HECTF2024部分wp
Re
littleasm
1 | |
babyre
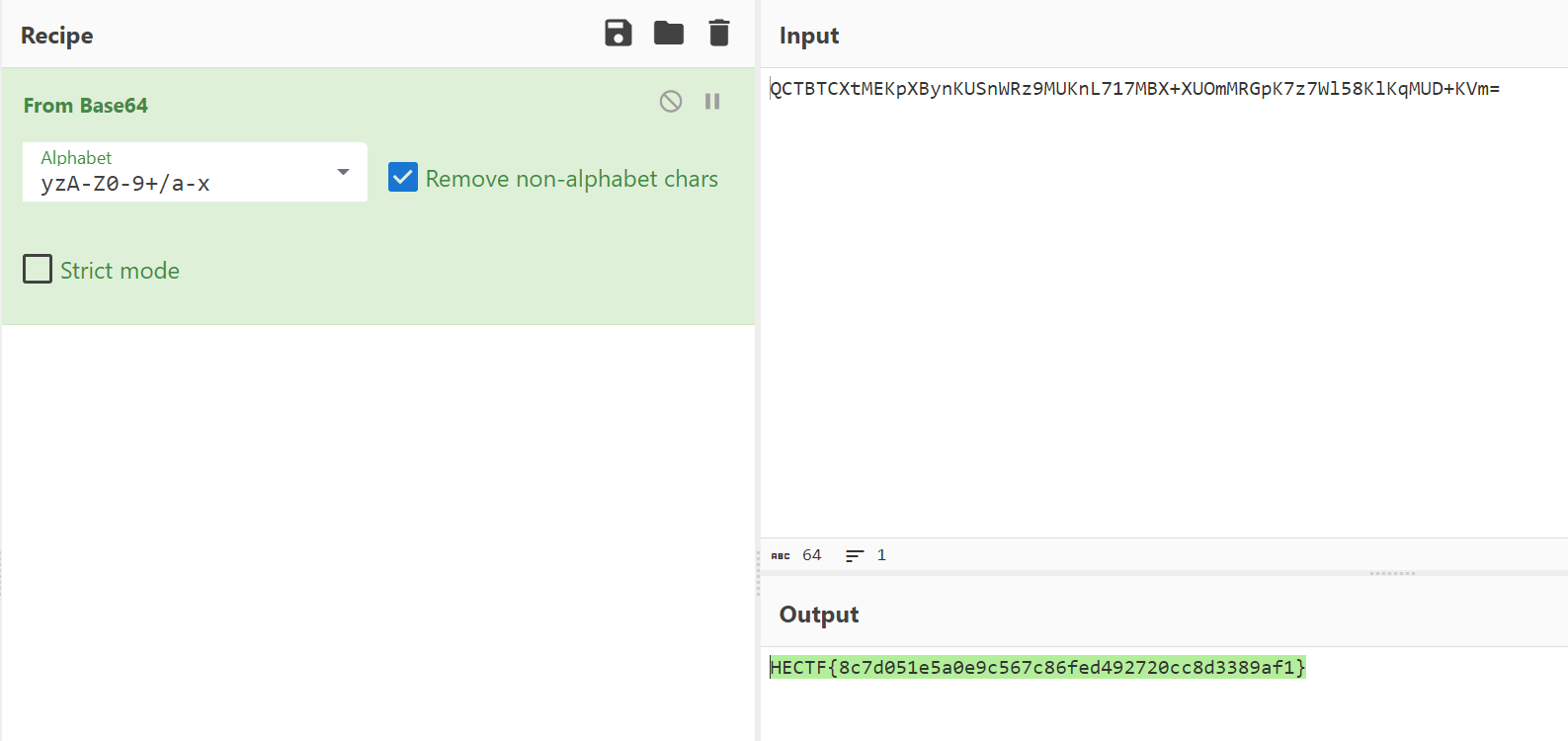
base64变表
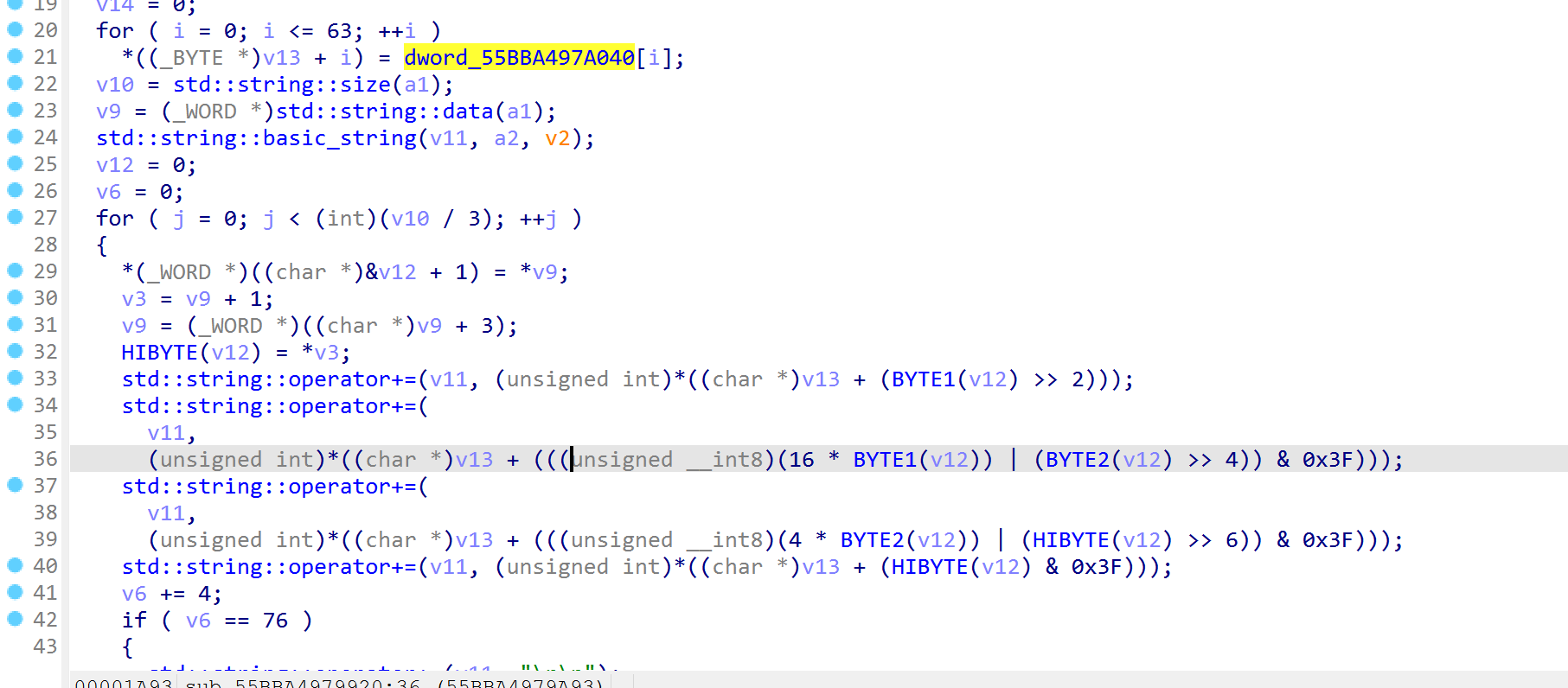
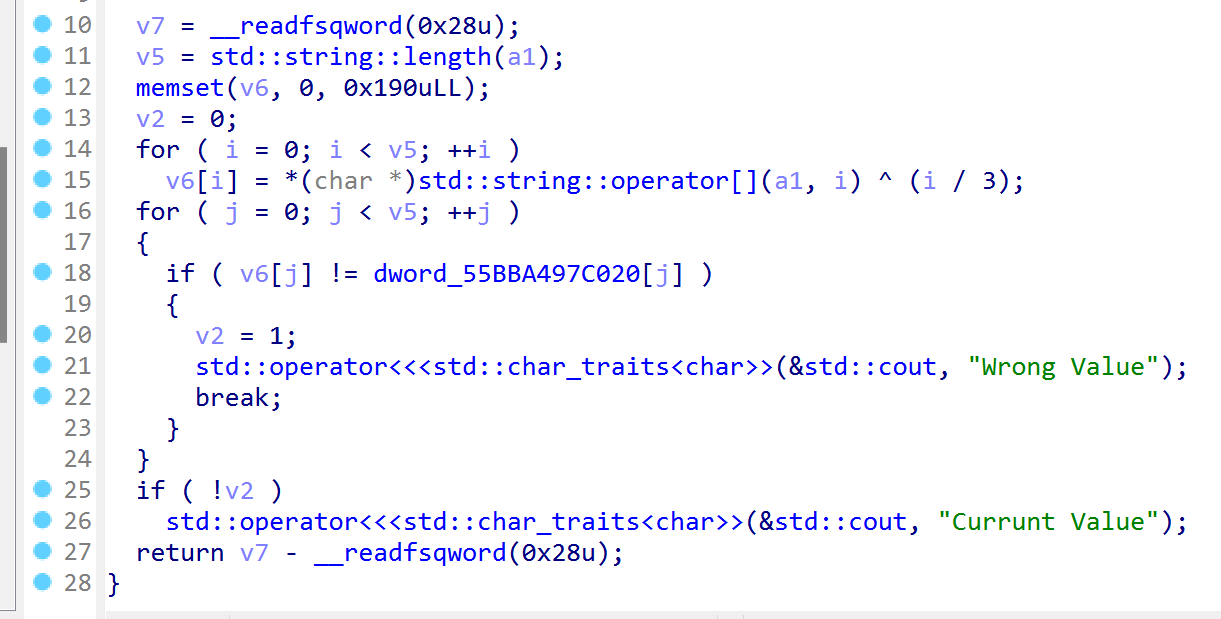
异或之后直接比较
1 | |
