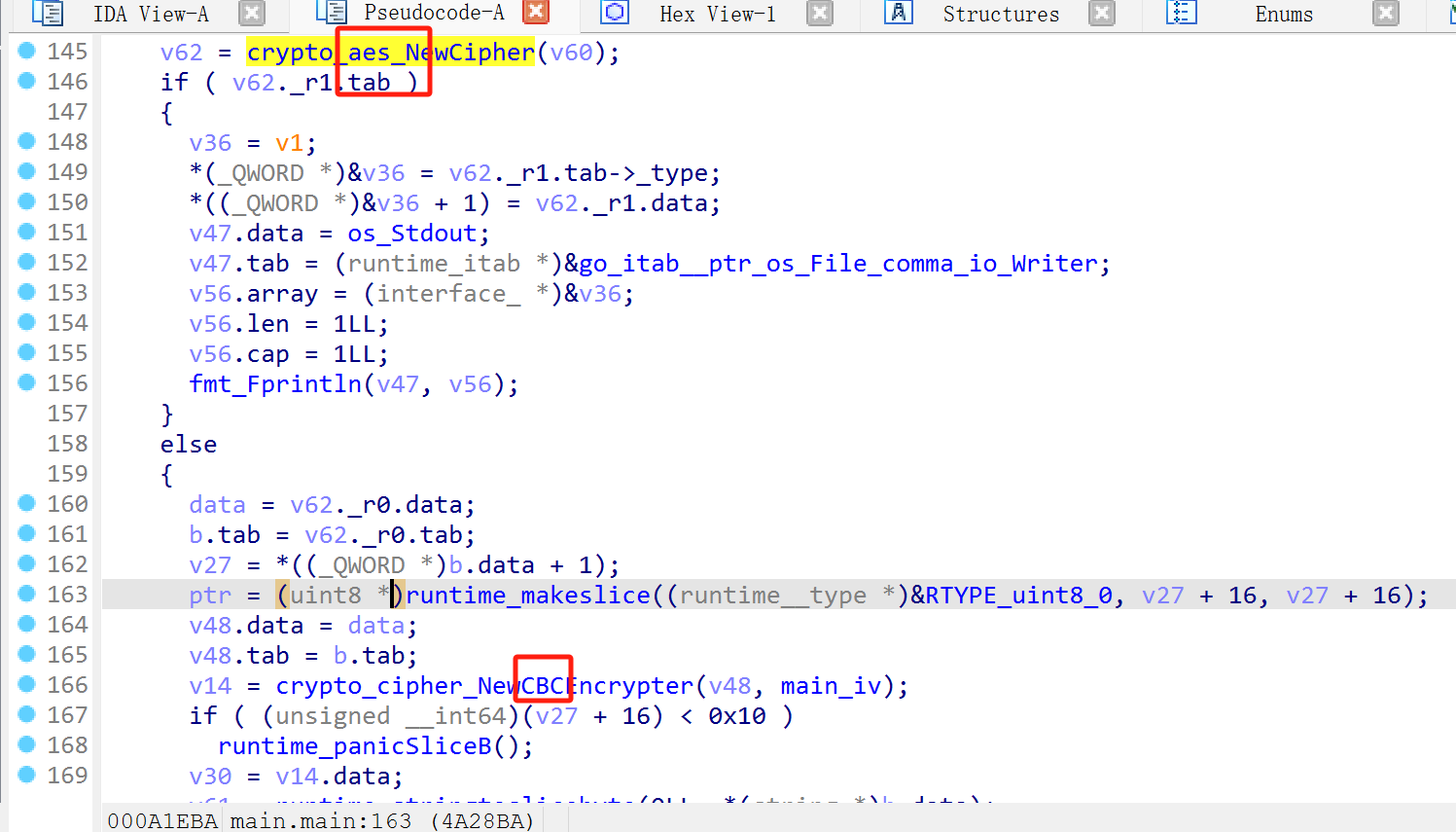
交叉引用iv
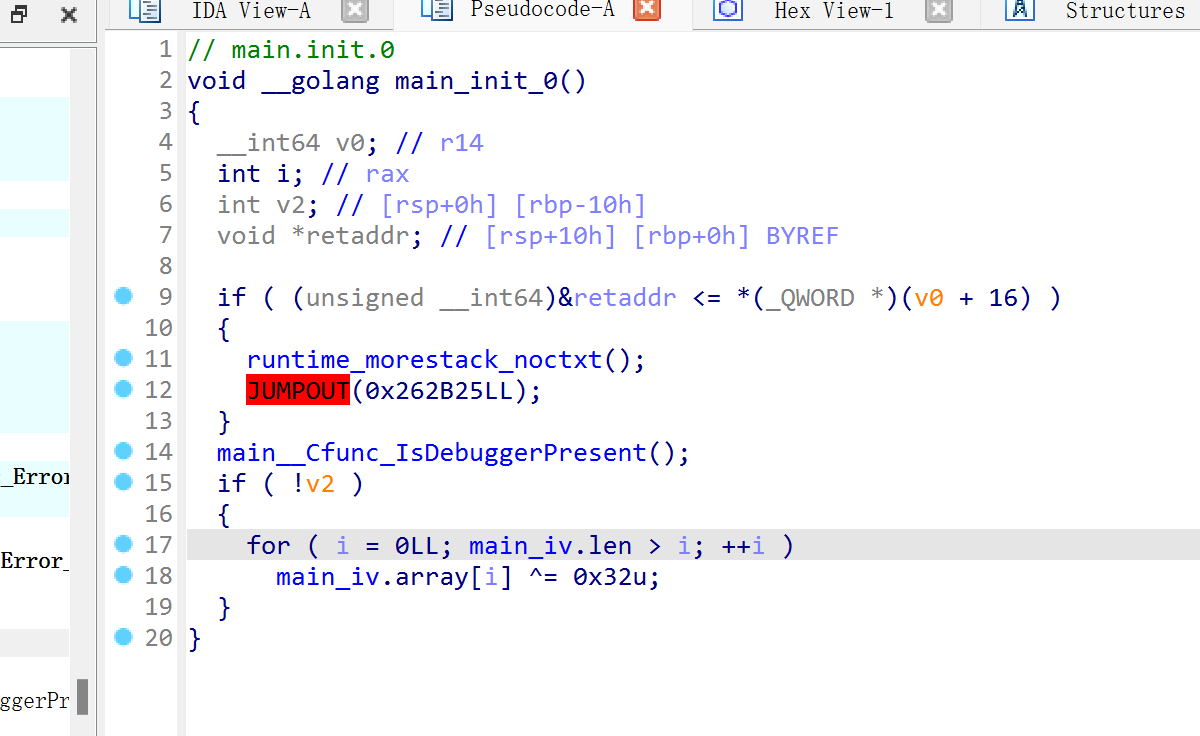
绕过之后得到iv
这题难道是大端序?,反正可以多试试,且nopaddding有和没有还是不一样的
1 | |
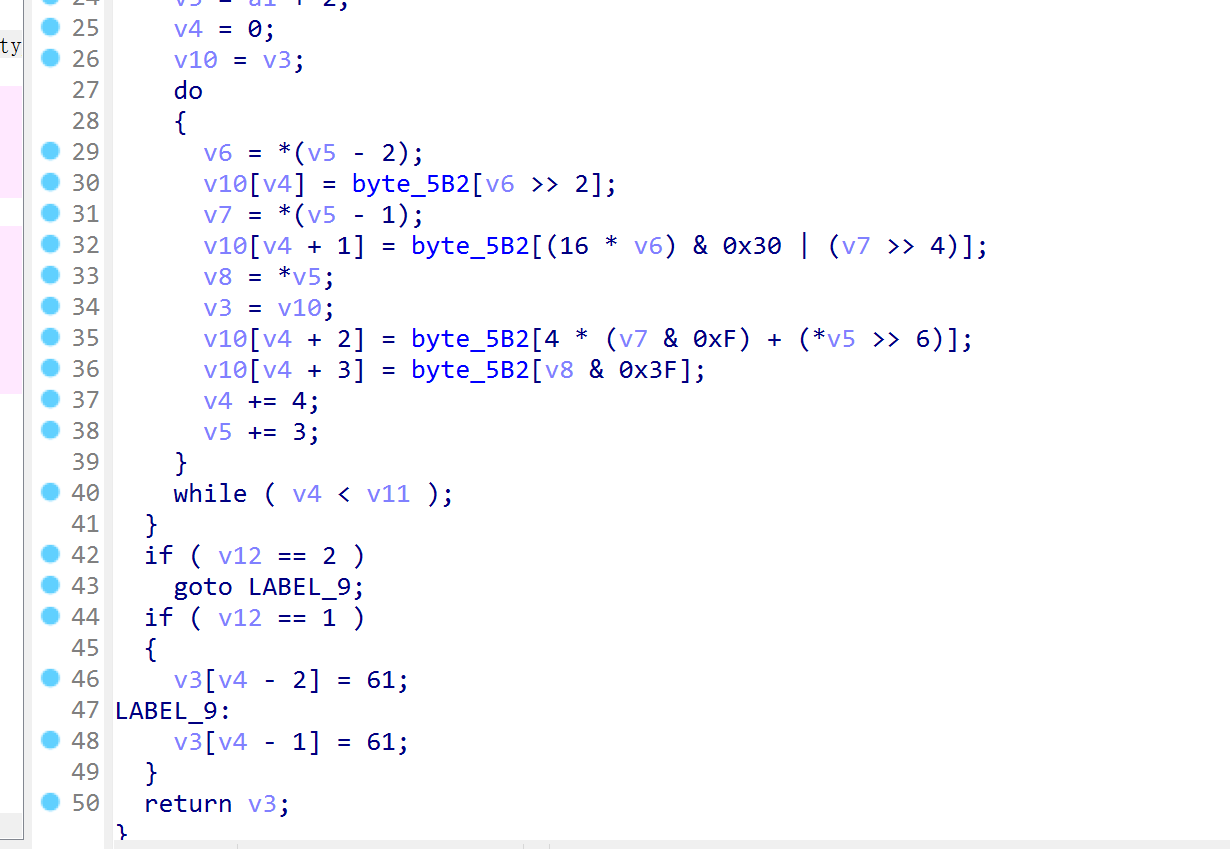
AndroNative-1
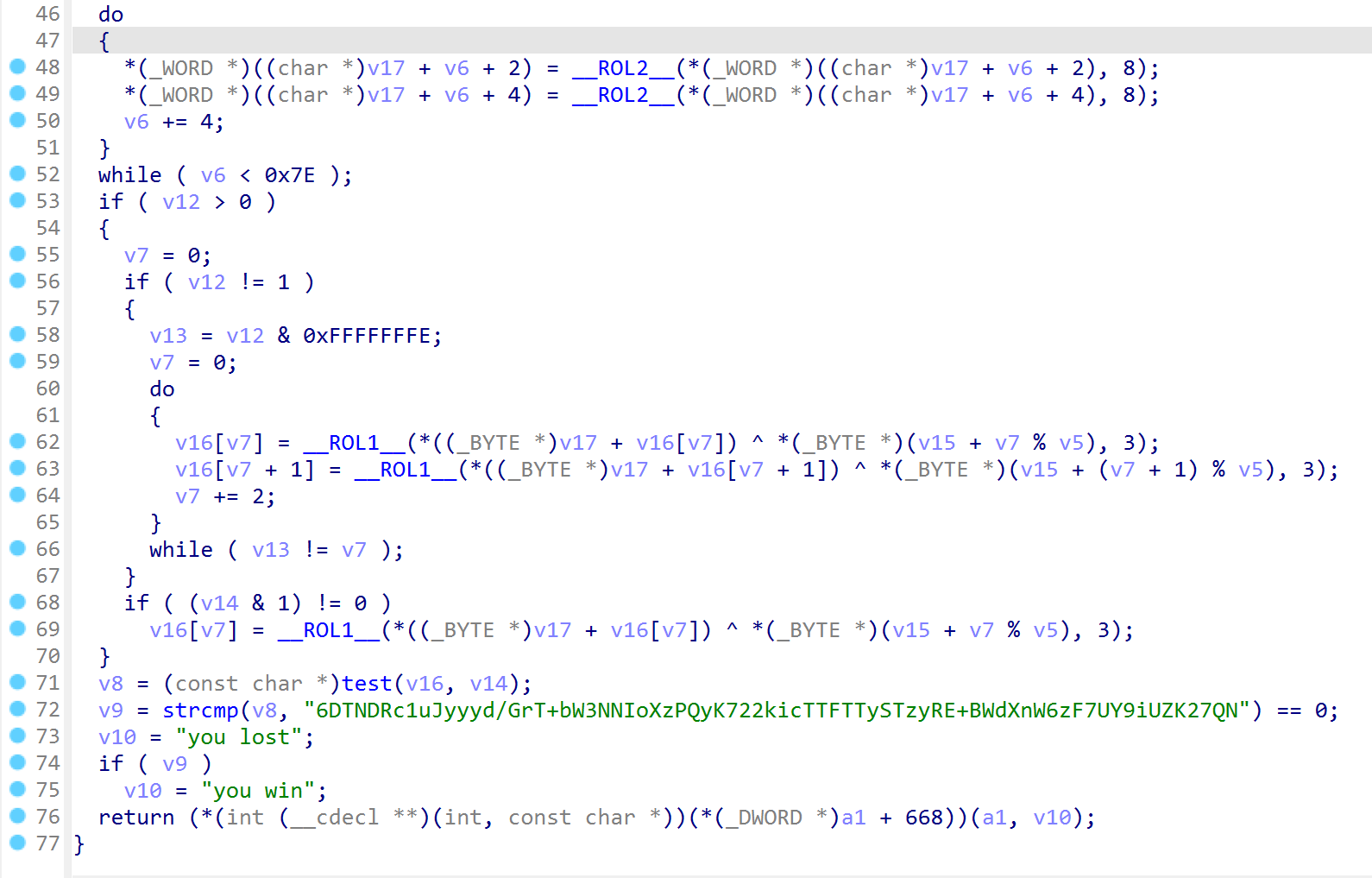
test是base64变表
v22赋完值(0~0xff)后,进行了_ROL2_移位
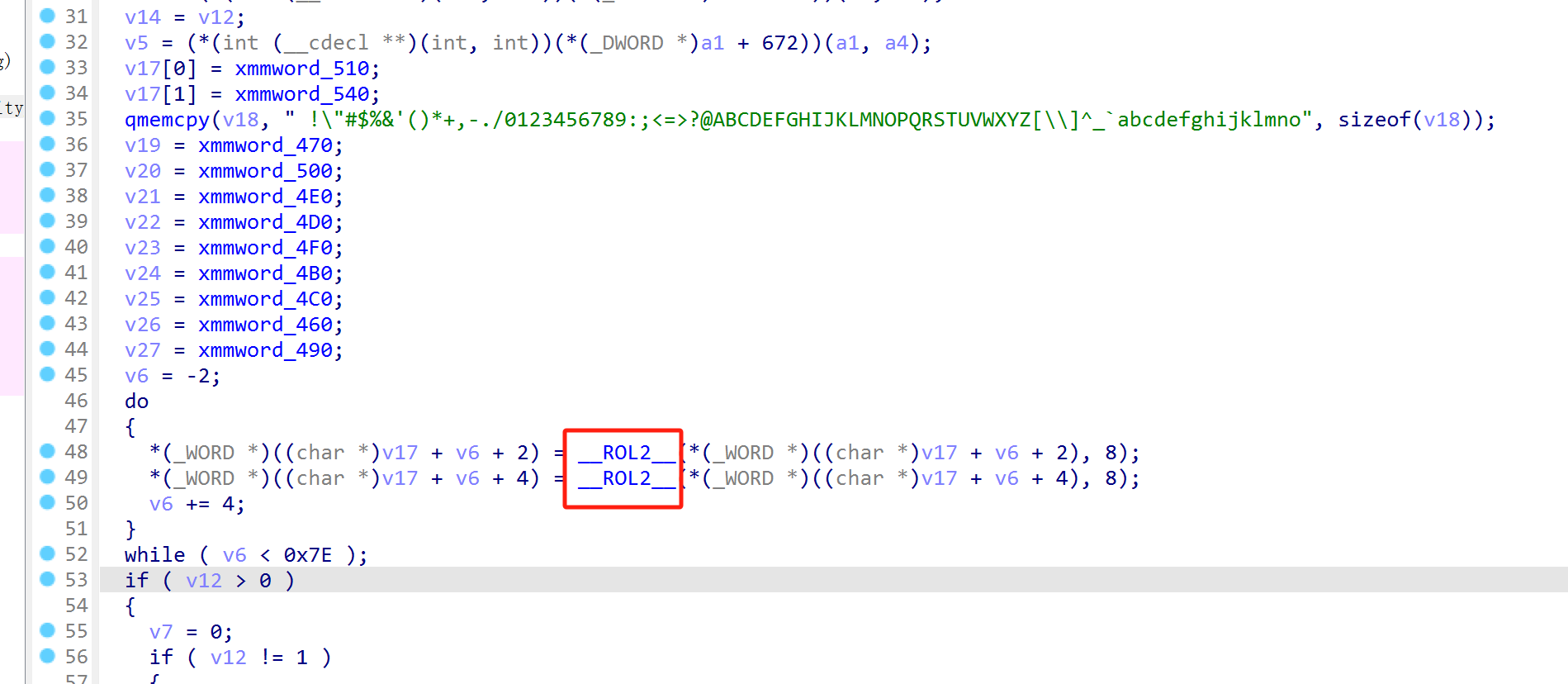
ROL有两个参数:(value, int count)
第一个参数为左移的数,第二个参数为左移的位数,如果第二个参数值为负数,则实际上为循环右移 -count位
