Geek2023部分Reverse与Pwn
Re
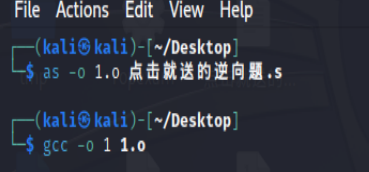
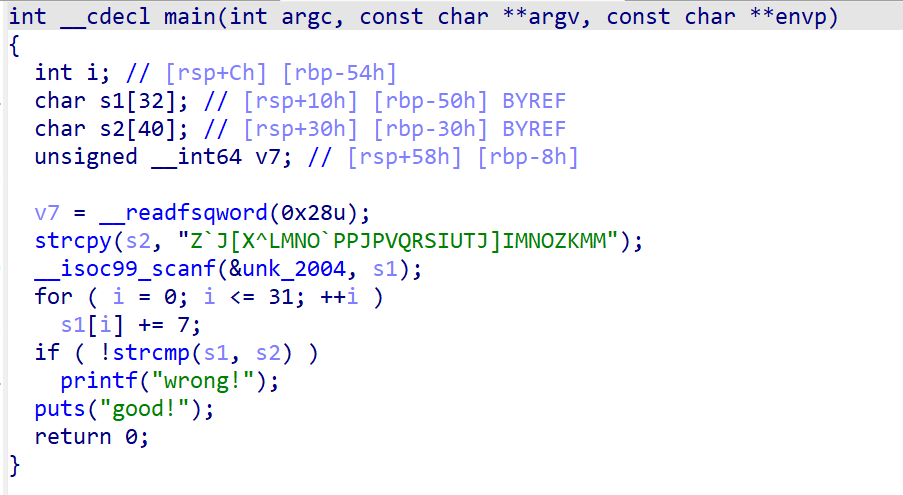
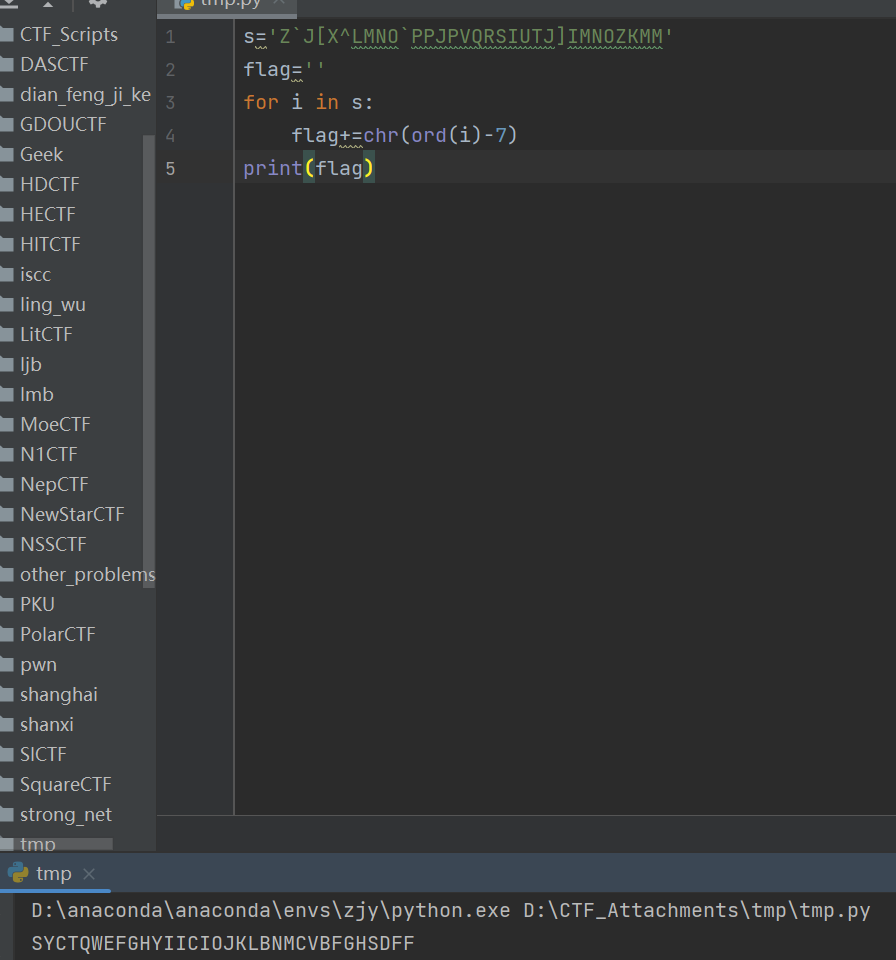
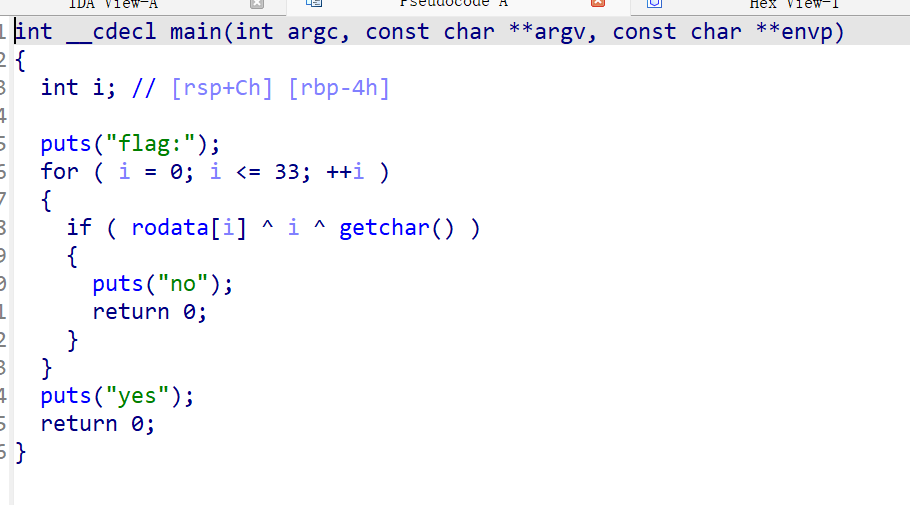
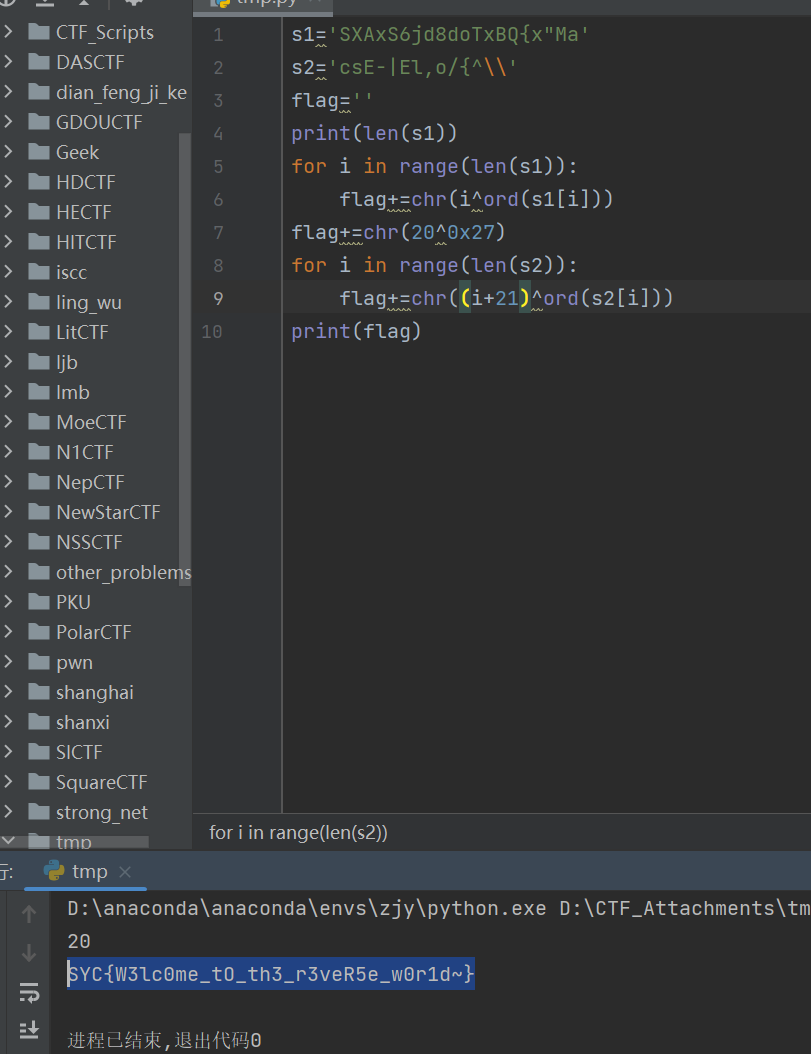
点击就送的逆向题
汇编,链接得到可执行文件
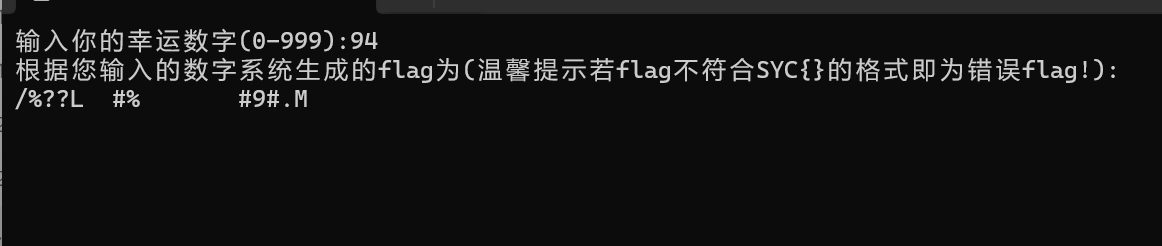
幸运数字
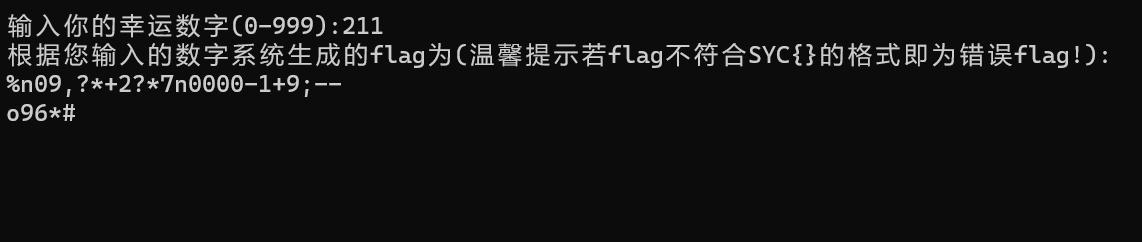
第三位要得到C,就要异或94
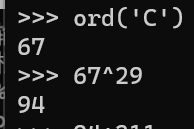
最后一位也是94
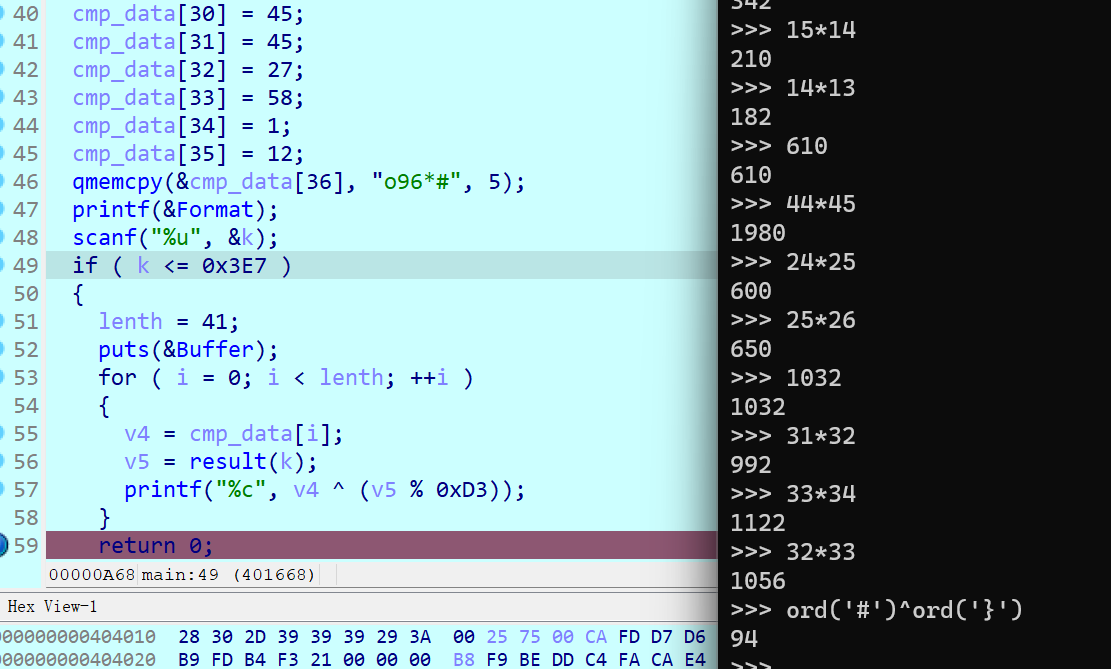
但直接输94是不对的
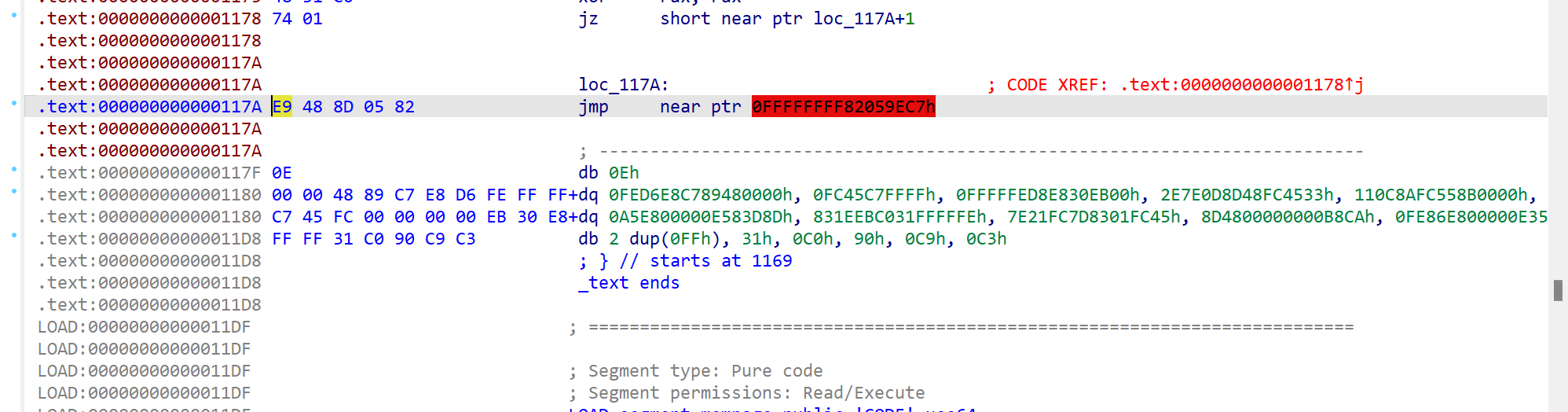
shiftjmp
经典花指令
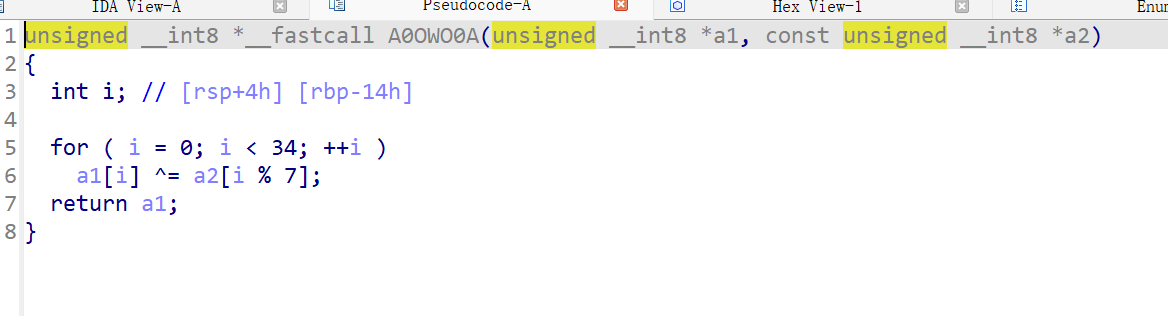
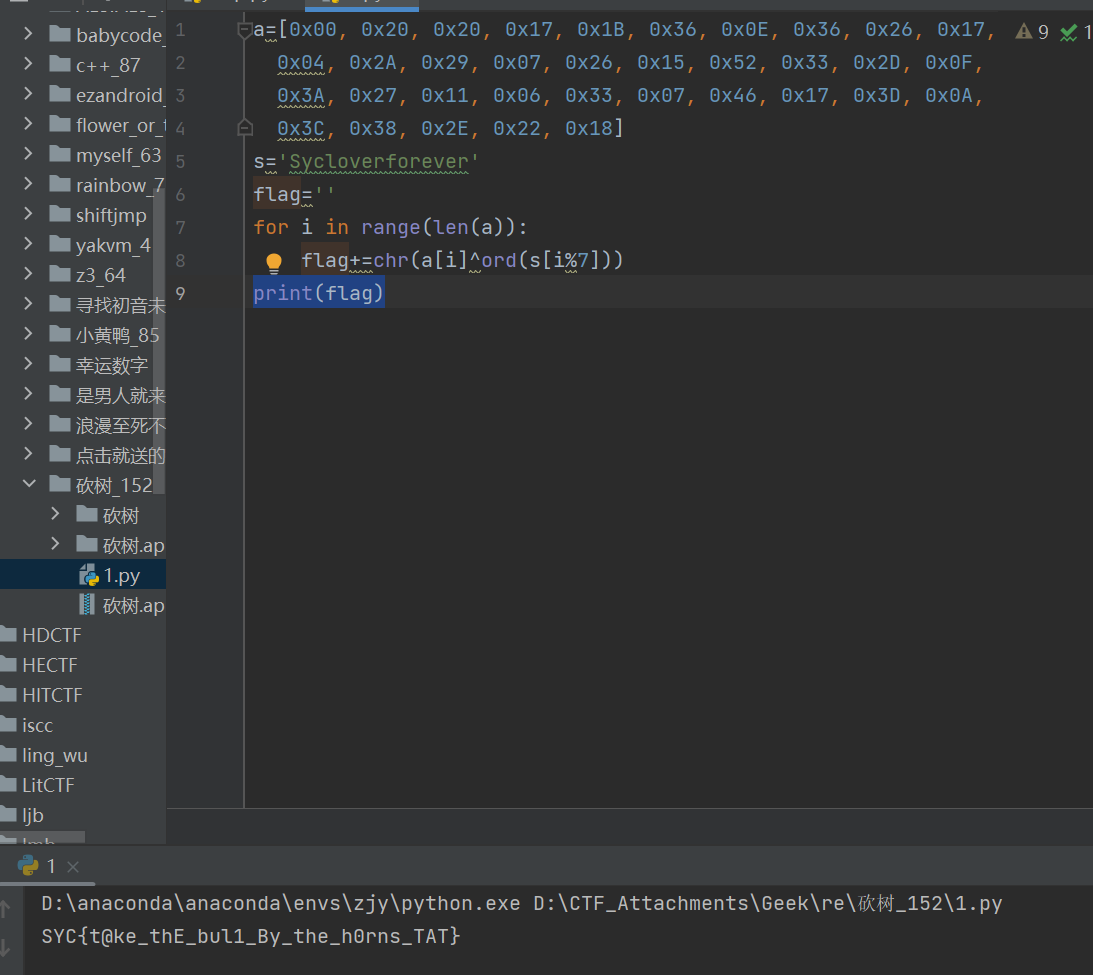
砍树
Loadlibrary和native想到去看so文件
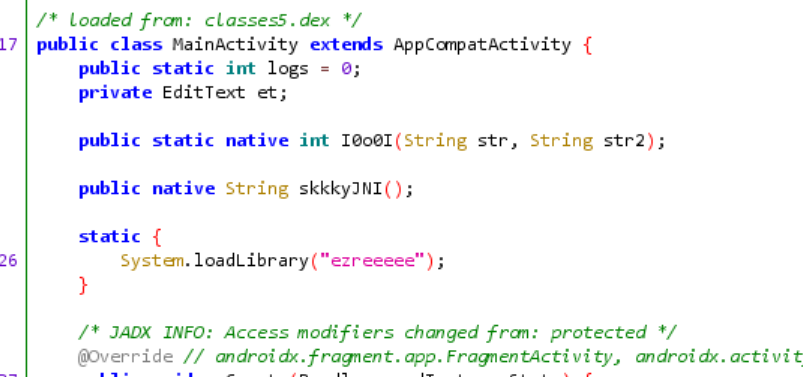
得到dest数组要动调so文件
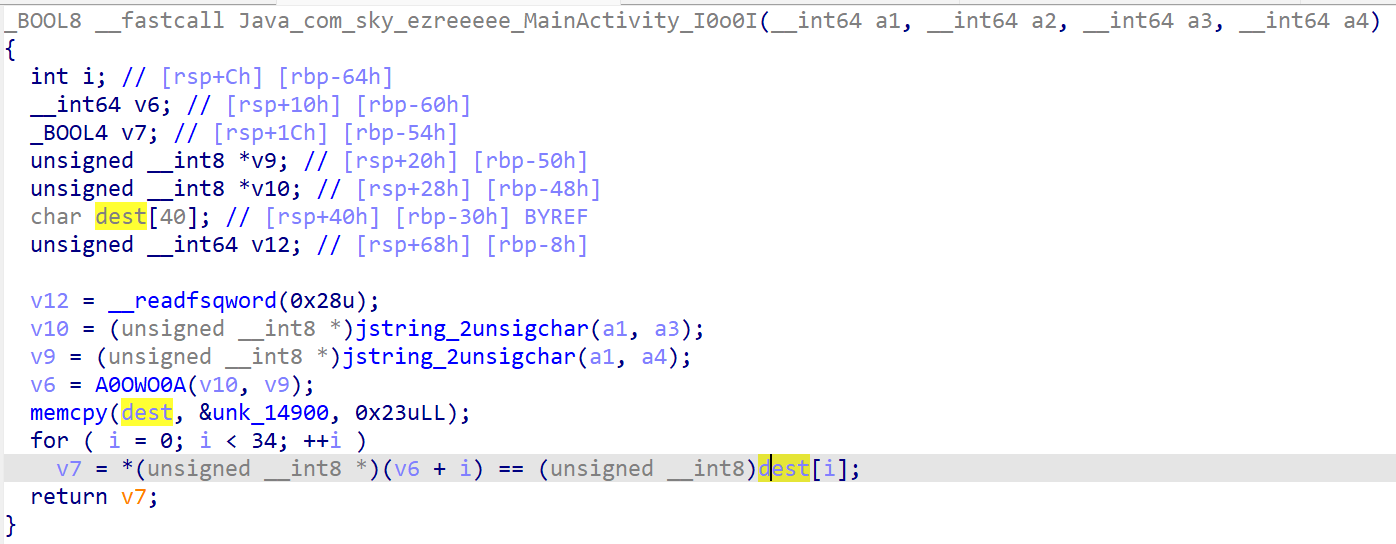