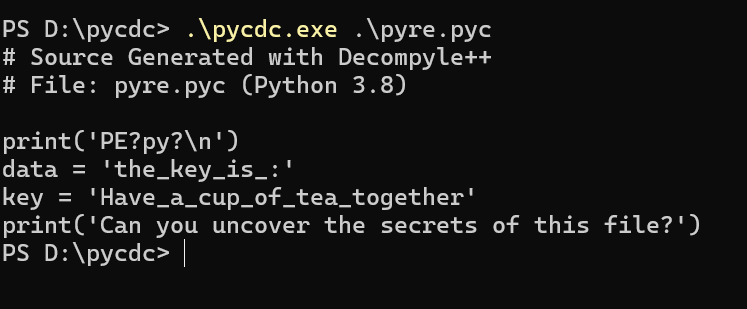
pyre
python反编译,所有exe开头都是4D4E
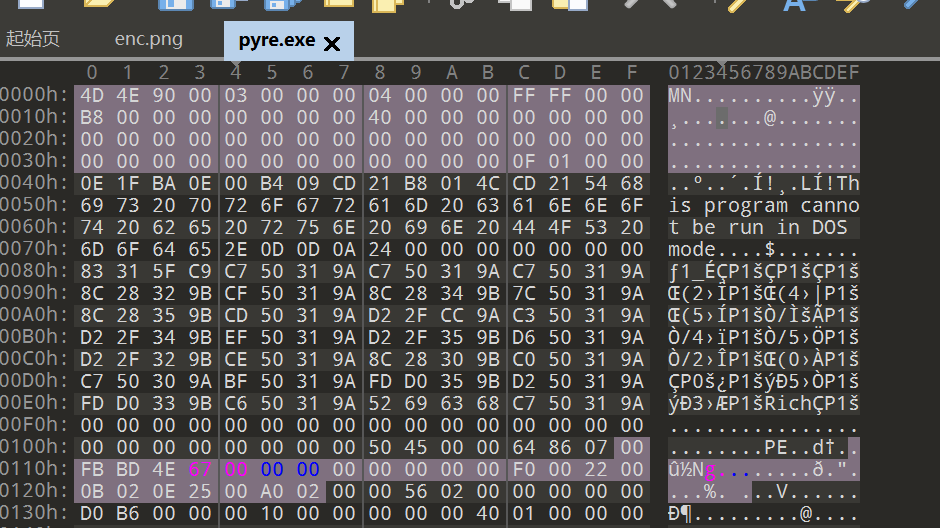
得到压缩包密码
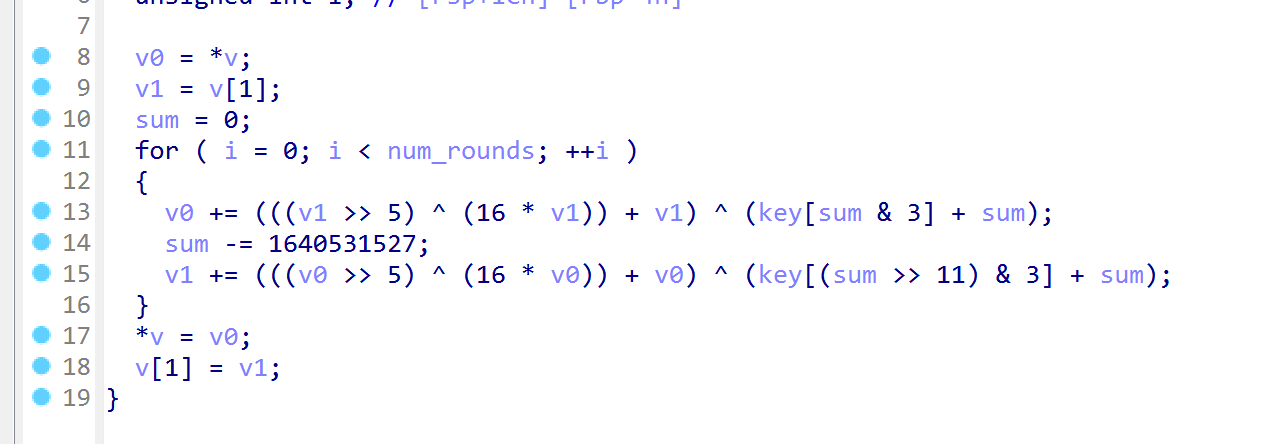
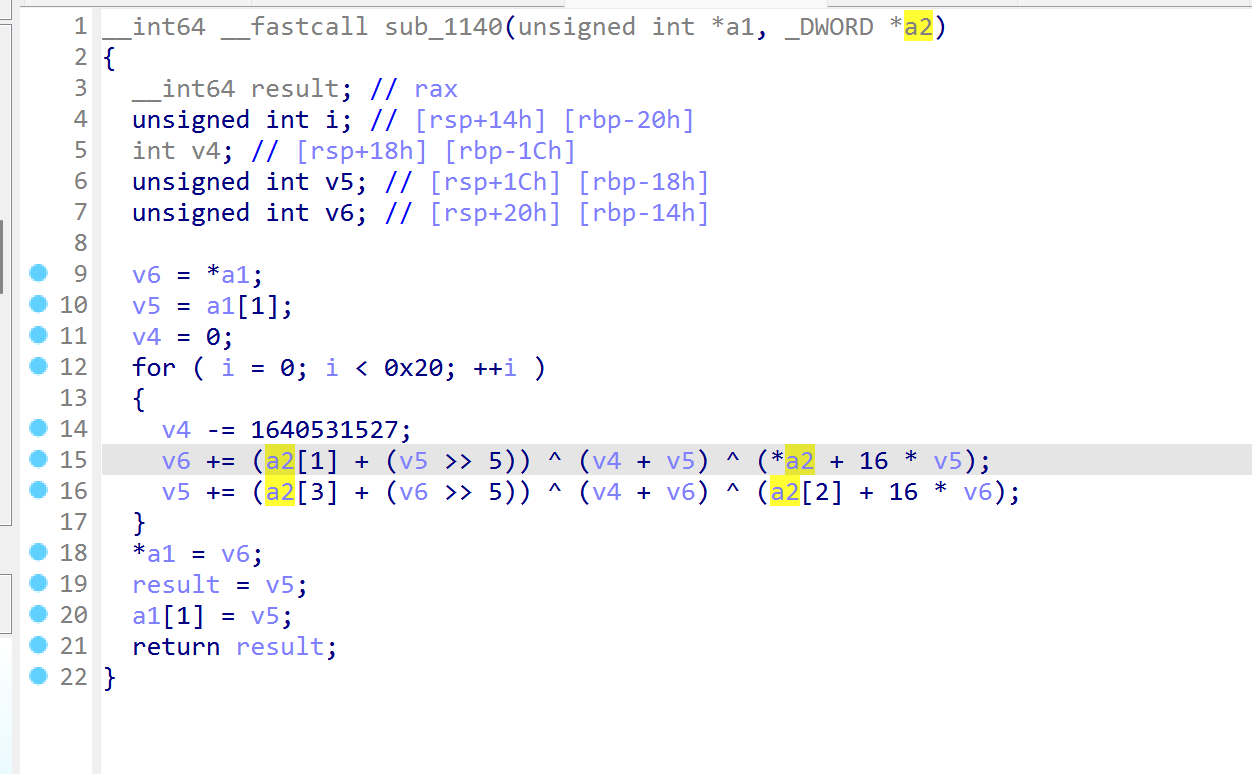