该函数的实现细节为:
先得到value的位数,然后count对位数取模。
如果count值大于0,则先右移-count取模的结果,然后在左移取模的结果,得到的两个数相或,即为循环左移的结果;如果count值小于0,先左移再右移
举例来说: value = 0110, count = 6,value为4位数, 6 % 4 = 2,0110先右移4-2=2位,得到0001,然后再左移2位,得到1000,0001 | 1000结果为1001,即循环左移结果为1001
1 | |
之后是ROL1,再异或key
1 | |
2hard2u-1
jeb自动去除BlackObfuscator混淆
两次rc4得到s1


先解tea
1 | |
因为在java字符串传递到jni接口时,采用了GetStringUtfChars,这个函数会自动采用utf-8的解码格式。
我们需要将提取到的utf-8编码的数据转化为对应的Unicode编码
UTF-8编码,是Unicode的一种可变长度字符编码,是Unicode的一种实现方式,又称万国码;UTF8使用1~4字节为每个字符编码,相对于Unicode 固定的四字节长度,更节省存储空间。UTF-8字节长度与Unicode 码点对应关系如下:
一字节(0x00-0x7F)-> U+00~U+7F
二字节(0xC280-0xDFBF)-> U+80~U+7FF
三字节(0xE0A080-0xEFBFBF)-> U+800~U+FFFF
四字节(0xF0908080-0xF48FBFBF)-> U+10000~U+10FFFF