小丑了dest前面有整体复制
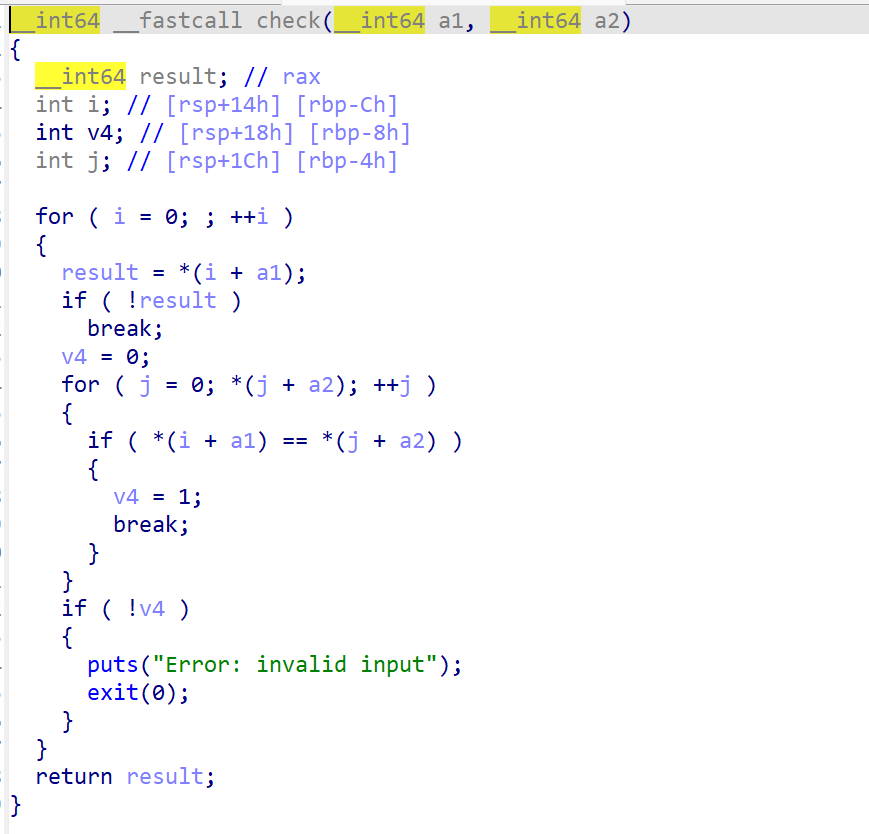
easymath
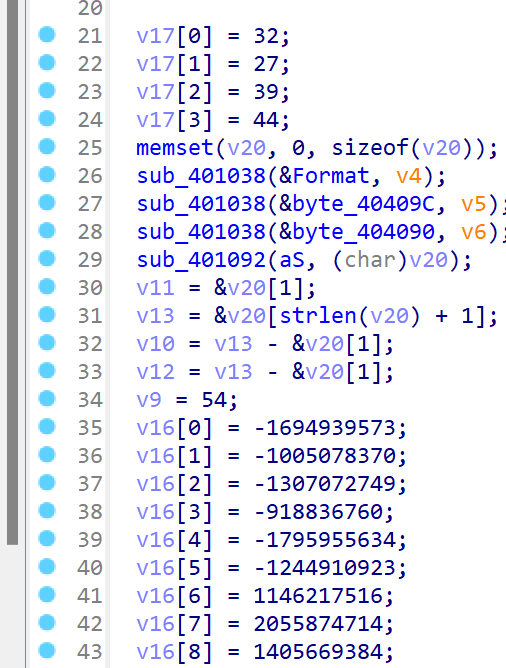
从0矩阵变成单位阵,last也就是matrix的逆矩阵
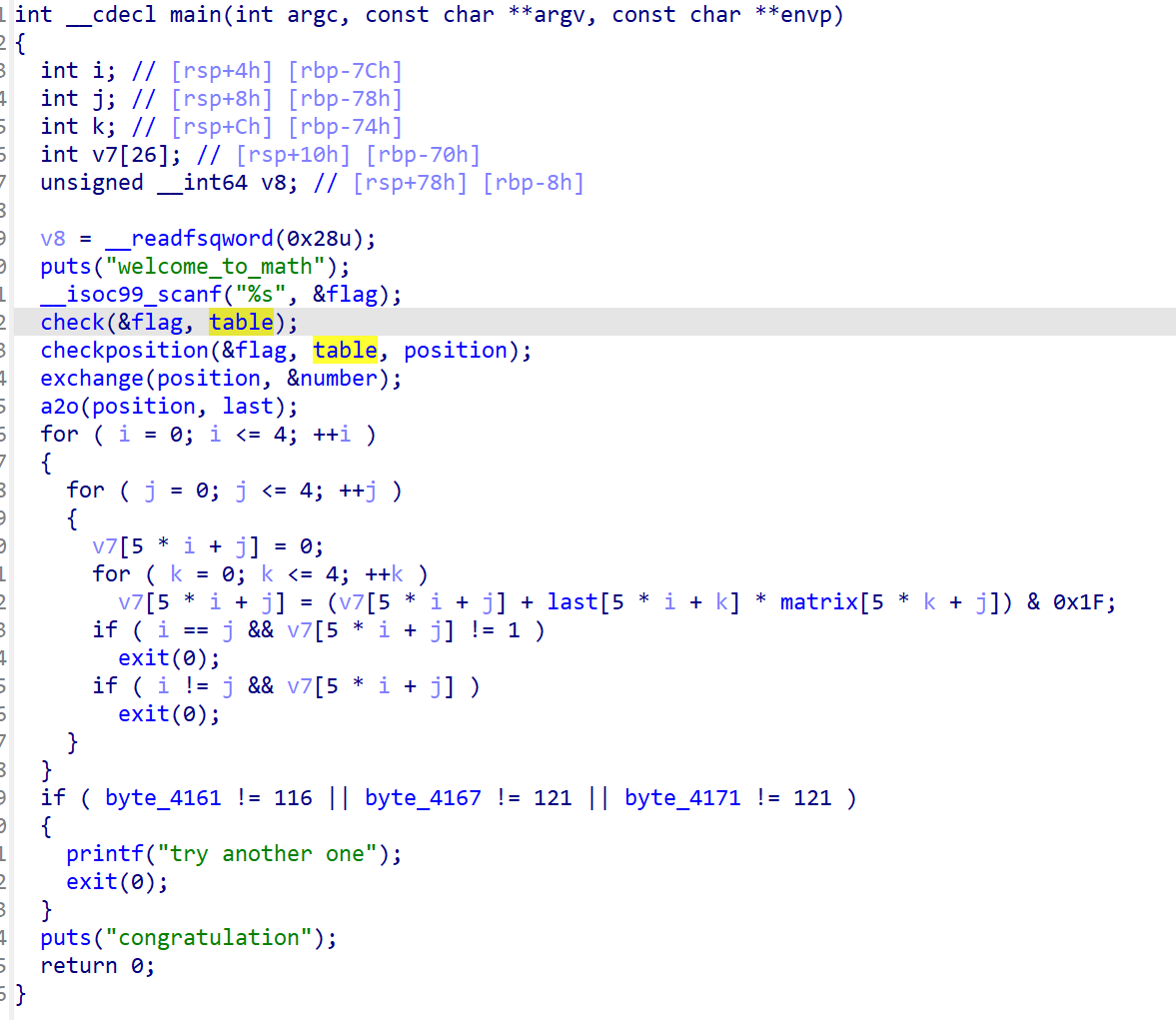
flag的每一位都从table表里取
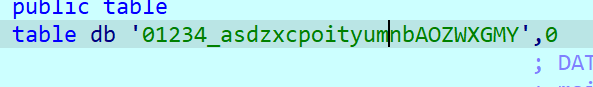
table表
flag的每一位对应table,取出下标后转为字符存到position
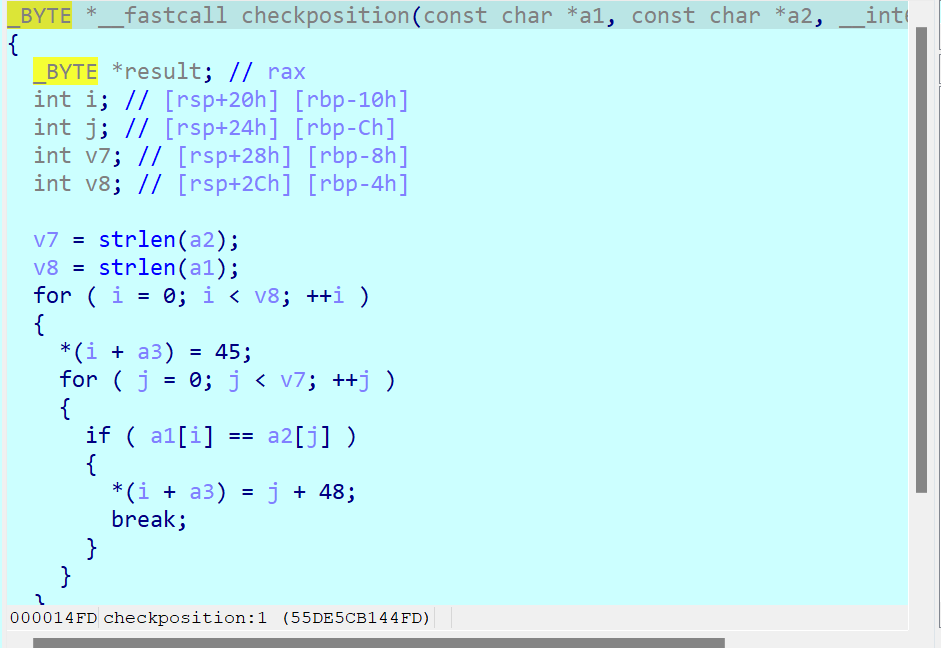
输入aaaa,得到6666
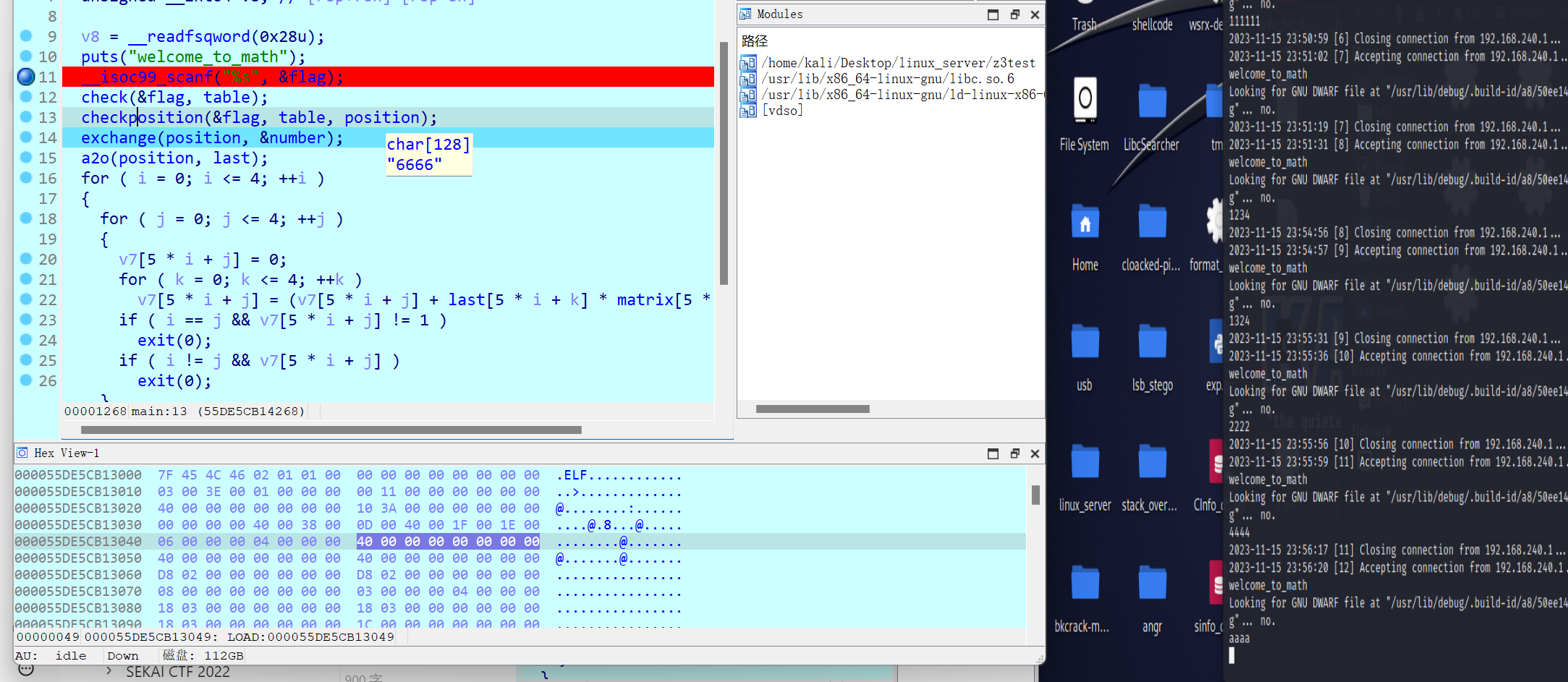
最后的last为7777
输入asdz,得到7,8,9,10,说明是下标+1
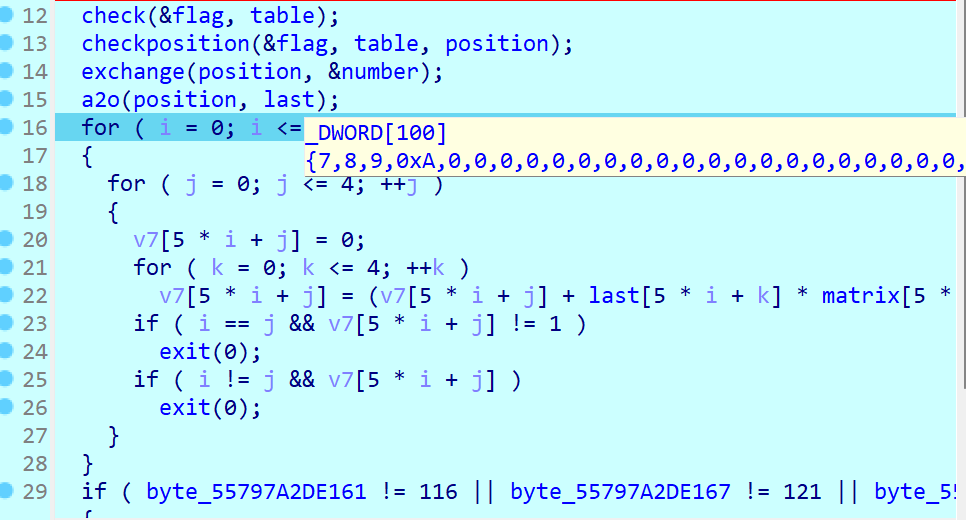
大致功能是在table里面找到对应的值,并取下标然后储存到position里面,接着再用这个下标在number里面取值存到last里面
有约束,防止多解
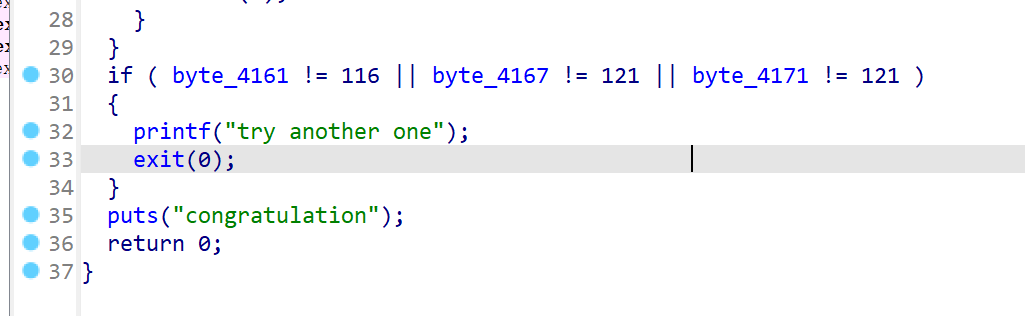
下面这种写法最容易理解
1 | |
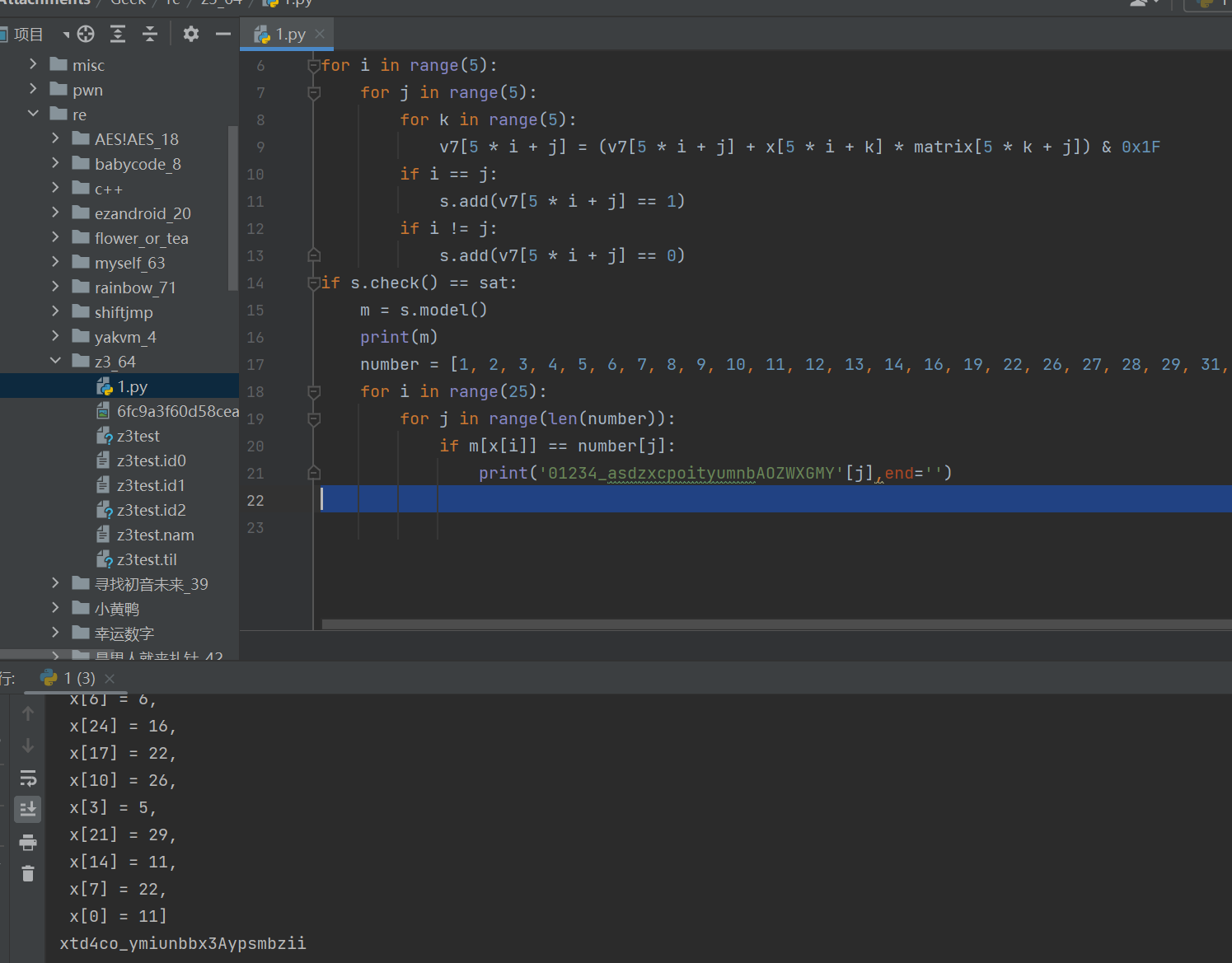
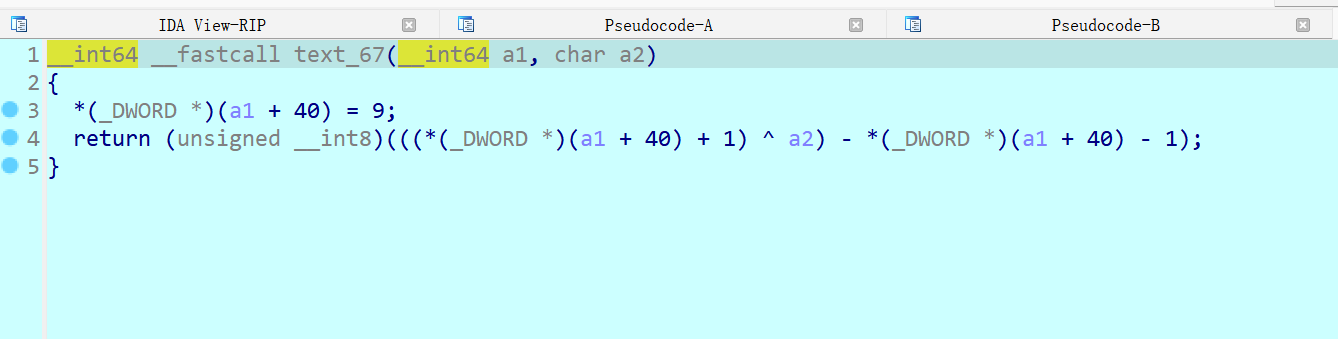
c++