发现是tea
1 | |
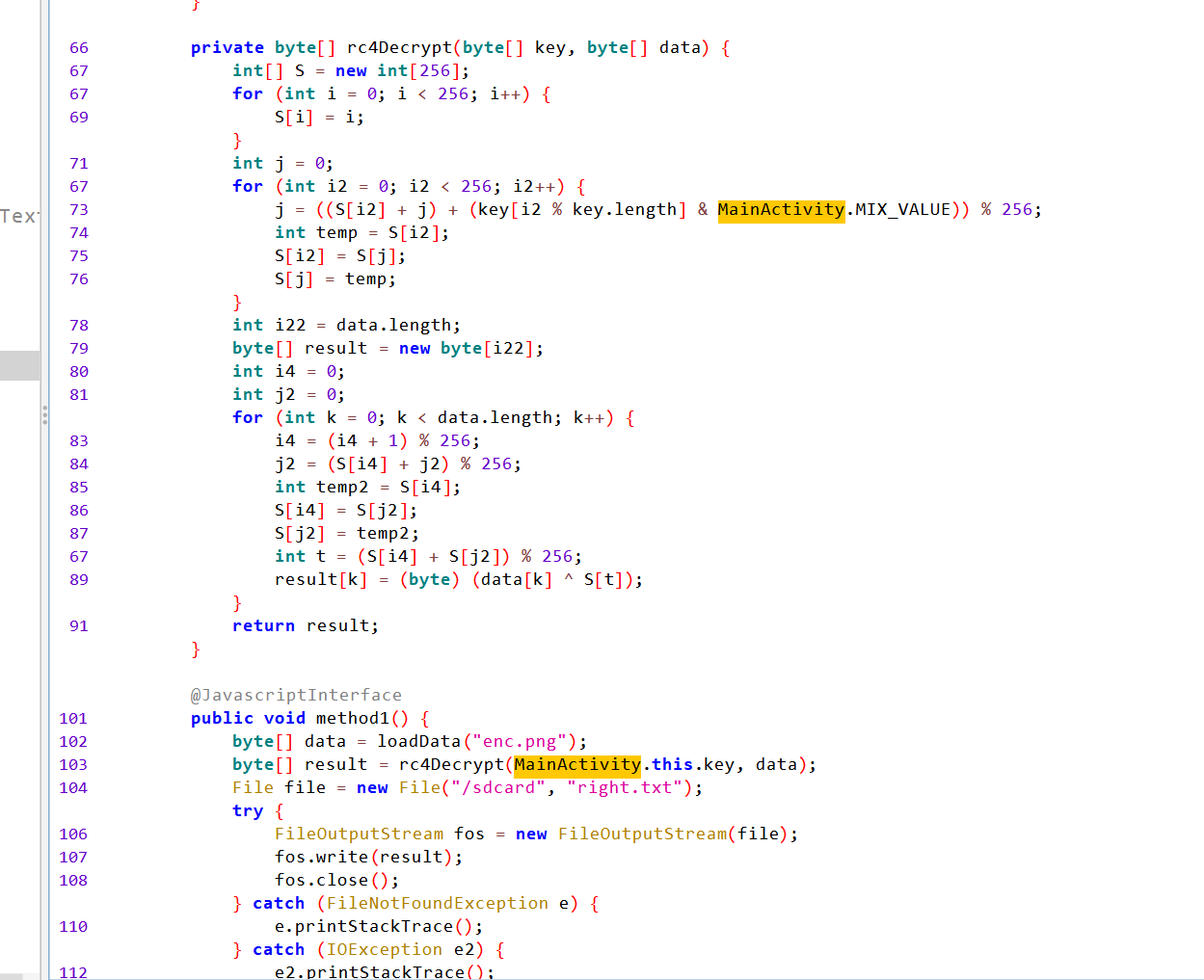
ezAndroid
找到enc.png,rc4解密
1 | |
修改后缀得到png

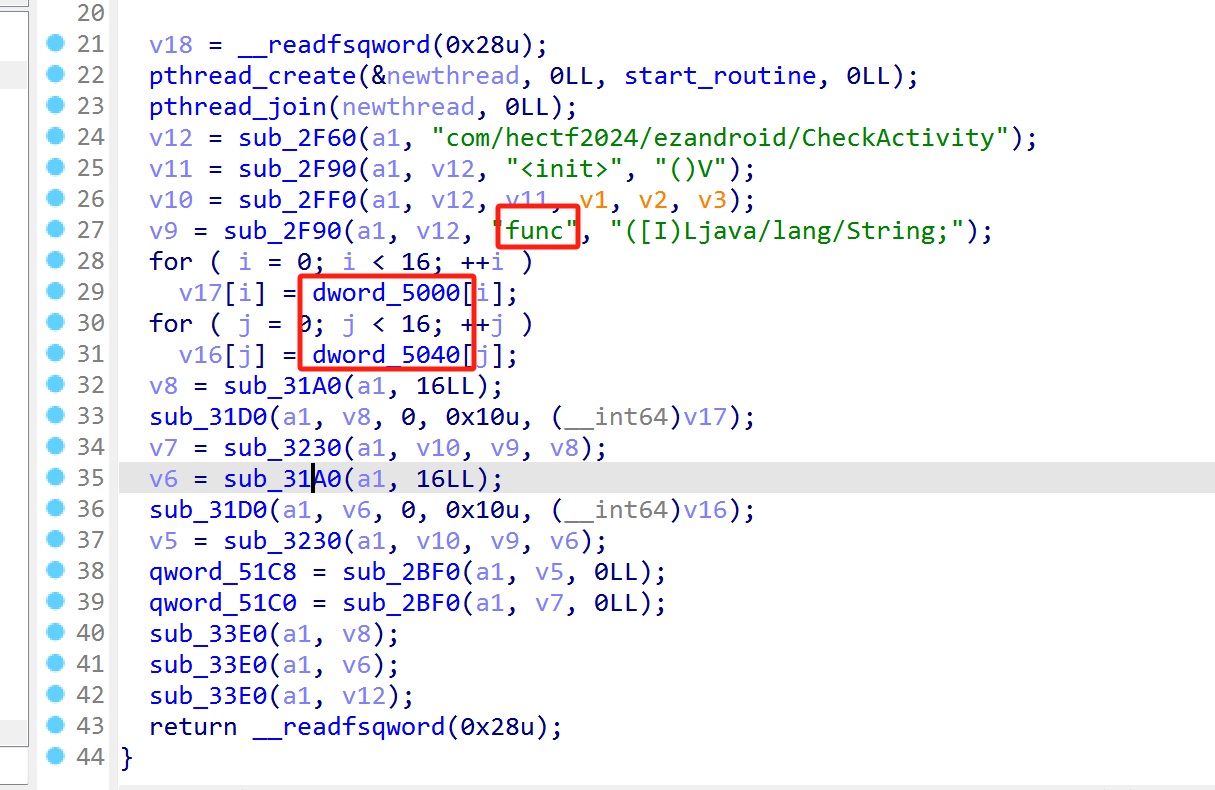
分析CheckActivity
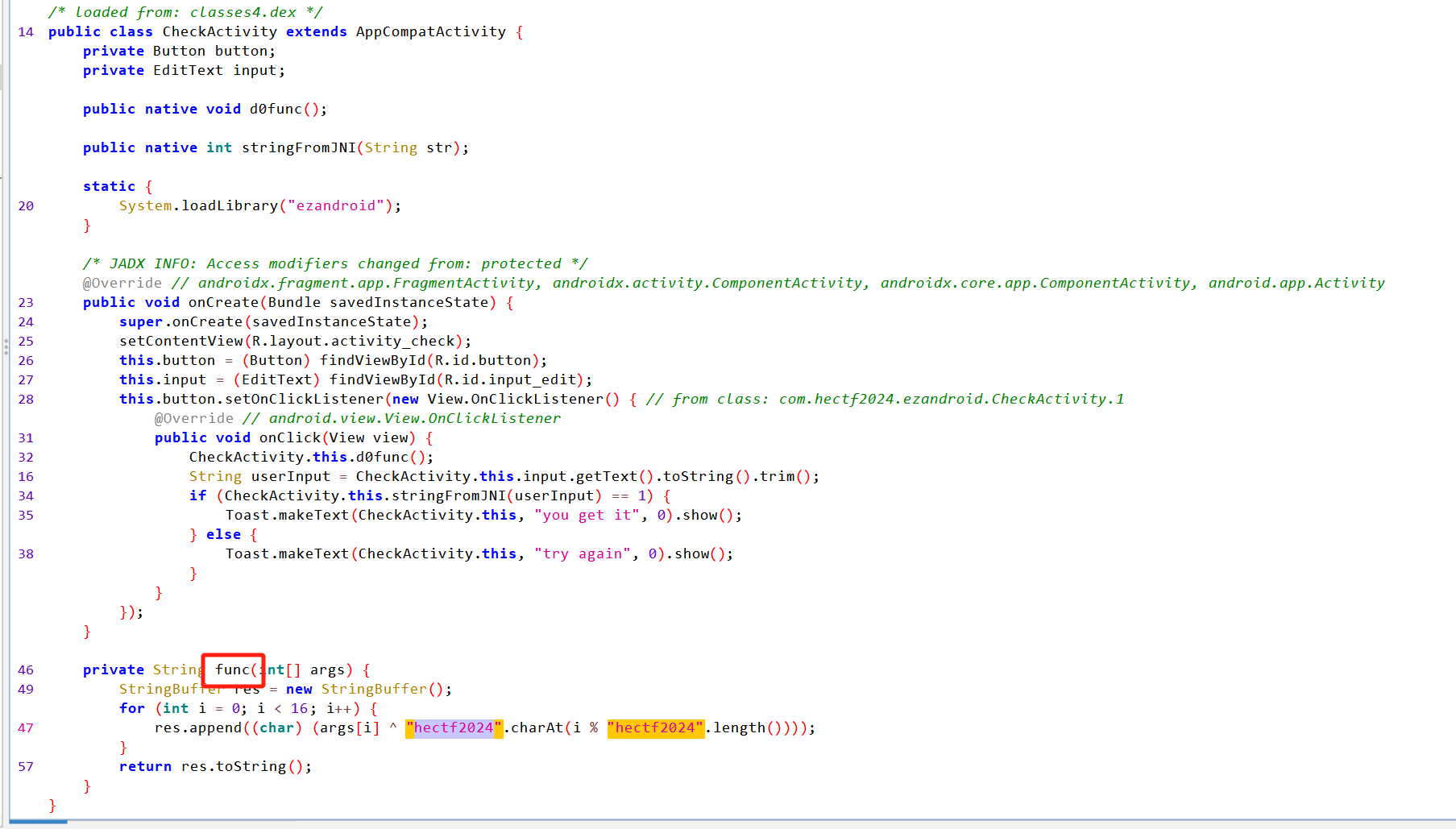