字符U+0000到U+007F(ASCII)被编码为字节0×00到0x7F(ASCIⅡ兼容)。这意味着只包含7位ASCIl字符的文件在ASCIⅡ和UTF-8两种编码方式下是一样的。而所有大于0x007F的字符被编码为一个有多个字节的串,每个字节都有标记位集,常用汉字基本上都被编码成三字节
1 | |
Pwn
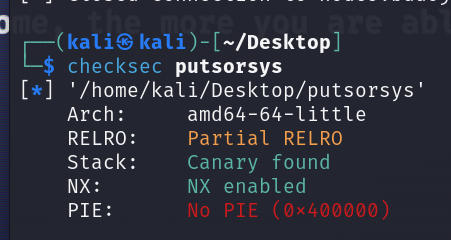
putsorsys
got表可修改,泄露基址之后直接getshell
1 | |
srop
第一个syscall是write,这里没有syscall_ret只有syscall@plt
到时候返回给rax
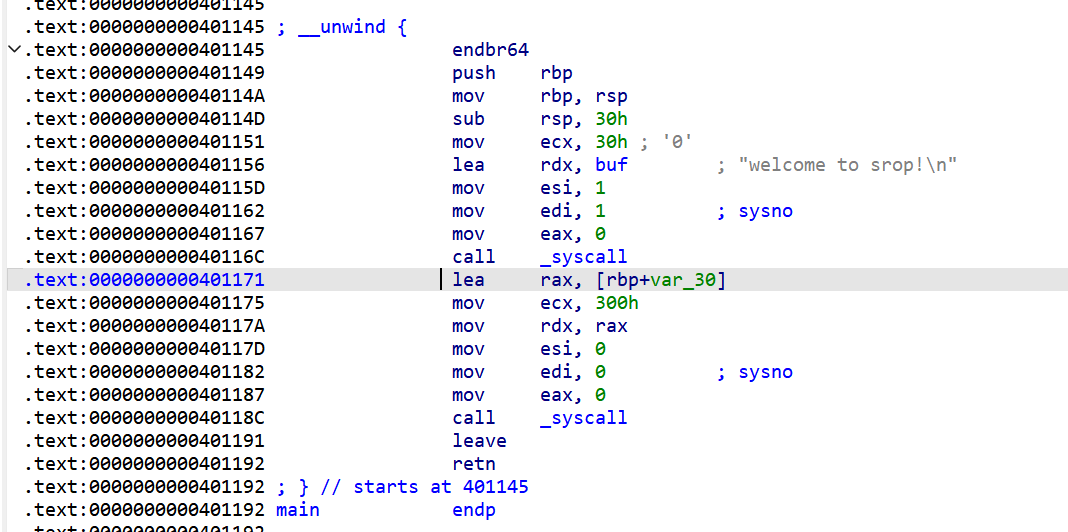
栈迁移之后一次SROP
1 | |
也可以两次SROP
1 | |
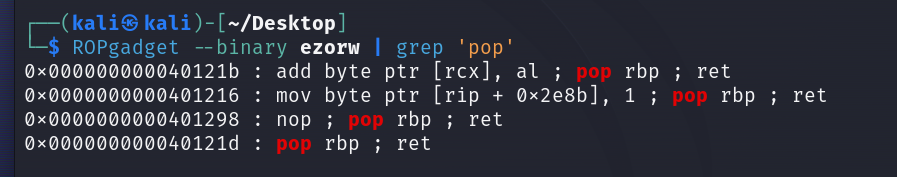