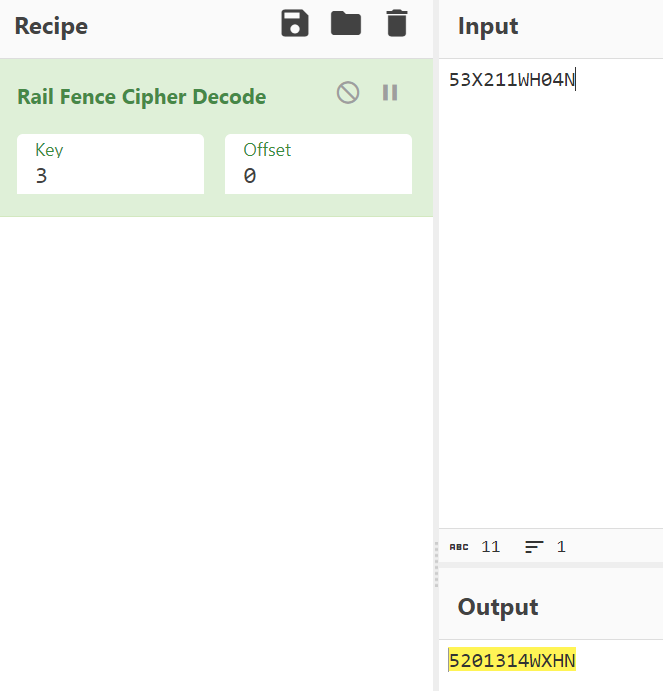
一开始无法调试
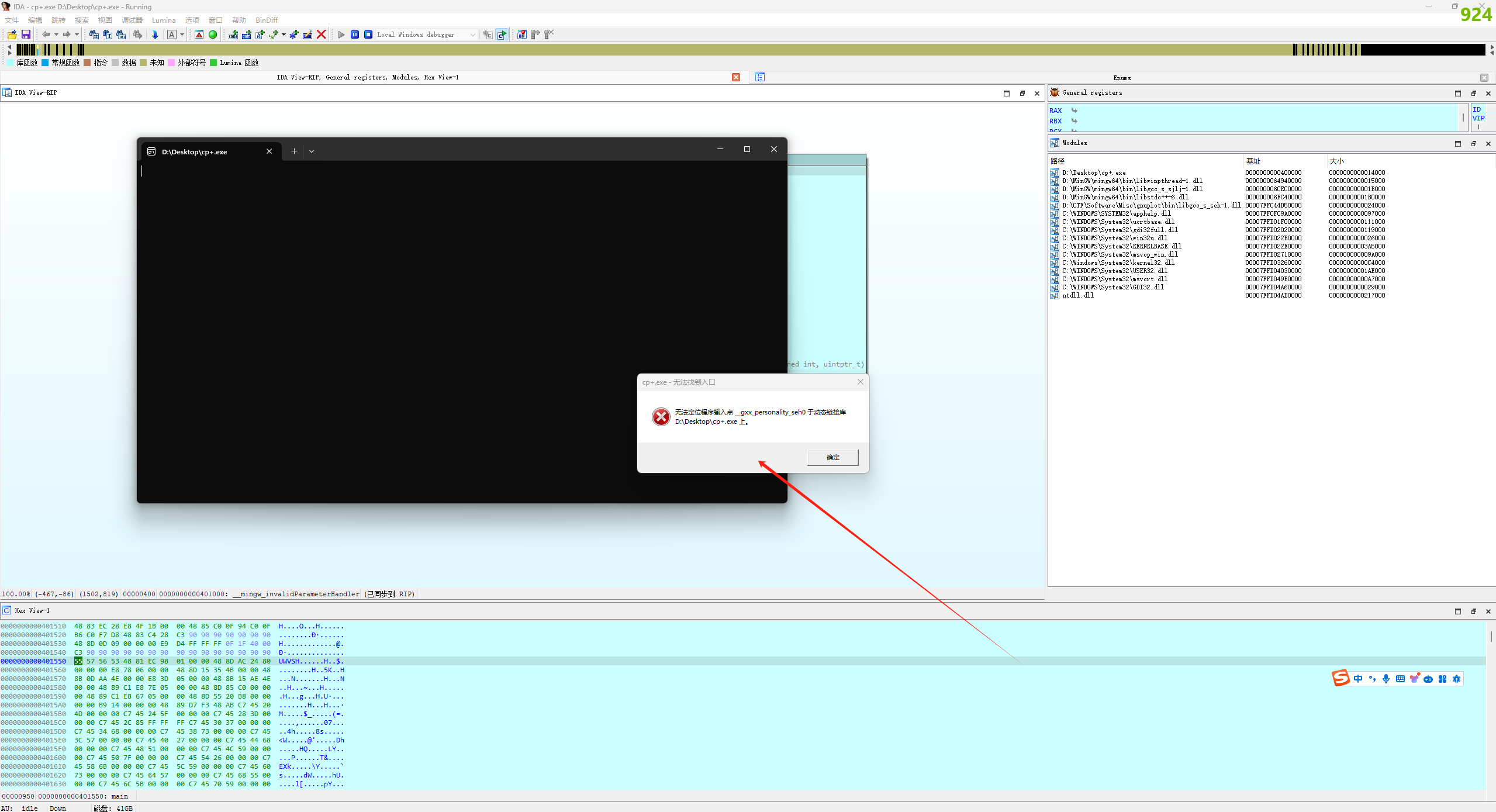
把libstdc++-6.dll放到当前目录
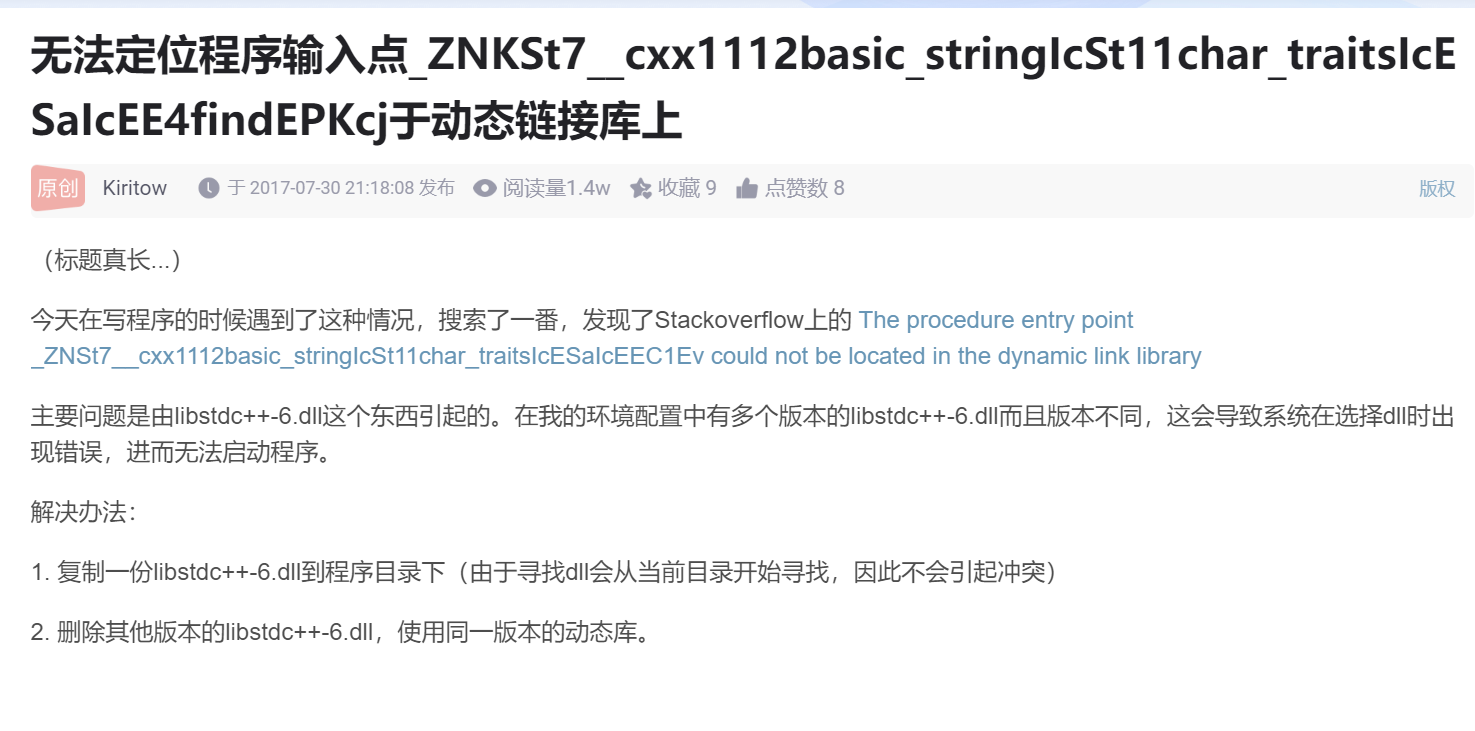
调试发现+=10
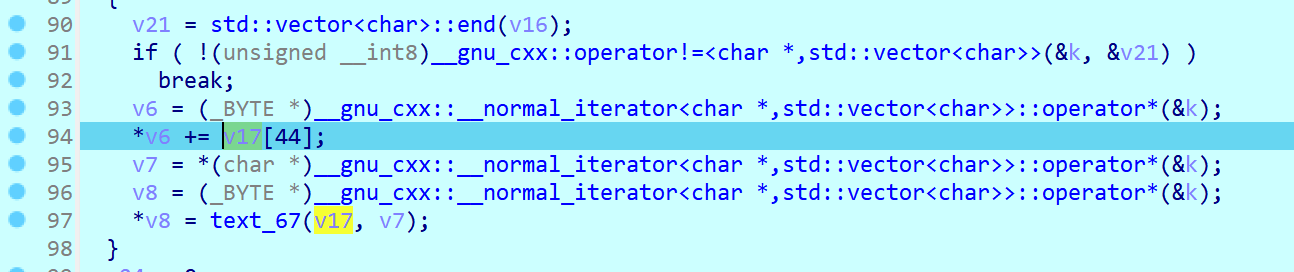
rdx恒为0xa
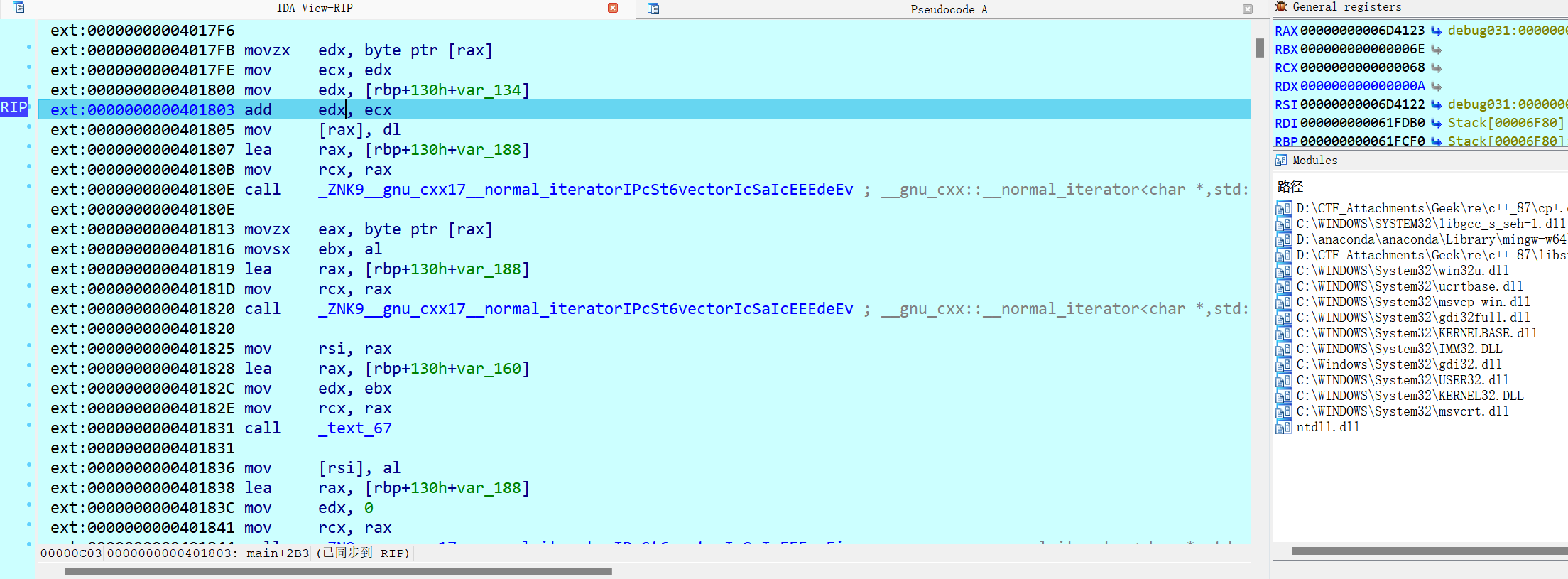
先^10,再-10
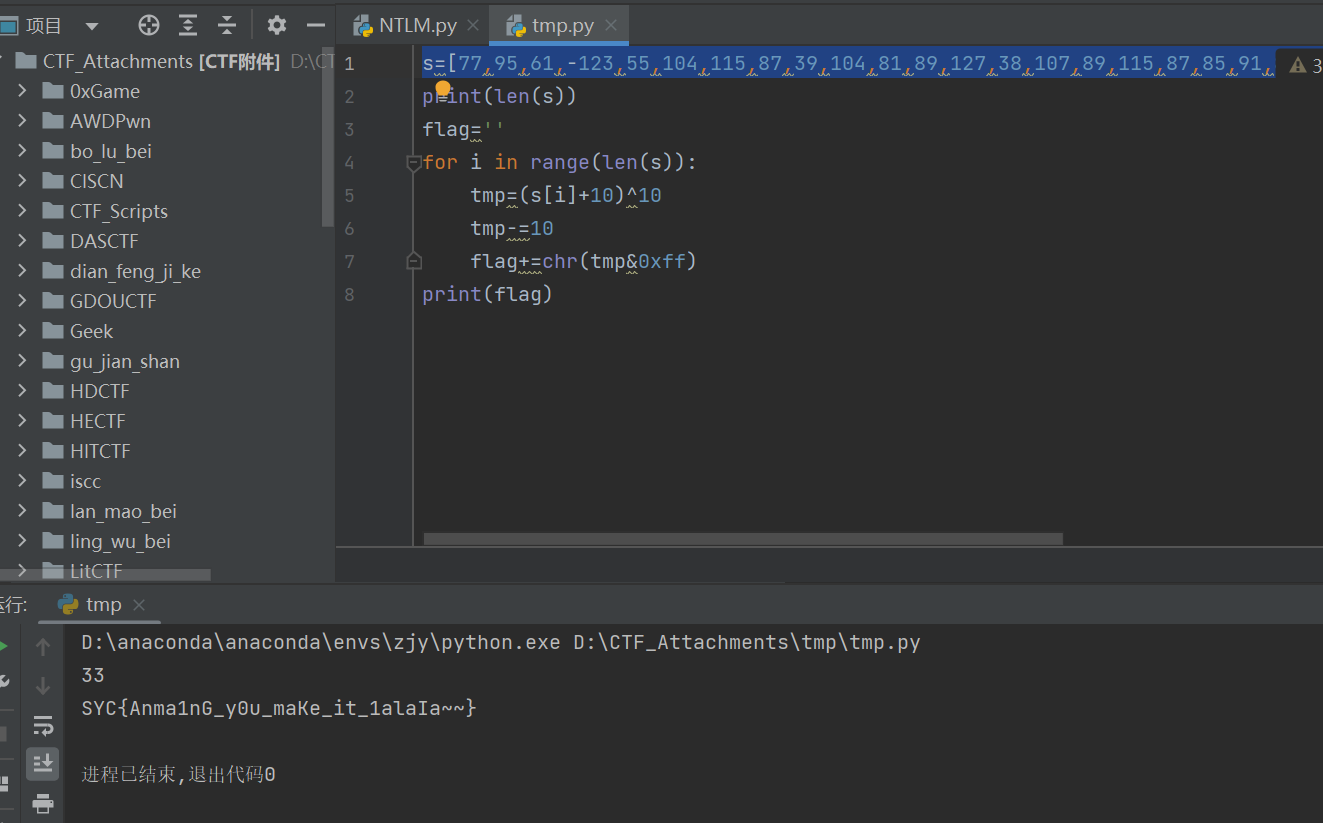
re虽然可以只根据关键代码猜出flag但是平时还是要提升审计能力的
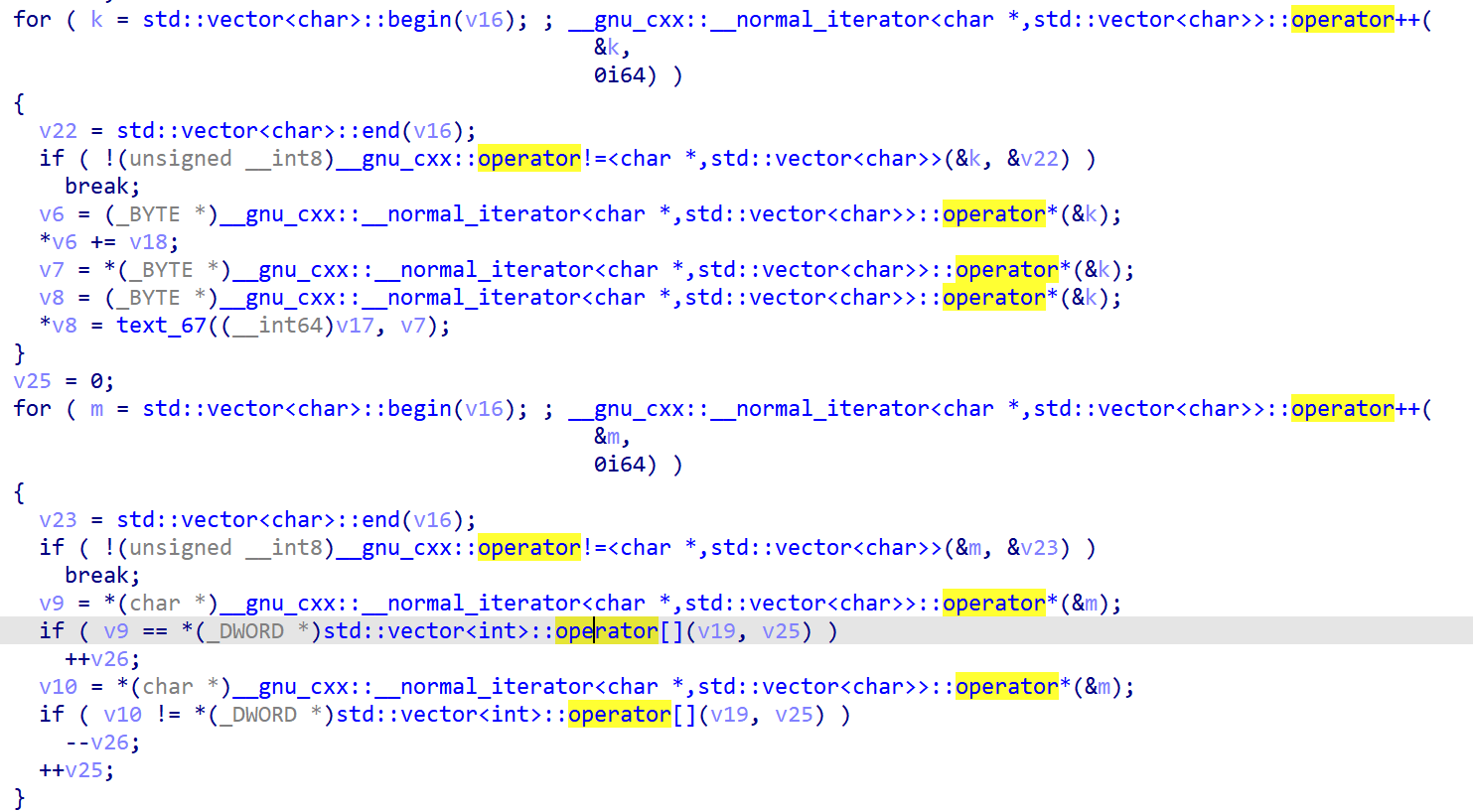
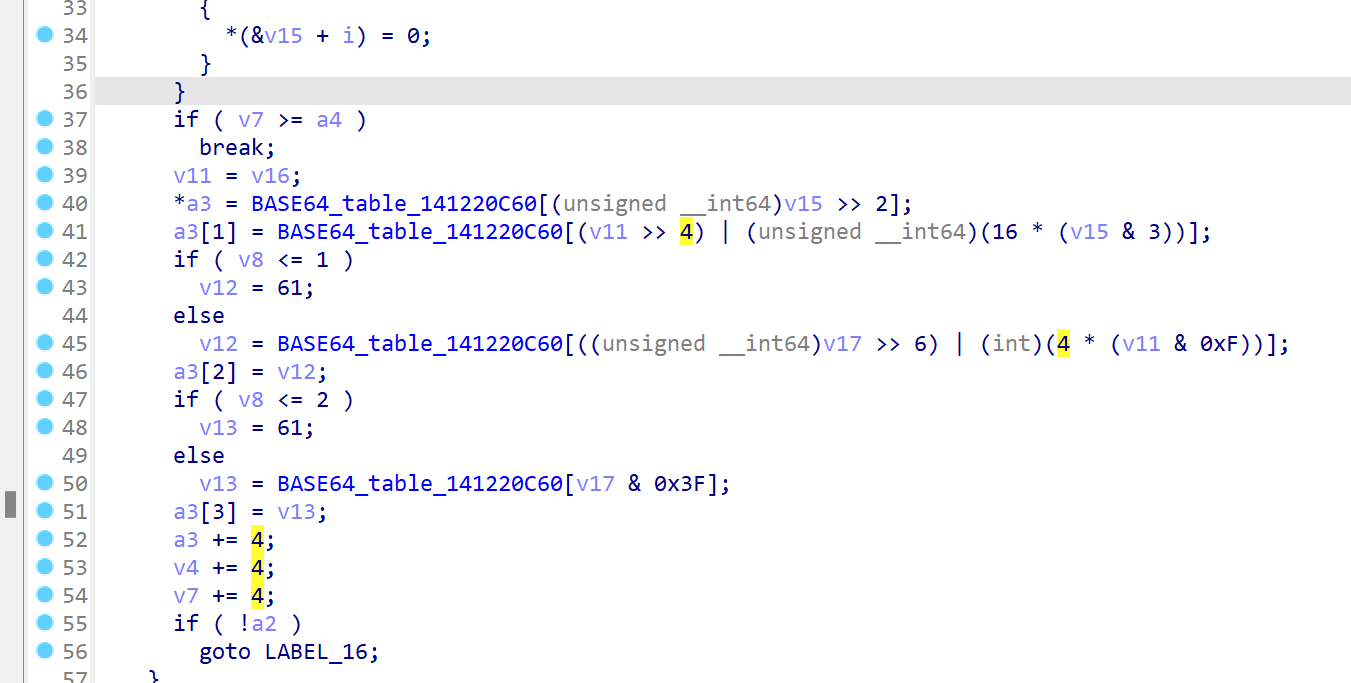
v21作为输入,经过encode函数编码(经调试发现值并没变化),一个个添加到字符向量v16中去
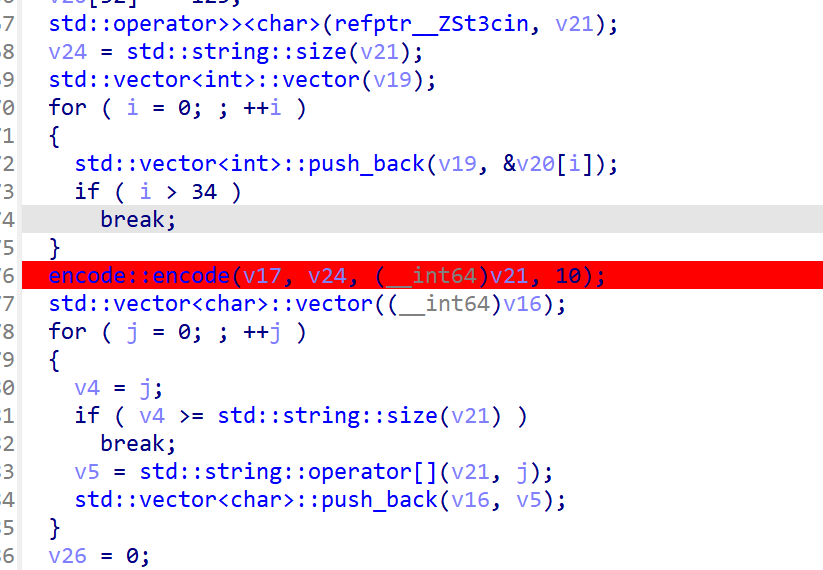
迭代器k和m都指向v16,std::vector
flower_tea
有花指令,经典jz和jnz同时存在
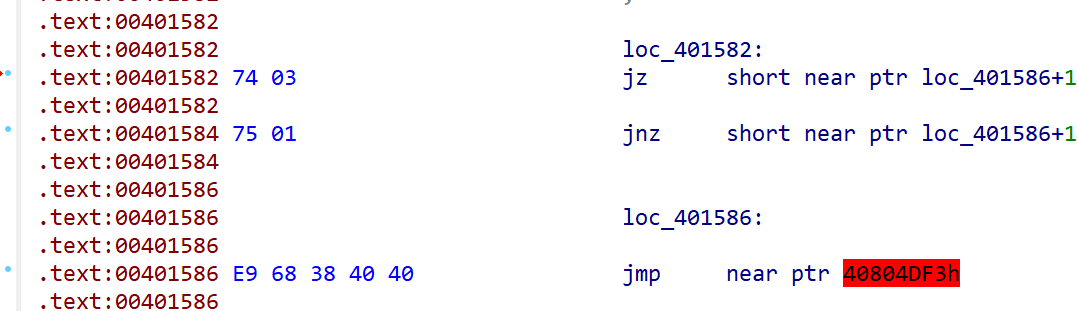
先按U
E9下一行按C,然后nopjz,jnz和E9
把黄色的按C修复
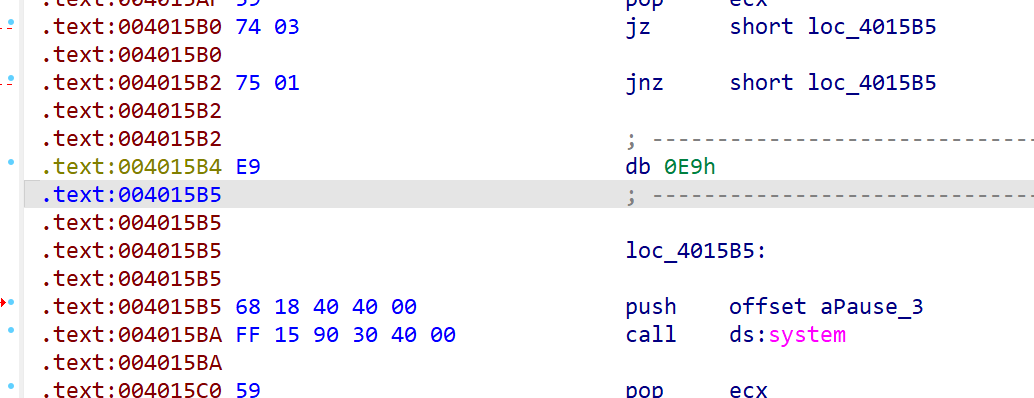
后面十个左右花指令也是如此
效果
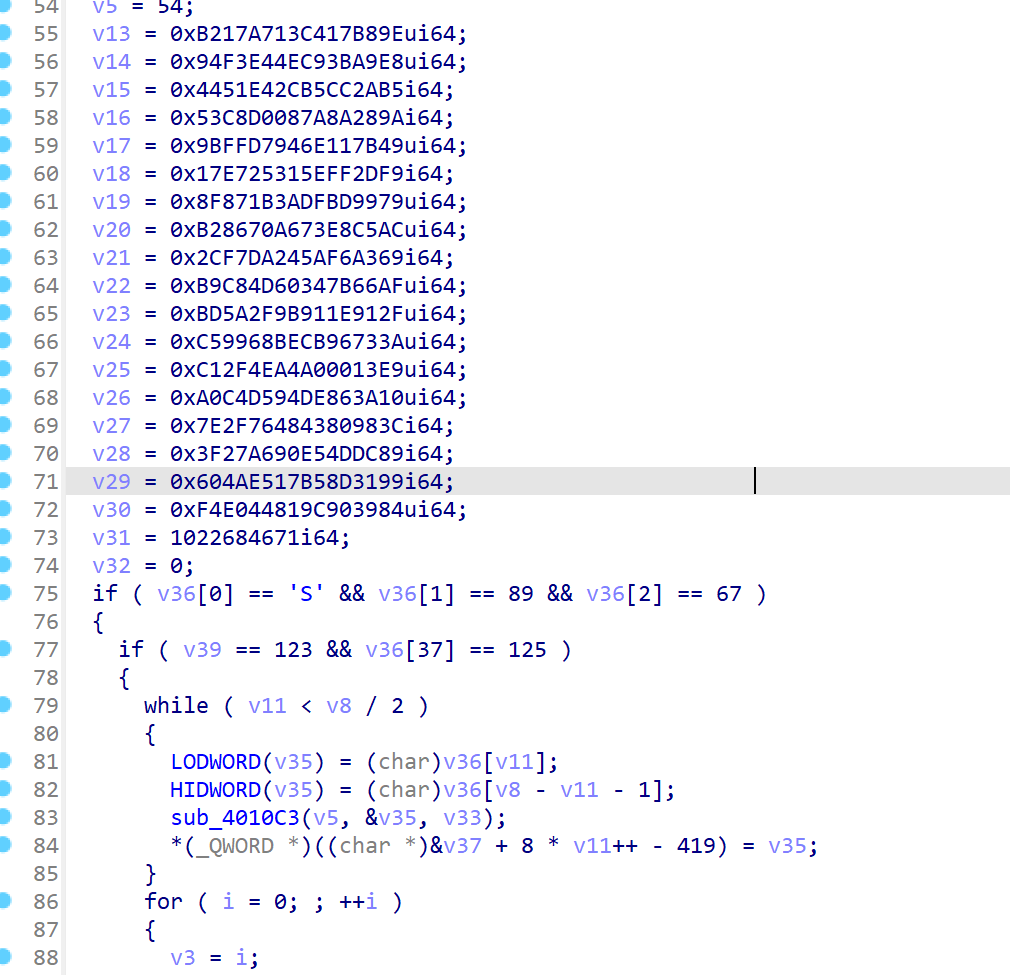