d0func中加载内存并调用func函数,注意内存初始值被修改了
交叉引用找到密文
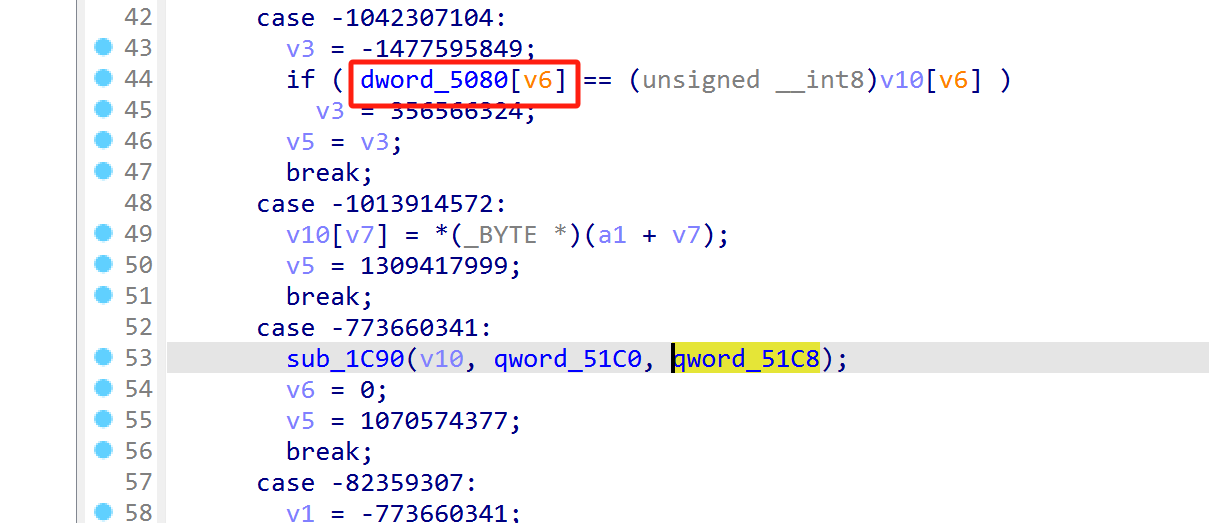
和51c8异或
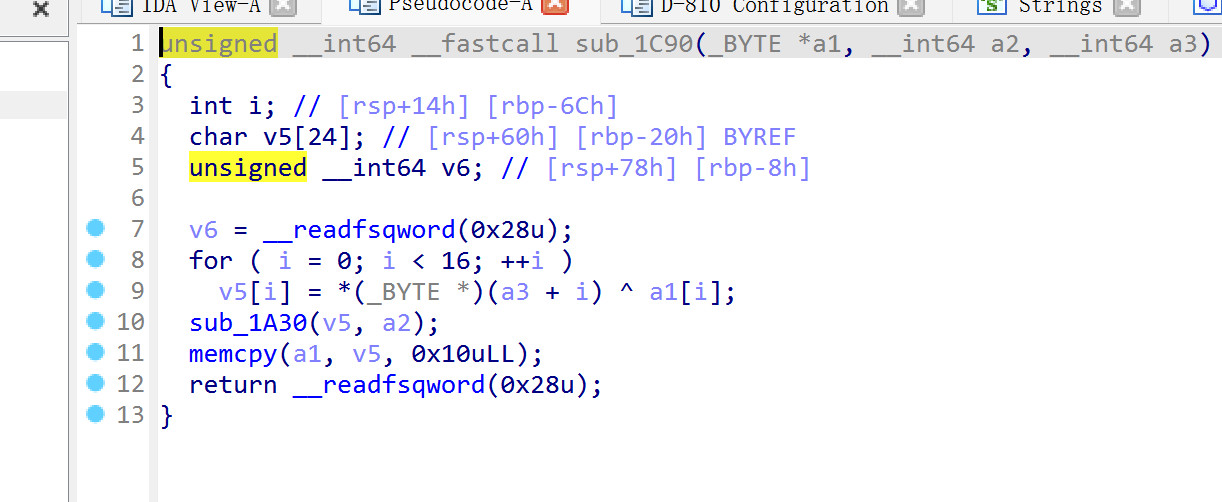
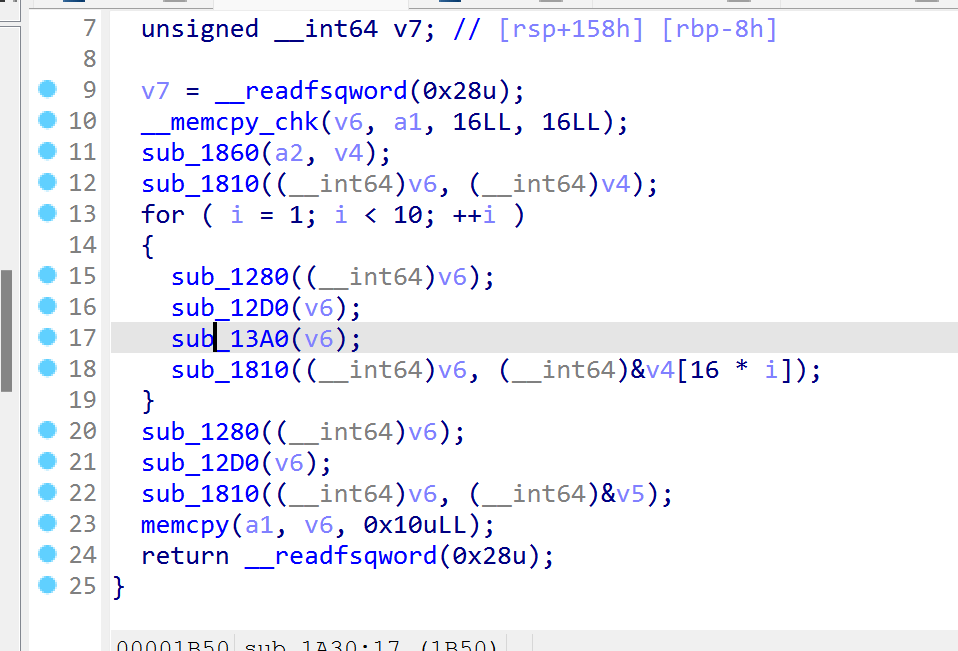
后面是标准aes