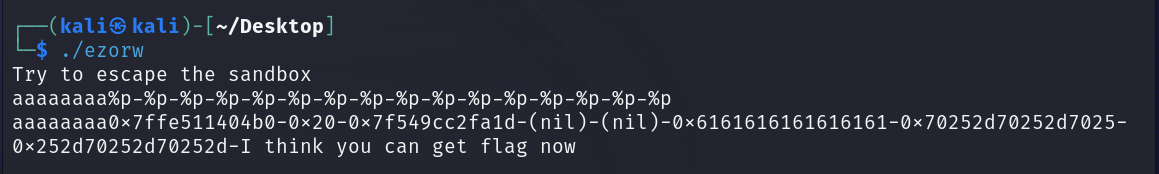
ezorw-1


格式化字符串泄露canary,然后orw读flag
mmap参数:0x1000 代表 4096 字节(4KB),这是一个典型的内存页面大小;7 表示读、写和执行权限的组合;50表示请求创建一个匿名映射,并强制将其放置在特定地址;后两个参数通常为默认值,可以忽略
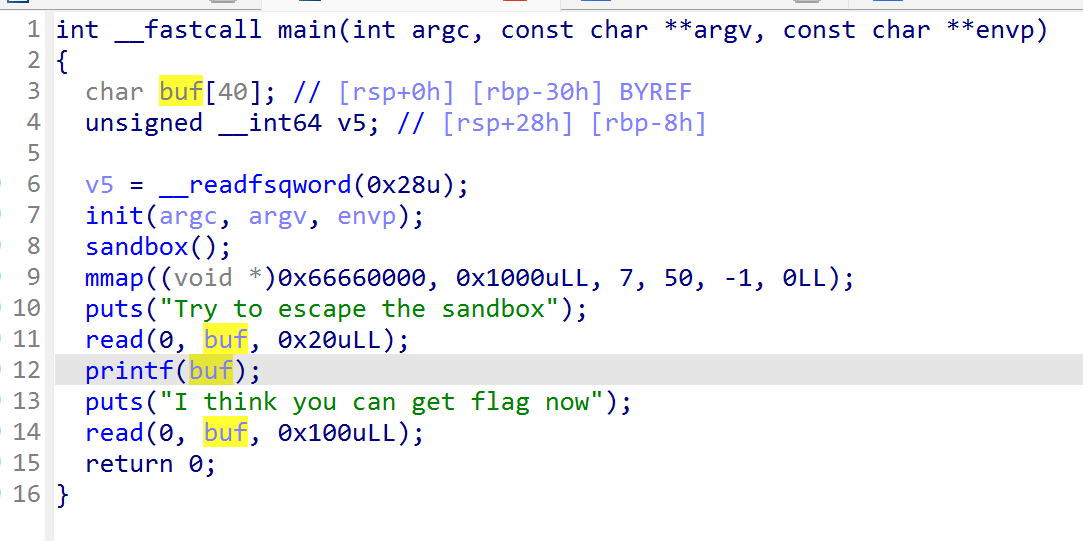
canary偏移为0x28/8+6=11,原有的gadget很少,需要在libc中寻找用于rop的gadget
格式化字符串是第六个参数,put_got是第八个参数
1 | |
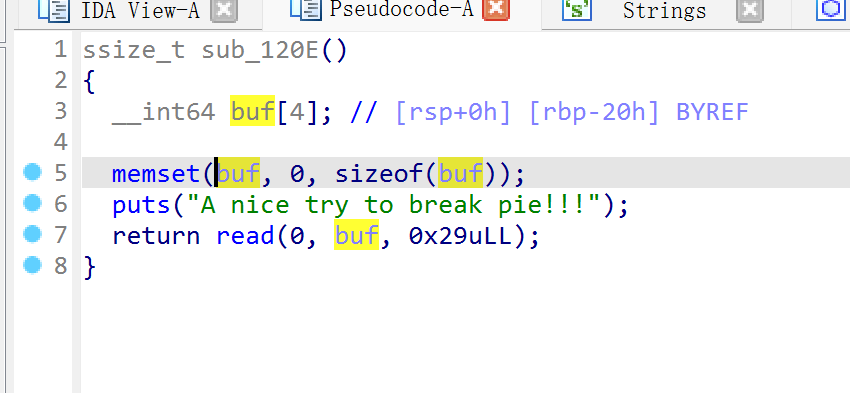
stack_migration_revenge-1
和之前相比这次没有泄露栈地址