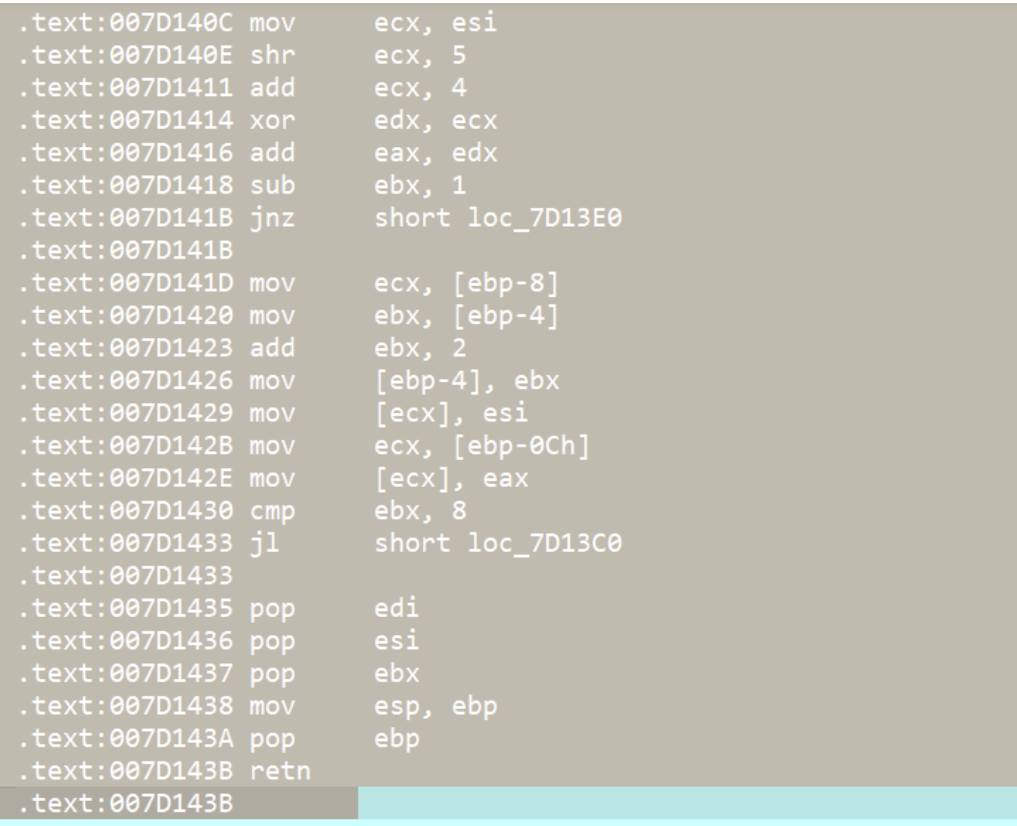
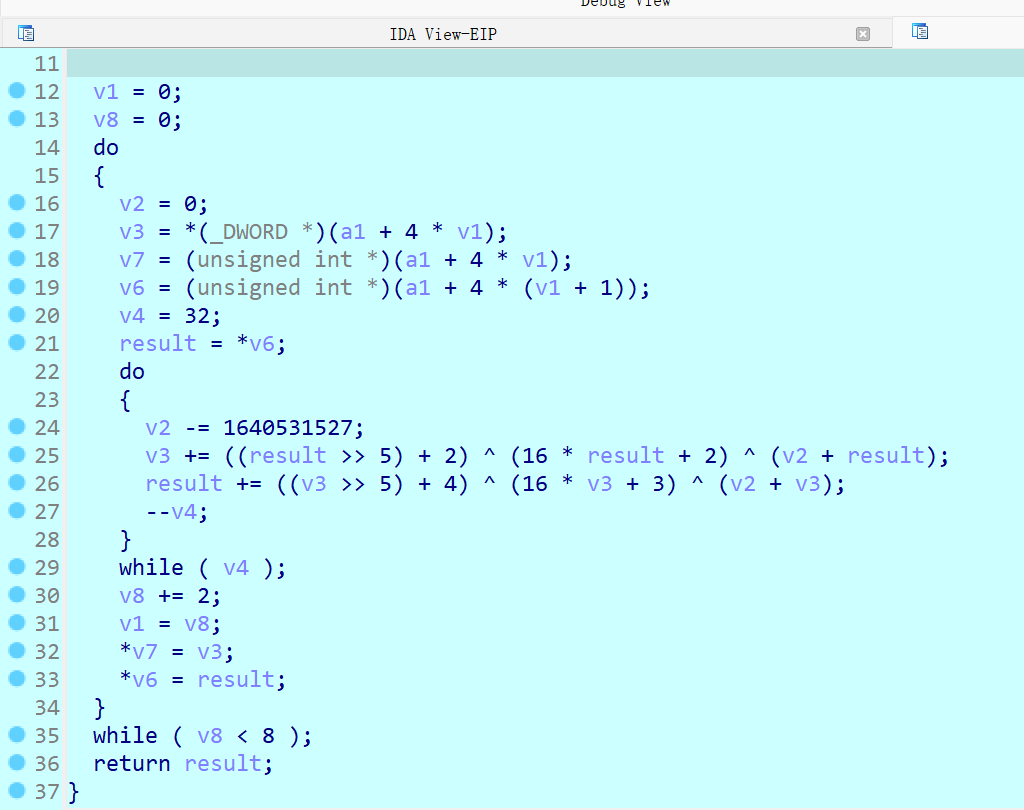
tea算法
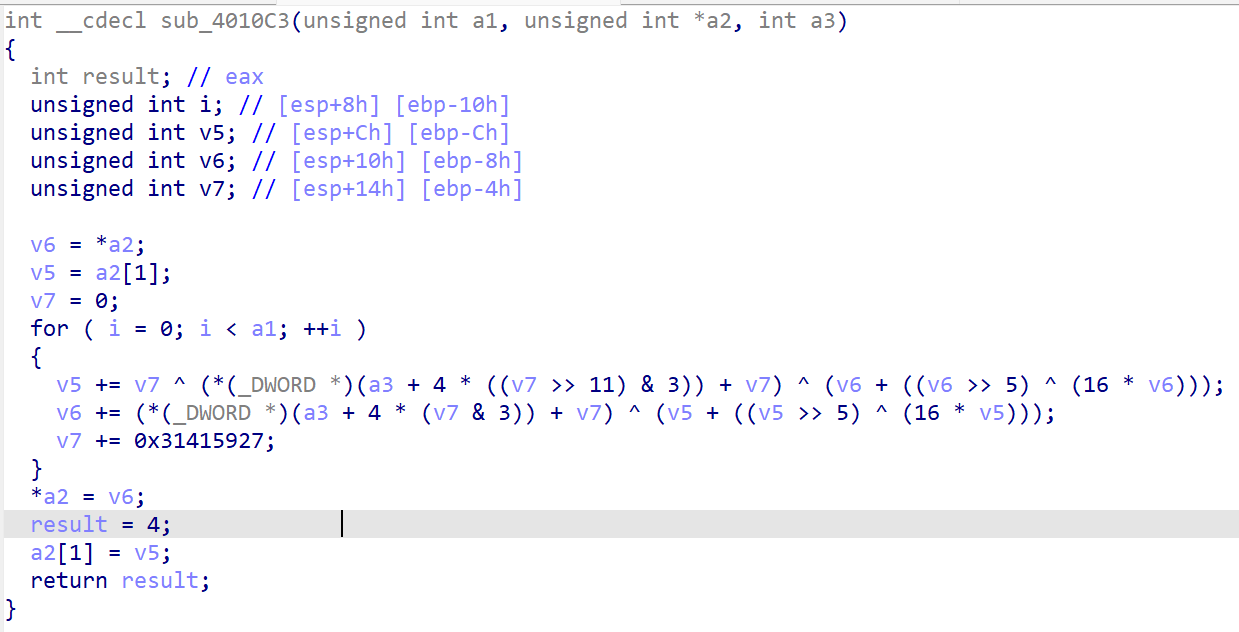
key
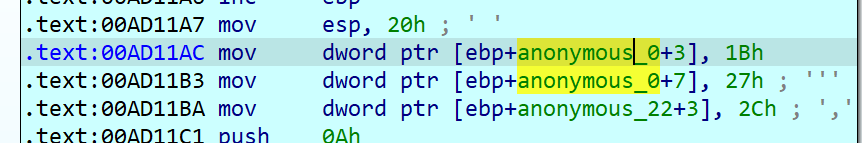
v8是len,相当于外层循环38/2=19次
nop到位数据更加完整,可以直接看到key和密文数组
1 | |
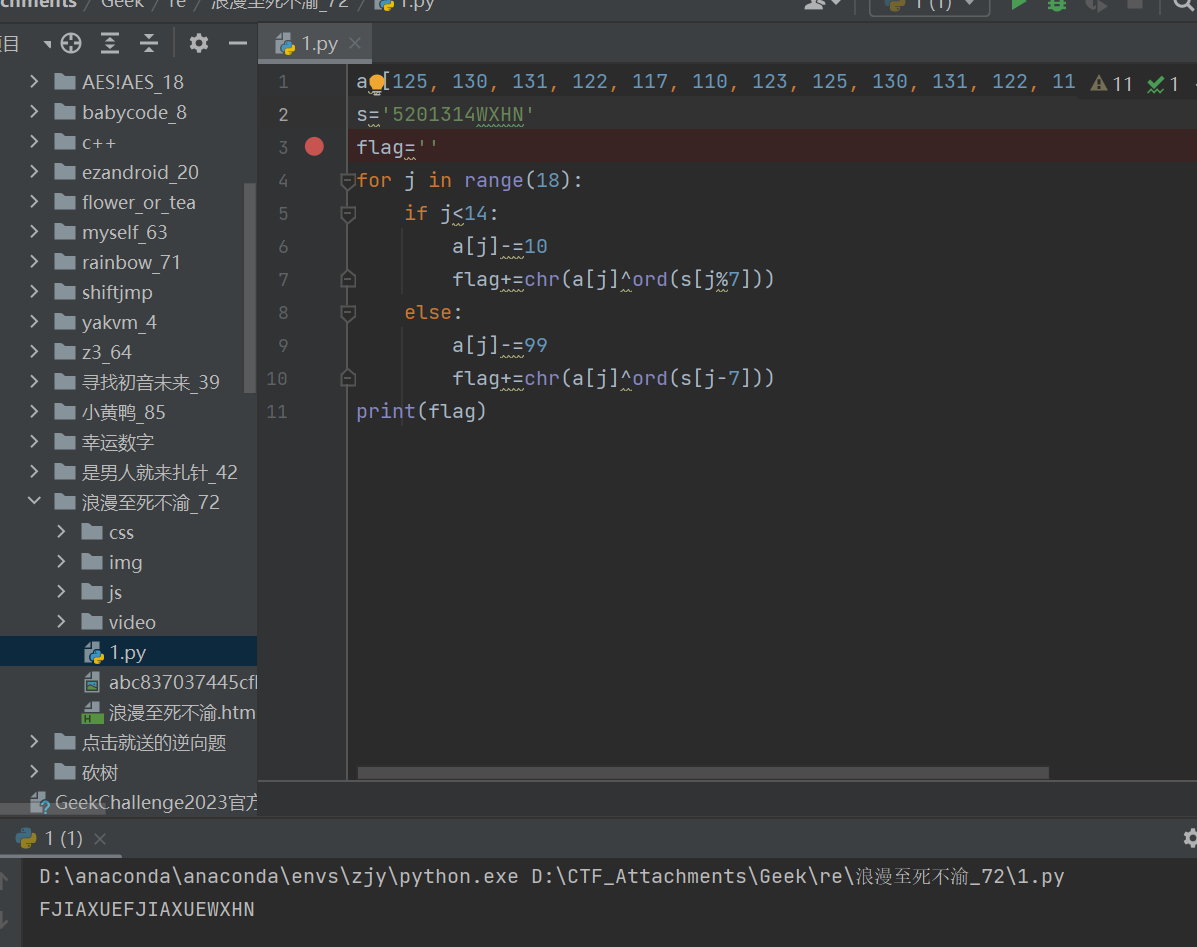
浪漫至死不渝
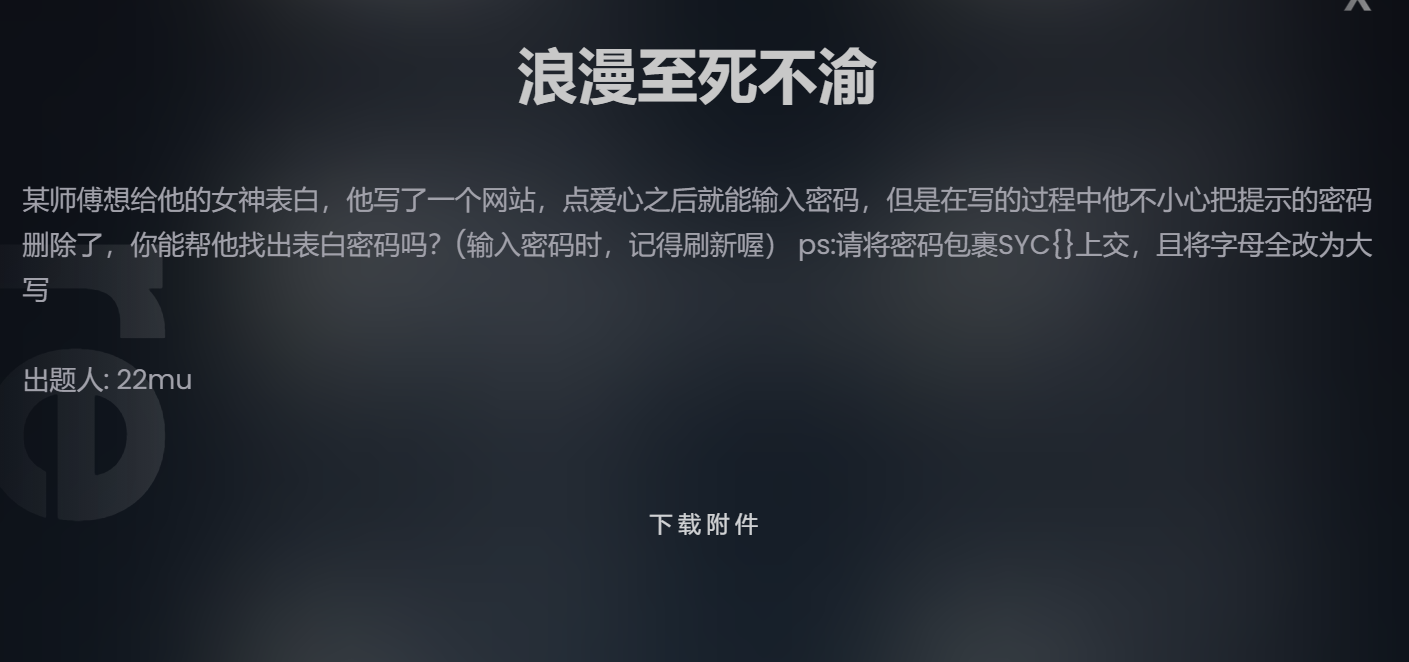
点完爱心也没让我输密码
附件给的一堆音频也没用,毕竟不是misc,那就看代码,两百多行,第一眼是拒绝的,后来静下心就开始了
第一眼看到这个字符串,还以为直接就是密码
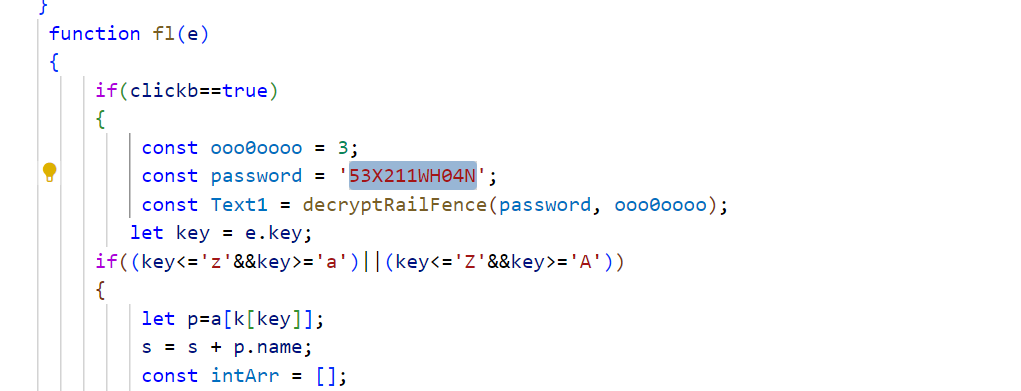
看到后面有比较,那就能找到密文了
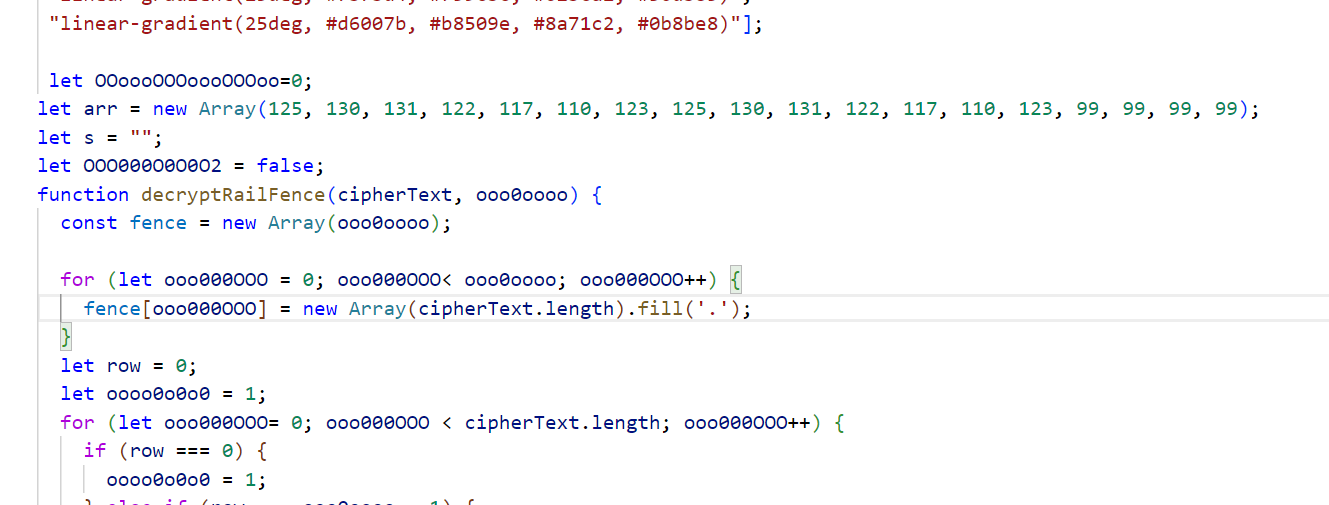
也去看了加密的过程
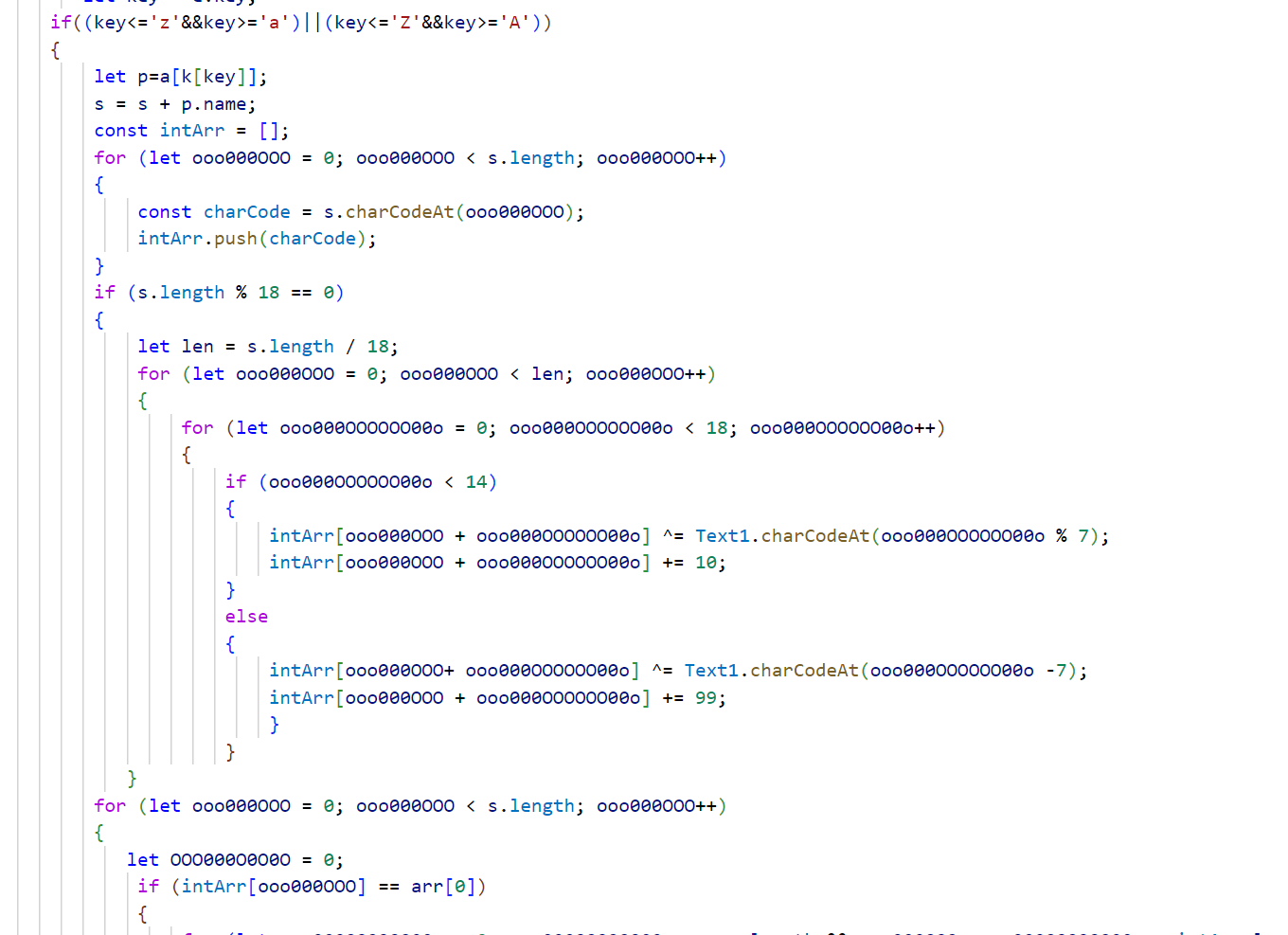
发现text1是由函数生成的,怎么看名字像栅栏密码
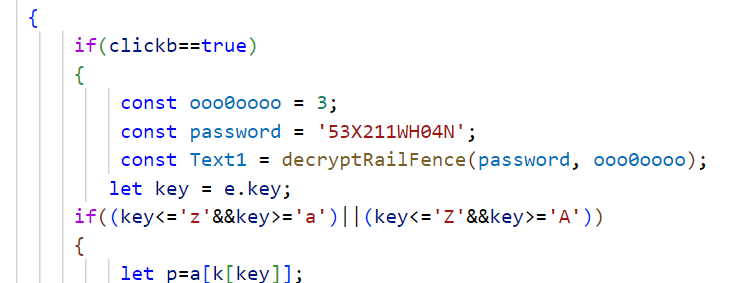
先试试,这密文,那还真是
也可以js调试获取text1
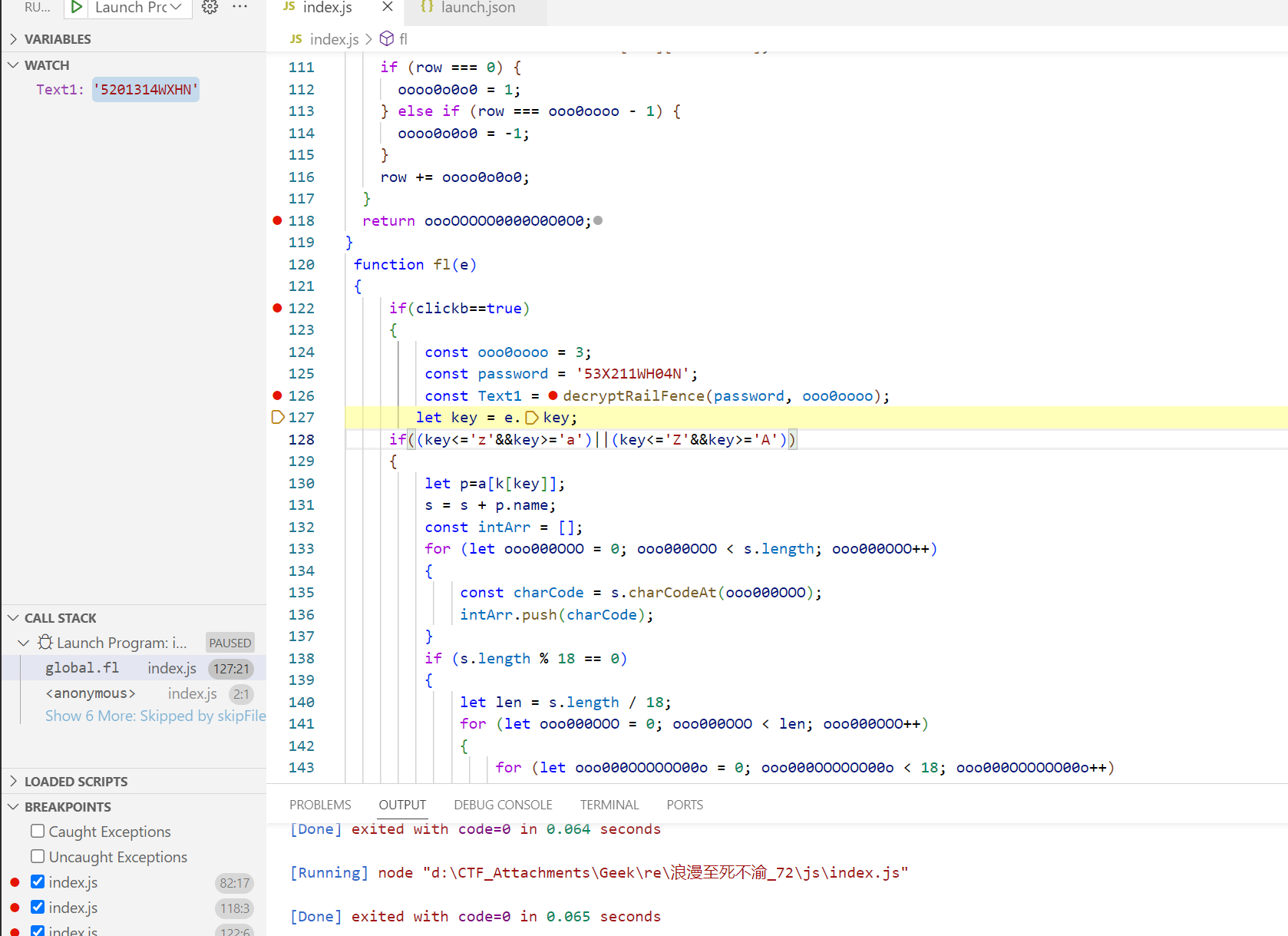