通过交叉引用51c8找到tea,实际上没用,因为在aes后面
1 | |
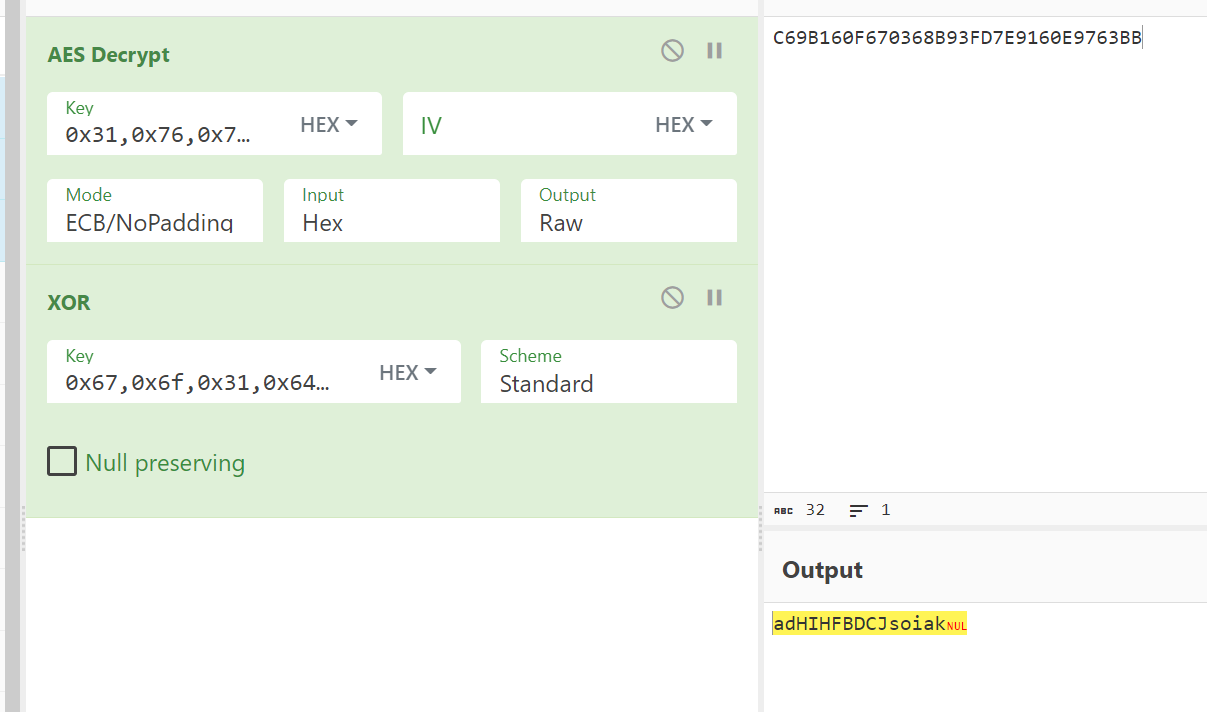
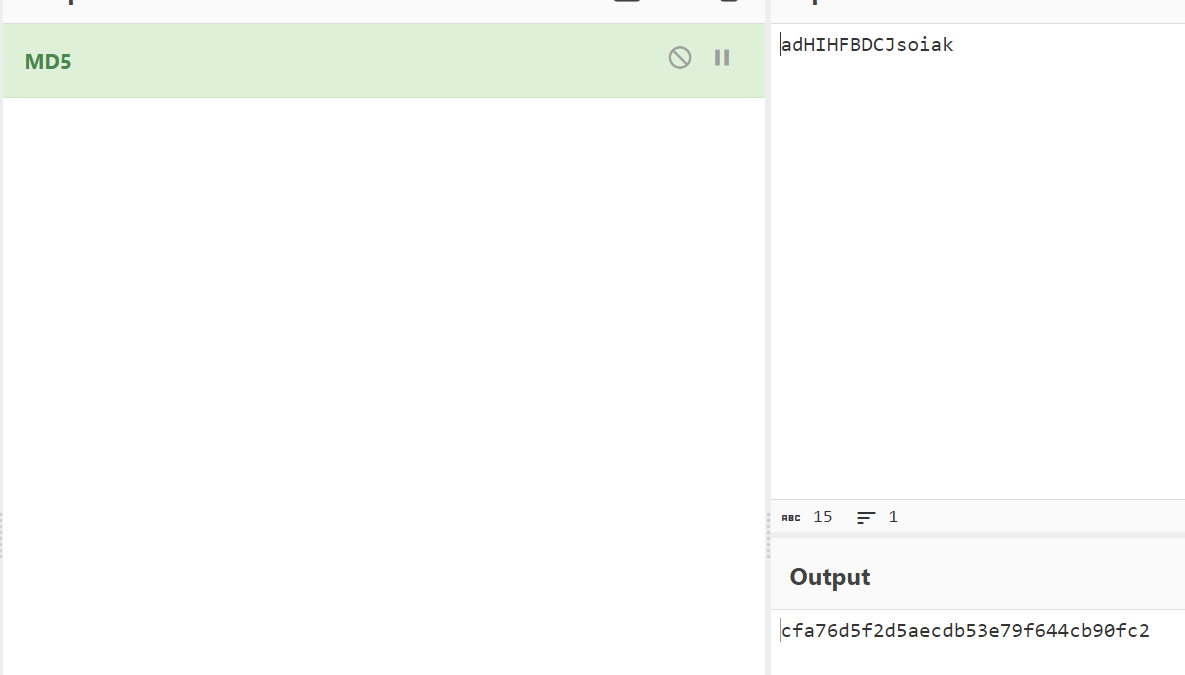
去除最后一个结束符然后md5
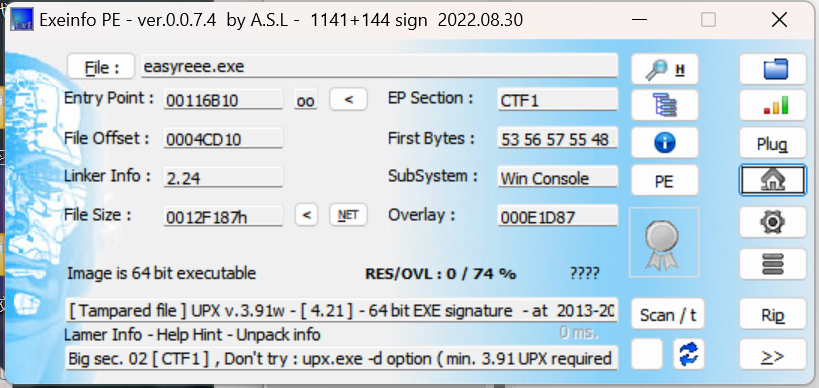
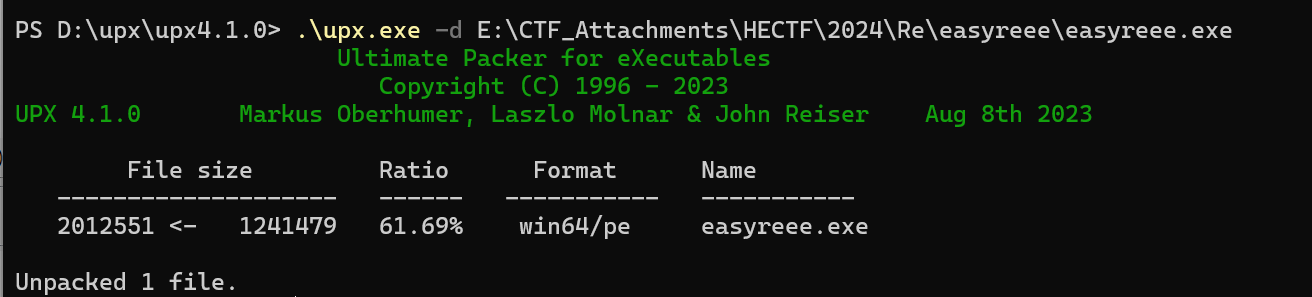