没开pie,把栈迁移到bss段上
用lic.address不用管base,puts的bss比system的高0x50
1 | |
dlsolve
只有read
目的是伪造一个名字,got,plt项让程序自动按字符串去找相应的libc然后调用
1 | |
Week4
Re
easy_js
1 | |
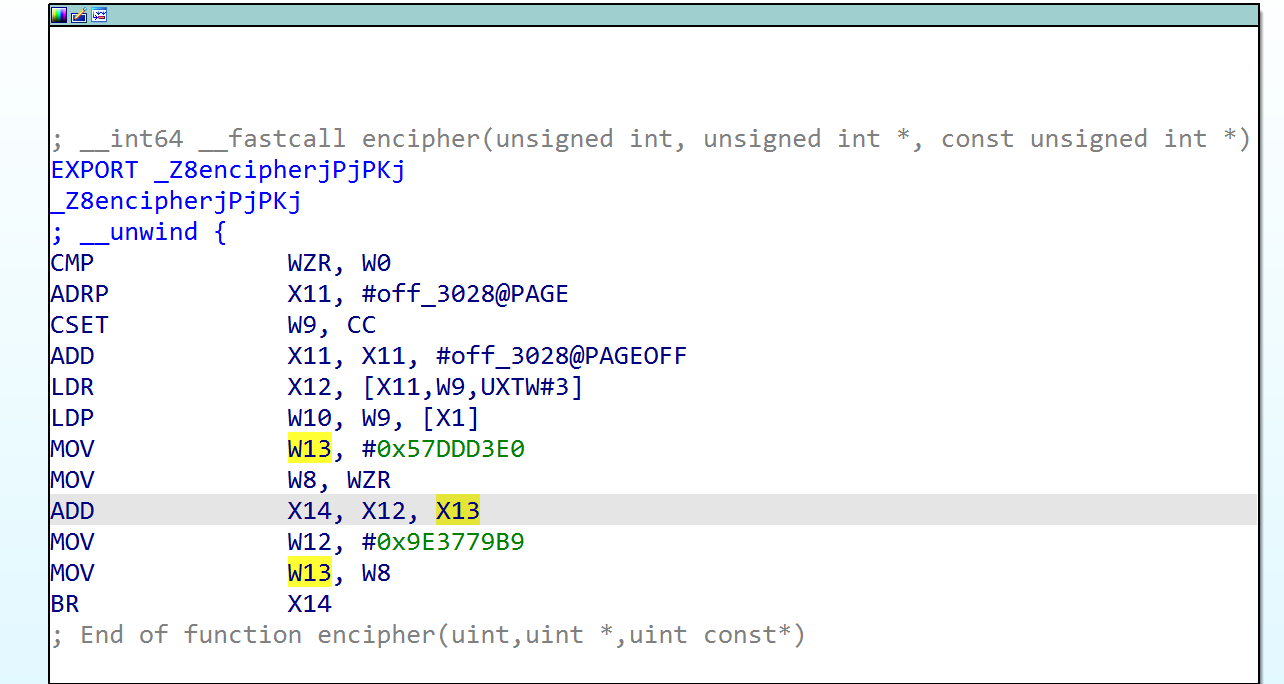
茶
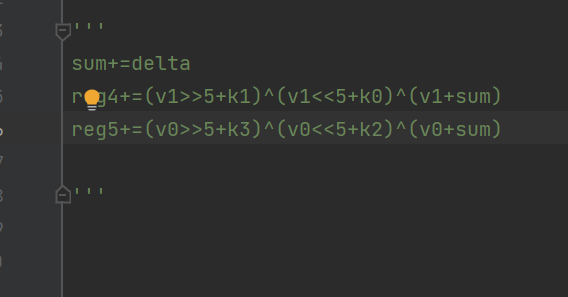
用VM模拟tea
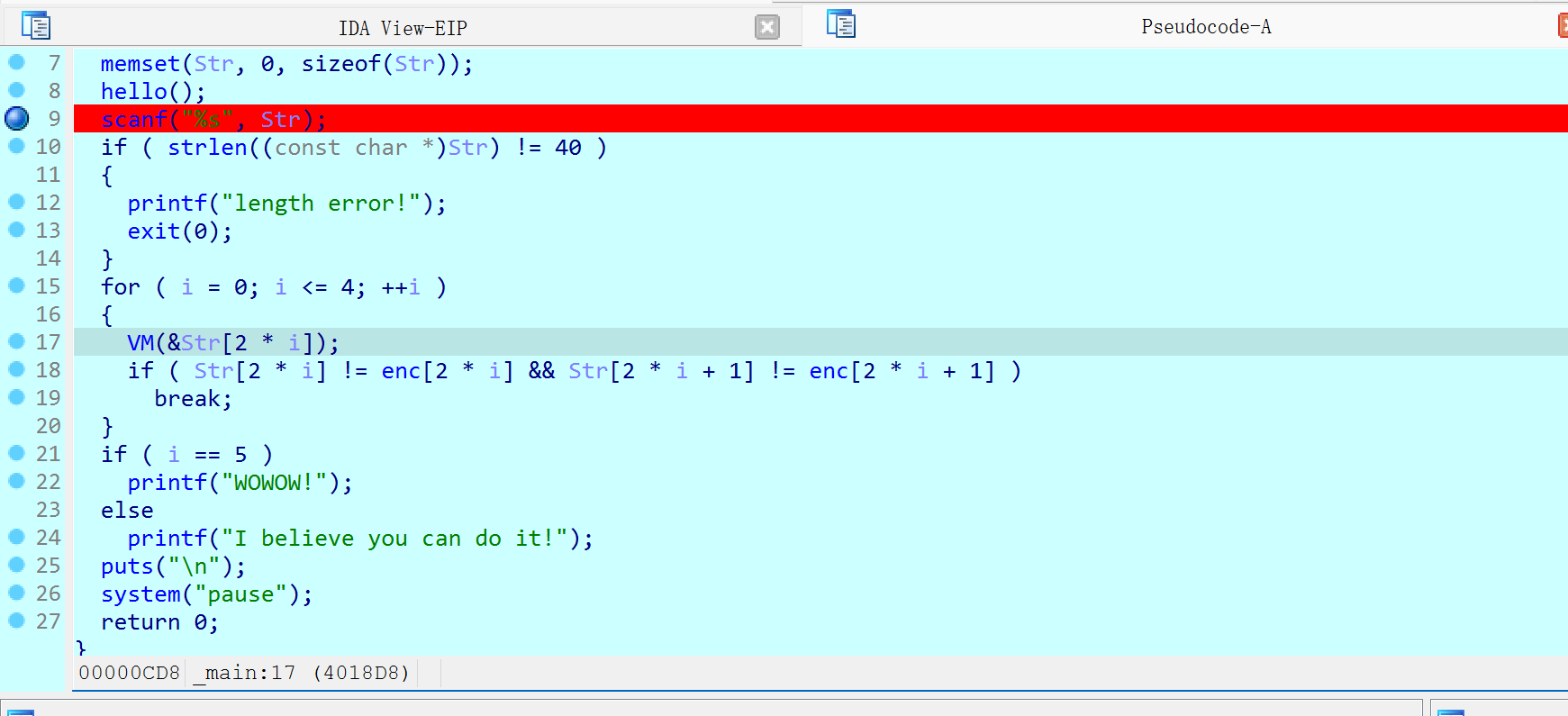
得到delta=0x9e3779b9
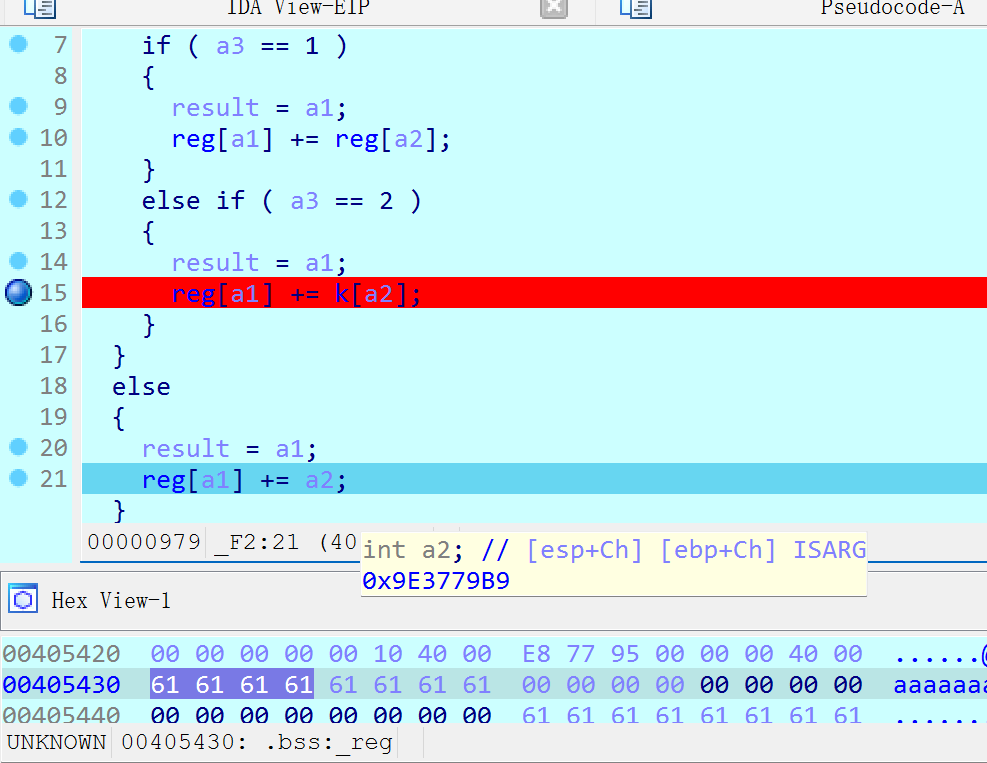
dd是双字类型,k=[2,0,2,3]