接下来就是简单逆向了
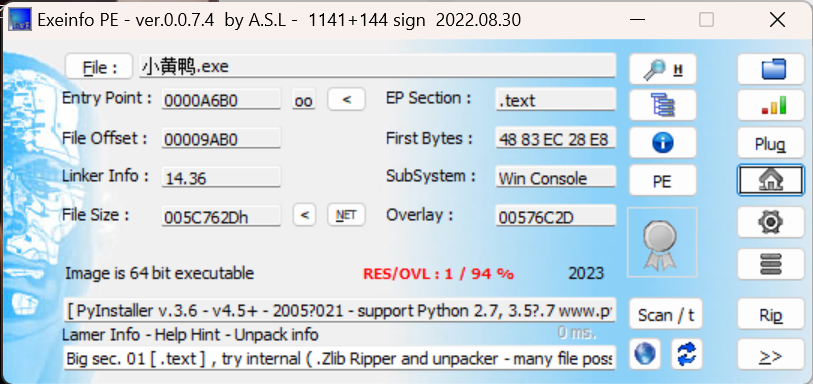
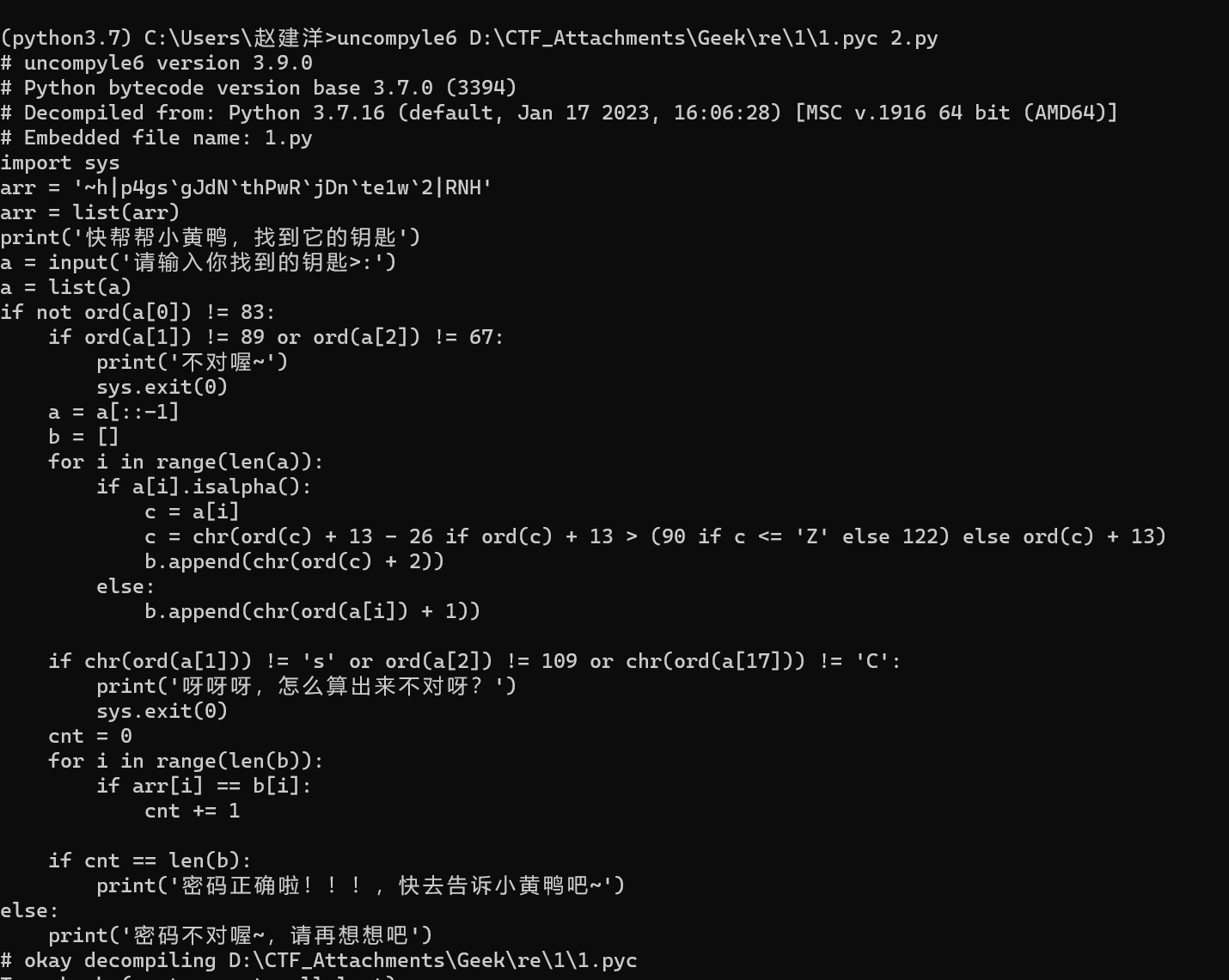
小黄鸭
一眼pyinstaller
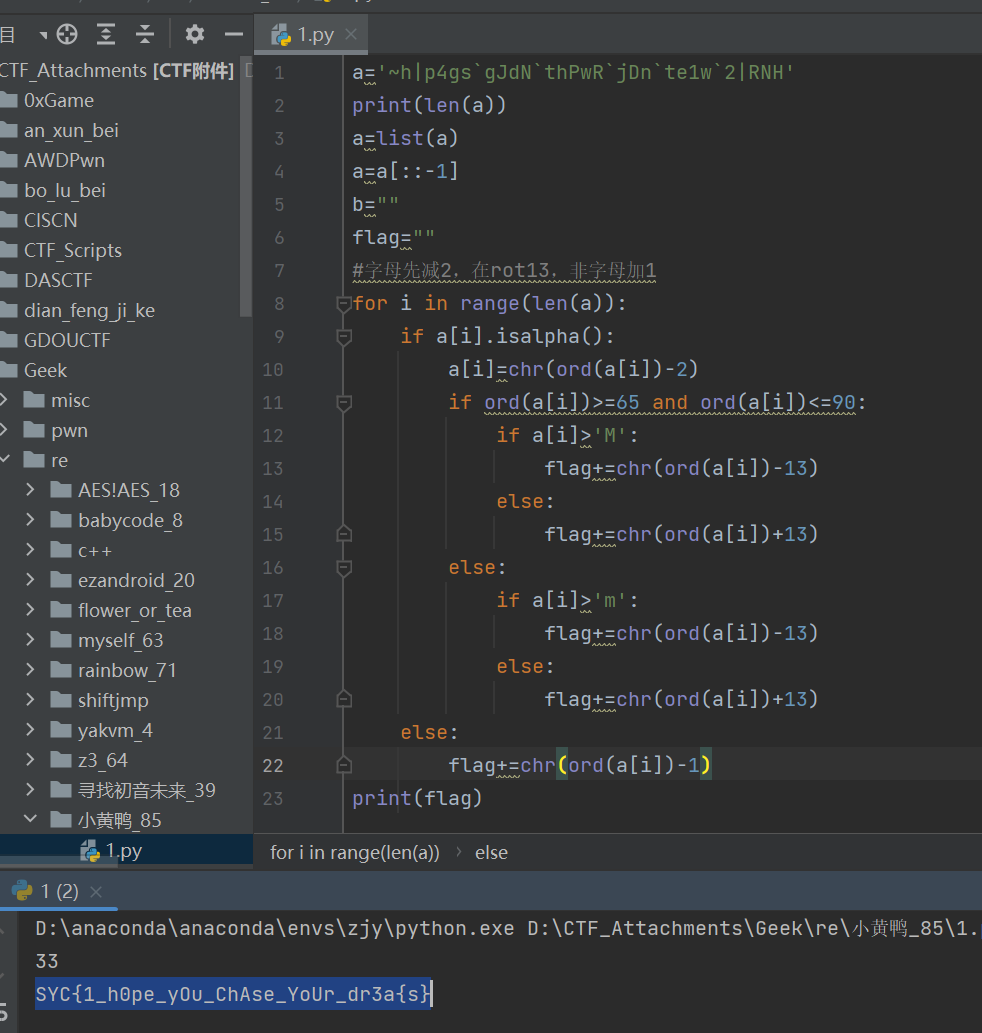
发现倒数第三位有问题,说明在线反编译有问题,其实猜也可以猜到是dream
用uncompyle6出来是or
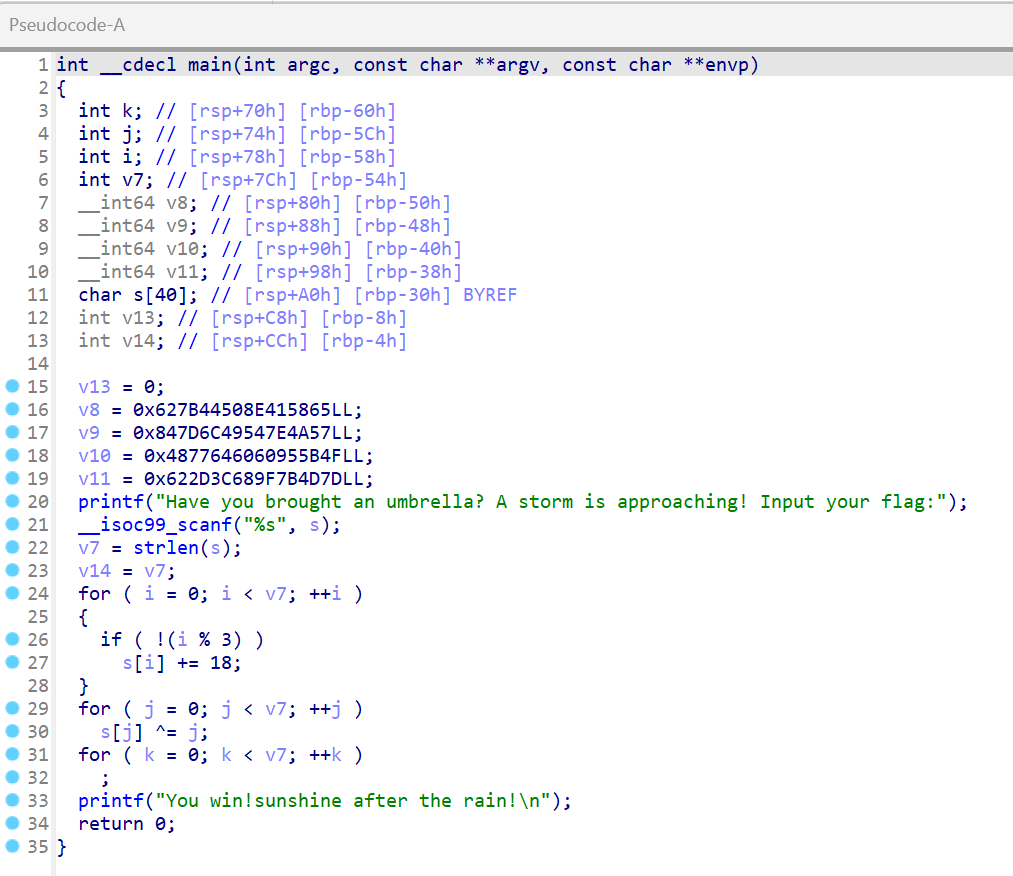
rainbow
这种一堆while循环,一个错了就得退出,看着就烦
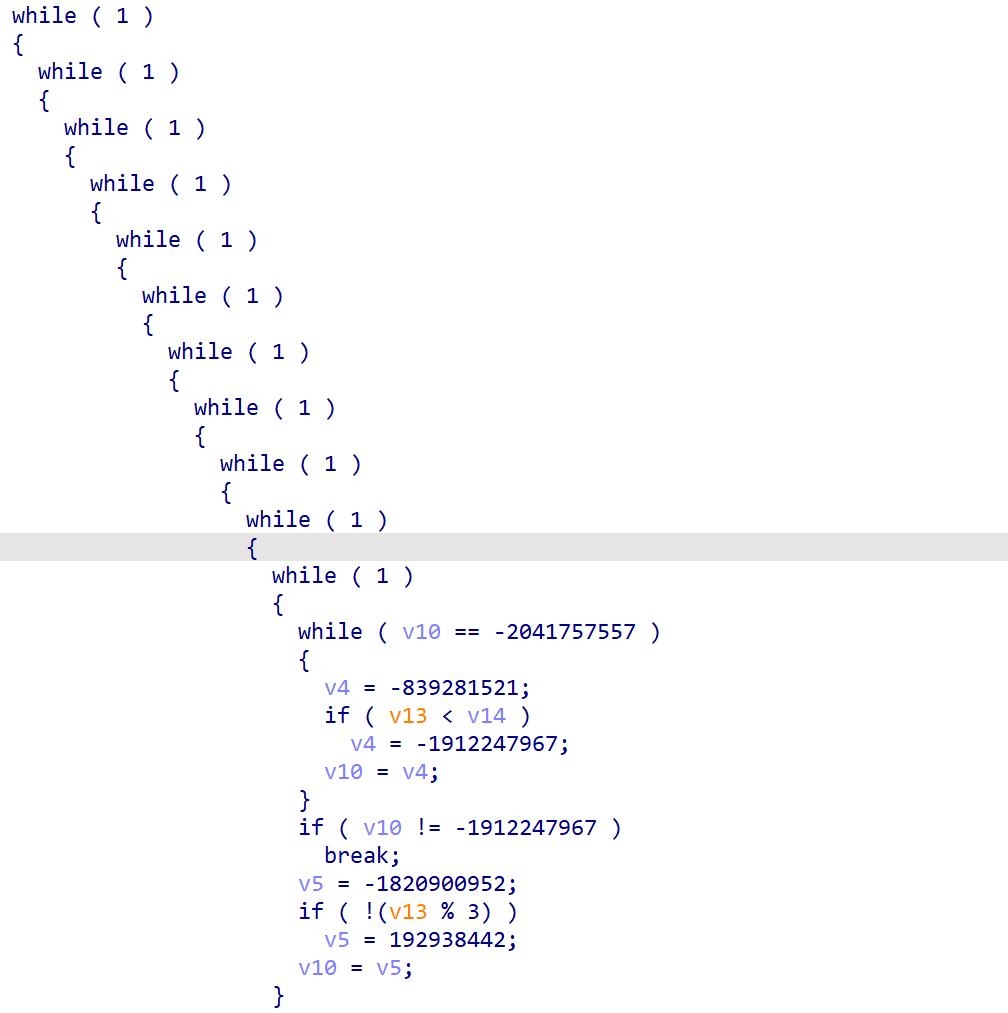
密文
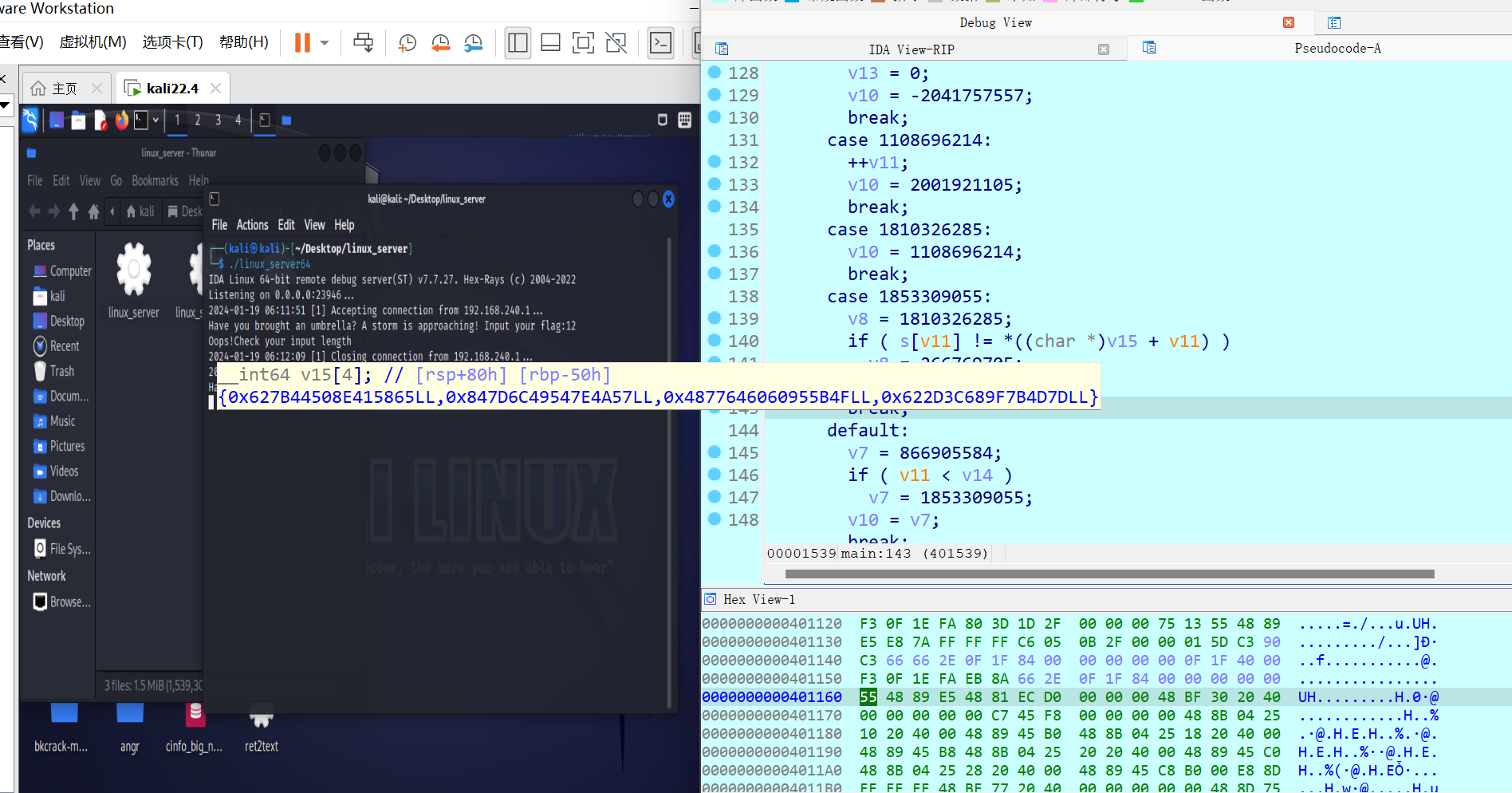
下标整除3的时候加18
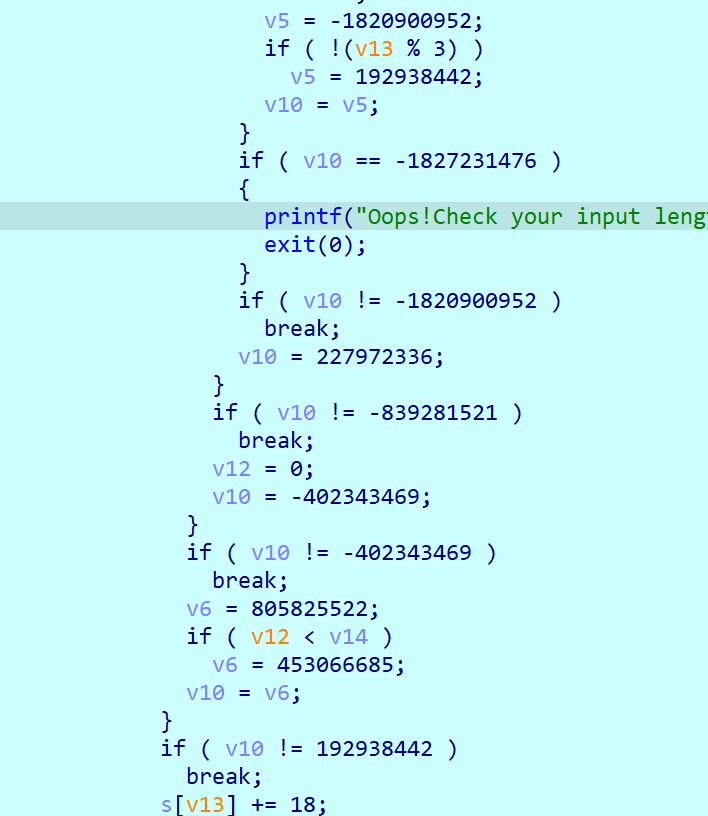
异或i
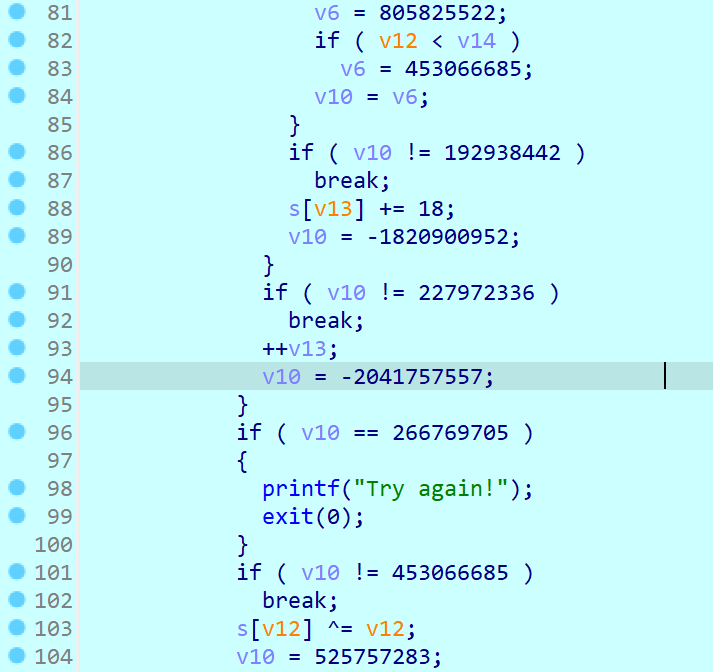
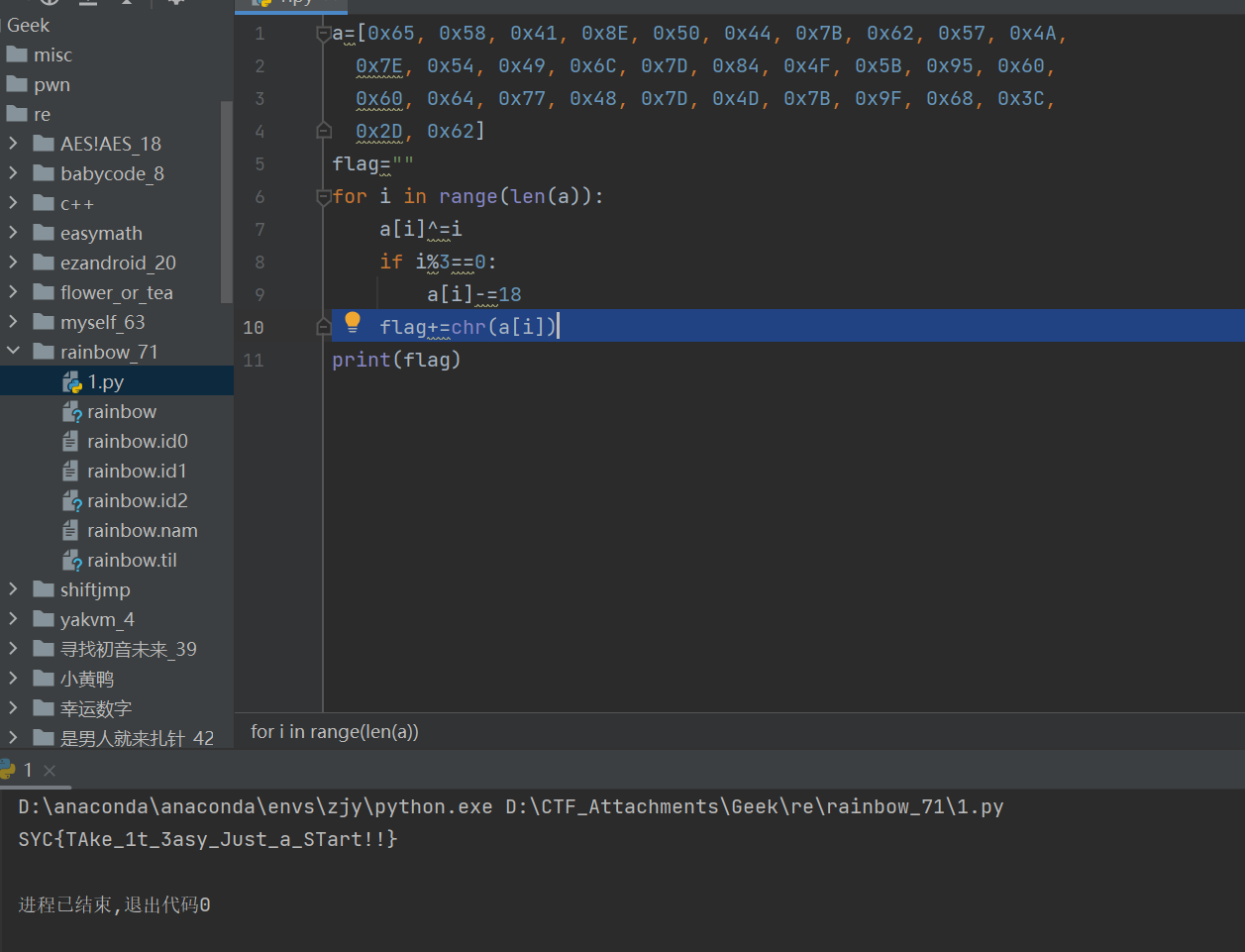
要去混淆,wp说是控制流平坦化,新知识来了😏
这种流程图就很典型

用D-810插件去ollvvm混淆,注意提前用idapyswitch选择3.7的python,可以看以下链接
https://www.yuque.com/u34082223/swqzq3/qr5reox5g6k3q9m3
myself
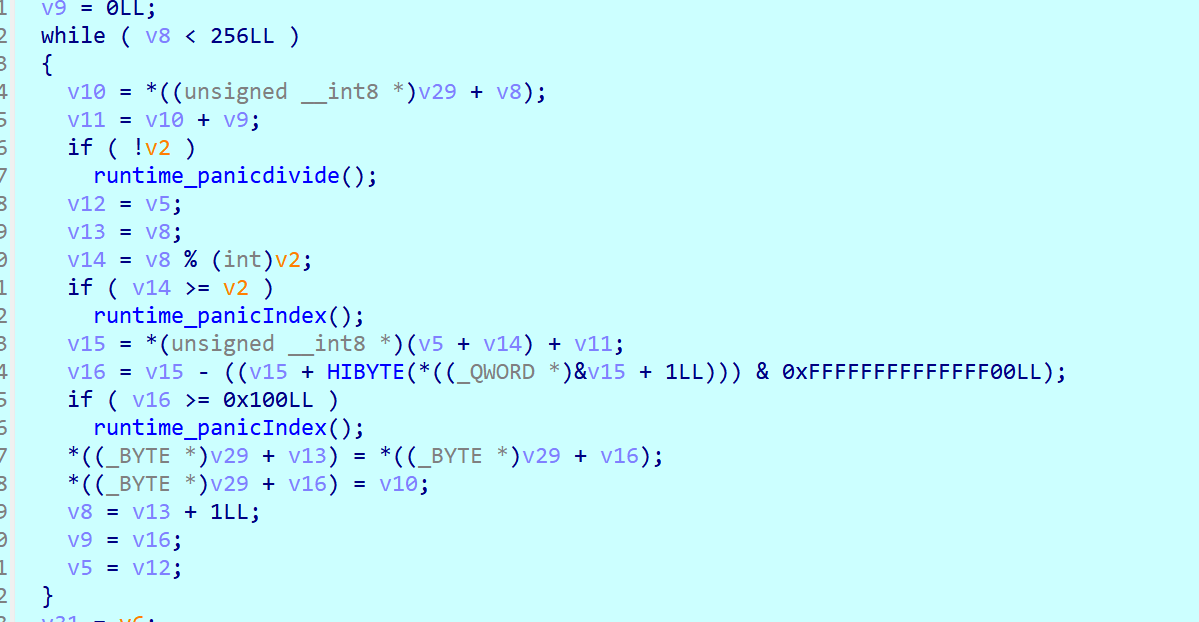
魔改rc4?