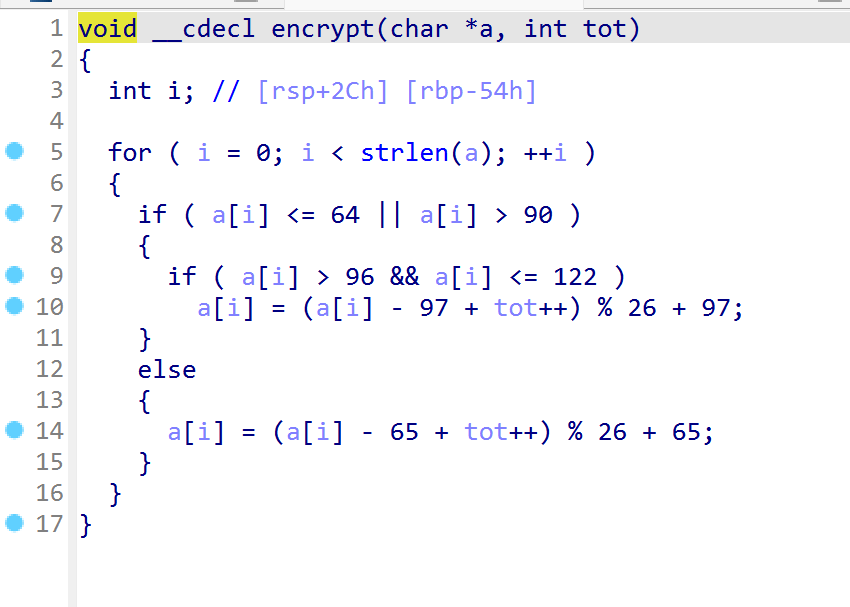
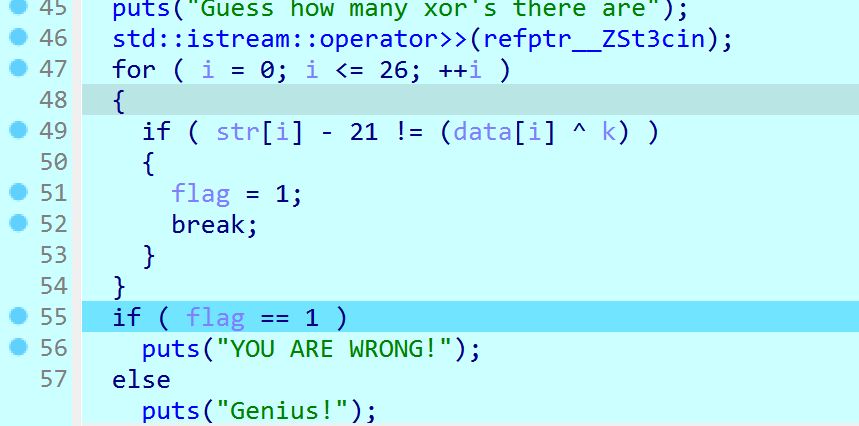
easyreee
1 | |
Pwn
signin
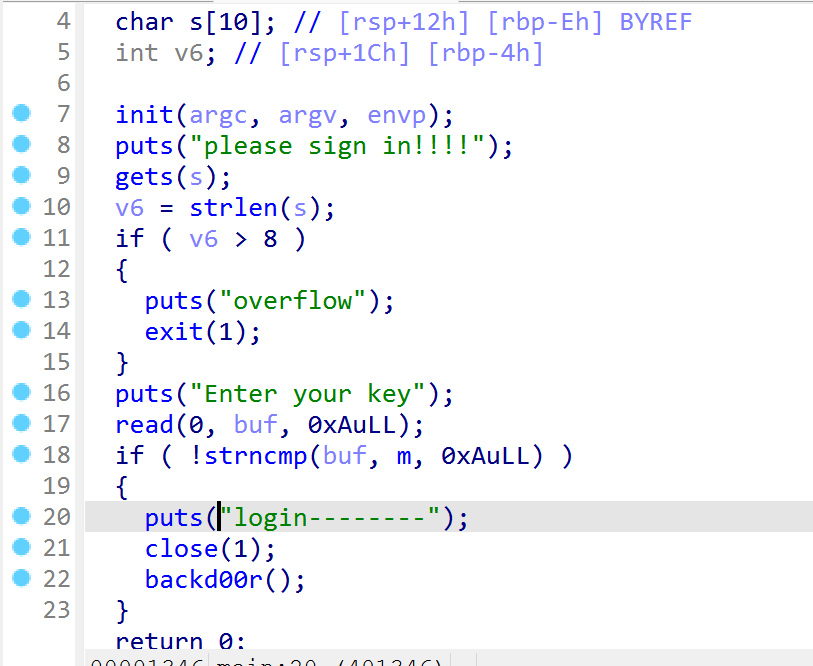
用\x00绕过strlen,然后ret2text
1 | |
Crypto