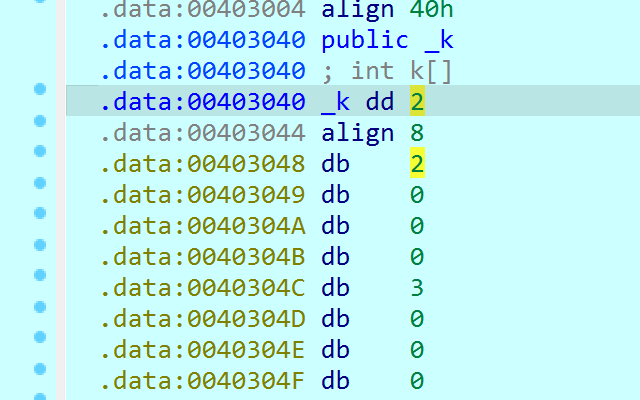
提取opcode
1 | |
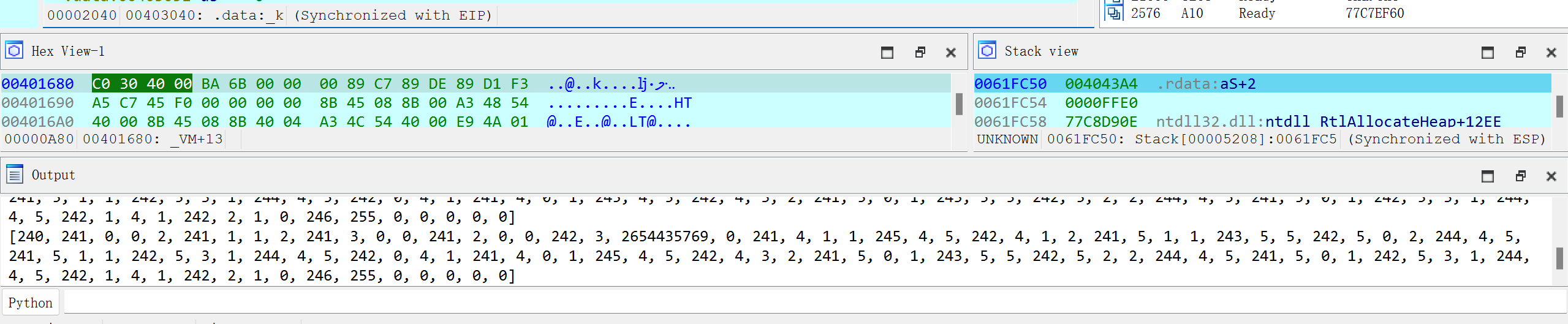
抄一下并打印得到汇编
1 | |
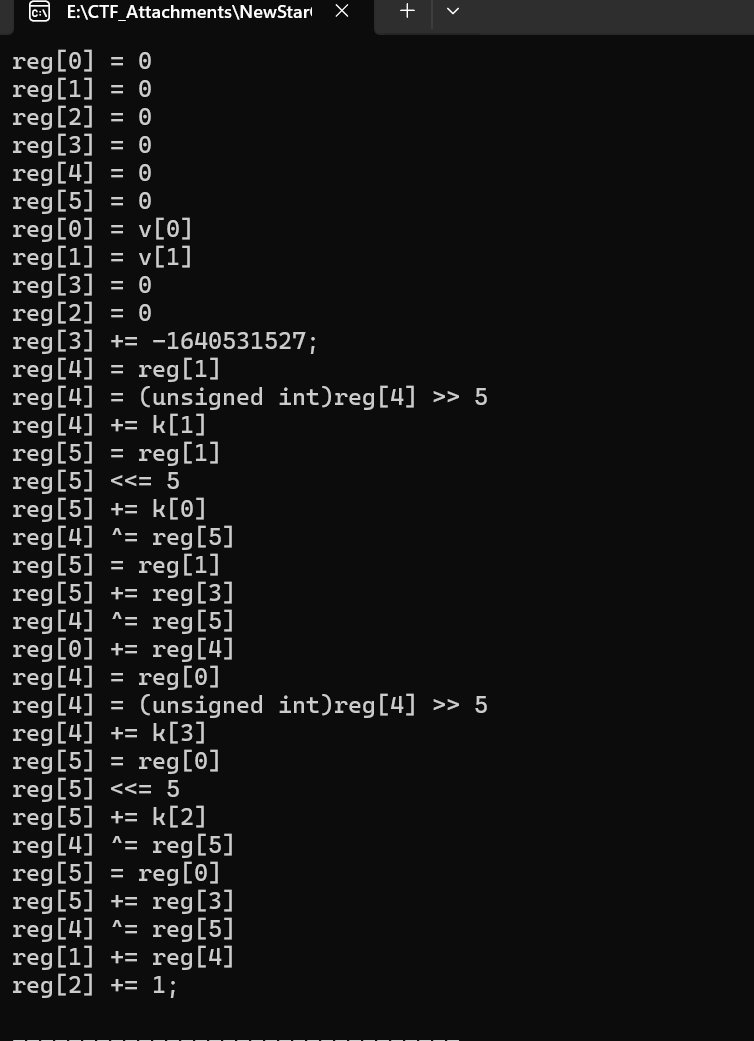
分析一下得到算法
1 | |
iwanarest
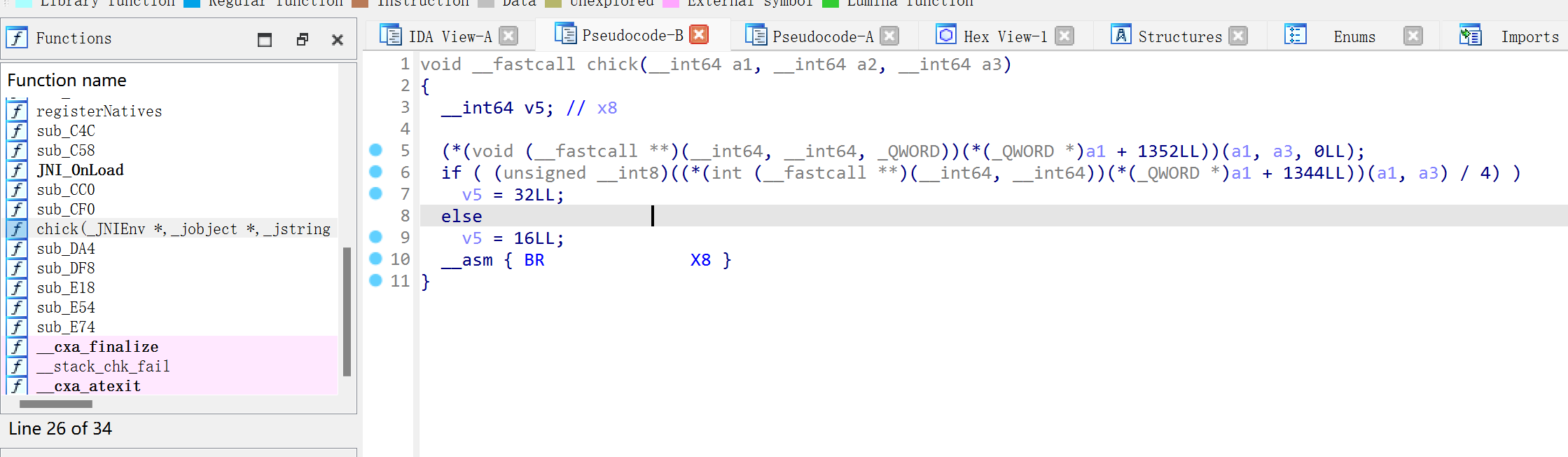
采用了动态注册的方式去注册native层函数
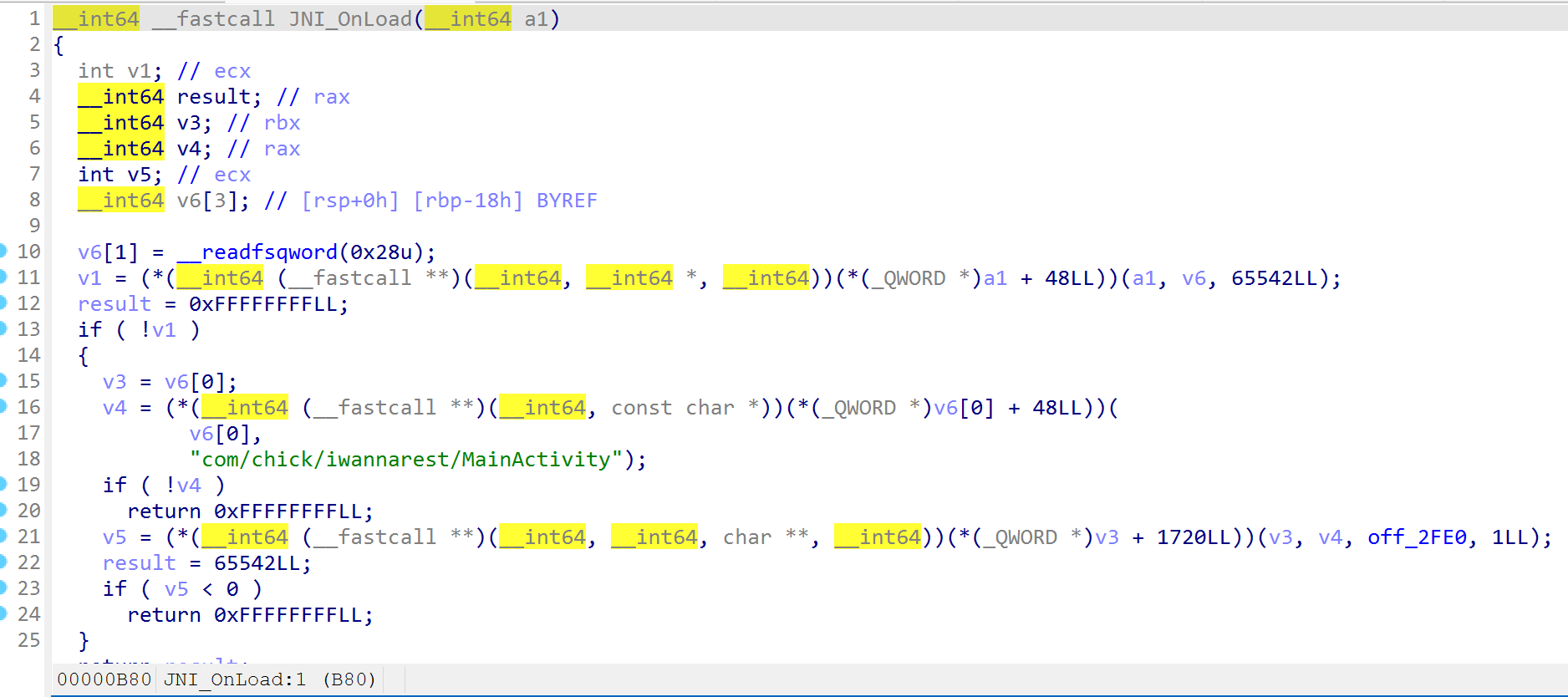
xxtea
key被修改了
1 | |
简单的跨栏
同样是动态注册
java字符串传递到jni接口时,采用了GetStringUtfChars,这个函数会自动采用utf-8的解码格式