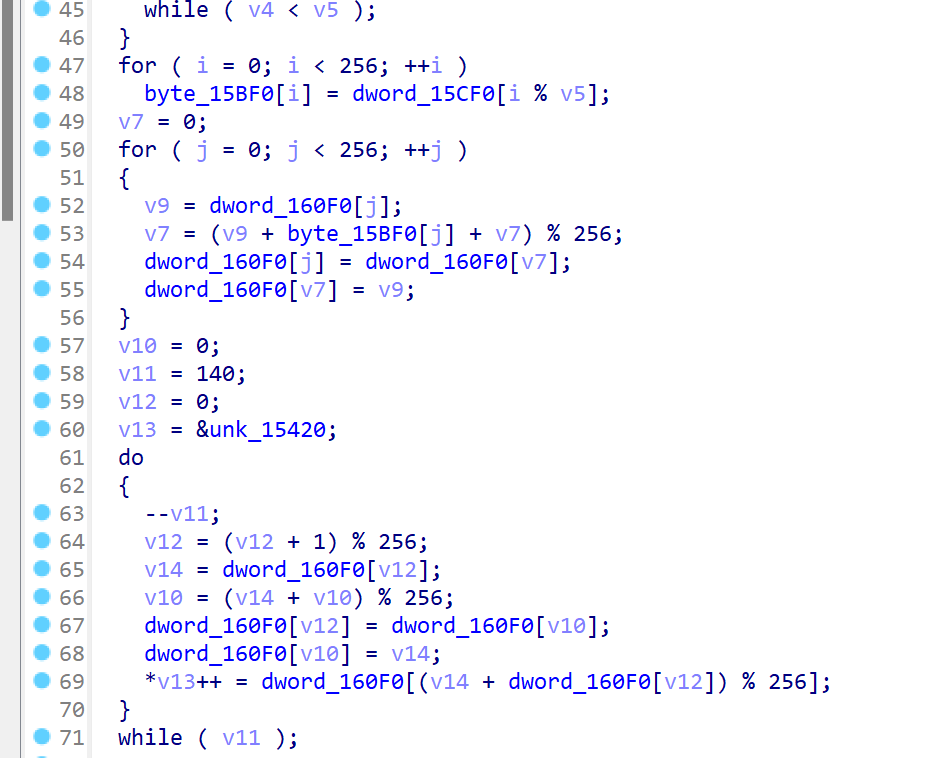
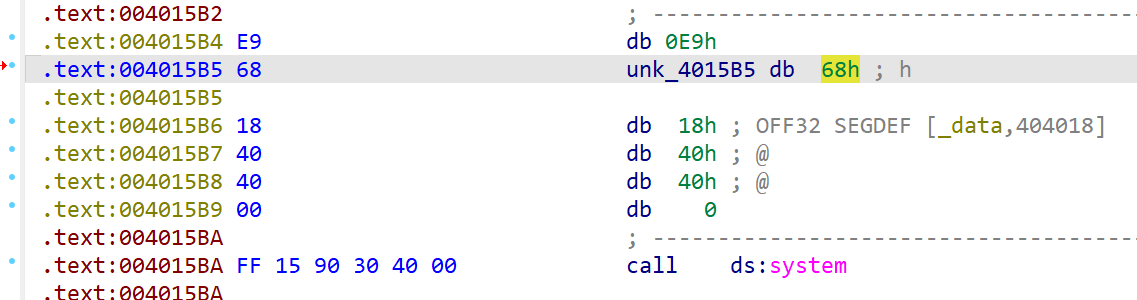
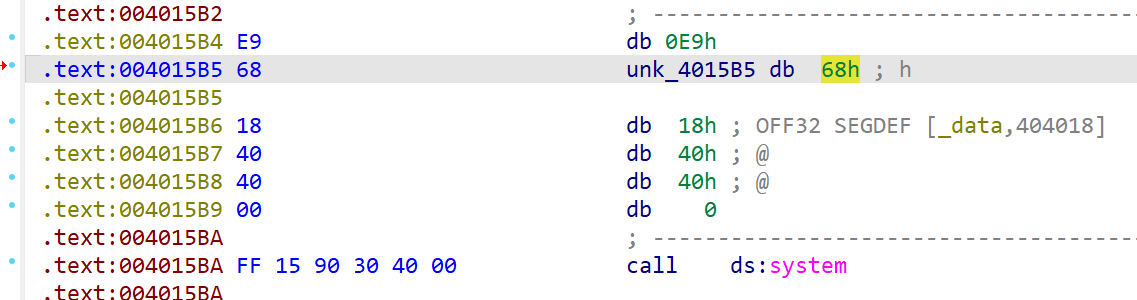
VirtualProtect函数可以修改某个数据段的权限,j将开始的0x8c个地址内存属性设为可读可写可执行
再调用sub_401010(),再sub_4013B0地址开始的0x8c个地址内存属性改回来
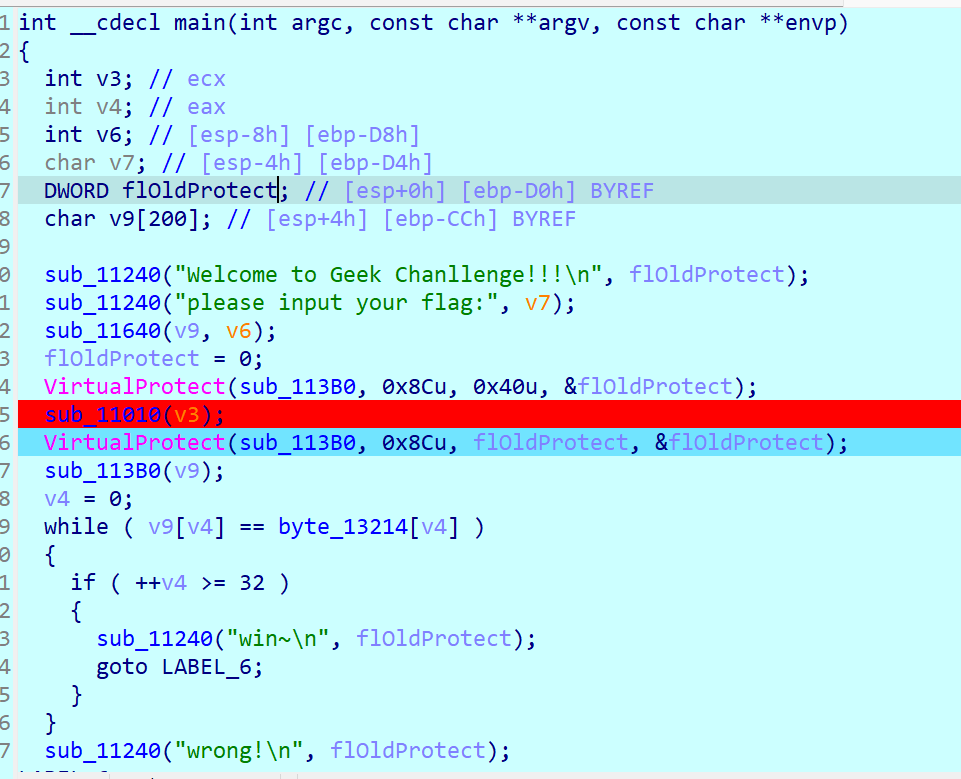
一开始是这样的,就感觉怪怪的
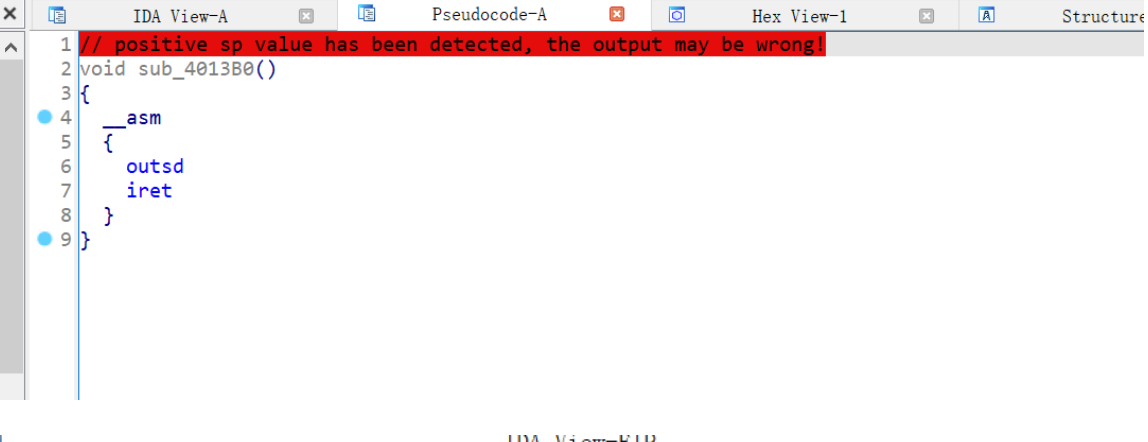
将4013B0起始处一直到第一个retn的汇编全部U掉,再转换成代码,创建函数
变成tea了
1 | |
是男人就来扎针-1
好像挺多算法
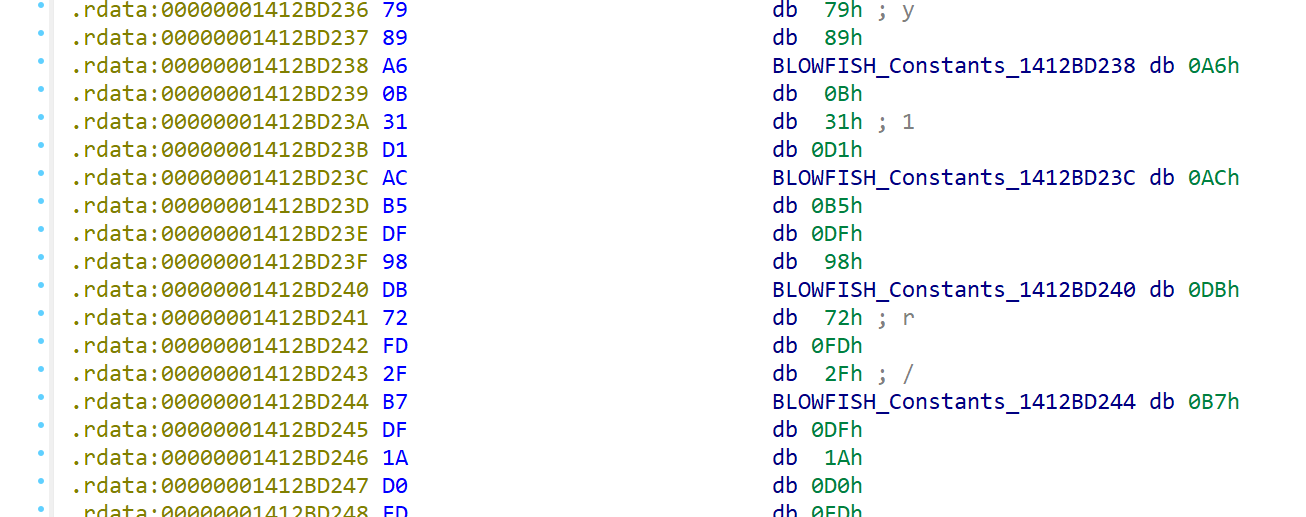
blowfish
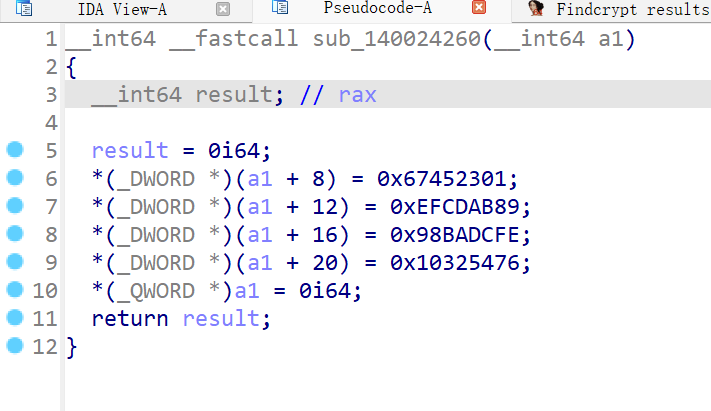
md5或者sha系列
crc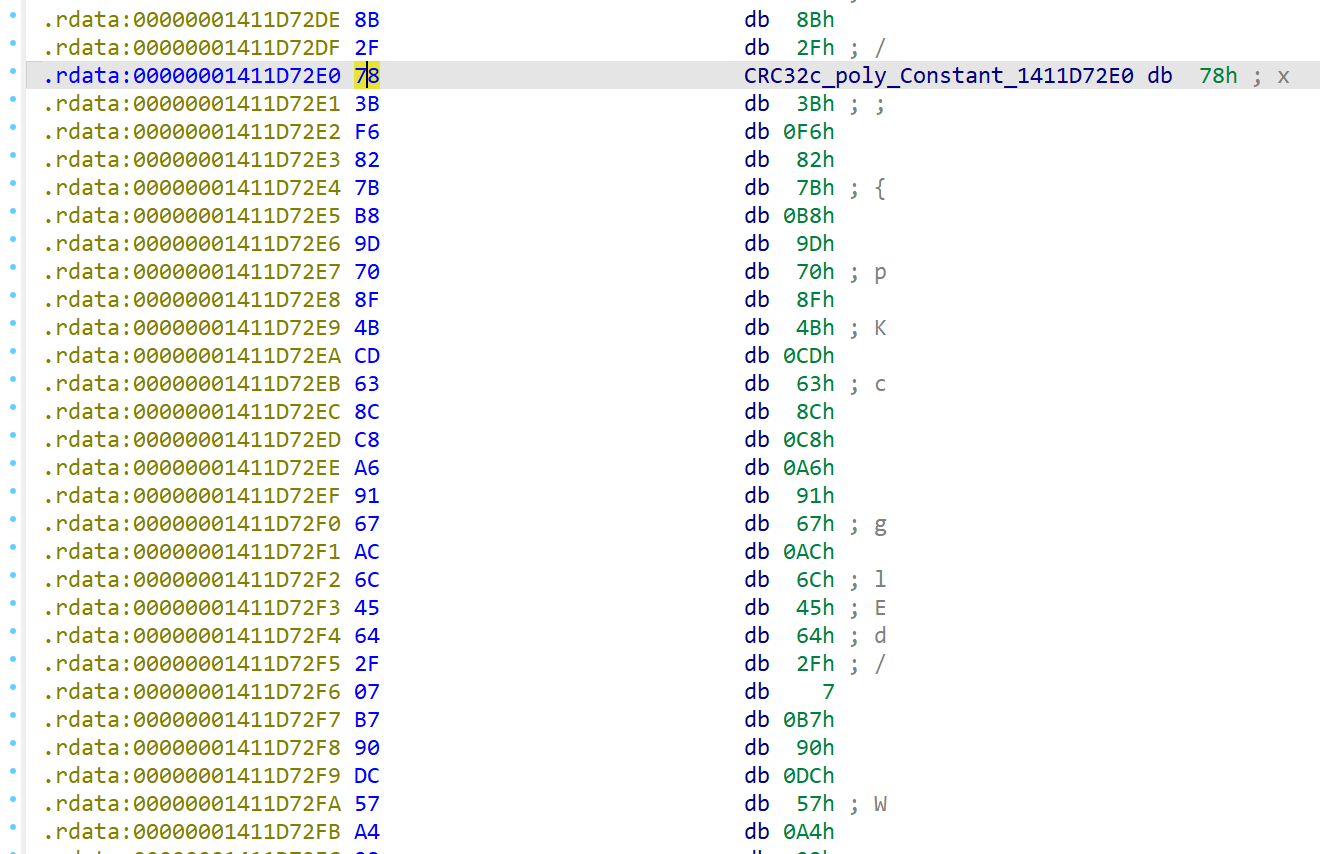
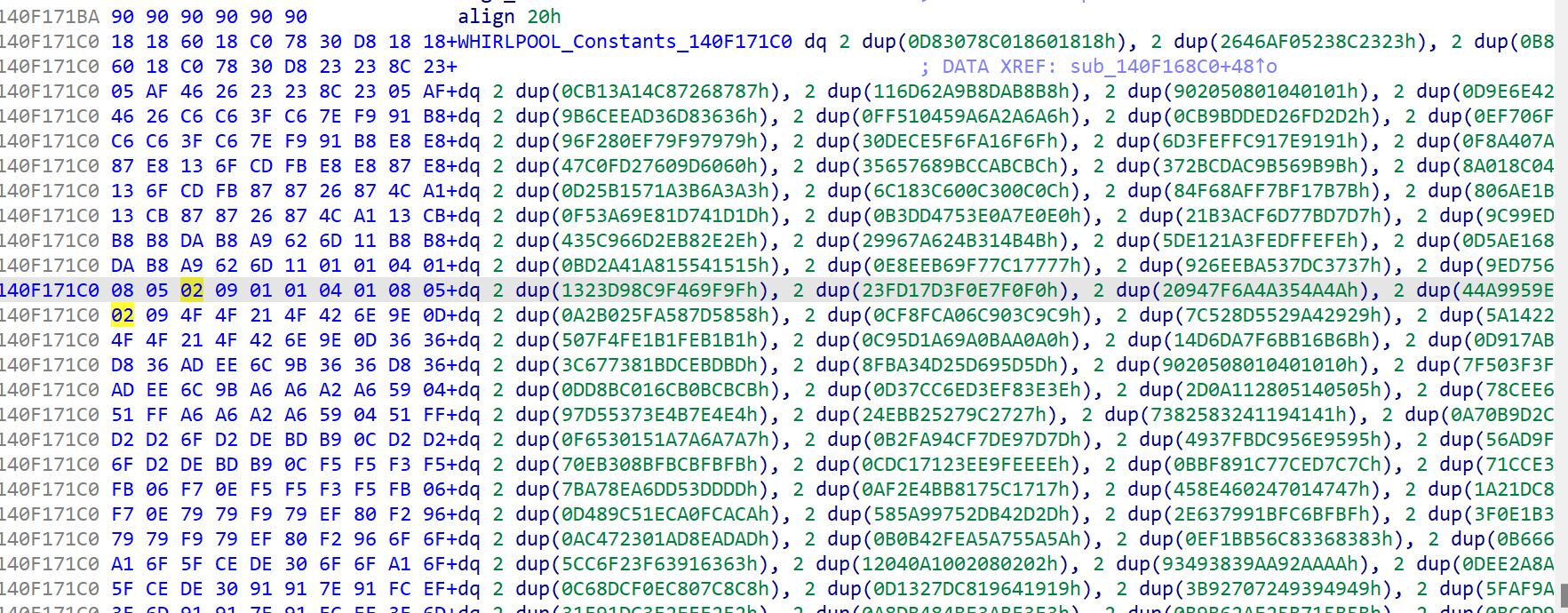
whirlpool
感觉复杂,看wp了
unity游戏逆向,C#,所以用dnSpy打开文件夹中的Assembly-CSharp.dll,分析GameManager
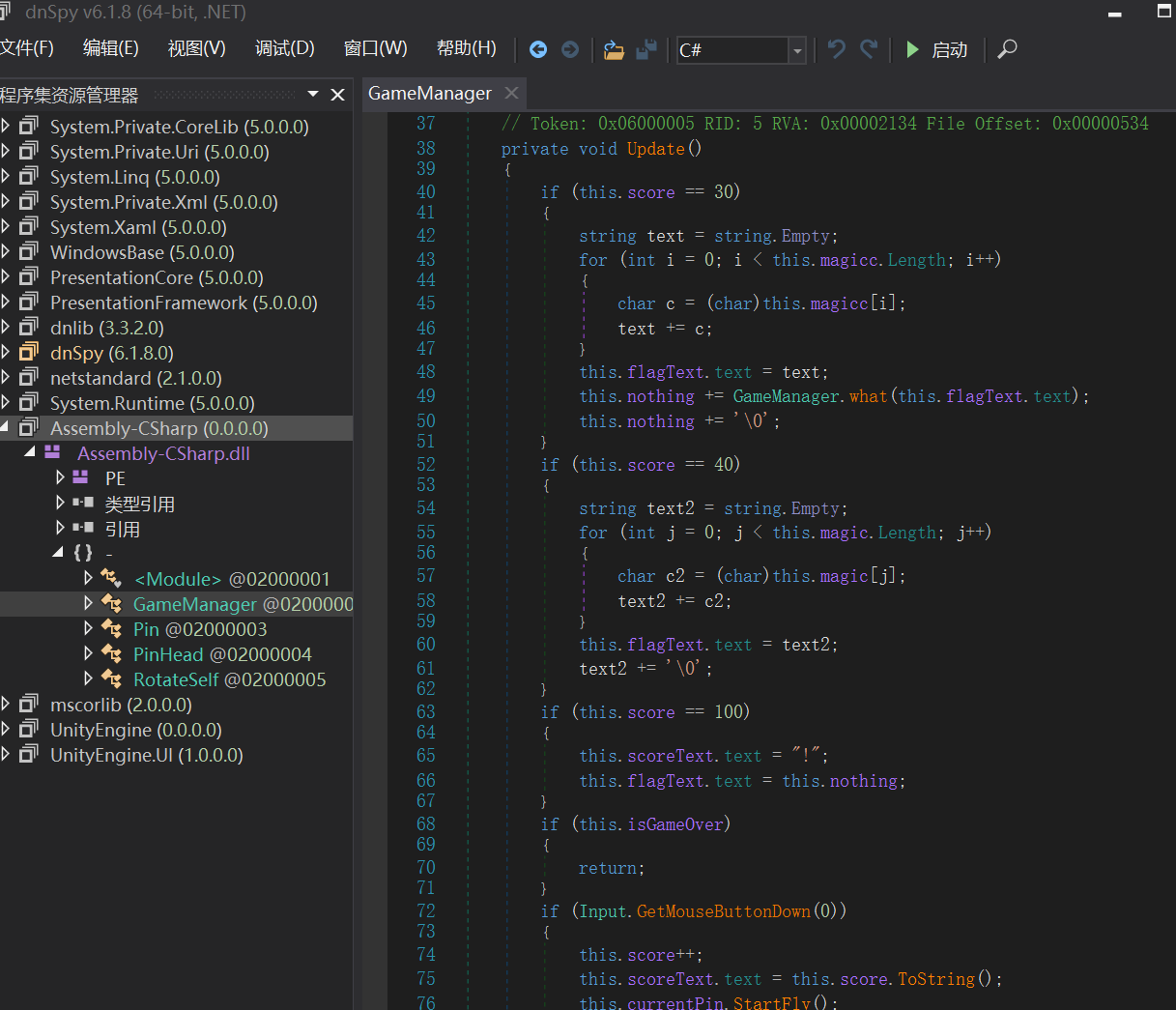
根据点击次数异或
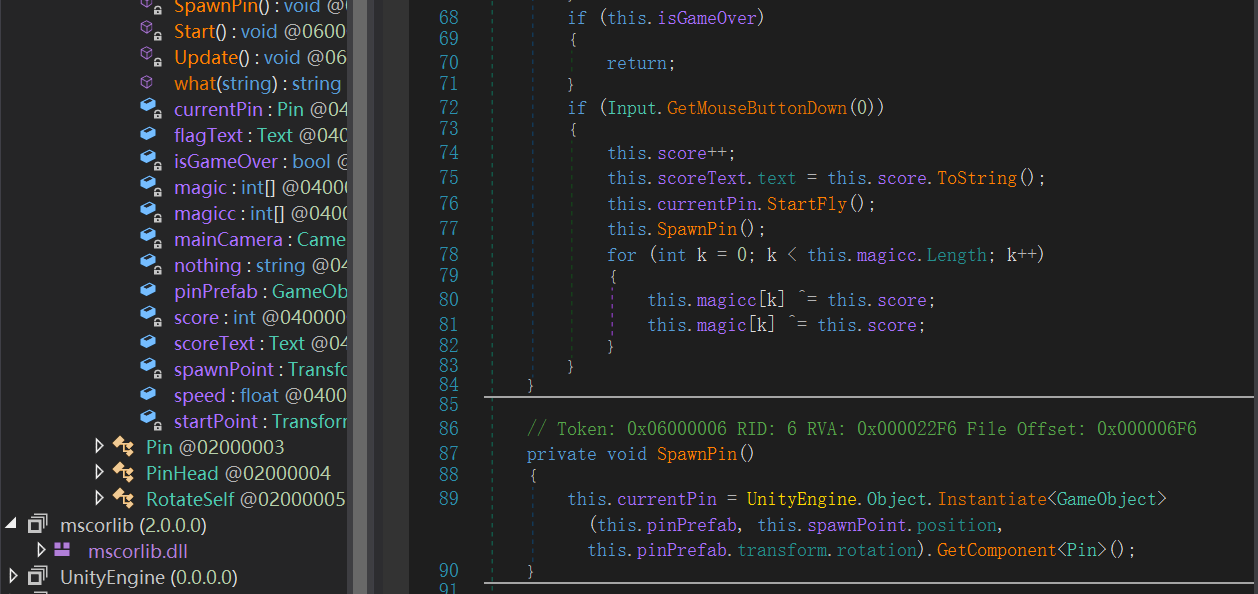