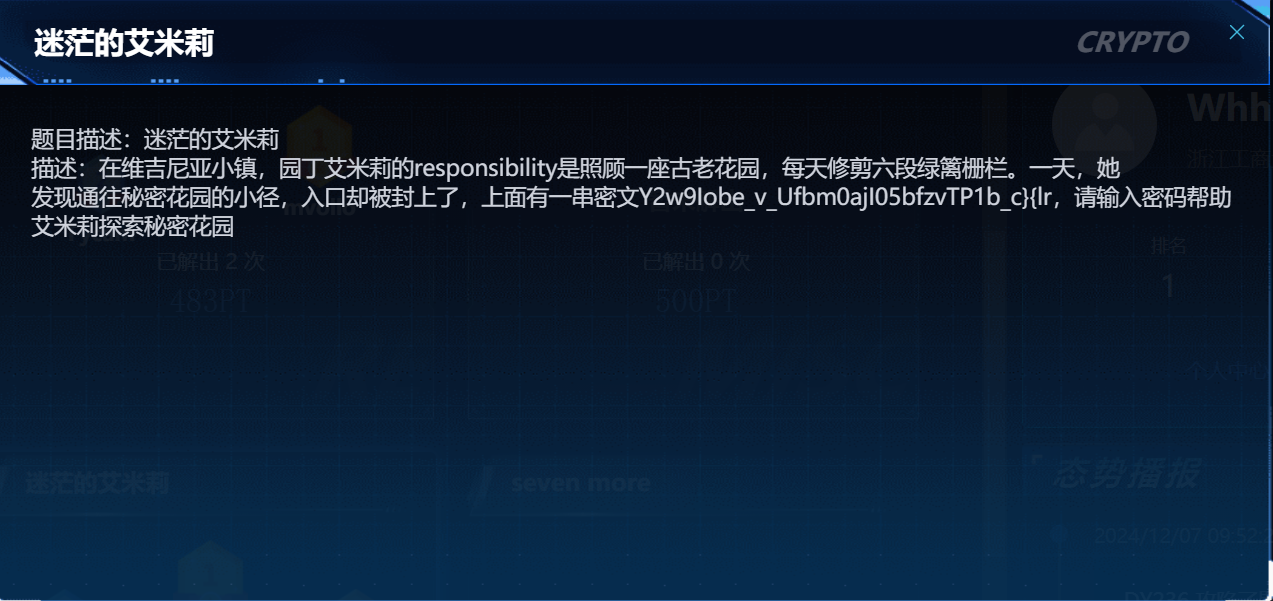
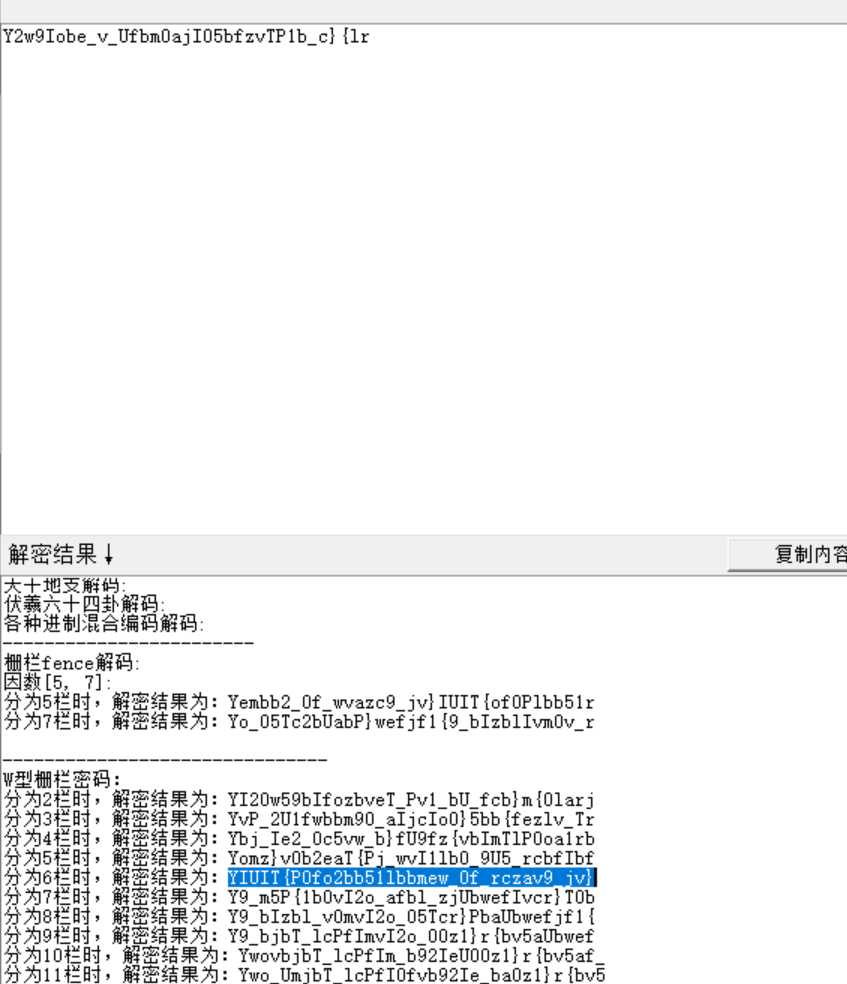
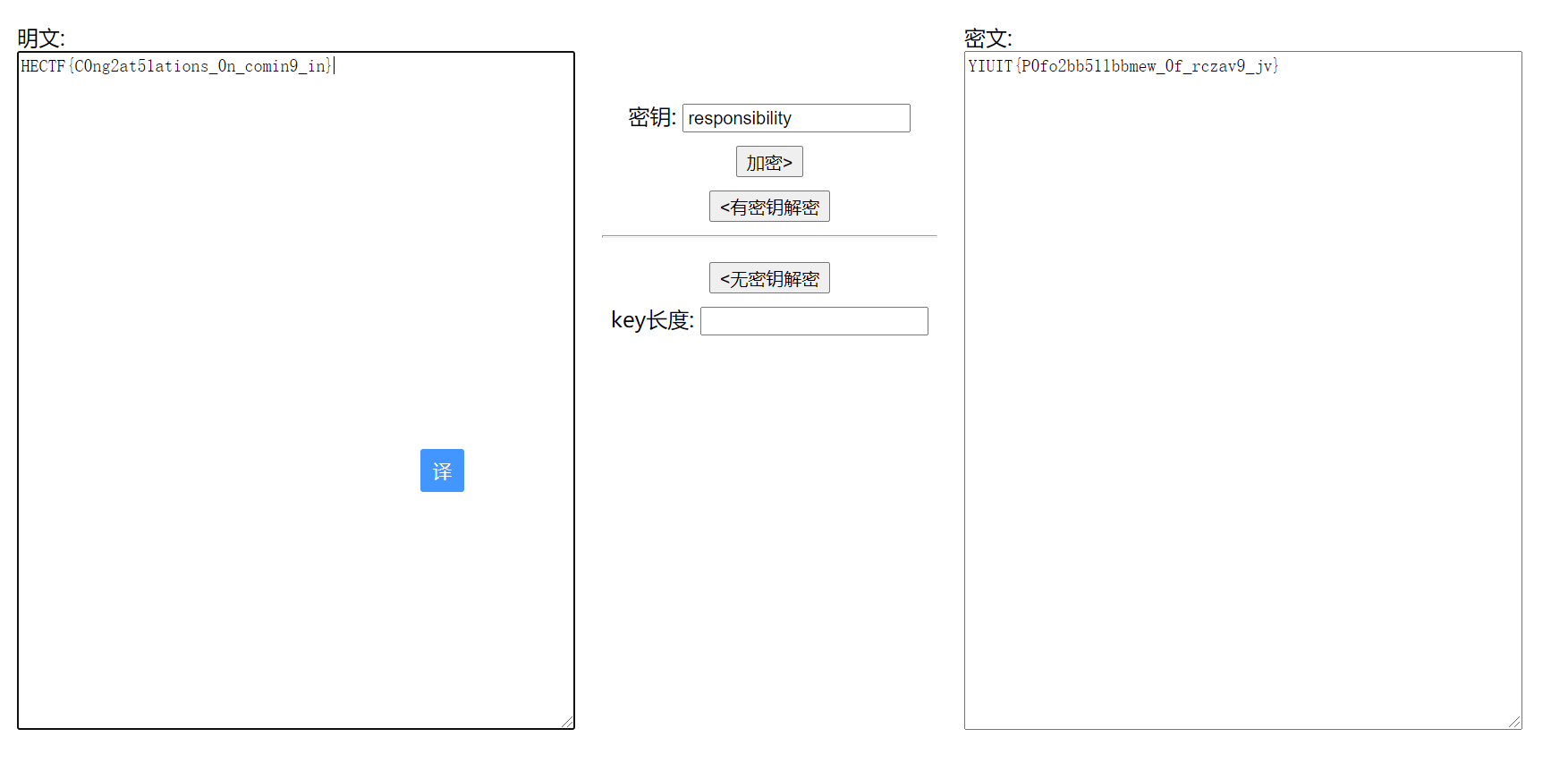
艾米莉
维吉尼亚responsibility作为密钥+栅栏
seven_more
phi是e的倍数
1 | |
爆破大约半小时就能出