我们需要将base64解密后的utf-8编码的数据转化为对应的Unicode编码
1 | |
Week5
Re
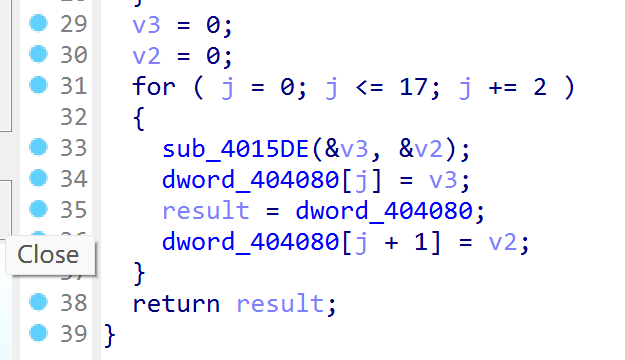
yu
这里去花指令比较特殊,汇编代码里有db,那就重新分析一下
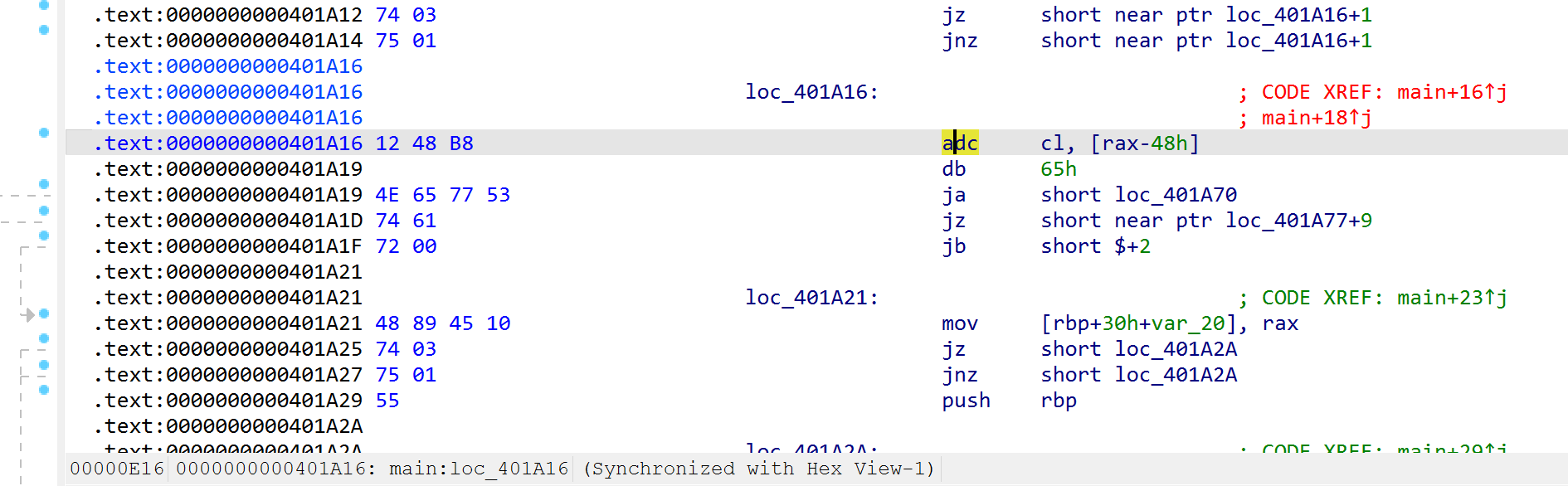
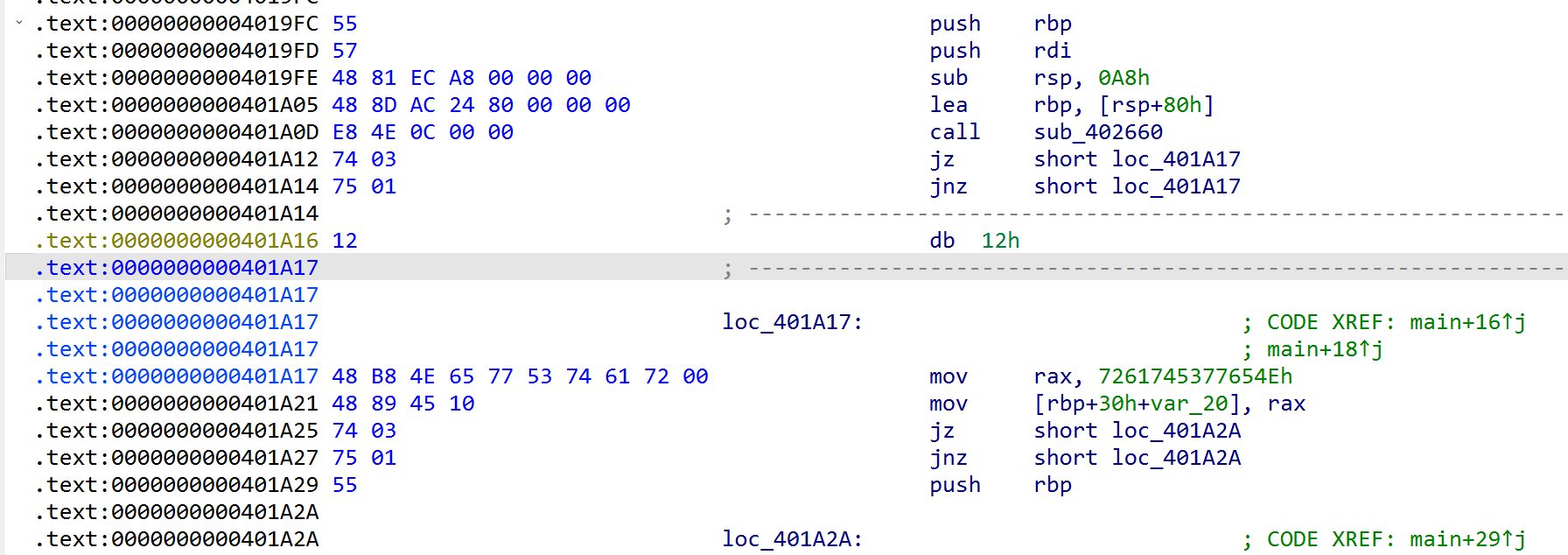
后续还是正常的,就是出现有点多
从题目名就可以猜到大概是blowfish
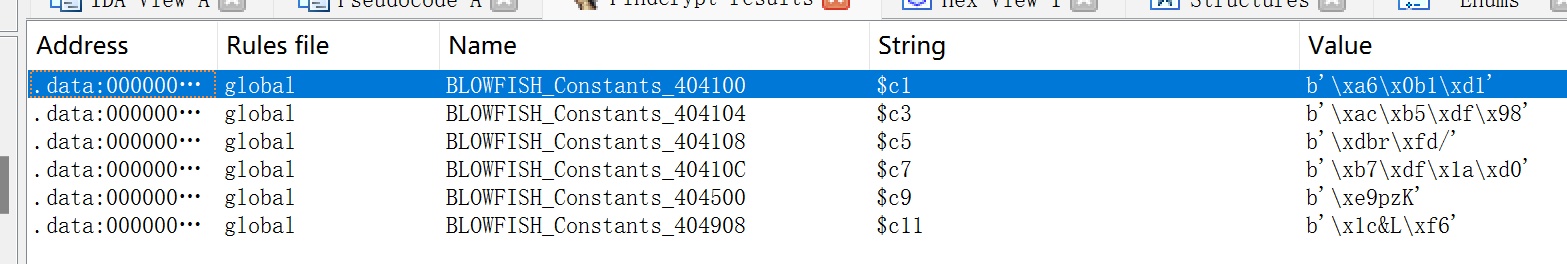
算法流程也符合
1 | |
The_Last_Dance
发现常数
key和密文
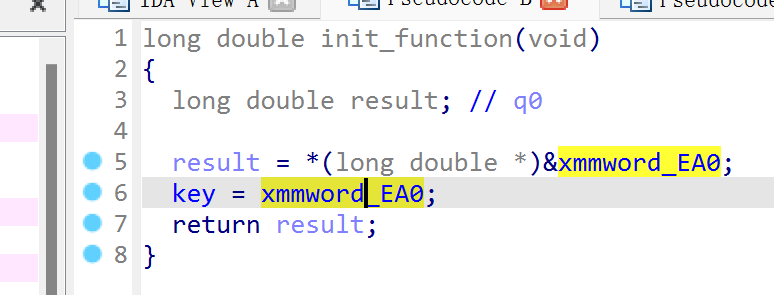
还可以尝试unidbg
1 | |