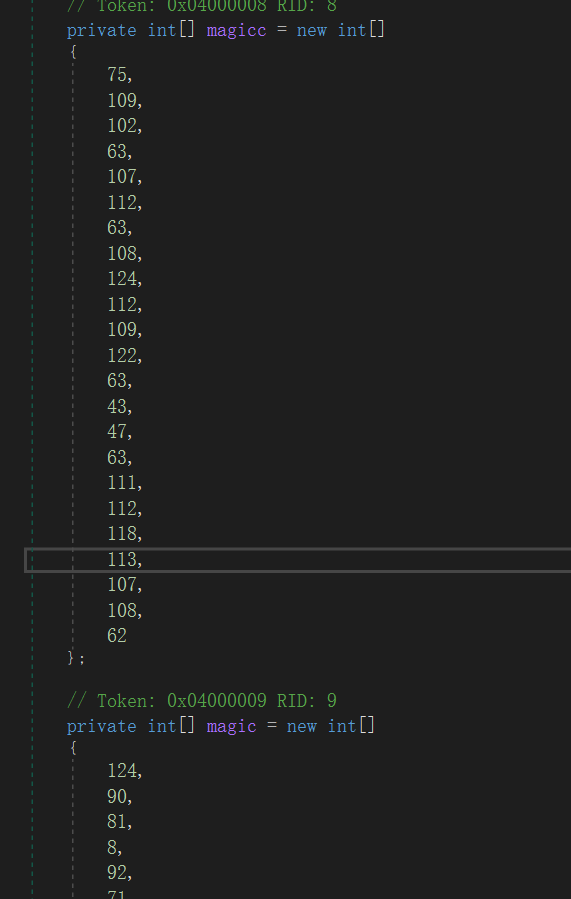
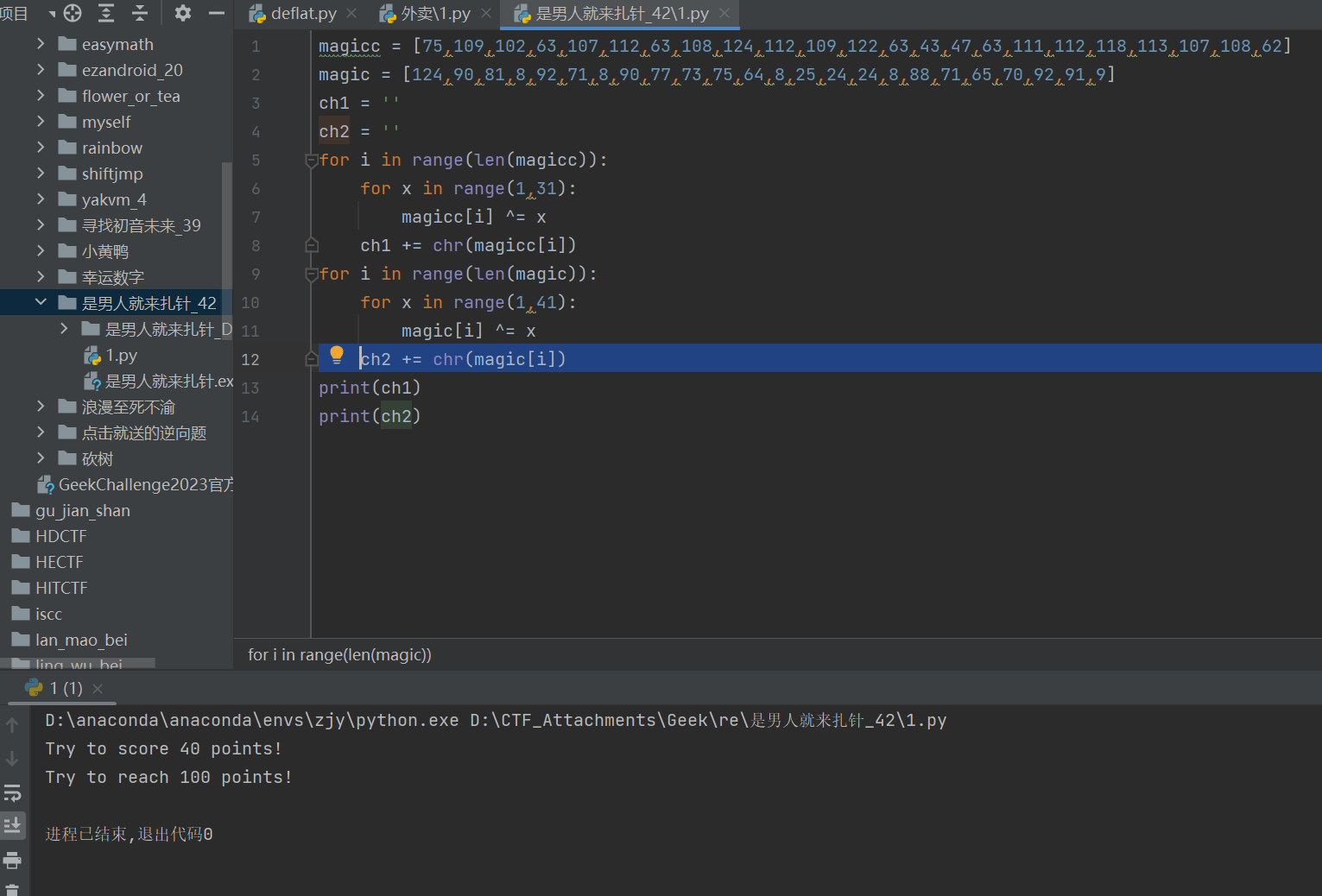
扎了100次
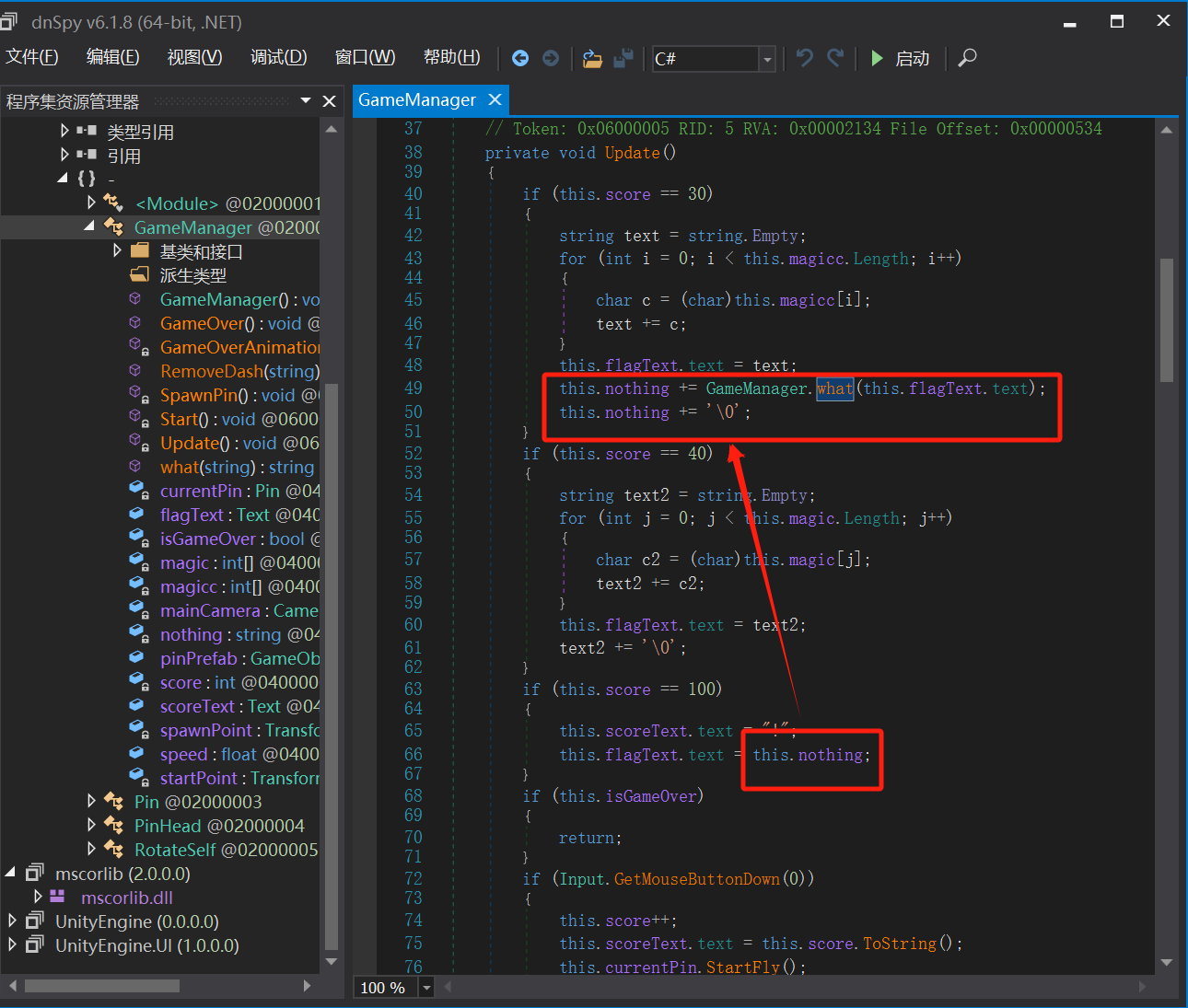
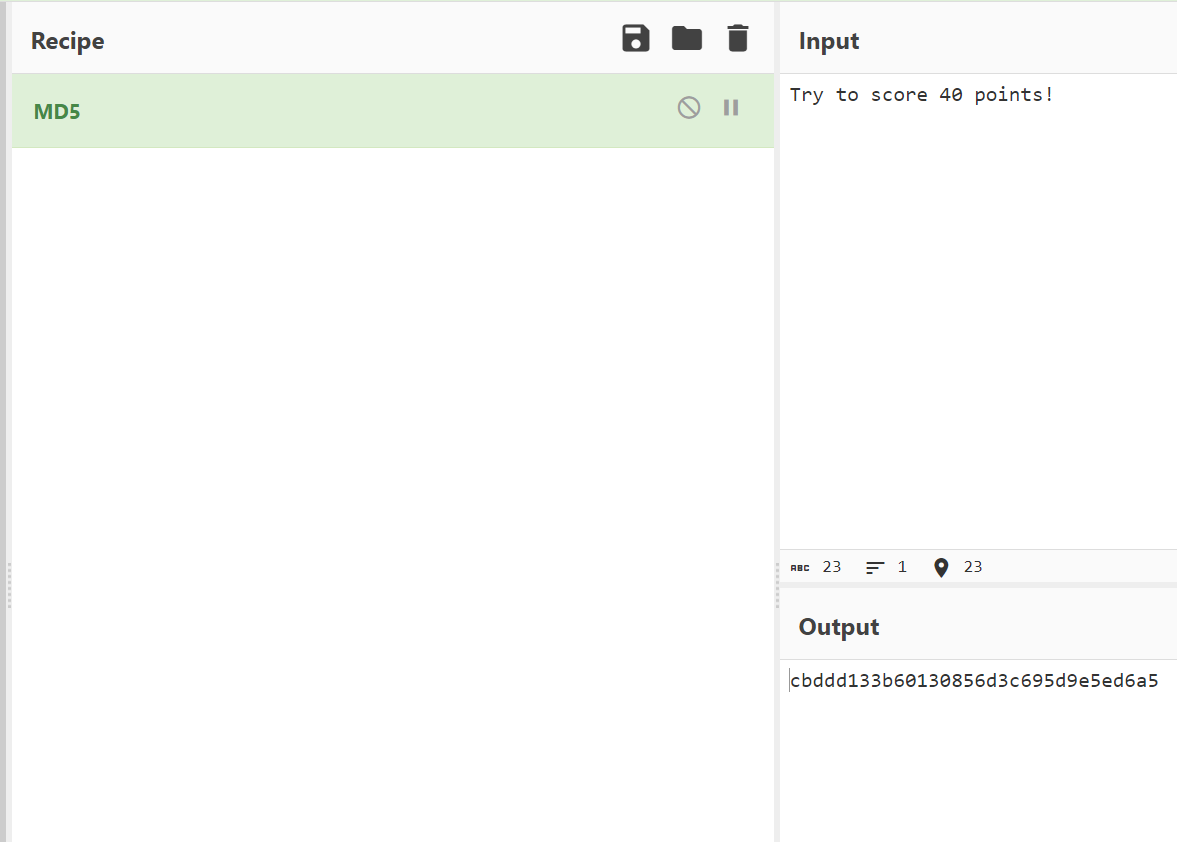
求md5
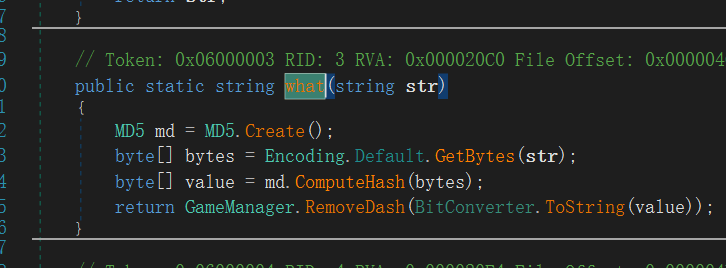
这个大小写有点恶心,最后flag是大写
还有师傅用的CE,第一次CE用到题目上

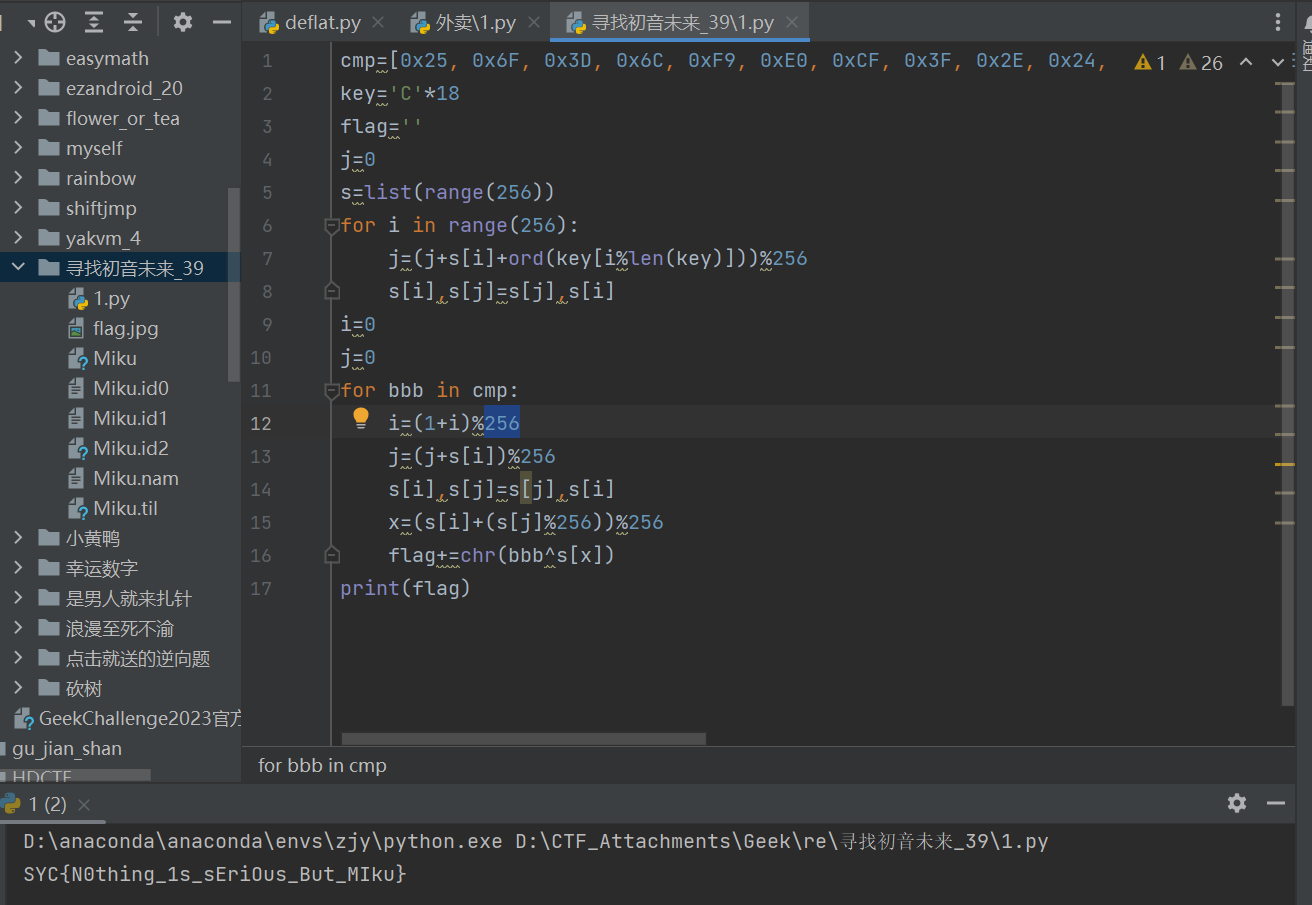
寻找初音未来-1
rc4之后直接去和密文比较
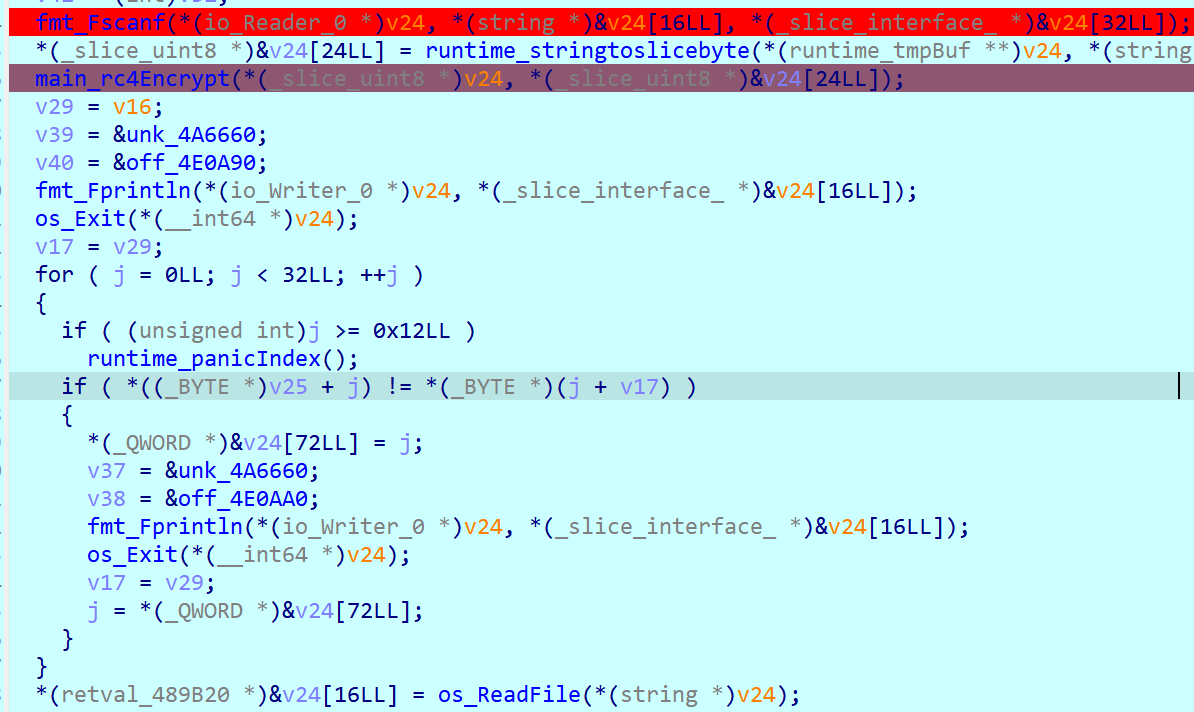
伪c和汇编的不一样
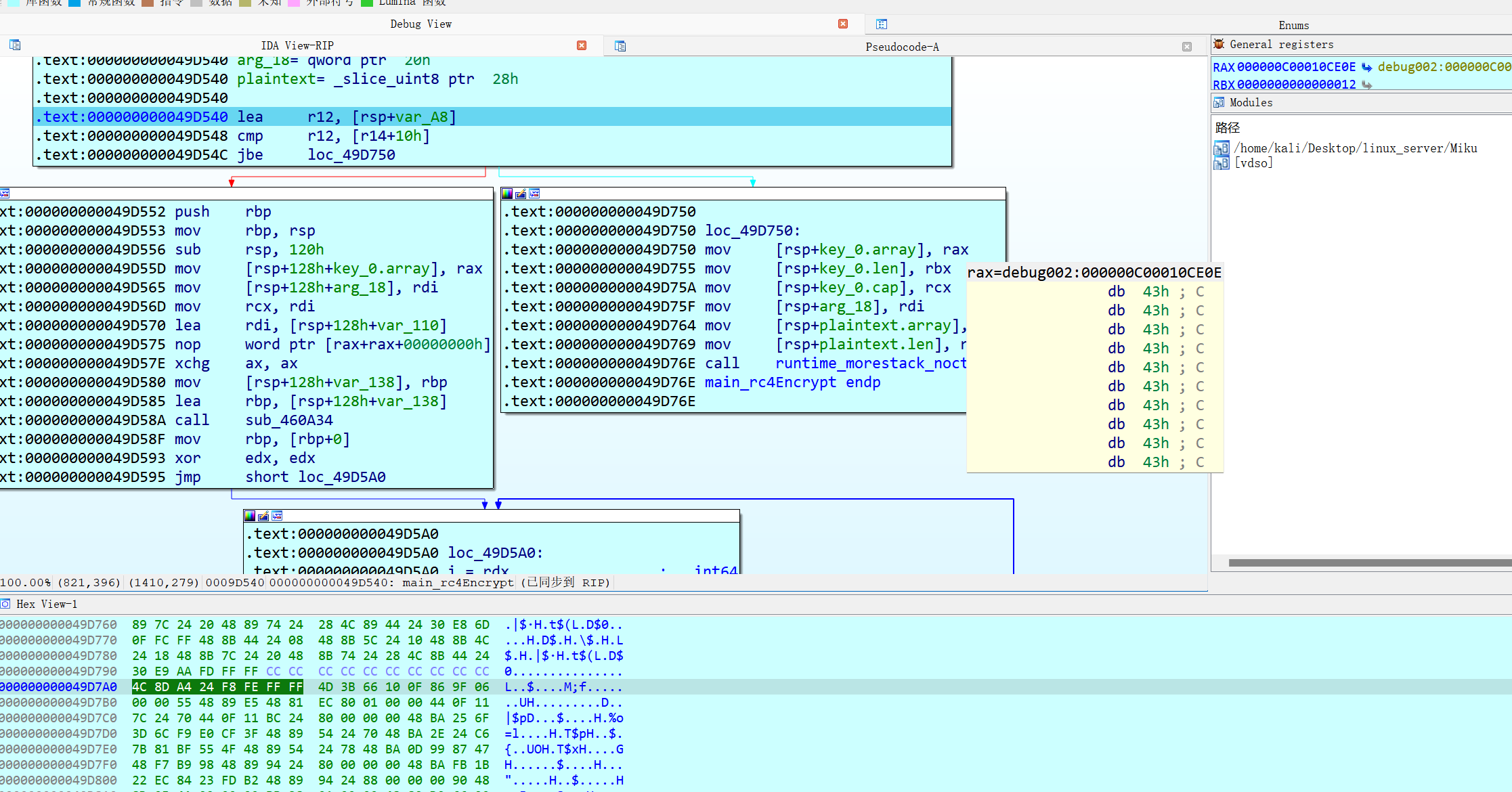
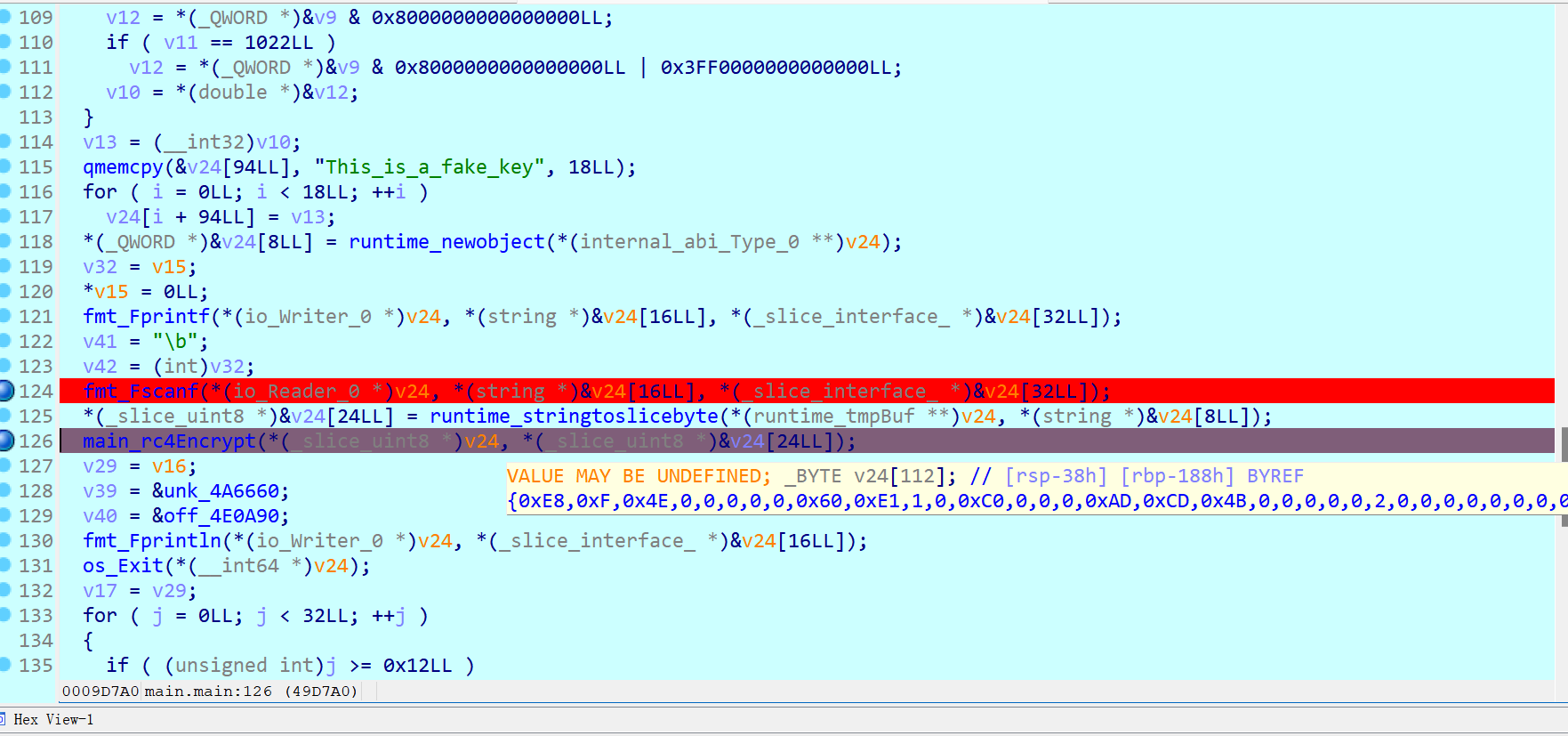
这里伪c可能不准,算法里看不到key
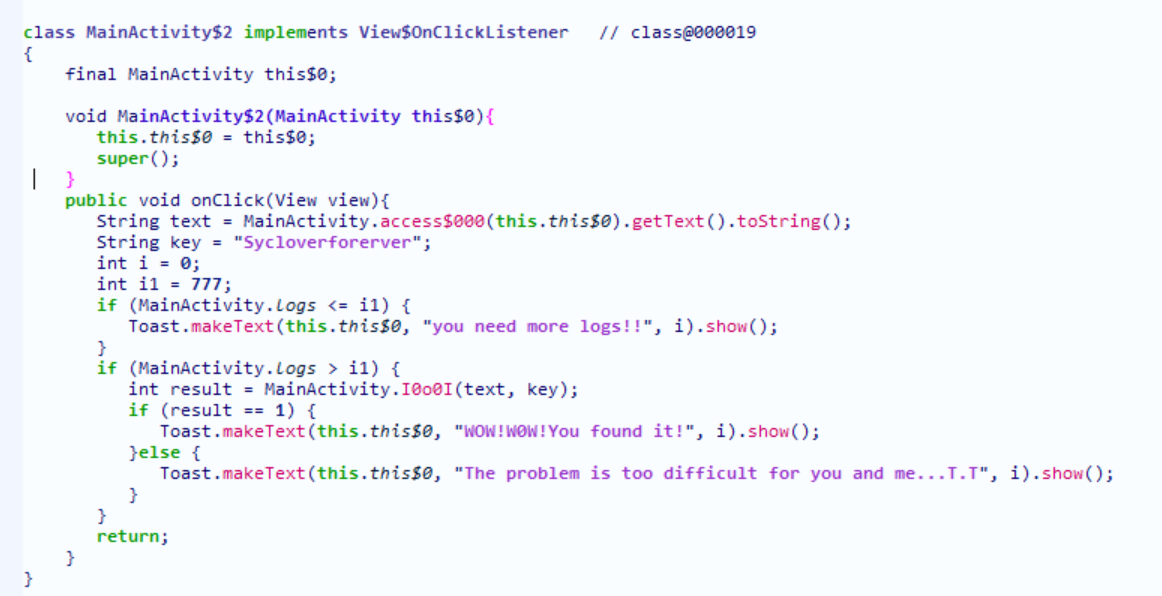
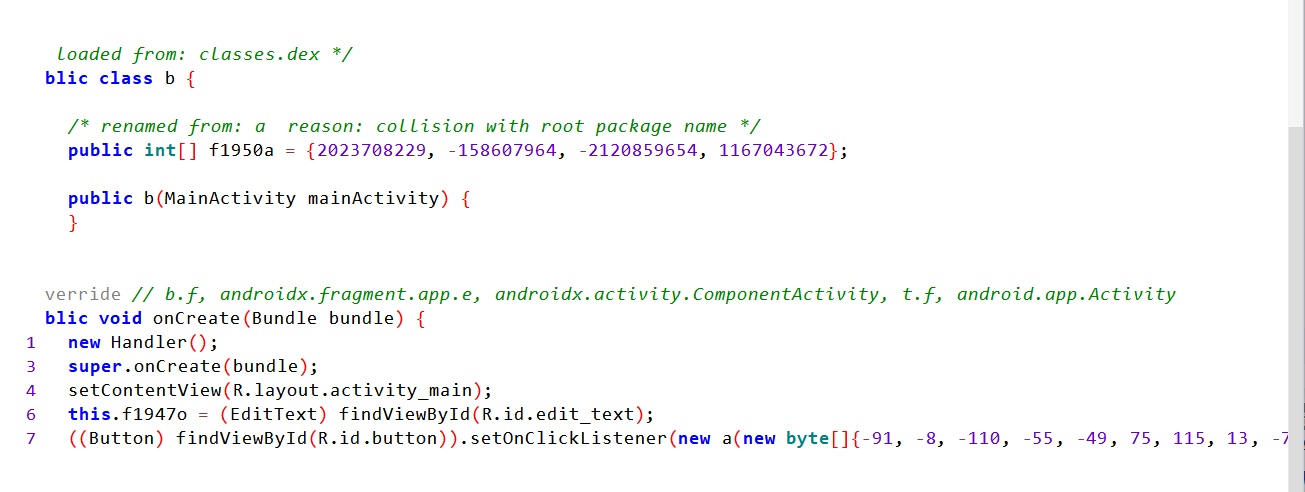
ezAndroid-1
在mainActivity找到密文和main函数
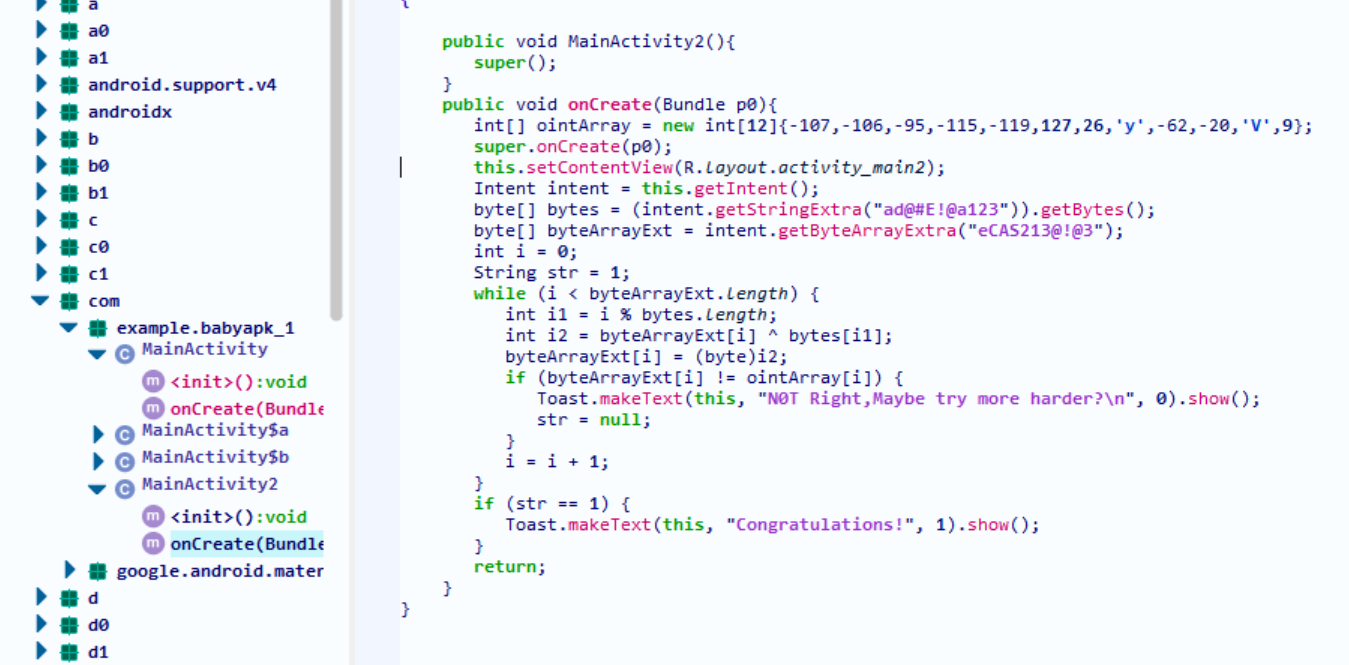
搜string
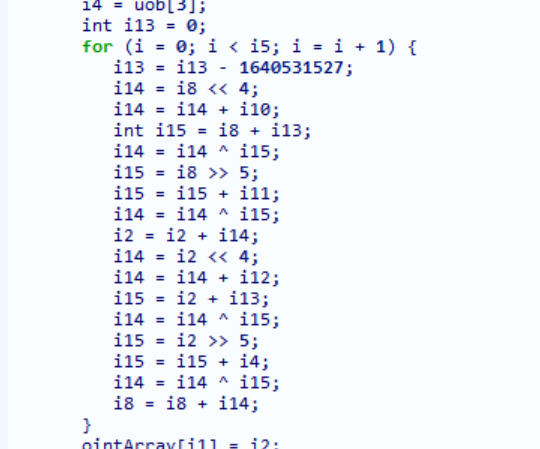
根据题目提示,往上翻得到tea
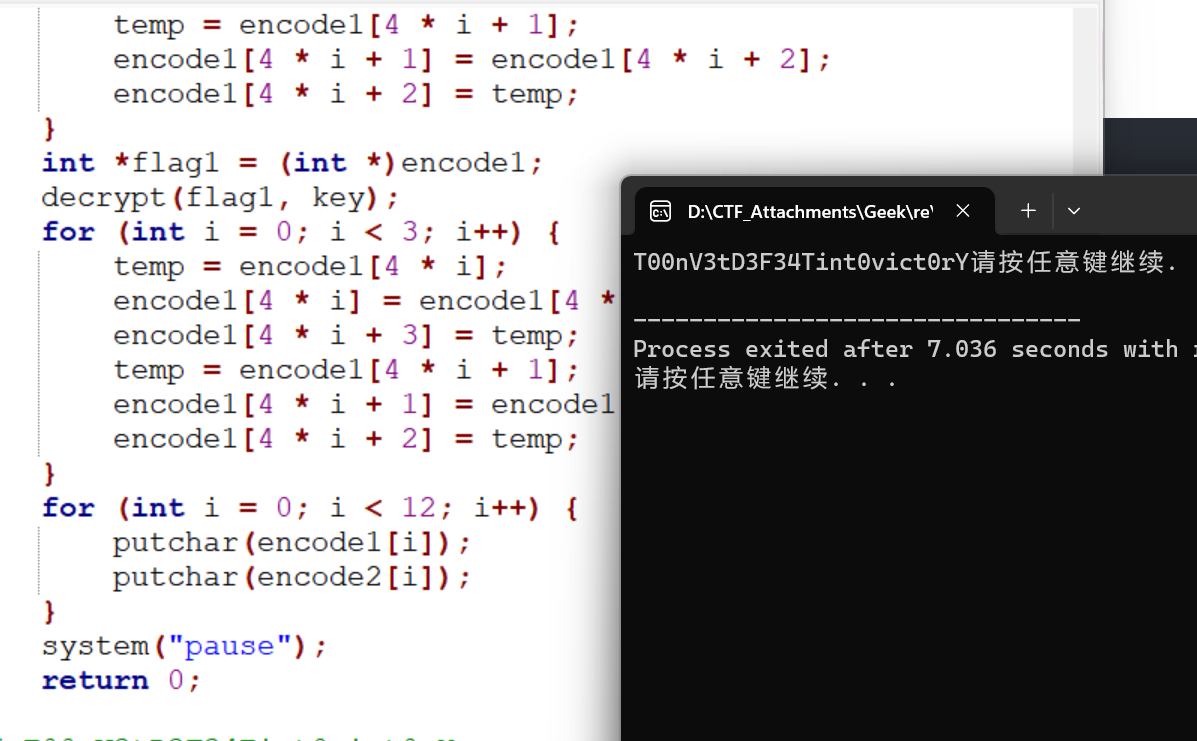
长度为24,奇数位放到str1,偶数位放到str2