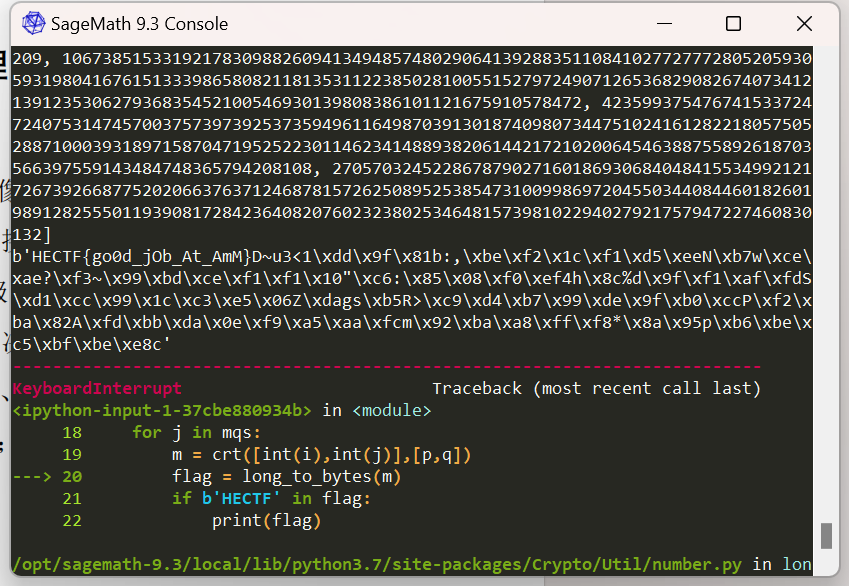
翻一翻
p是q的10进制翻转,找到文章
https://kt.gy/blog/2015/10/asis-2015-finals-rsasr/
先得到pq
1 | |
后面标准rsa
1 | |
HECTF2024部分wp
https://j1ya-22.github.io/2024/12/12/HECTF2024/