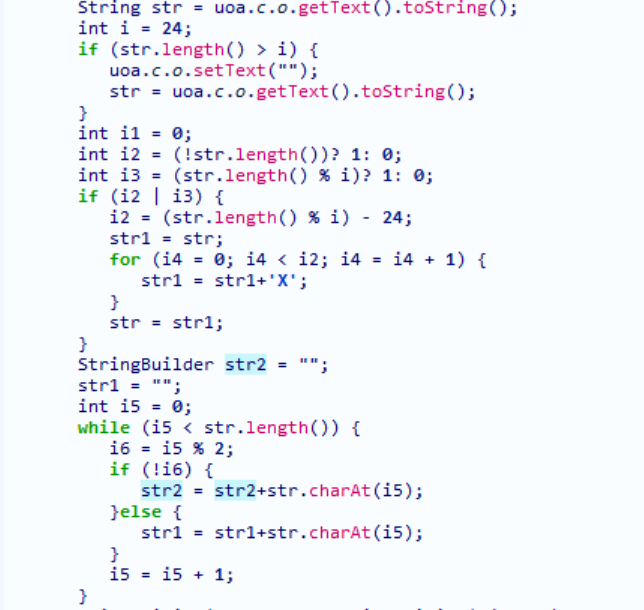
总体思路:str2->ointArray->uobyteArray^str1->密文
GDA分析有点问题
str2->ointArray->uobyteArray->密文1
密文1^数组->密文2
jadx的tea效果比较好
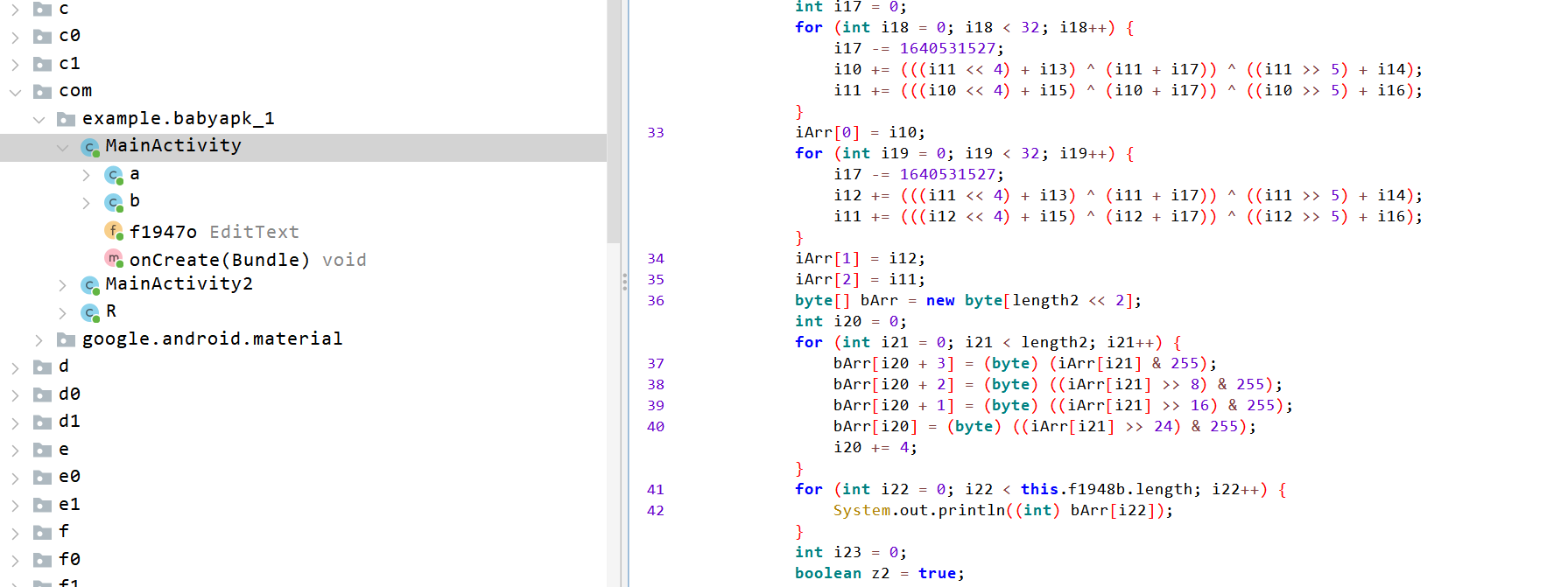
tea的密文和key
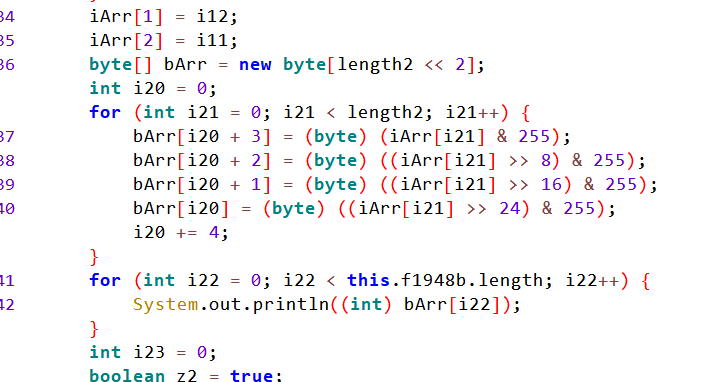
按位运算,实质上是bytes数组转换成了int数组iArr
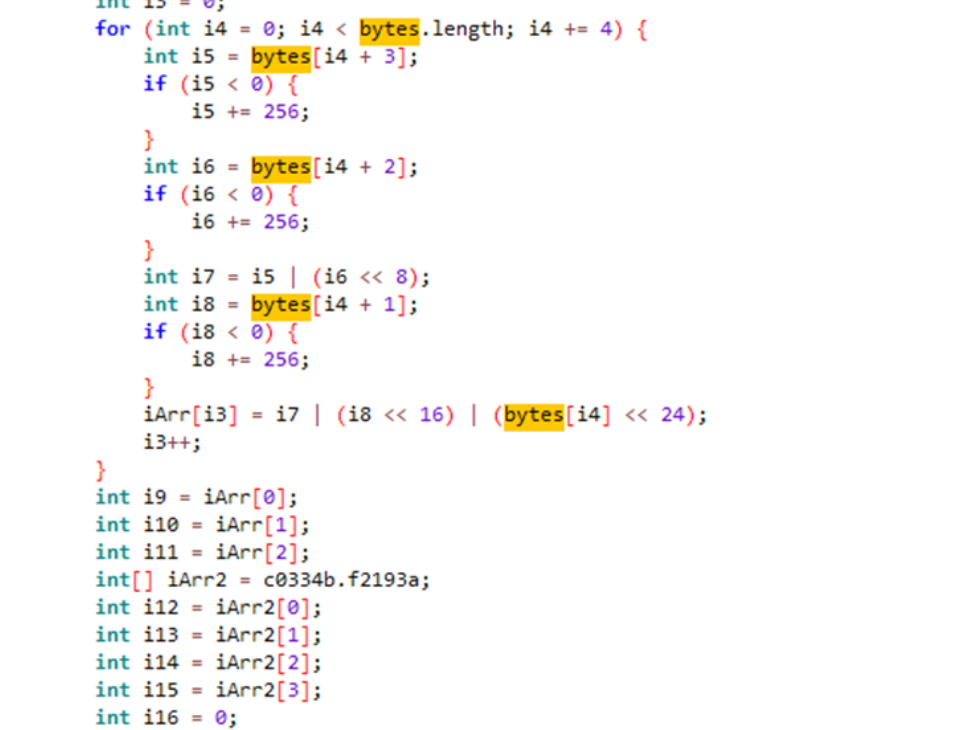
下面是int逆变换到bytes,由此也可猜上面的功能
1 | |
AES?AES!-1
密文
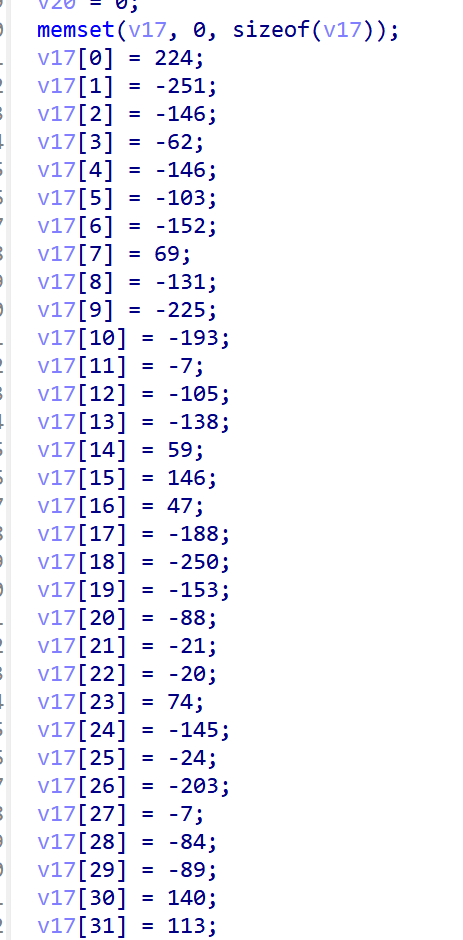
明显的s盒
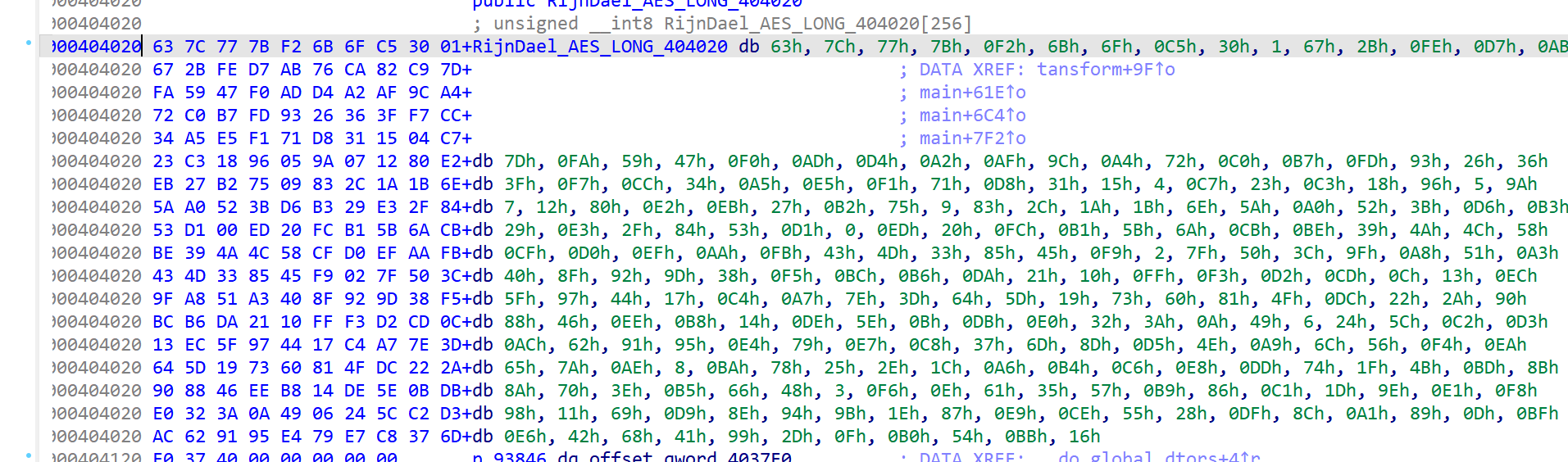
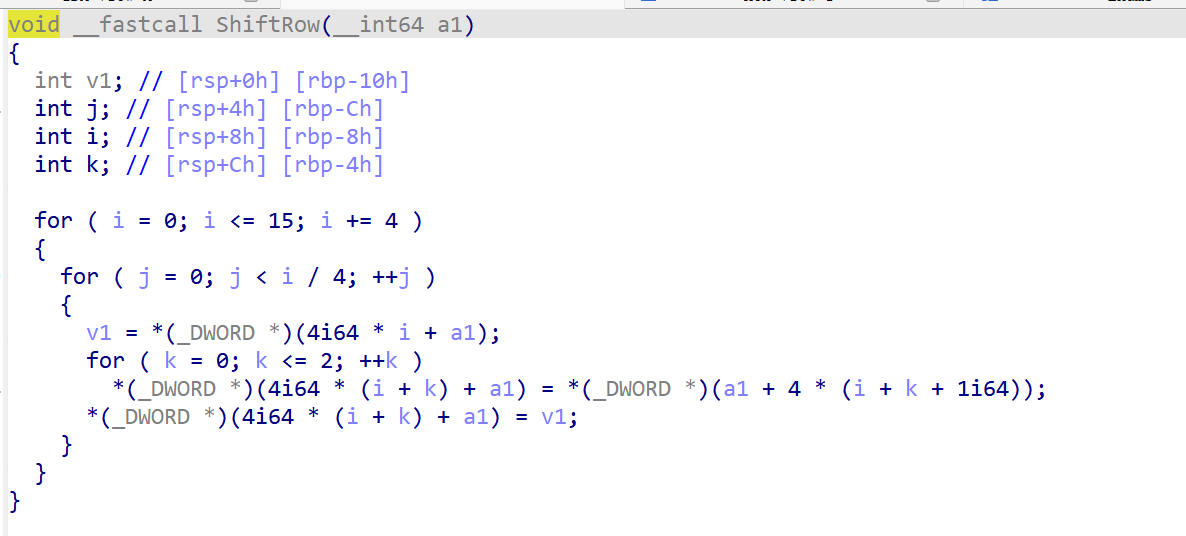
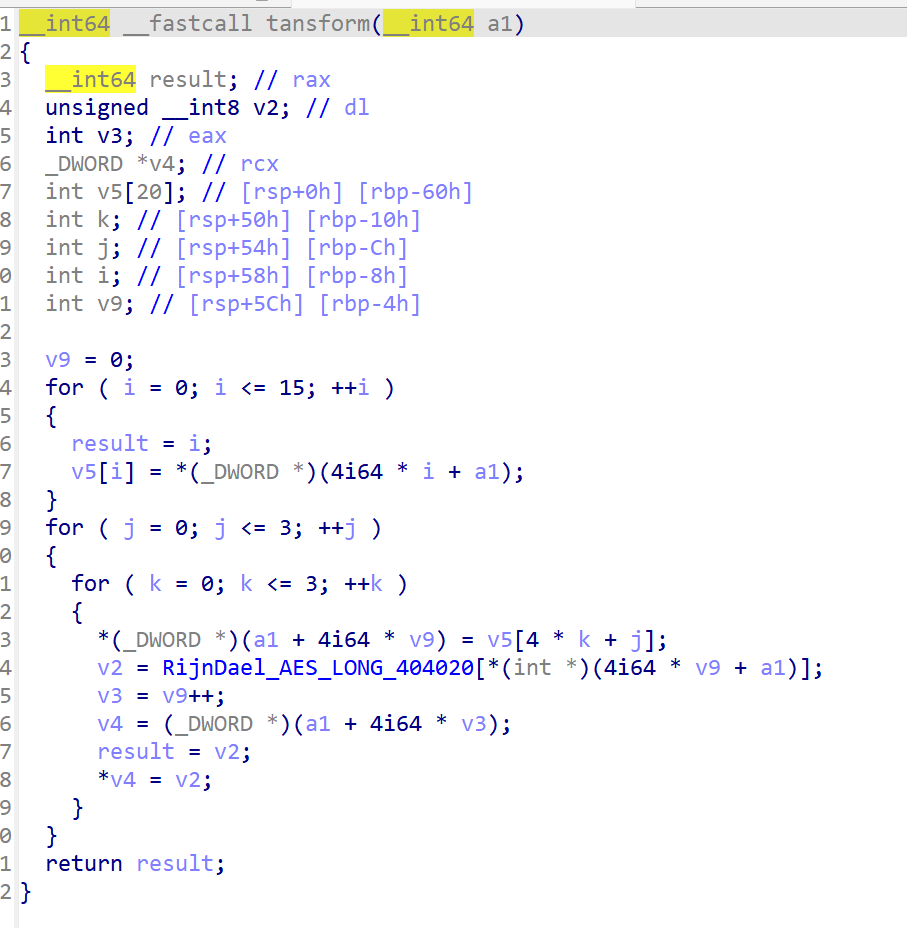
一开始是轮密钥(和s和异或),后面行位移和列混淆,两次行位移针对同一个数组,v6只不过是v5+64,也可以认为只有针对全部的一次操作
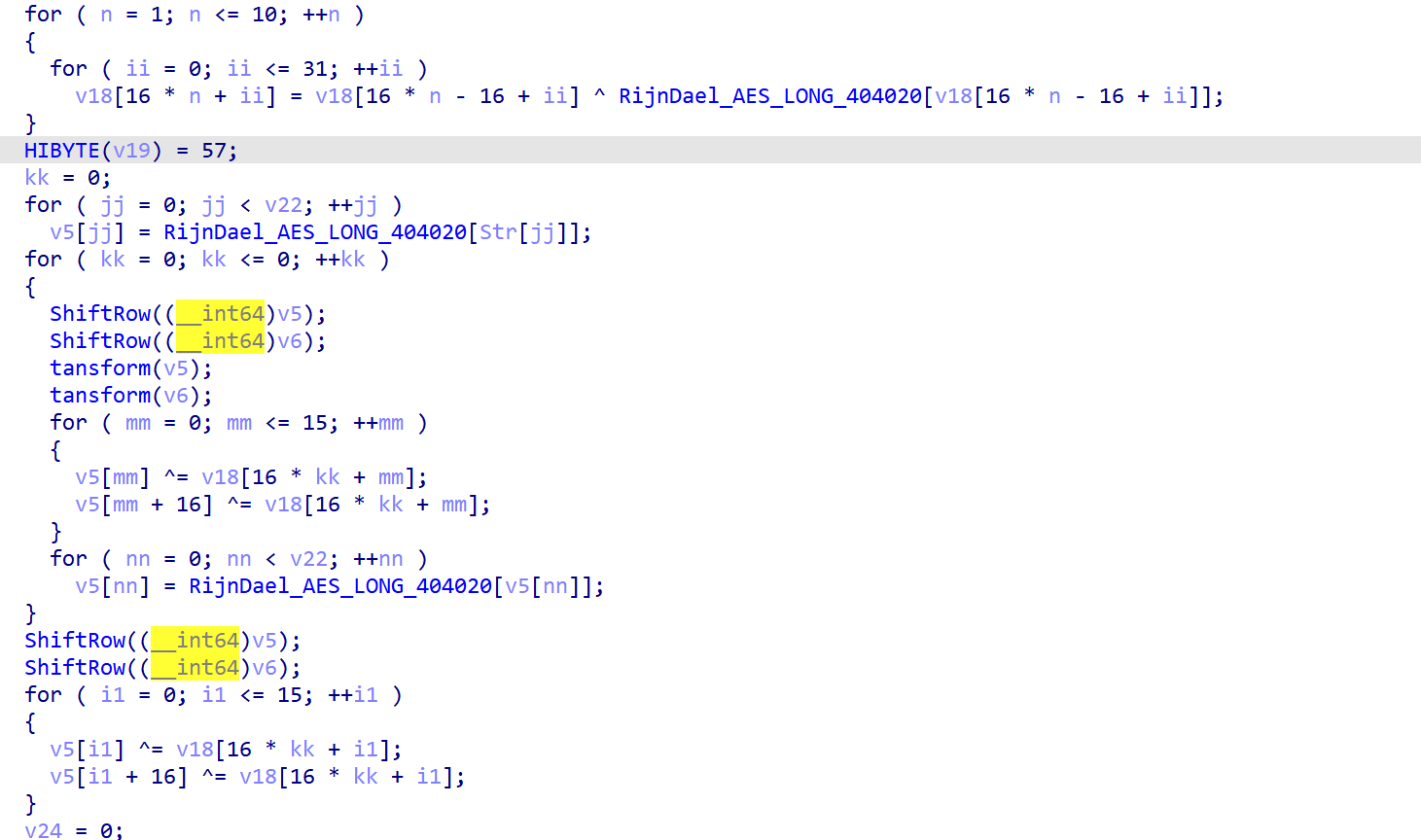
异或s盒得到密钥(调试的时候输入aaaaa.aaaalaaaaaa0aaaaaaaaaaaaaa)
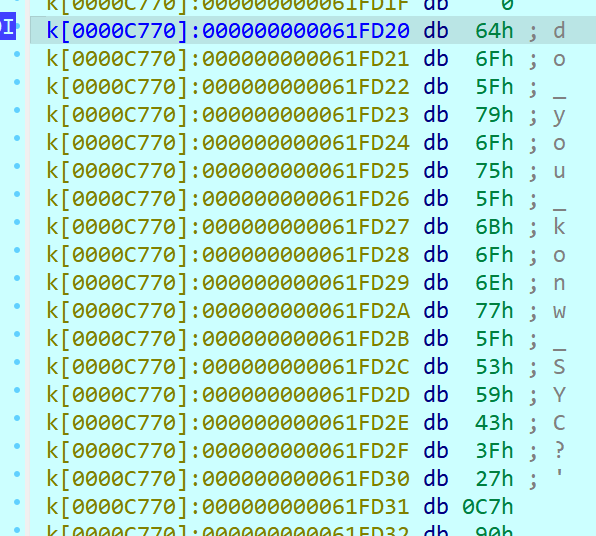
行位移和列混淆都简化了
1 | |